BIOMETRICS AND NETWORK AUTHENTICATION Security Innovators Identification Methods

BIOMETRICS AND NETWORK AUTHENTICATION Security Innovators
Identification Methods n Traditional identification n Something that you have n n Something that you know n n Entrance permit, key User-id and password, PIN Problems n n Unauthorized person takes control of these traditional identification Difficult to remember password and PIN
Secure Authentication n In a PKI world: n n n Cryptographic key pair (private and public key) If someone gains access to the password that secures the cryptographic keys, he also gains access to every cryptographically protected application. Solution n Something that you are n Biometric
What is Biometrics? n n Biometric technology uses a physical or psychological trait for identification and authentication Key properties: n n Universal - common characteristic Unique - no two persons is the same in term of characteristic Permanent - time invariant Collectable - quantitatively measurable
Why Biometrics? n Enhance security n n n Convenient n n "Who you claim to be" NOT "what you know" Fast, easy-to-use, reliable, and less expensive authentication Avoid n n Lost, stolen, duplicated, or left at home Forgotten, shared, or observed
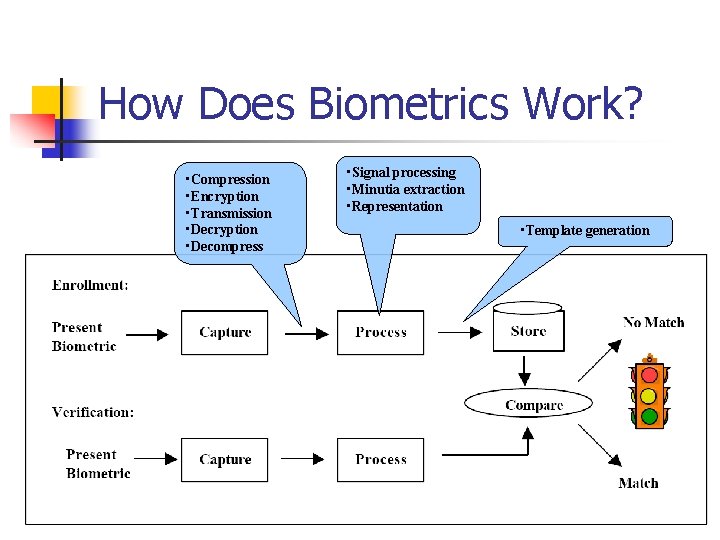
How Does Biometrics Work? • Compression • Encryption • Transmission • Decryption • Decompress • Signal processing • Minutia extraction • Representation • Template generation
If Match… n Smart card data converted into a number n n Used as a symmetric cryptographic key to decrypt the private key A nonce passed from the computer application to smart card Private key on smart card encrypted nonce. The application verifies: n n certified public key obtained from the networkbased directory service decrypt the encrypted message from the card
