CAP 6135 Malware and Software Vulnerability Analysis Botnets
CAP 6135: Malware and Software Vulnerability Analysis Botnets Cliff Zou Spring 2014
Acknowledgement q This lecture uses some contents from the lecture notes from: q q q Dr. Dawn Song: CS 161: computer security Richard Wang – Sophos. Labs: The Development of Botnets Randy Marchany - VA Tech IT Security Lab: Botnets 2
Botnets q Collection of compromised hosts q q q Spread like worms and viruses Once installed, respond to remote commands A network of ‘bots’ robot : an automatic machine that can be programmed to perform specific tasks. Also known as ‘zombies’ 3
q Platform for many attacks q q q Spam forwarding (70% of all spam? ) Click fraud Keystroke logging Distributed denial of service attacks Serious problem q q Top concern of banks, online merchants Vint Cerf: ¼ of hosts connected to Internet 4
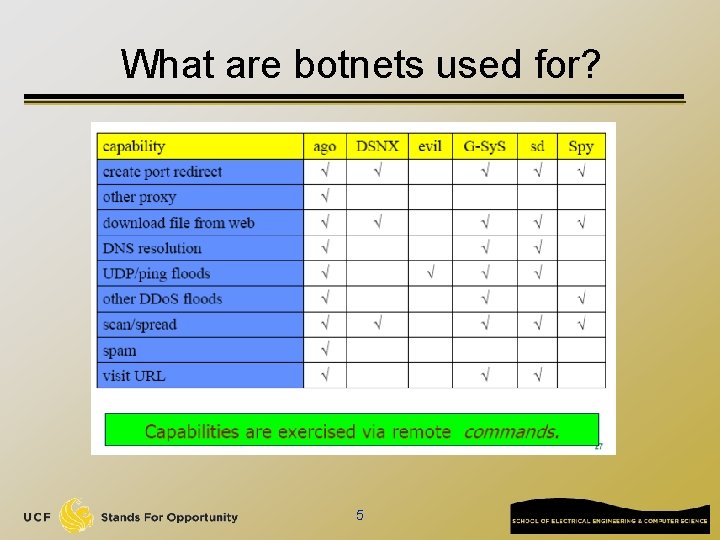
What are botnets used for? 5
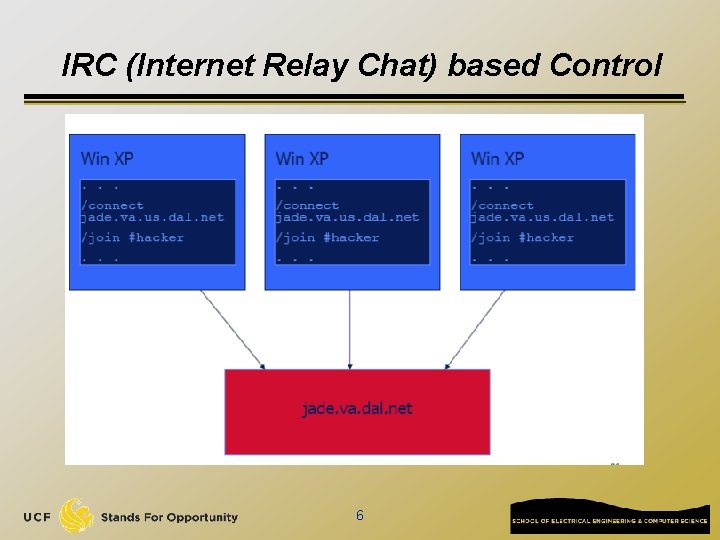
IRC (Internet Relay Chat) based Control 6
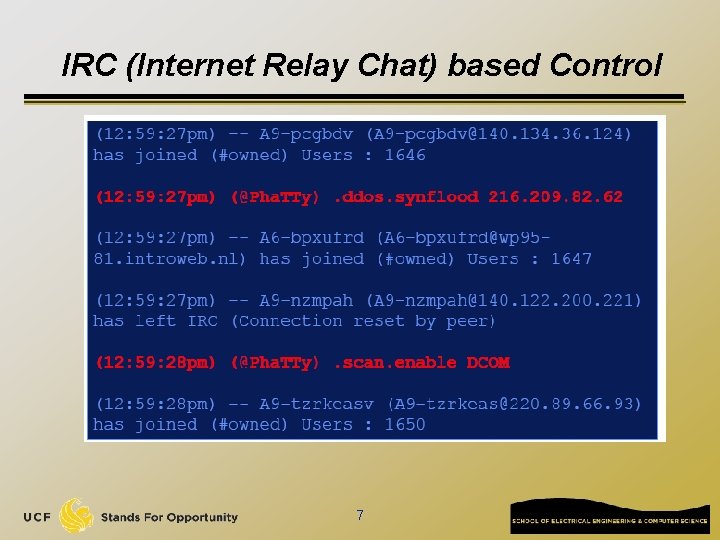
IRC (Internet Relay Chat) based Control 7
Why IRC? q IRC servers are: freely available q easy to manage q easy to subvert q q q Attackers have experience with IRC bots usually have a way to remotely upgrade victims with new payloads to stay ahead of security efforts 8
