How Ransomware Beats Your Backups Learn How to
How Ransomware Beats Your Backups Learn How to Eliminate Downtime and Data loss
AGENDA Introduction Our mission How is ransomware winning? What can you do to beat it? Q&A RECORDING? The video will be posted at www. infrascale. com/webinars. SLIDES? Yes! The slides are available in handouts now. JOIN THE CONVERSATION! Follow us on Twitter @infrascale. QUESTIONS? Post questions for our presenter(s) throughout the webinar.
ABOUT COMPANY NAME At A Glance Founded: Locations: Businesses Served: Active Customers: Active Technicians: Specialties/Key Focus Areas: Notable Customers
ABOUT INFRASCALE Unrivaled initial backup speed and a full set of features and tools make it a top choice for off-site data protection. INFRASCALE AT A GLANCE Founded: HQ: Partners: Customers: Data Centers: Data Protected: 2011 Los Angeles, CA 1, 000 1 M devices protected & counting 7 global data centers 100+ petabytes of data THIRD PARTY VALIDATION VISIONARY Disaster Recovery as a Service

OUR MISSION ERADICATE DOWNTIME & DATA-LOSS
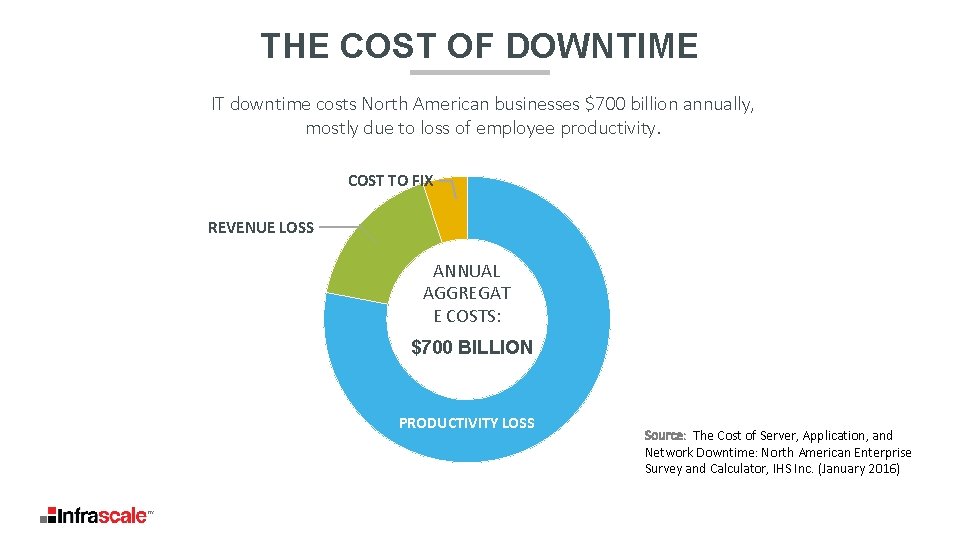
THE COST OF DOWNTIME IT downtime costs North American businesses $700 billion annually, mostly due to loss of employee productivity. COST TO FIX REVENUE LOSS ANNUAL AGGREGAT E COSTS: $700 BILLION PRODUCTIVITY LOSS Source: The Cost of Server, Application, and Network Downtime: North American Enterprise Survey and Calculator, IHS Inc. (January 2016)
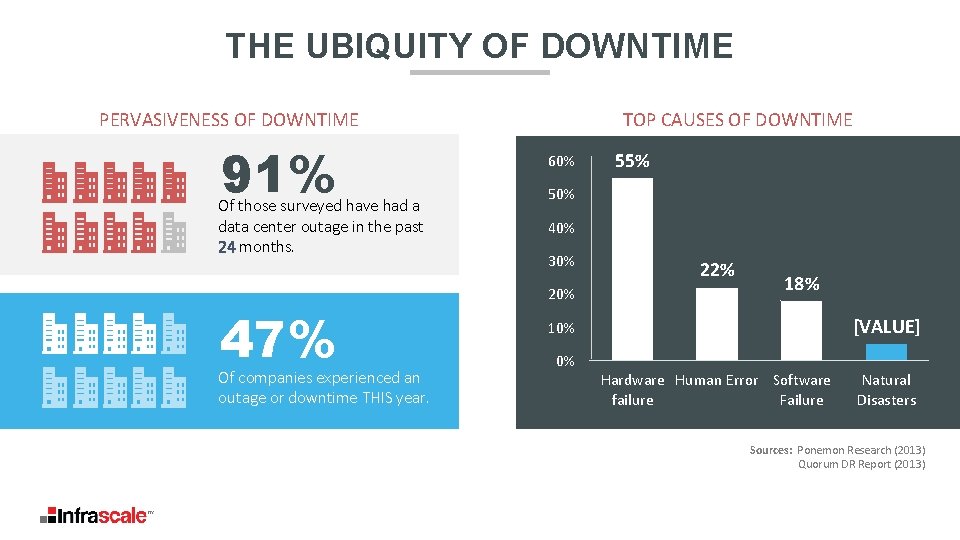
THE UBIQUITY OF DOWNTIME PERVASIVENESS OF DOWNTIME 91% Of those surveyed have had a data center outage in the past 24 months. 47% Of companies experienced an outage or downtime THIS year. TOP CAUSES OF DOWNTIME 60% 55% 50% 40% 30% 22% 18% [VALUE] 10% 0% Hardware Human Error Software failure Failure Natural Disasters Sources: Ponemon Research (2013) Quorum DR Report (2013)
POLL Do you know how much your company loses for every day of downtime? A No, but it’s not good. B Rough idea, but it hasn’t been formally assessed. C Yes, that’s why we’re here.

CHALLENGES WITH RANSOMWARE It’s not the ransom that’s so damaging to your business. It’s the downtime.
