Client and ServerSide Vulnerabilities Stephen Reese Pen Testing
Client and Server-Side Vulnerabilities Stephen Reese
Pen Testing vs. Vuln Assessments • Vulnerability Assessments • Penetration Testing • Maturity Levels • Goals • Expectations

Plug-ins are useful evil • Dynamic Content • Browser plug-in • Mobile code • Sandbox evasion
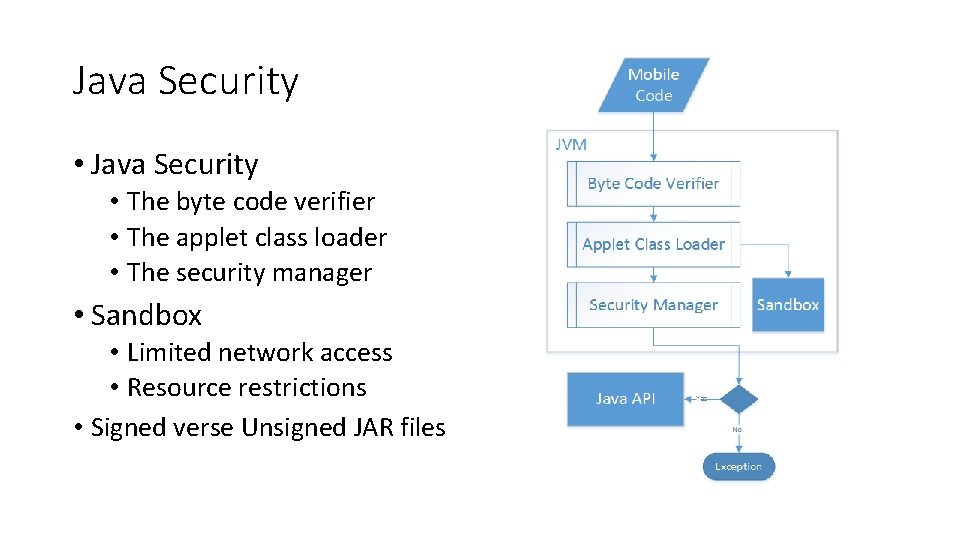
Java Security • The byte code verifier • The applet class loader • The security manager • Sandbox • Limited network access • Resource restrictions • Signed verse Unsigned JAR files
Java Demo • Virtualized Environment • Attacker (Linux Host) • Victim (Windows XP SP 3) • Meta. Sploit Framework • CVE-2013 -2465 • <= JRE 7 u 21 • <= JRE 6 u 45 • <= JRE 5 u 45
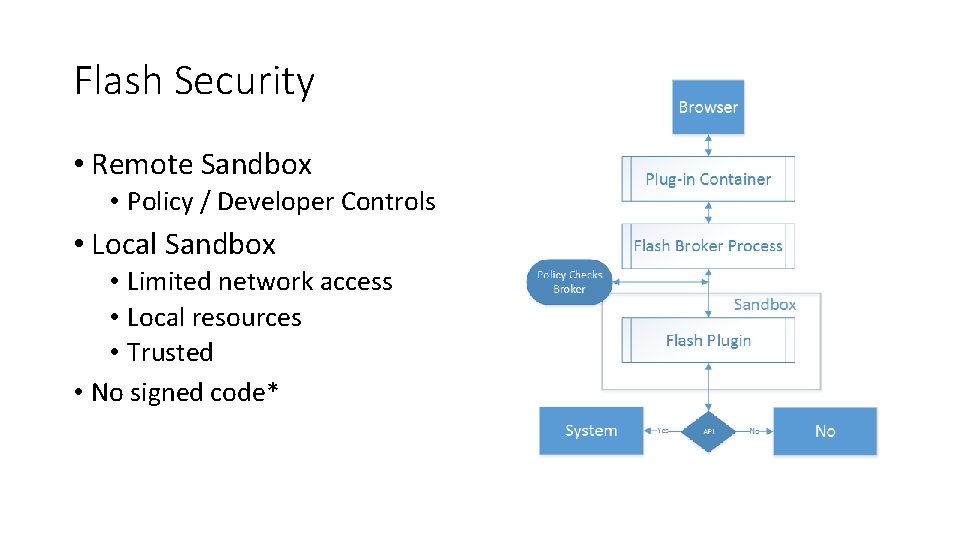
Flash Security • Remote Sandbox • Policy / Developer Controls • Local Sandbox • Limited network access • Local resources • Trusted • No signed code*
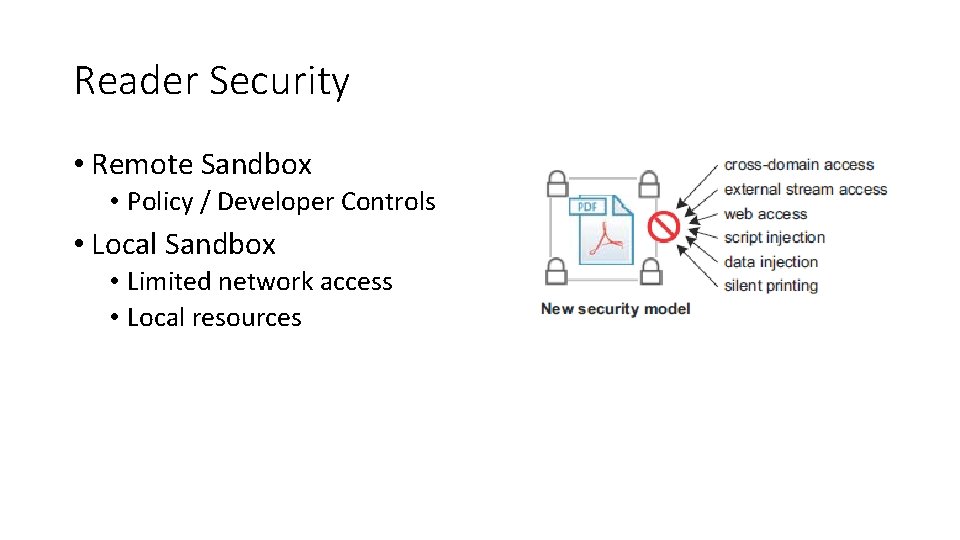
Reader Security • Remote Sandbox • Policy / Developer Controls • Local Sandbox • Limited network access • Local resources