How bad is the problem? q q Symantec identified a 400 K node botnet Netadmin in the Netherlands discovered 1 -2 M unique IPs associated with Phatbot infections. q q Phatbot harvests My. Doom and Bagel infected machines. Researchers in Gtech monitored thousands of botnets 9
Spreading Problem q Spreading mechanism is a leading cause of background noise q q Port 445, 139, 137 accounted for 80% of traffic captured by German Honeynet Project Other ports 2745 q 3127 q 3410 q 5000 q – – bagle backdoor My. Doom backdoor Optix trojan backdoor upnp vulnerability 10
Most commonly used Bot families q Agobot q SDBot q Spy. Bot q GT Bot
Agobot q q q q q Most sophisticated 20, 000 lines C/C++ code IRC based command/control Large collection of target exploits Capable of many Do. S attack types Shell encoding/polymorphic obfuscation Traffic sniffers/key logging Defend/fortify compromised system Ability to frustrate dissassembly
SDBot q q Simpler than Agobot, 2, 000 lines C code Non-malicious at base Utilize IRC-based command/control Easily extended for malicious purposes q Scanning q Do. S Attacks q Sniffers q Information harvesting q Encryption
Spy. Bot q q <3, 000 lines C code Possibly evolved from SDBot q Similar command/control engine q No attempts to hide malicious purposes
GT Bot Functions based on m. IRC scripting capabilities q Hide. Window program hides bot on local system q q q Basic rootkit function Port scanning, Do. S attacks, exploits for RPC and Net. BIOS
q q Variance in codebase size, structure, complexity, implementation Convergence in set of functions q q q Possibility for defense systems effective across bot families Bot families extensible Agobot likely to become dominant
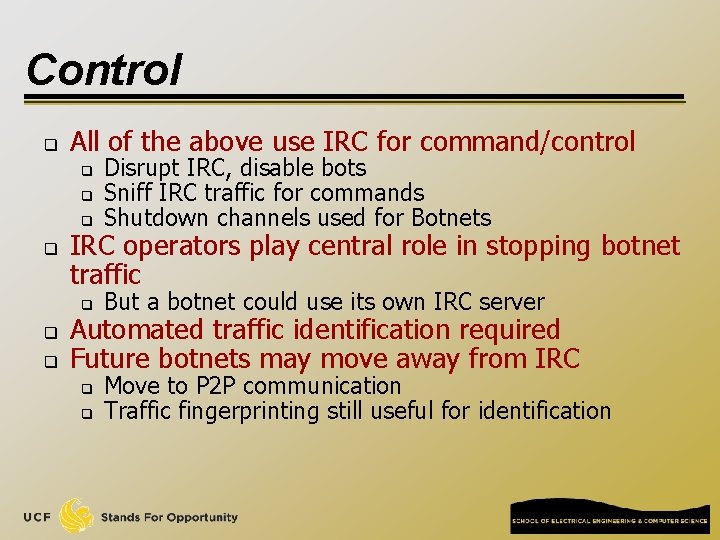
Control q All of the above use IRC for command/control q Disrupt IRC, disable bots Sniff IRC traffic for commands Shutdown channels used for Botnets q But a botnet could use its own IRC server q q q IRC operators play central role in stopping botnet traffic Automated traffic identification required Future botnets may move away from IRC q q Move to P 2 P communication Traffic fingerprinting still useful for identification
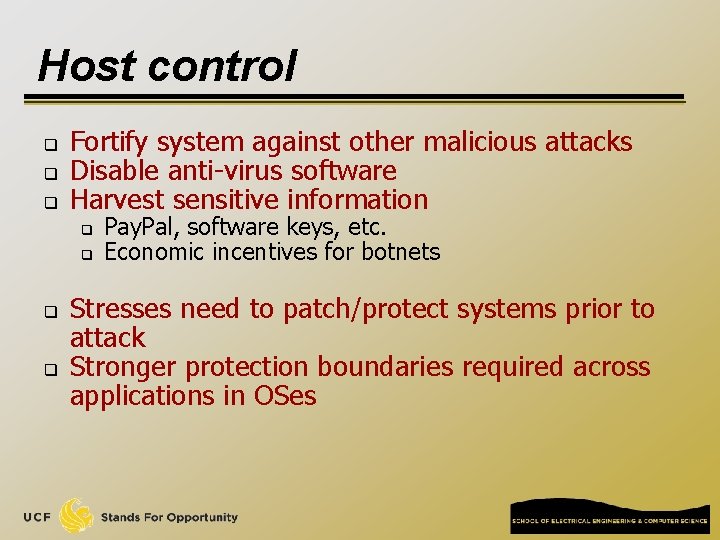
Host control q q q Fortify system against other malicious attacks Disable anti-virus software Harvest sensitive information q q Pay. Pal, software keys, etc. Economic incentives for botnets Stresses need to patch/protect systems prior to attack Stronger protection boundaries required across applications in OSes