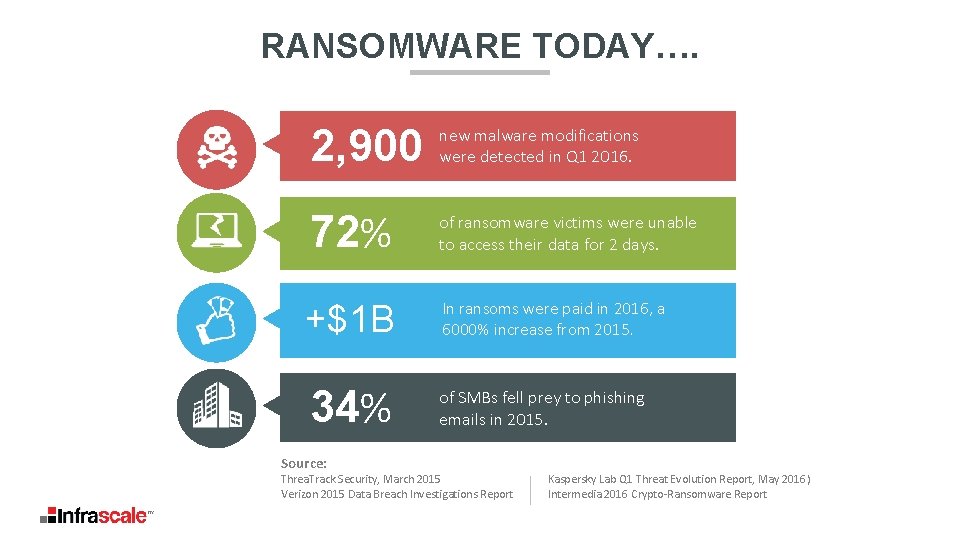
RANSOMWARE TODAY…. 2, 900 new malware modifications were detected in Q 1 2016. 72% of ransomware victims were unable to access their data for 2 days. +$1 B In ransoms were paid in 2016, a 6000% increase from 2015. 34% of SMBs fell prey to phishing emails in 2015. Source: Threa. Track Security, March 2015 Verizon 2015 Data Breach Investigations Report Kaspersky Lab Q 1 Threat Evolution Report, May 2016) Intermedia 2016 Crypto-Ransomware Report
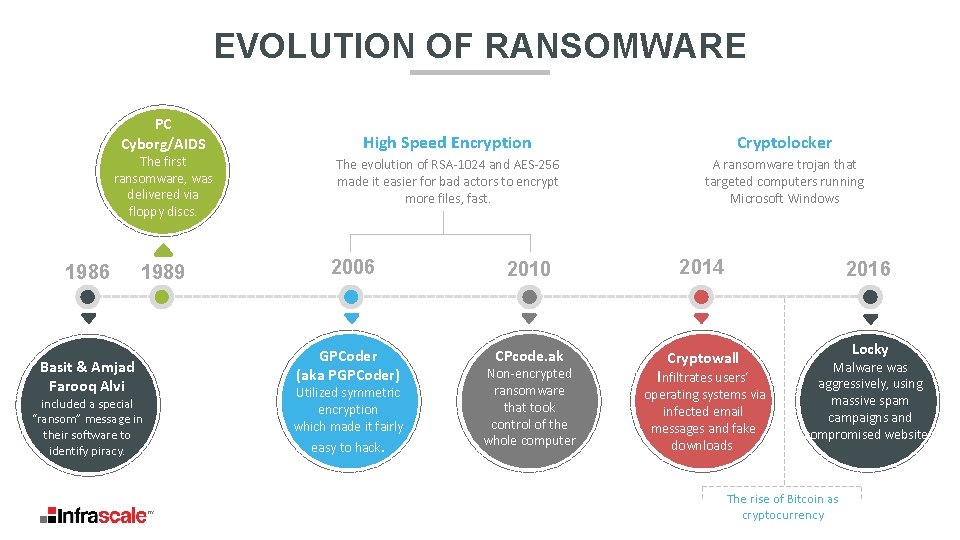
EVOLUTION OF RANSOMWARE PC Cyborg/AIDS The first ransomware, was delivered via floppy discs. 1986 Basit & Amjad Farooq Alvi 1989 included a special “ransom” message in their software to identify piracy. High Speed Encryption Cryptolocker The evolution of RSA-1024 and AES-256 made it easier for bad actors to encrypt more files, fast. A ransomware trojan that targeted computers running Microsoft Windows 2006 GPCoder (aka PGPCoder) Utilized symmetric encryption which made it fairly easy to hack. 2010 2014 CPcode. ak Cryptowall Non-encrypted ransomware that took control of the whole computer 2016 Infiltrates users‘ operating systems via infected email messages and fake downloads Locky Malware was aggressively, using massive spam campaigns and compromised websites. The rise of Bitcoin as cryptocurrency
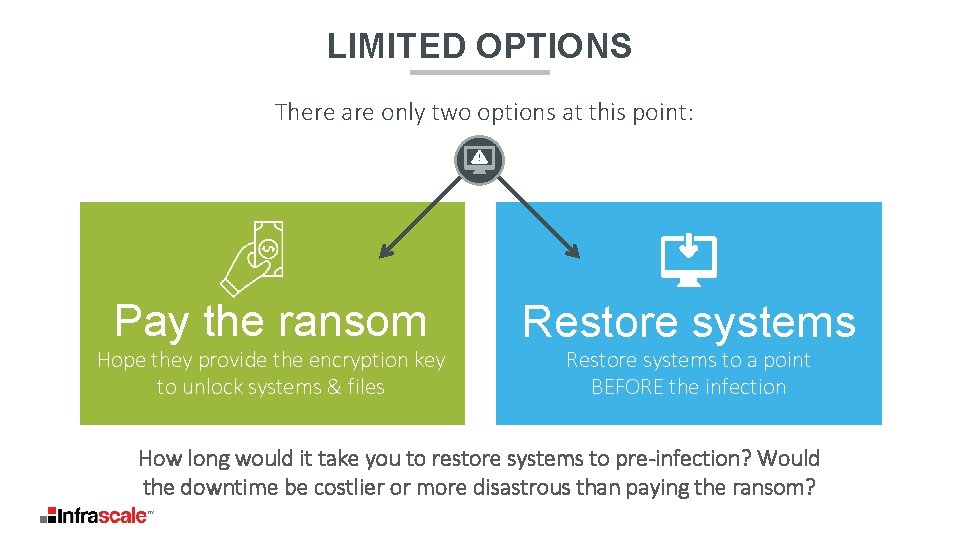
LIMITED OPTIONS There are only two options at this point: Pay the ransom Hope they provide the encryption key to unlock systems & files Restore systems to a point BEFORE the infection How long would it take you to restore systems to pre-infection? Would the downtime be costlier or more disastrous than paying the ransom?
