A warfare inspired optimization algorithm the Find FixFinishExploitAnalyze

- Slides: 21
A warfare inspired optimization algorithm: the Find. Fix-Finish-Exploit-Analyze (F 3 EA) metaheuristic Dr. Ali Husseinzadeh Kashan Prof. Reza Tavakkoli Mogaddam Prof. Mitsuo Gen
Introduction • Since the 1970 s that the idea of a general algorithmic framework, which can be applied with relatively few modifications to different optimization problems, emerged. • Metaheuristics: methods that combine rules and randomness while imitating natural phenomena. • These methods are from now on regularly employed in all the sectors of business, industry, engineering. • Besides all of the interest necessary to application of metaheuristics, occasionally a new metaheuristic algorithm is introduced that uses a novel metaphor as guide for solving optimization problems. 2
Some example • particle swarm optimization algorithm (PSO): models the flocking behavior of birds; • harmony search (HS): models the musical process of searching for a perfect state of harmony; • bacterial foraging optimization algorithm (BFOA): models foraging as an optimization process where an animal seeks to maximize energy per unit time spent foraging; • artificial bee colony (ABC): models the intelligent behavior of honey bee swarms; • League Championship algorithm (LCA): tries to mimic a championship environment wherein artificial teams play in an artificial league for several weeks • fire fly algorithm (FA): performs based on the idealization of the flashing characteristics of fireflies. • Optics Inspired Optimization (OIO): performs based on the rationale of optical characteristics of concave and convex mirrors. 3
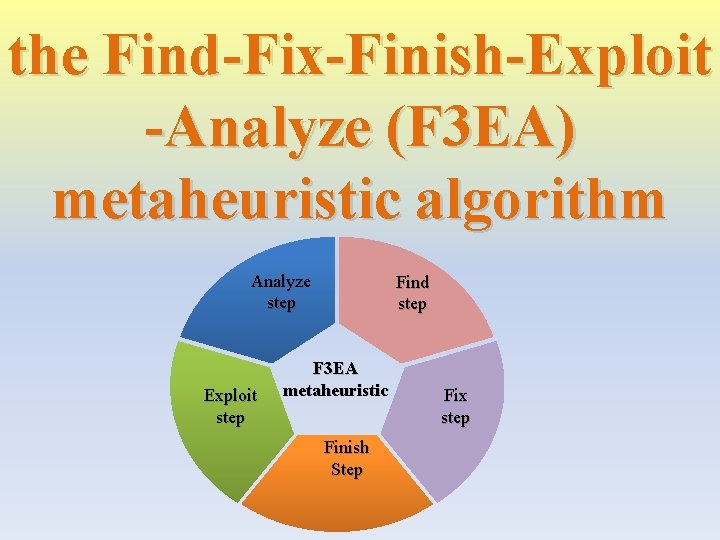
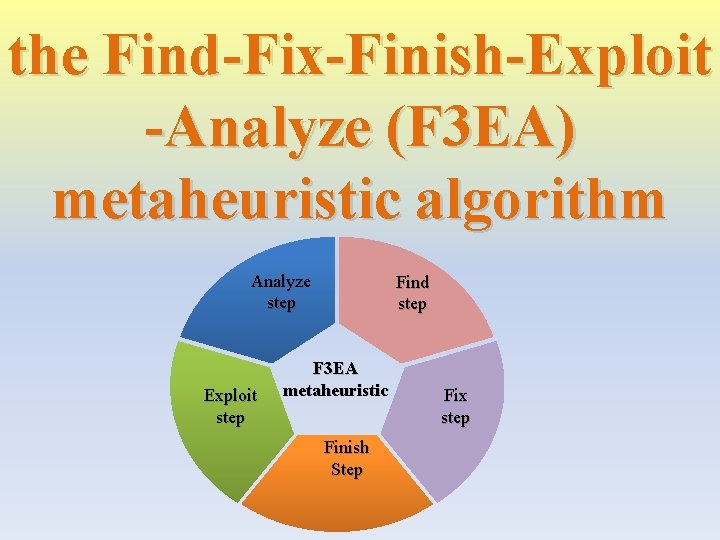
the Find-Fix-Finish-Exploit -Analyze (F 3 EA) metaheuristic algorithm Analyze step Exploit step Find step F 3 EA metaheuristic Finish Step Fix step
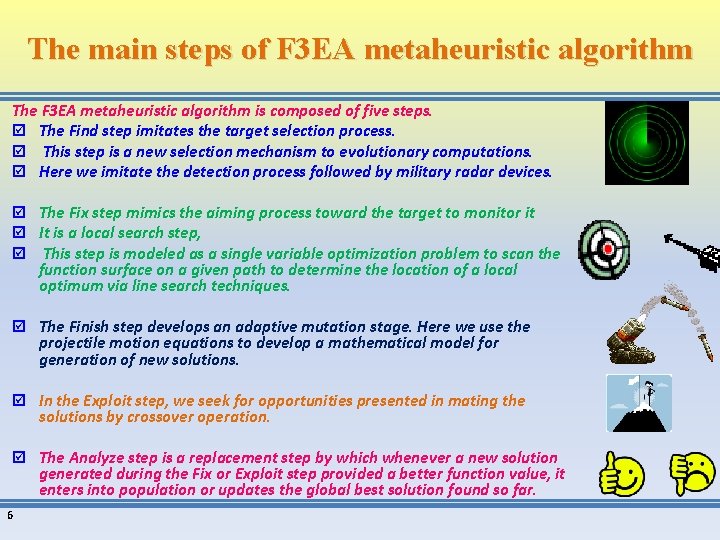