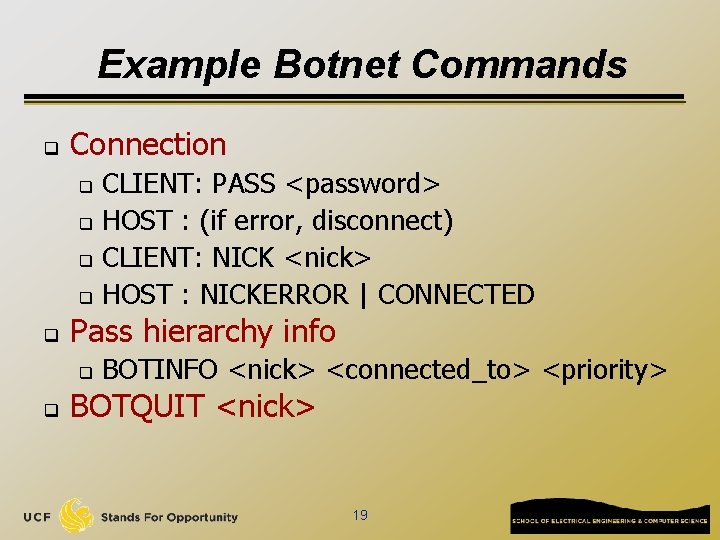
Example Botnet Commands q Connection CLIENT: PASS <password> q HOST : (if error, disconnect) q CLIENT: NICK <nick> q HOST : NICKERROR | CONNECTED q q Pass hierarchy info q q BOTINFO <nick> <connected_to> <priority> BOTQUIT <nick> 19
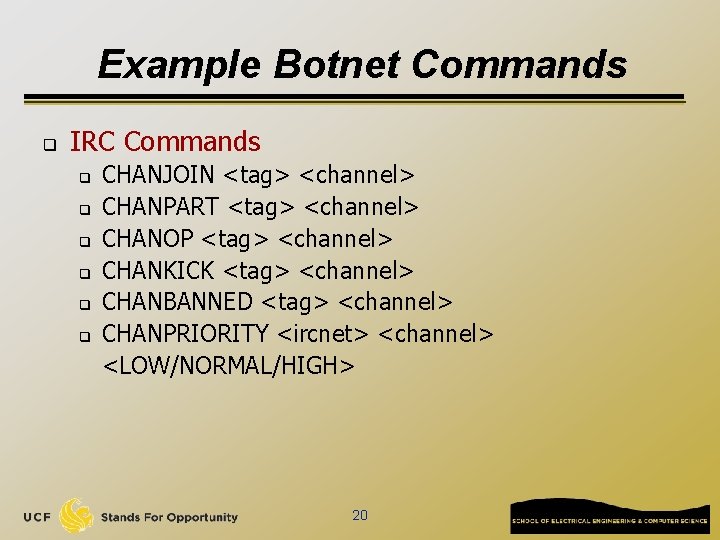
Example Botnet Commands q IRC Commands q q q CHANJOIN <tag> <channel> CHANPART <tag> <channel> CHANOP <tag> <channel> CHANKICK <tag> <channel> CHANBANNED <tag> <channel> CHANPRIORITY <ircnet> <channel> <LOW/NORMAL/HIGH> 20
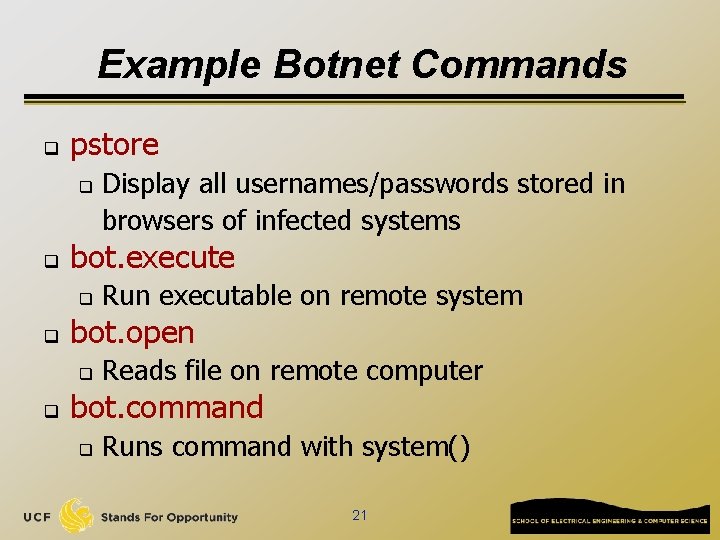
Example Botnet Commands q pstore q q bot. execute q q Run executable on remote system bot. open q q Display all usernames/passwords stored in browsers of infected systems Reads file on remote computer bot. command q Runs command with system() 21
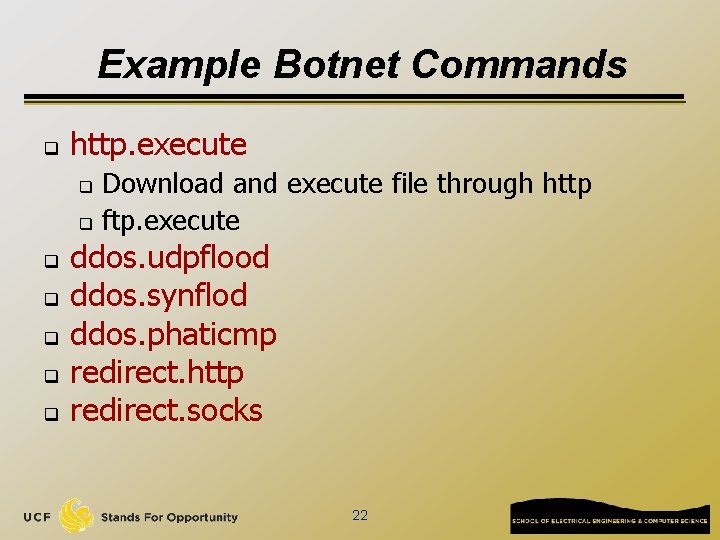
Example Botnet Commands q http. execute Download and execute file through http q ftp. execute q q q ddos. udpflood ddos. synflod ddos. phaticmp redirect. http redirect. socks 22
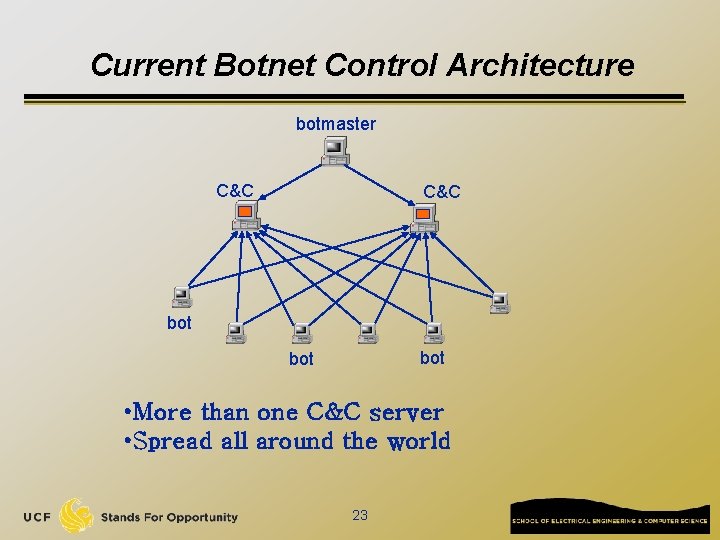
Current Botnet Control Architecture botmaster C&C bot bot • More than one C&C server • Spread all around the world 23