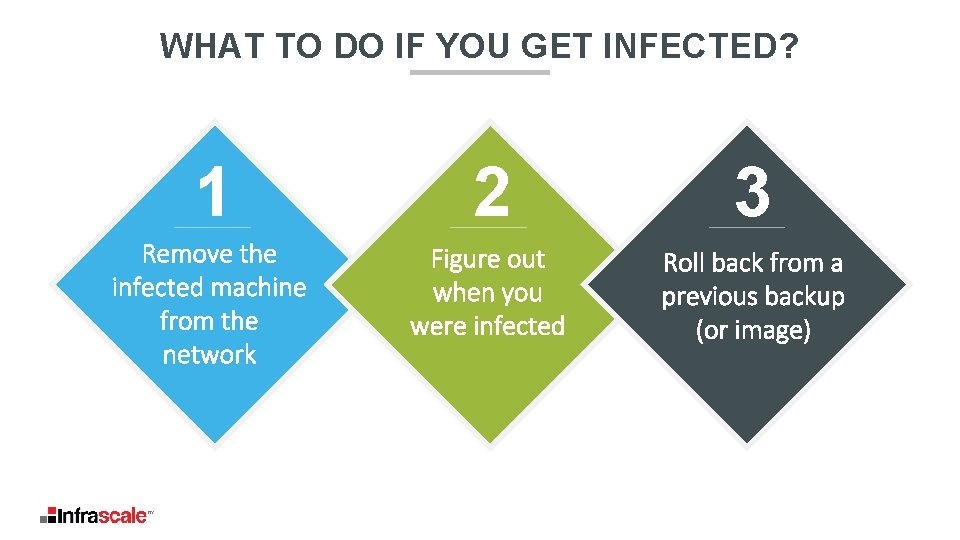
WHAT TO DO IF YOU GET INFECTED? 1 2 3 Remove the infected machine from the network Figure out when you were infected Roll back from a previous backup (or image)
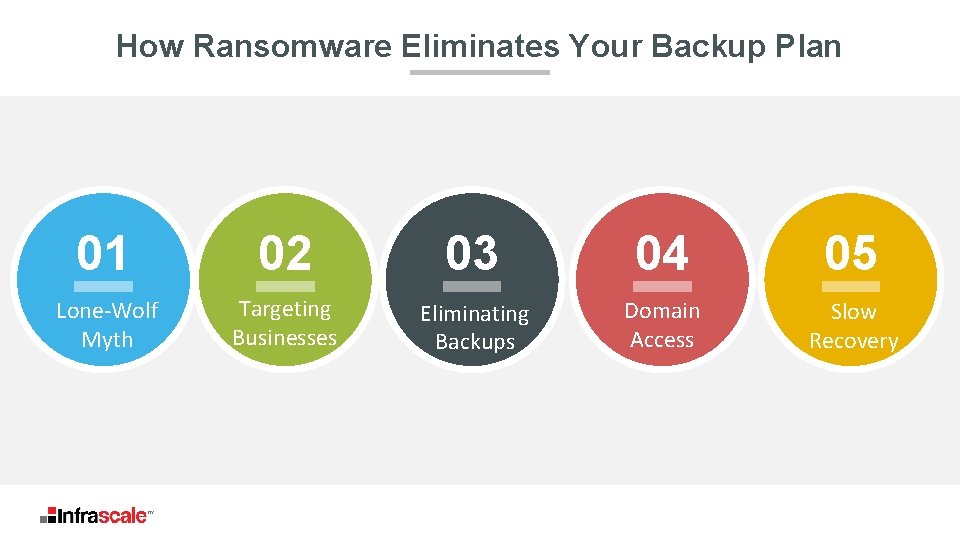
How Ransomware Eliminates Your Backup Plan 01 02 03 04 05 Lone-Wolf Myth Targeting Businesses Eliminating Backups Domain Access Slow Recovery
THE LONE-WOLF MYTH 01 Lone-wolf Myth Ransomware variants and campaigns are purpose built to optimize revenue generated § § § Campaign tracking and identification Vulnerability specific targeting Industry-specific targeting Business profile targeting Product Roadmaps and evolution
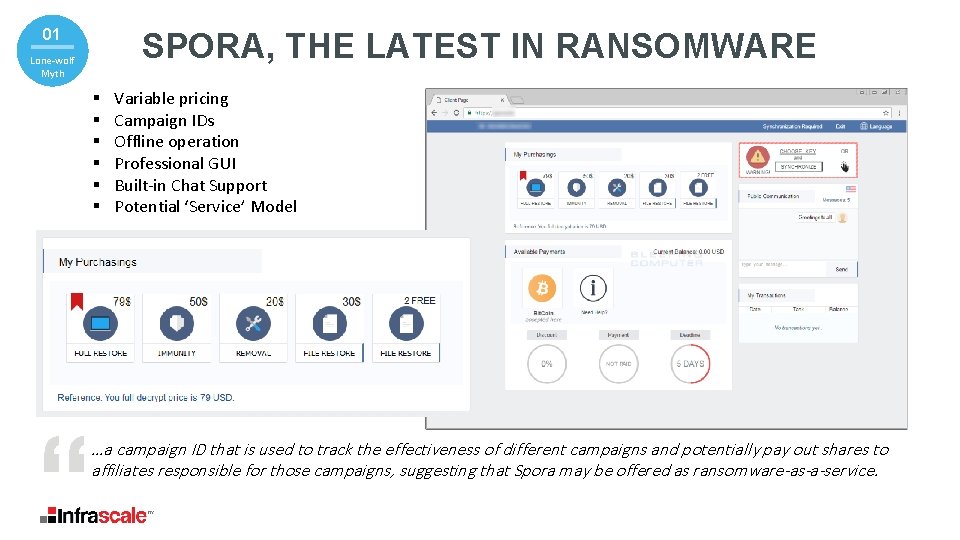
02 01 SPORA, THE LATEST IN RANSOMWARE Lone-wolf Myth § § § Variable pricing Campaign IDs Offline operation Professional GUI Built-in Chat Support Potential ‘Service’ Model …a campaign ID that is used to track the effectiveness of different campaigns and potentially pay out shares to affiliates responsible for those campaigns, suggesting that Spora may be offered as ransomware-as-a-service.