Internet Explorer Demo • Virtualized Environment • Attacker (Linux Host) • Victim (Windows XP SP 3) • Meta. Sploit Framework • Recent 0 -day • CVE-2013 -3893 • IE 6 – 11 • IE 8 (target)
Java Mitigations • Patch • Different Browsers • Click-to-Play • Trusted Zones • Third-party plugins • Disable JRE in browser • Uninstall
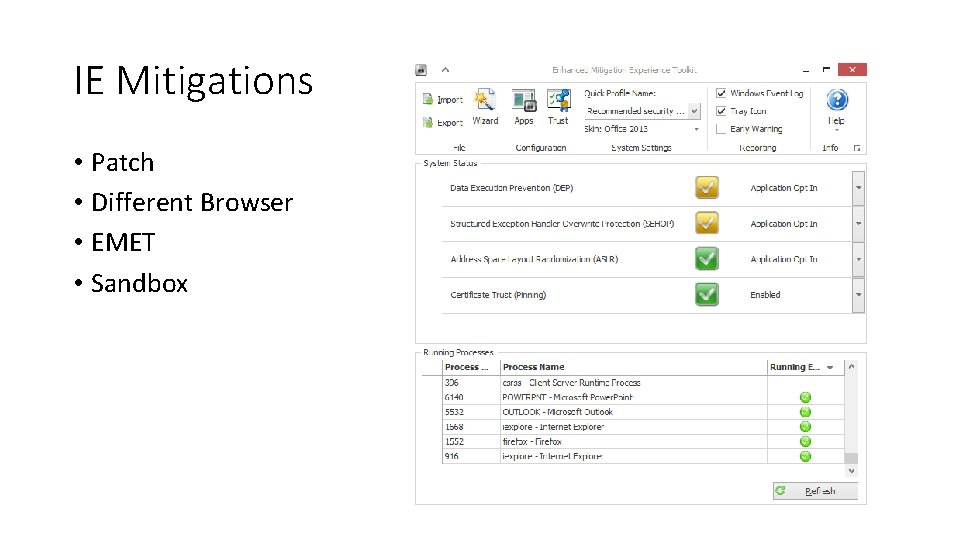
IE Mitigations • Patch • Different Browser • EMET • Sandbox
Flash Mitigations • Patch • Different Browsers • Click-to-Play • Trusted Zones • Third-party plugins • Disable JRE in browser • Uninstall
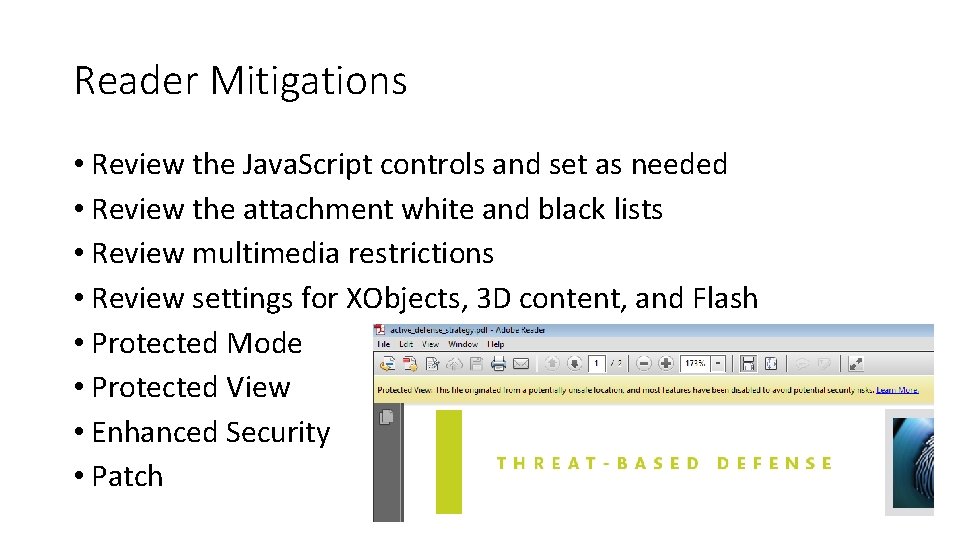
Reader Mitigations • Review the Java. Script controls and set as needed • Review the attachment white and black lists • Review multimedia restrictions • Review settings for XObjects, 3 D content, and Flash • Protected Mode • Protected View • Enhanced Security • Patch
SQLi • SQL queries are run in an unsafe manner • View and/or modify application data • Escalate privileges • Execute OS commands • Demo • Browser or a scanner • Vulnerable Web App
![SQLi Migations • Filter input • Encode output $id = $_GET['id']; $id = stripslashes($id); SQLi Migations • Filter input • Encode output $id = $_GET['id']; $id = stripslashes($id);](http://slidetodoc.com/presentation_image/c785c3b09dea6d3cea2d0d0ef61c6ac6/image-14.jpg)
SQLi Migations • Filter input • Encode output $id = $_GET['id']; $id = stripslashes($id); $id = mysql_real_escape_string($id); htmlentities() htmlspecialchars() strip_tags() addslashes()
Questions?
References • http: //www. rapid 7. com/db/modules/exploit/windows/browser/ms 13_06 9_caret • http: //www. rapid 7. com/db/modules/exploit/multi/browser/java_storeim agearray • http: //www. offensive-security. com/metasploitunleashed/Meterpreter_Basics • http: //www. pcworld. com/article/261562/six_ways_to_protect_against_th e_new_actively_exploited_java_vulnerability. html • https: //www. owasp. org/index. php/OWASP_Broken_Web_Applications_Pr oject • http: //caffeinept. blogspot. com/2012/01/dvwa-sql-injection. html • http: //samiux. blogspot. com/2013/08/howto-dvwa-sql-injection. html
- Slides: 16