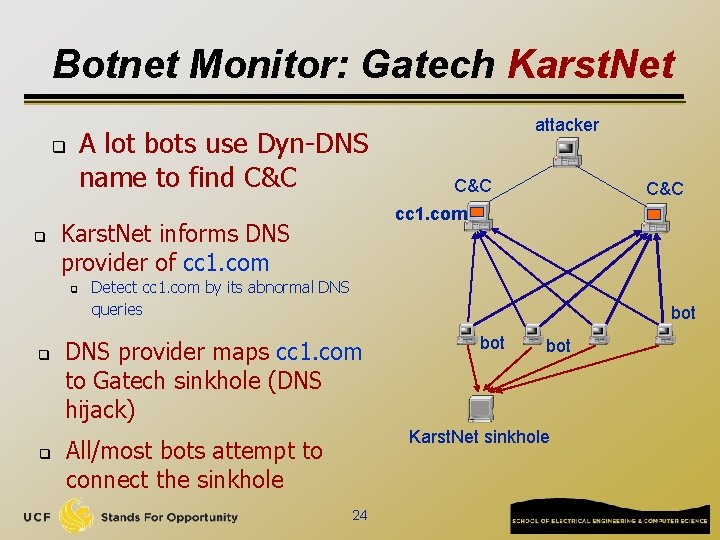
Botnet Monitor: Gatech Karst. Net A lot bots use Dyn-DNS name to find C&C q q C&C cc 1. com Karst. Net informs DNS provider of cc 1. com q attacker Detect cc 1. com by its abnormal DNS queries bot DNS provider maps cc 1. com to Gatech sinkhole (DNS hijack) bot Karst. Net sinkhole All/most bots attempt to connect the sinkhole 24
Botnet Monitor: Honeypot Spy q Security researchers set up honeypots q q Honeypots: deliberately set up vulnerable machines When compromised, put close monitoring of malware’s behaviors Tutorial: http: //en. wikipedia. org/wiki/Honeypot_%28 computing%29 When compromised honeypot joins a botnet q q q Passive monitoring: log all network traffic Active monitoring: actively contact other bots to obtain more information (neighborhood list, additional c&c, etc. ) Representative research paper: q A multifaceted approach to understanding the botnet phenomenon, Abu Rajab, Moheeb and Zarfoss, Jay and Monrose, Fabian and Terzis, Andreas, 6 th ACM SIGCOMM conference on Internet measurement (IMC), 2006. 25
The Future Generation of Botnets q Peer-to-Peer C&C q Polymorphism q Anti-honeypot q Rootkit techniques 26
- Slides: 26