TARGETING YOUR BUSINESS In 2016, Cyber criminals began moving to business targets for bigger ransoms. 02 Targeting Businesses § § § SMBs Industrial Services Medical Facilities Financial Services Government Agencies Are you a soft target?
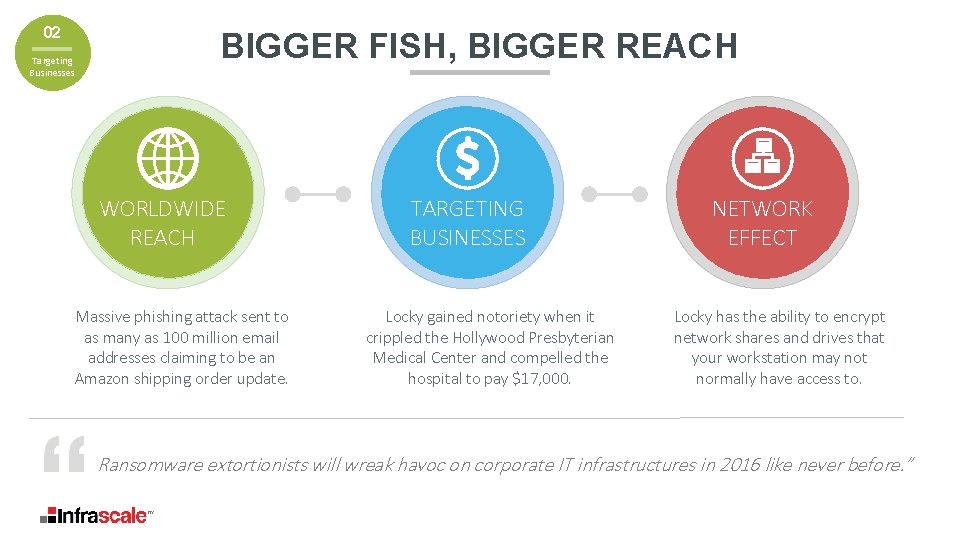
02 Targeting Businesses BIGGER FISH, BIGGER REACH WORLDWIDE REACH Massive phishing attack sent to as many as 100 million email addresses claiming to be an Amazon shipping order update. TARGETING BUSINESSES Locky gained notoriety when it crippled the Hollywood Presbyterian Medical Center and compelled the hospital to pay $17, 000. NETWORK EFFECT Locky has the ability to encrypt network shares and drives that your workstation may not normally have access to. Ransomware extortionists will wreak havoc on corporate IT infrastructures in 2016 like never before. ”
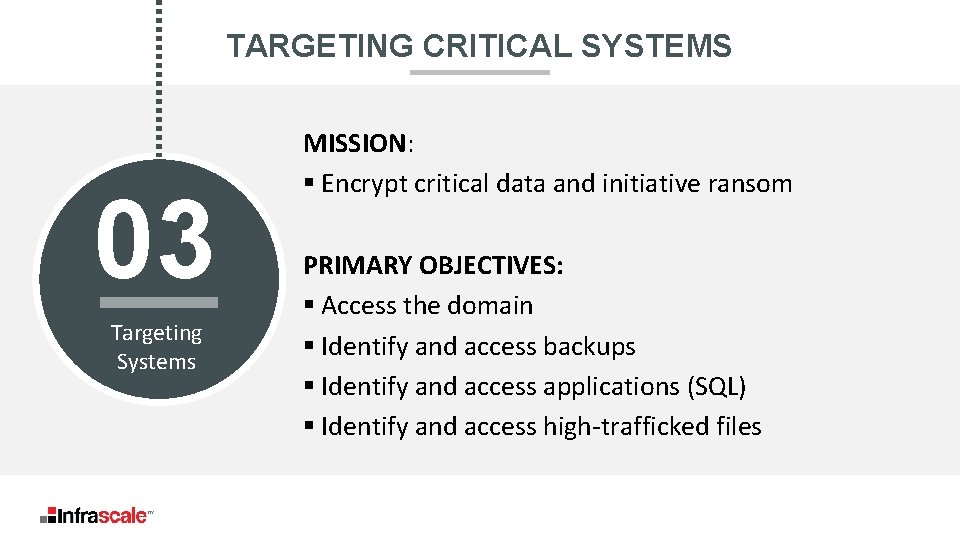
TARGETING CRITICAL SYSTEMS 03 Targeting Systems MISSION: § Encrypt critical data and initiative ransom PRIMARY OBJECTIVES: § Access the domain § Identify and access backups § Identify and access applications (SQL) § Identify and access high-trafficked files

03 Targeting Systems HOW RANSOMWARE ATTACKS END USER ADMIN Critical Applications & Network Backups
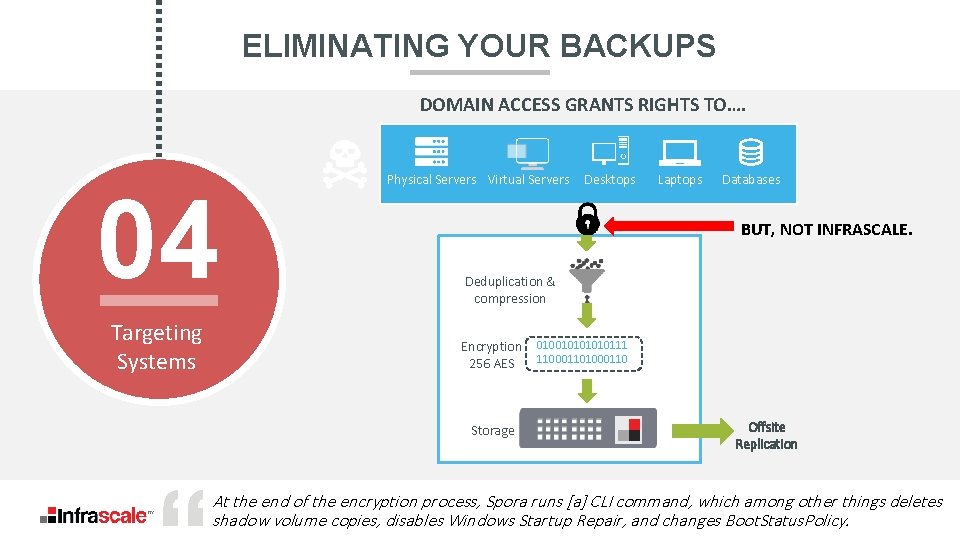
ELIMINATING YOUR BACKUPS DOMAIN ACCESS GRANTS RIGHTS TO…. 04 Targeting Systems Physical Servers Virtual Servers Desktops Laptops Databases BUT, NOT INFRASCALE. Deduplication & compression Encryption 256 AES Storage 01001010111 11000110 Offsite Replication At the end of the encryption process, Spora runs [a] CLI command, which among other things deletes shadow volume copies, disables Windows Startup Repair, and changes Boot. Status. Policy.