Types of Biometrics n n n n Fingerprint Face Pattern Voice Pattern Retina Identification Hand DNA Signature Etc…
Fingerprint n Reasons to use n n n Possible Attack n n n 100 to 600 bytes of data size can easily be fitted into the smart cards It cannot be easily reproduced from the templates Surgery to alter print Latex finger Solution n n Monitor pulse, sweat, temperature and more Best solution: Measure the amount of oxygenated hemoglobin in the blood
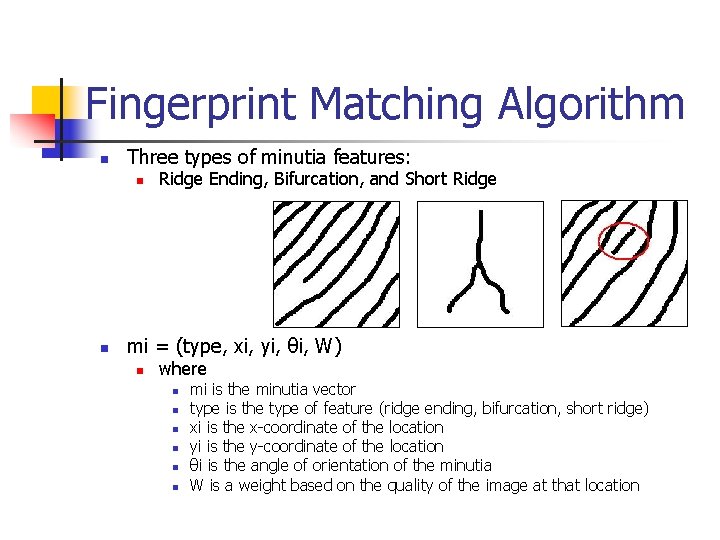
Fingerprint Matching Algorithm n Three types of minutia features: n n Ridge Ending, Bifurcation, and Short Ridge mi = (type, xi, yi, θi, W) n where n n n mi is the minutia vector type is the type of feature (ridge ending, bifurcation, short ridge) xi is the x-coordinate of the location yi is the y-coordinate of the location θi is the angle of orientation of the minutia W is a weight based on the quality of the image at that location
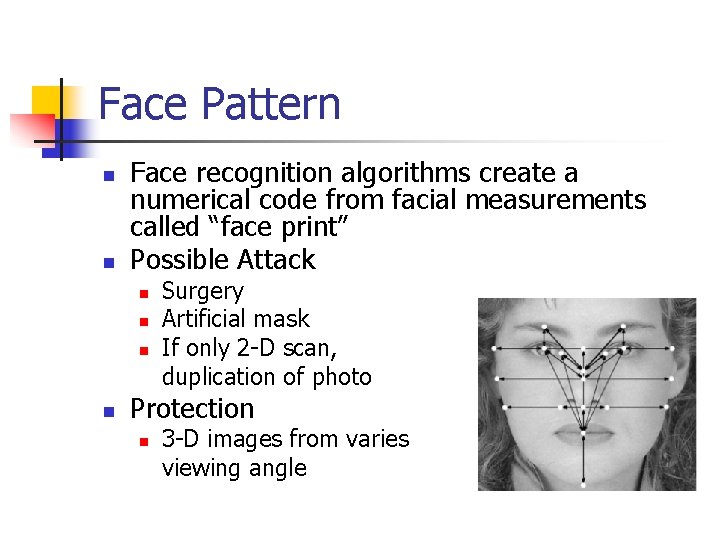
Face Pattern n n Face recognition algorithms create a numerical code from facial measurements called “face print” Possible Attack n n Surgery Artificial mask If only 2 -D scan, duplication of photo Protection n 3 -D images from varies viewing angle
Retina Identification n Based on the unique configuration of blood vessels 360 degree circular scan in the retina Most accurate Possible attack n n Surgery prosthetic eye
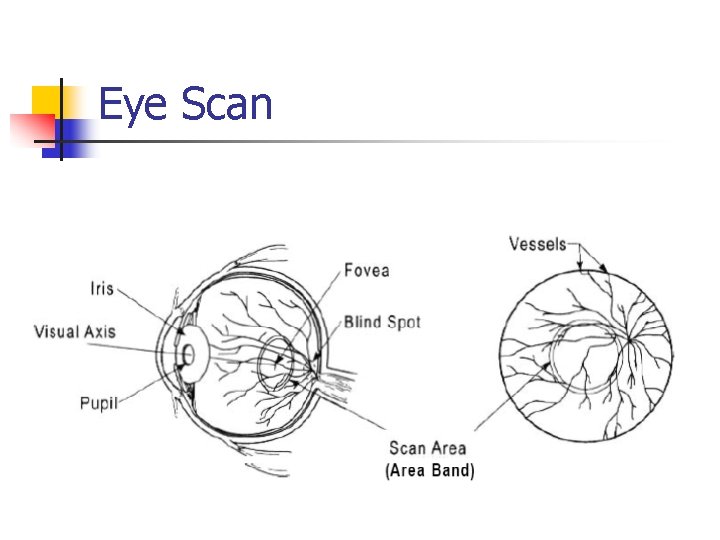
Eye Scan
