4 Basic Dynamic Analysis Malware Analysis 1 What
4. Basic Dynamic Analysis Malware Analysis 1
What is Basic Dynamic Analysis? o Allowing the malware to run - executing the program binary o It complements static analysis o Makes analysis more efficient in some cases o Helps us understand the program behavior 2
Various Types of Malware Analysis o Basic Static Analysis o Examining target binary without execution (i. e. , strings, hashing, signature) o Advanced Static Analysis o Understanding target binary using reverse engineering (i. e. , disassembly) o Basic Dynamic Analysis o Executing target binary and observing its behavior o Advanced Dynamic Analysis o Executing target binary and using a debugger to analyze internal state 3
Basic Dynamic Analysis o Monitored execution of a program in order to perform analysis o Often performed after static analysis is done o Advantages o Efficient way to determine program functionality o Able to check file activity, process creation, network activity, etc. o Disadvantage o Not all functional paths may be explored 4
Executing the Malware o In most cases, you can just double-click the “exe” file ◦ You may want to run it from the command-line as well (Why? ) o o What if the extension is not “exe”? ◦ You can change it. Verify it is a PE file using a PE parser What if it is a DLL? ◦ You can run a DLL using the rundll 32 program ◦ Format: C: > rundll 32. exe <name>. dll 5
Sandboxes o What is Sandbox? o All-in-one software solutions to analyze the execution of a program o Provides security mechanism for running untrusted programs in a safe environment o Lets you monitor behavior/changes to the system o The “real” system remains isolated – so, it does not get infected 6
Sandboxes o Usually use virtual components o Simulates network services to allow program to execute as it ‘normally’ would o Sandboxes for Malware Analysis o There are many free and commercial versions available o Some online and some you can download o Lets you analyze a variety of file types: EXE, PDF, Office Documents, URLs, etc. 7
Sandboxes - Drawbacks o May run the EXE w/o command line arguments o EXE may wait for response from C 2 o Malware may find out that it is running in a sandbox o An anti-analysis technique o In that case, the malware may change its behavior o Often the environment is not properly setup 8