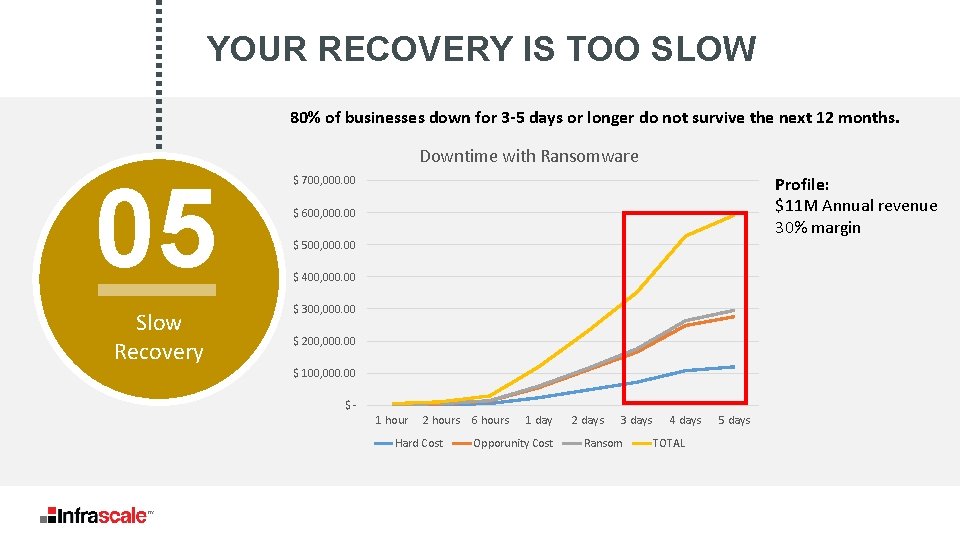
YOUR RECOVERY IS TOO SLOW 80% of businesses down for 3 -5 days or longer do not survive the next 12 months. Downtime with Ransomware 05 $ 700, 000. 00 Slow Recovery $ 300, 000. 00 Profile: $11 M Annual revenue 30% margin $ 600, 000. 00 $ 500, 000. 00 $ 400, 000. 00 $ 200, 000. 00 $ 100, 000. 00 $1 hour 2 hours Hard Cost 6 hours 1 day Opporunity Cost 2 days 3 days Ransom 4 days TOTAL 5 days
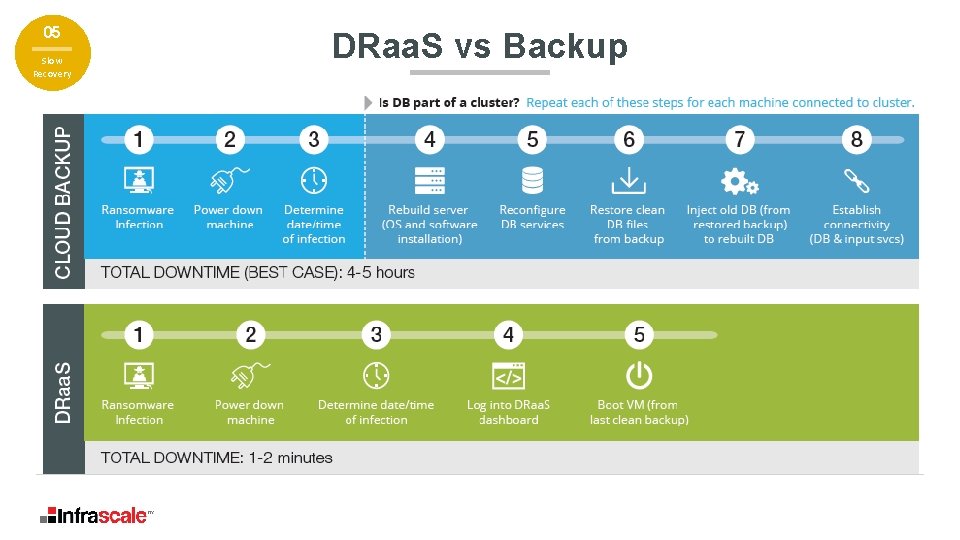
05 Slow Recovery DRaa. S vs Backup
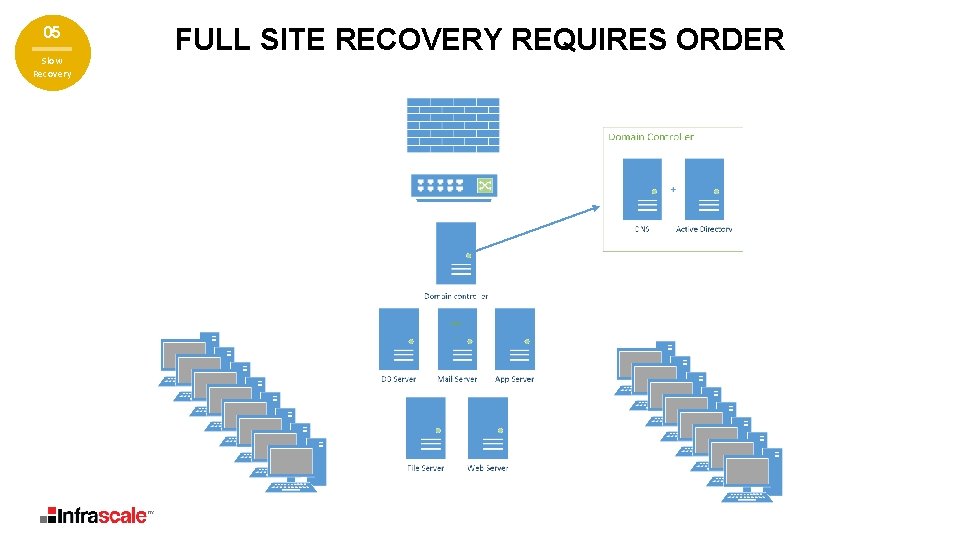
05 Slow Recovery FULL SITE RECOVERY REQUIRES ORDER
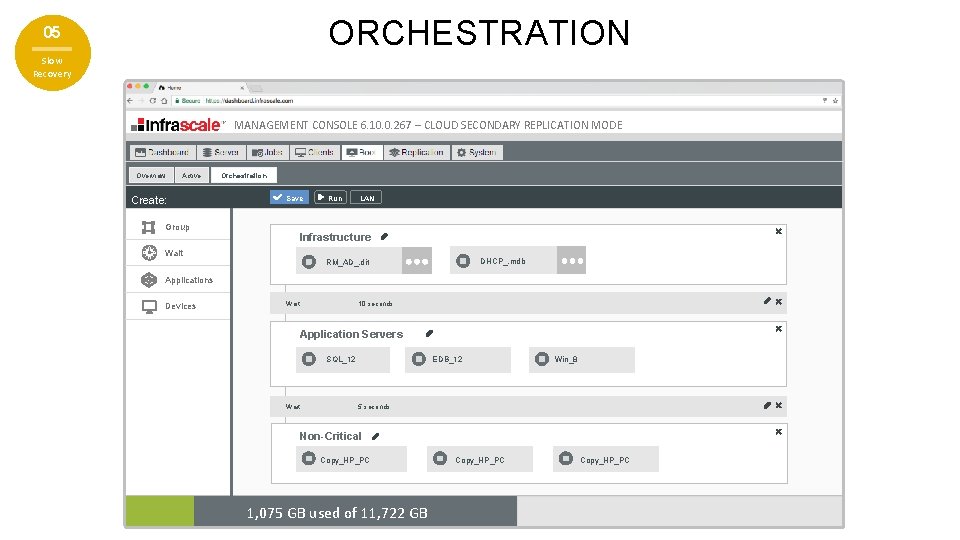
ORCHESTRATION 05 Slow Recovery MANAGEMENT CONSOLE 6. 10. 0. 