Voice Pattern n n Automatic speaker recognition and verification system Possible attack n n DAT voice recording Sound-alike voice
How Biometrics Applies to Network Security? n Authentication n n Biometrics technology replace Username and Password Can be used on n n n n Workstation and network access Single sign-on Application logon Data Protection Remote access to resources Transaction security Web security Encrypt sensitive data transmitted over the internet
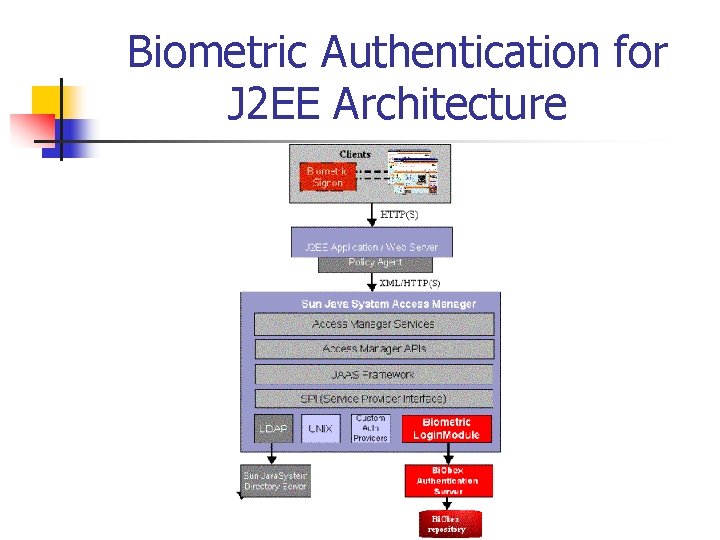
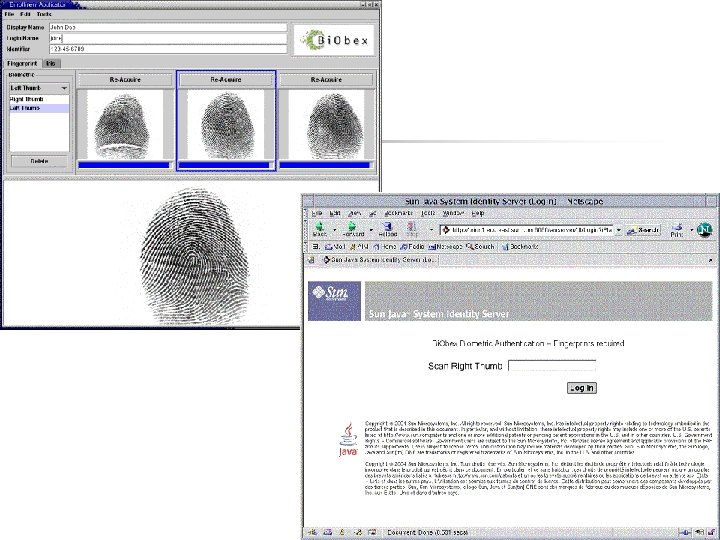
Biometric Authentication for J 2 EE Architecture
Issues and Concerns n Accuracy n n n n False acceptance rate (FAR) and False Rejection Rate (FRR) Tradeoff between security and convenience Stability Suitability Difficulty of usage Availability Comparison failure
Summary n n Biometric is one more layer on top of PIN, physical token, and it makes them more secure Highest level of security is the combination of: n n n Something you know Something you have Something you are
![Reference n n [1] David Corcoran, "Smart Cards and Biometrics: Your Key to PKI” Reference n n [1] David Corcoran, "Smart Cards and Biometrics: Your Key to PKI”](http://slidetodoc.com/presentation_image_h2/fd74ca117132480b8e79dab931aeb837/image-20.jpg)
Reference n n [1] David Corcoran, "Smart Cards and Biometrics: Your Key to PKI” [2] Paul Reid, “Biometrics for Network Security, ” Prentice Hall PTR, December 30, 2003. [3] “Smart Cards and Biometrics in Privacy-Sensitive Secure Personal Identification Systems, ” A Smart Card Alliance White Paper, May 2002. [4] Anil Jain, “BIOMETRICS Personal Identification in Networked Society, ” Kluwer Academic Publishers, 2002
- Slides: 20