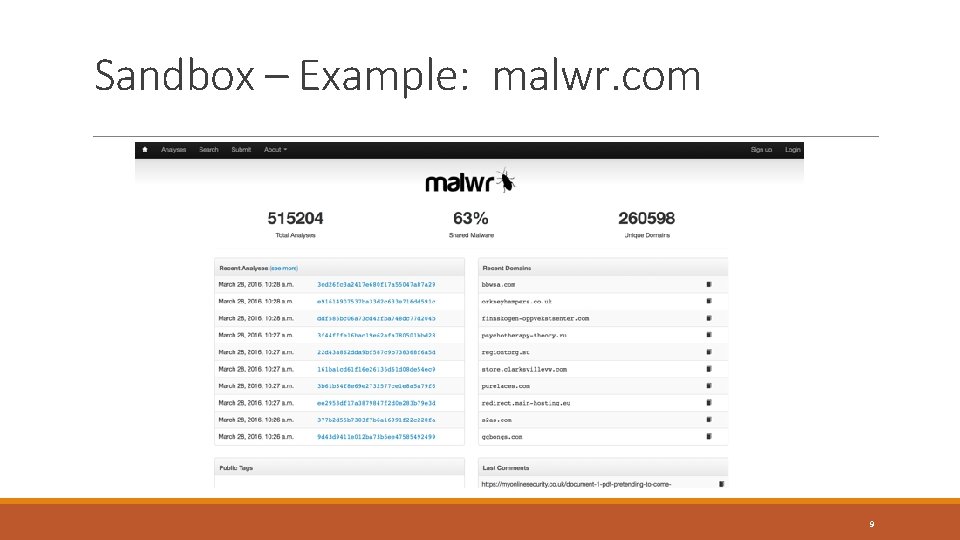
Sandbox – Example: malwr. com 9
Monitoring System Activity o Process Monitor (aka Proc. Mon) o Tool that allows monitoring of registry, file system, network, process, and thread activities o Not a reliable tool for network activities o So other tools need to be used o Monitors all system calls o Captures a lot of data (> 50, 000 events a minute) o Uses RAM to capture events o Can easily crash a VM - so, run for a limited amount of time 10
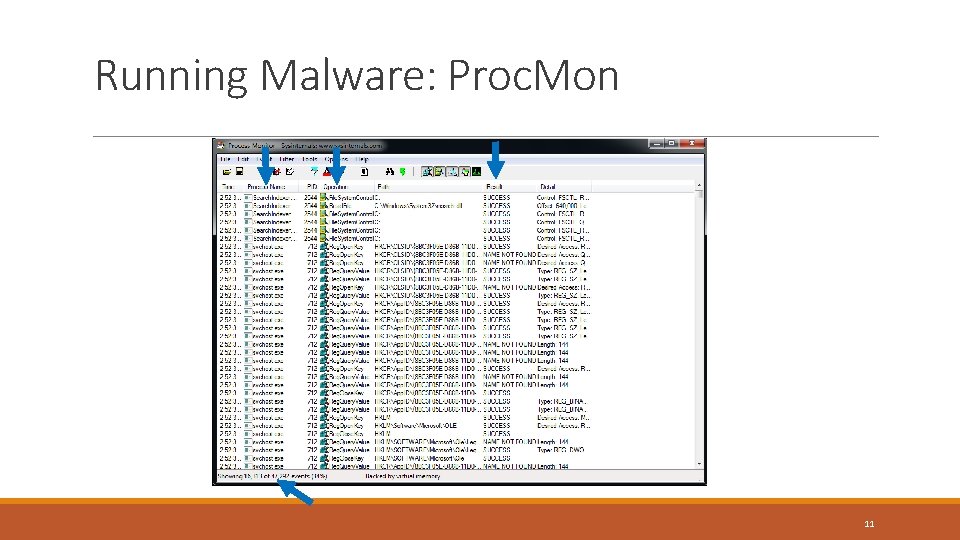
Running Malware: Proc. Mon 11
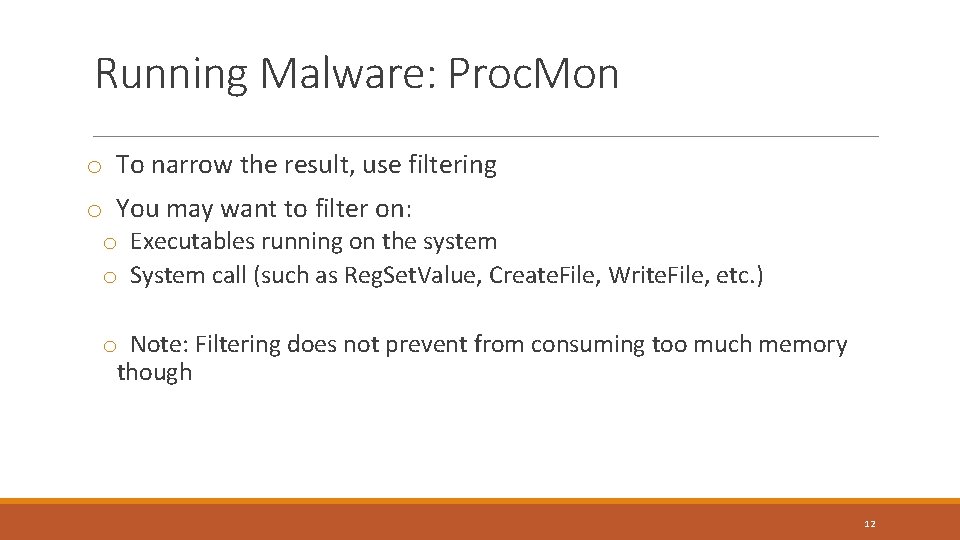
Running Malware: Proc. Mon o To narrow the result, use filtering o You may want to filter on: o Executables running on the system o System call (such as Reg. Set. Value, Create. File, Write. File, etc. ) o Note: Filtering does not prevent from consuming too much memory though 12
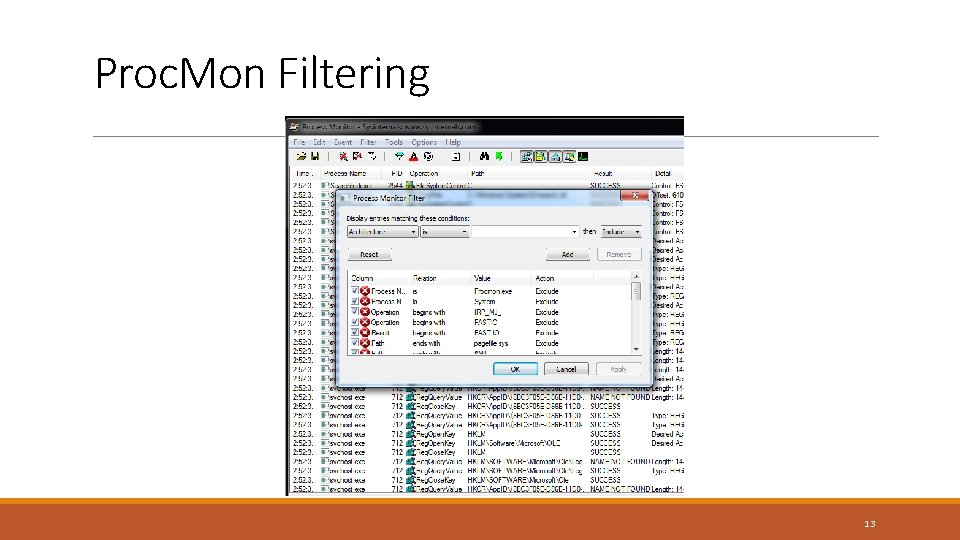
Proc. Mon Filtering 13
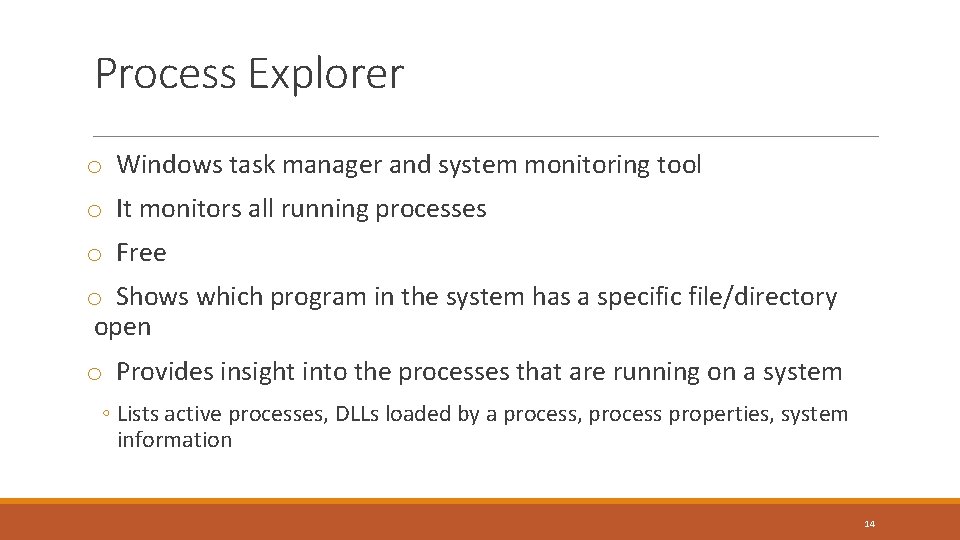