267 – CLOUD SECONDARY REPLICATION MODE Overview Active Create: Group Orchestration Save Run LAN Infrastructure Wait DHCP_. mdb RM_AD_. dit Applications Devices Wait: 10 seconds Application Servers SQL_12 Wait: EDB_12 Win_8 5 seconds Non-Critical Copy_HP_PC 1, 075 GB used of 11, 722 GB Copy_HP_PC
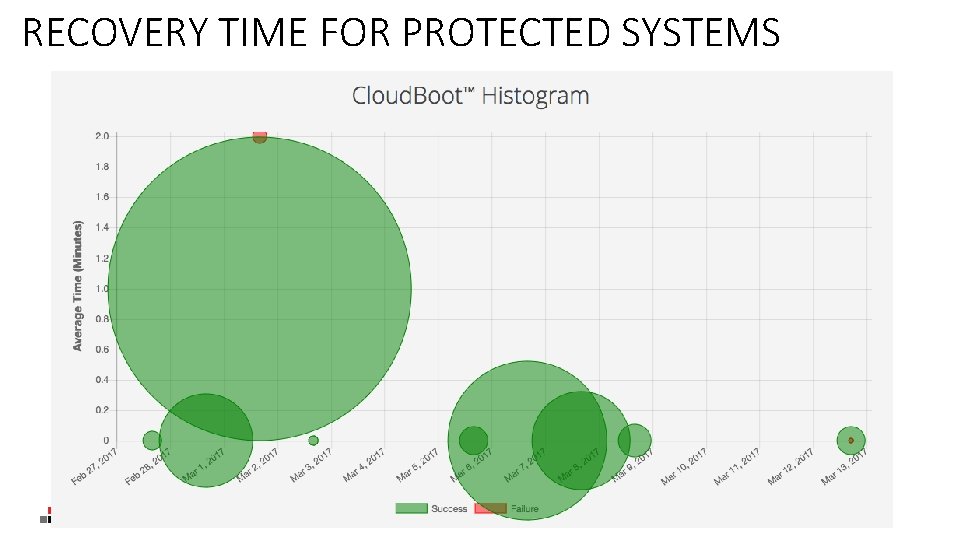
RECOVERY TIME FOR PROTECTED SYSTEMS
POLL If ransomware hit your business today, would you be prepared? A No. B Close, but no cigar. C Yes.
I never figured out the fuss over ransomware…The single most important thing any company or individual can do to improve security is have a good backup strategy. It’s been true for decades, and it’s still true today. -Security Guru, Bruce Schneier
OUR SOLUTION INFRASCALE GUARANTEES SYSTEM FAILOVER FROM ANY DISASTER IN 15 MINS OR LESS AT A FRACTION OF THE COST.
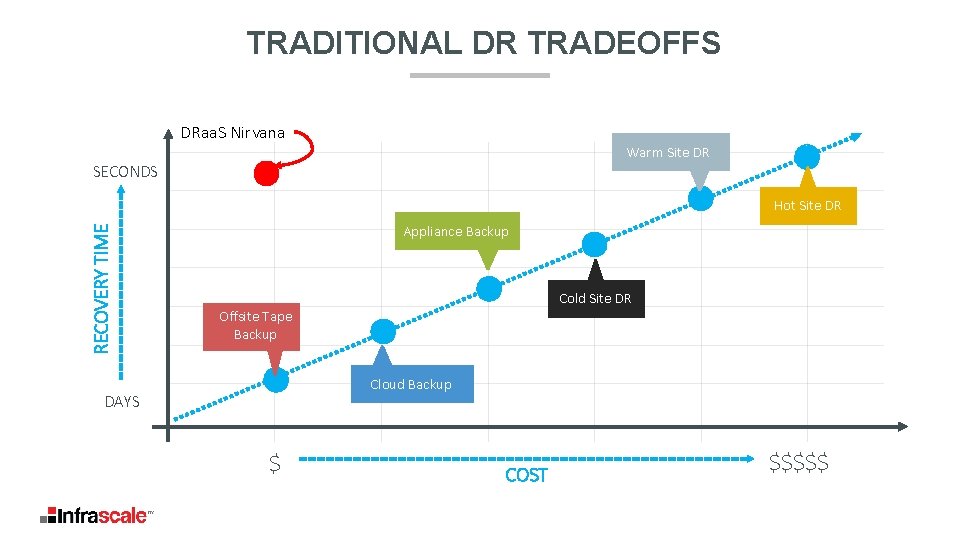
TRADITIONAL DR TRADEOFFS DRaa. S Nirvana Warm Site DR SECONDS RECOVERY TIME Hot Site DR Appliance Backup Cold Site DR Offsite Tape Backup Cloud Backup DAYS $ COST $$$$$
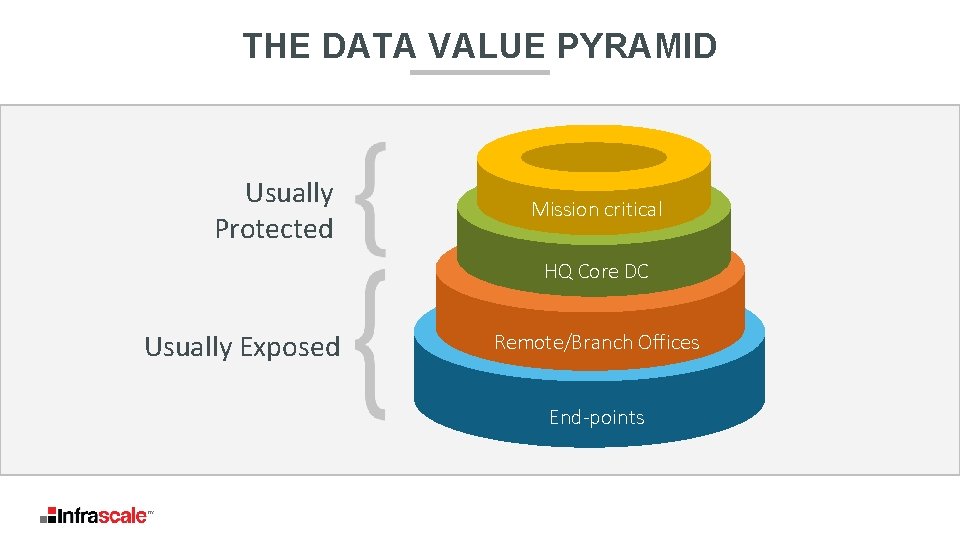
THE DATA VALUE PYRAMID Usually Protected Mission critical HQ Core DC Usually Exposed Remote/Branch Offices End-points
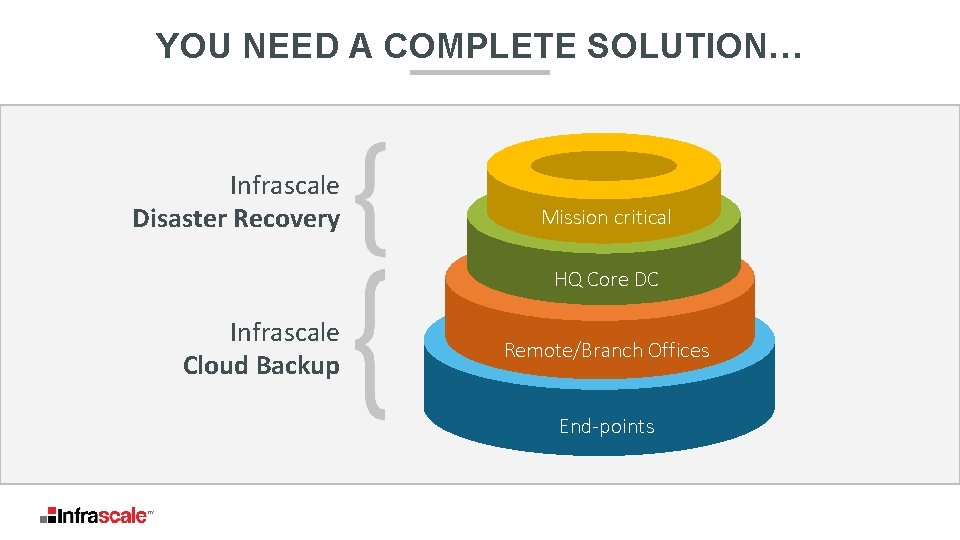
YOU NEED A COMPLETE SOLUTION… Infrascale Disaster Recovery Mission critical HQ Core DC Infrascale Cloud Backup Remote/Branch Offices End-points
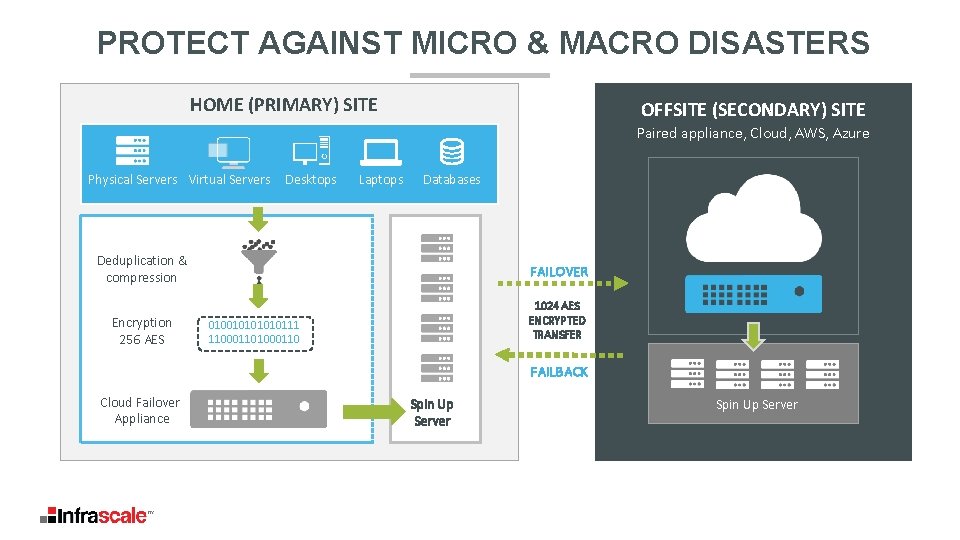
PROTECT AGAINST MICRO & MACRO DISASTERS HOME (PRIMARY) SITE OFFSITE (SECONDARY) SITE Paired appliance, Cloud, AWS, Azure Physical Servers Virtual Servers Desktops Laptops Databases Deduplication & compression FAILOVER Encryption 256 AES 1024 AES ENCRYPTED TRANSFER 01001010111 11000110 FAILBACK Cloud Failover Appliance Spin Up Server