Process Explorer o Windows task manager and system monitoring tool o It monitors all running processes o Free o Shows which program in the system has a specific file/directory open o Provides insight into the processes that are running on a system ◦ Lists active processes, DLLs loaded by a process, process properties, system information 14
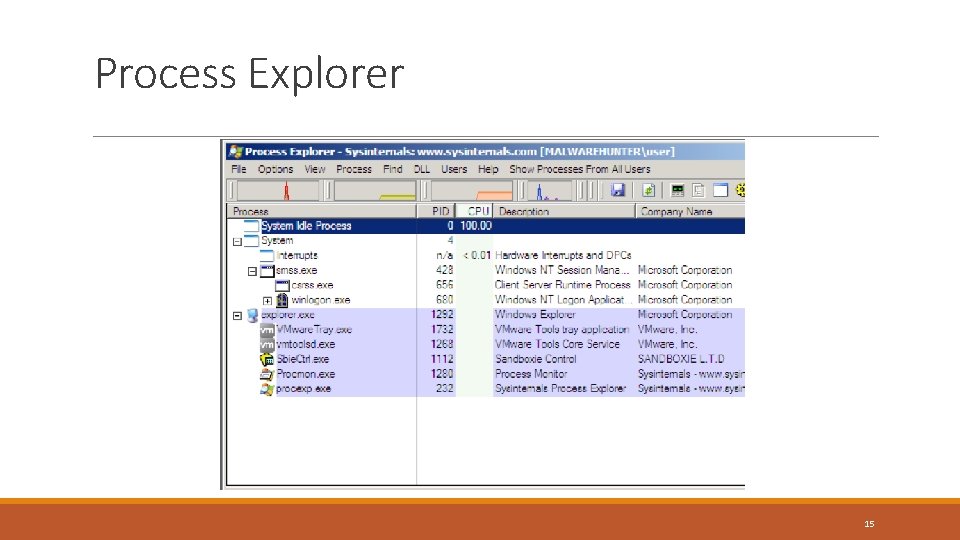
Process Explorer 15
Process Explorer Vs. Process Monitor o Process Explorer ◦ Shows current state of each process ◦ Shows files, registry keys and thread loaded by each running process o Process Monitor ◦ In addition to monitoring, it logs process information – all events ◦ Logs show the files, registry, network etc. the process attempted to use – successful or not ◦ “Access Denied” events also appear 16
Monitoring Network Activities o Why? o Most malware will need to communicate with external services/entities ◦ ◦ ◦ Download additional malware, files Exchange/obtain keys for encryption C 2 – Command Control: Receive instructions and check-in Extract data Infect other machines ◦ Question: Do we allow them access to network? 17