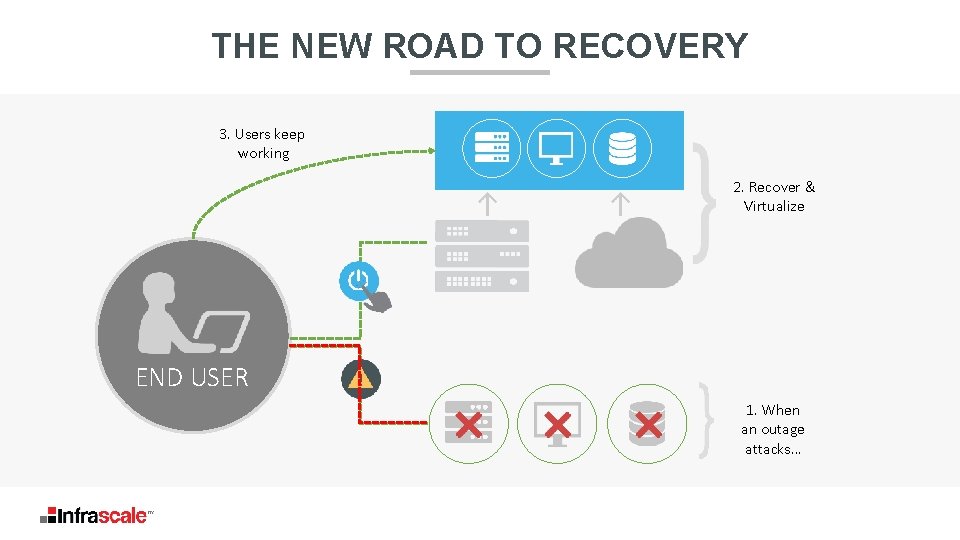
THE NEW ROAD TO RECOVERY 3. Users keep working 2. Recover & Virtualize END USER 1. When an outage attacks…
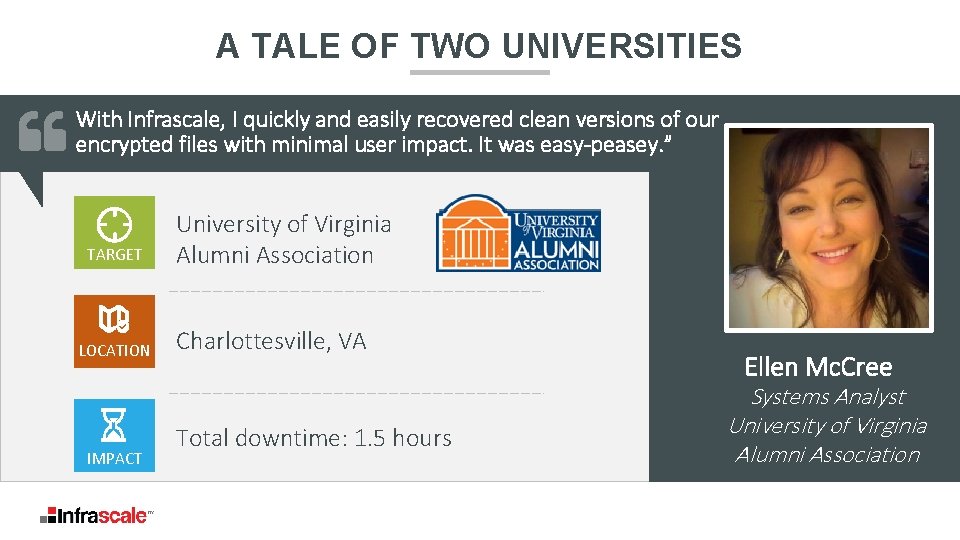
A TALE OF TWO UNIVERSITIES With Infrascale, I quickly and easily recovered clean versions of our encrypted files with minimal user impact. It was easy-peasey. ” TARGET LOCATION IMPACT University of Virginia Alumni Association Charlottesville, VA Total downtime: 1. 5 hours Ellen Mc. Cree Systems Analyst University of Virginia Alumni Association
POLL Would you like to be contacted about our free evaluation? A Yes B No C Yes, but not right away
CALL NOW ###-#### GET YOUR FREE EVALUATION 2 3 4 5 PROTECT YOUR BUDGET PROTECT ALL SYSTEMS PROTECT AGAINST MICRO & MACRO DISASTERS MULTI-LAYERED NETWORK SECURITY PROTECT AGAINST RANSOMWARE 4 1
- Slides: 37