Faking a Network o It is too risky to allow a malware to access the network o Faking a network allows us to find out how/what is communicated o Important: Faking requires that the malware does not realize it is executing on a virtualized environment 18
Faking a Network - Apate. DNS o Apate. DNS is a Free tool from Mandiant/Fire-Eye o Allows to control DNS responses though GUI o It listens on UDP port 53 on the local machine o Spoofs DNS responses to a user-specified IP address o One of the quickest and easiest ways to see DNS requests made on the system o It redirects all requests though o Typically redirects to localhost. But, you can also redirect to other IPs 19
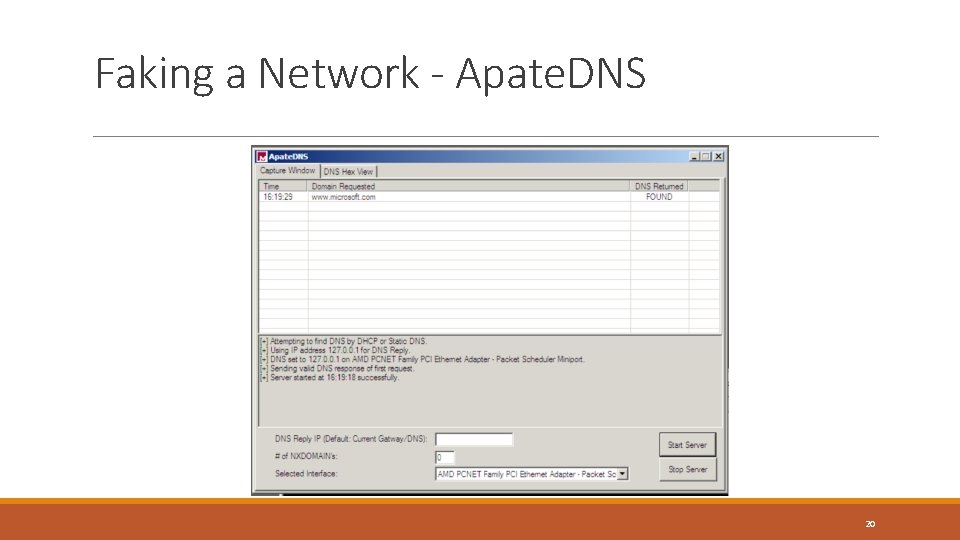
Faking a Network - Apate. DNS 20
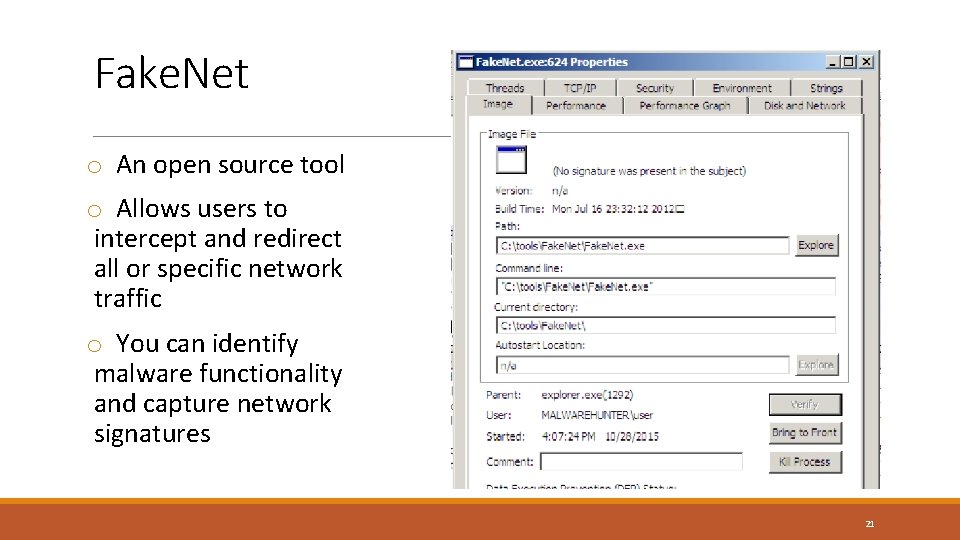
Fake. Net o An open source tool o Allows users to intercept and redirect all or specific network traffic o You can identify malware functionality and capture network signatures 21
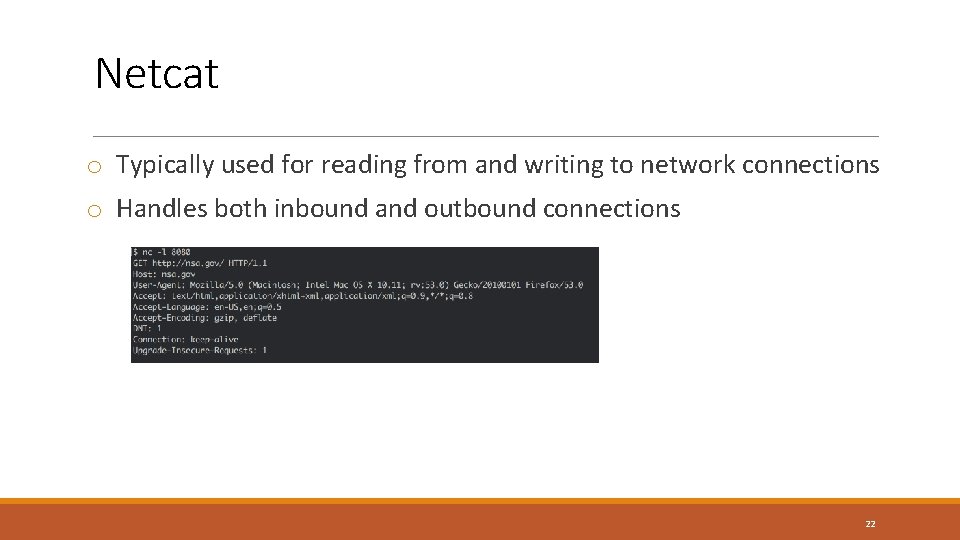
Netcat o Typically used for reading from and writing to network connections o Handles both inbound and outbound connections 22
- Slides: 22