The F 3 EA targeting process as a source of inspiration for F 3 EA metaheuristic algorithm In 2014 General S. A. Mc. Chrystal wrote about the “F 3 EA” targeting cycle which had been, used in the Afghanistan and Iraq wars. Find: the process through which targets (i. e. , person or location) are identified. Fix: the process that allows the prepared targets to be monitored in preparation for action. Finish: the process by which targets are actioned, killed or destroyed. Exploit: the process by which opportunities presented by the target effect are identified (target site exploitation, gathering information from the target area, battle damage assessment) Analyze: is an assessment phase that pertains to the results of attacks on targets. The F 3 EA metaheuristic algorithm specifically mimics the targeting process 5
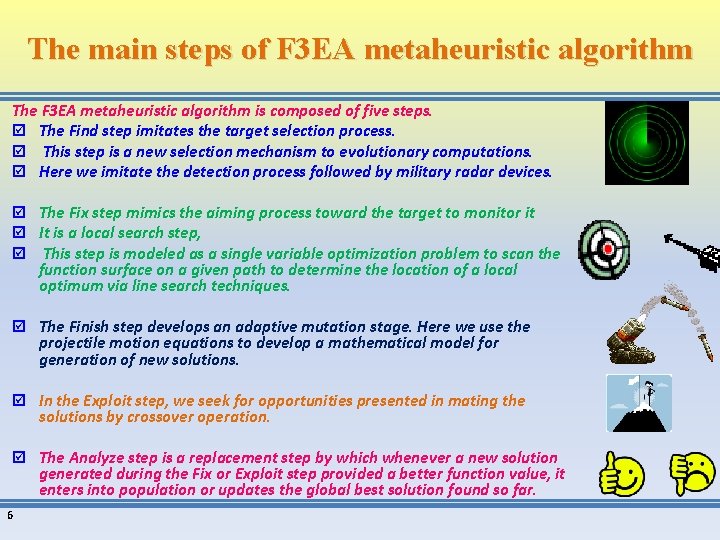
The main steps of F 3 EA metaheuristic algorithm The F 3 EA metaheuristic algorithm is composed of five steps. þ The Find step imitates the target selection process. þ This step is a new selection mechanism to evolutionary computations. þ Here we imitate the detection process followed by military radar devices. þ The Fix step mimics the aiming process toward the target to monitor it þ It is a local search step, þ This step is modeled as a single variable optimization problem to scan the function surface on a given path to determine the location of a local optimum via line search techniques. þ The Finish step develops an adaptive mutation stage. Here we use the projectile motion equations to develop a mathematical model for generation of new solutions. þ In the Exploit step, we seek for opportunities presented in mating the solutions by crossover operation. þ The Analyze step is a replacement step by which whenever a new solution generated during the Fix or Exploit step provided a better function value, it enters into population or updates the global best solution found so far. 6
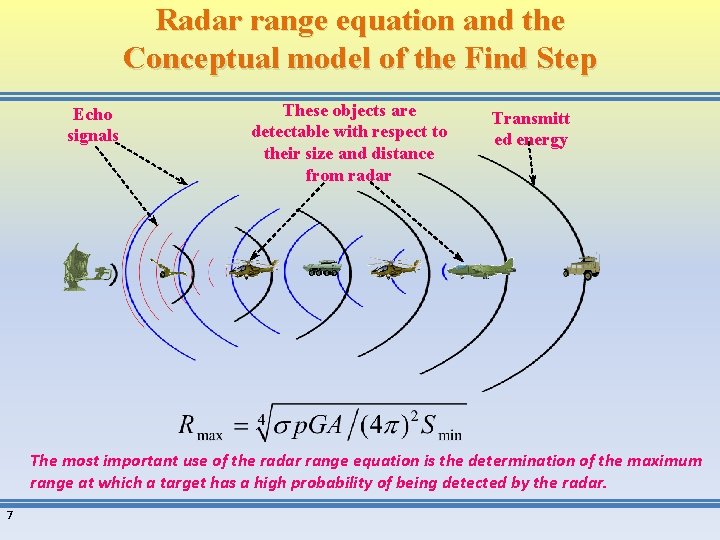
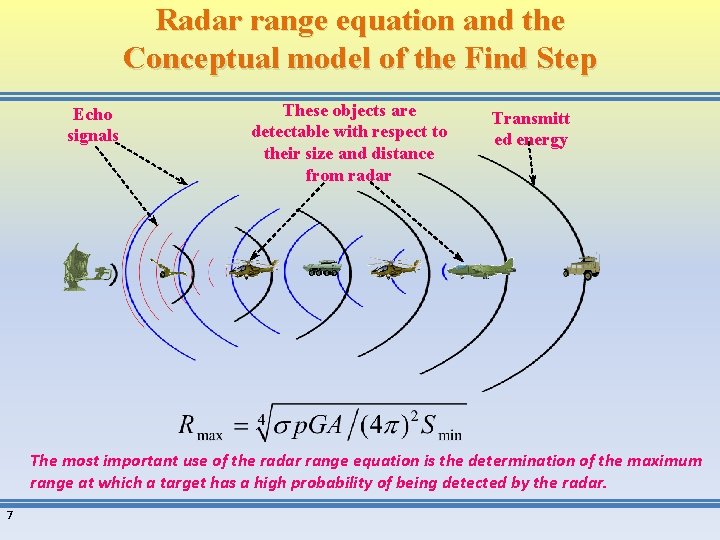
Radar range equation and the Conceptual model of the Find Step Echo signals These objects are detectable with respect to their size and distance from radar Transmitt ed energy The most important use of the radar range equation is the determination of the maximum range at which a target has a high probability of being detected by the radar. 7
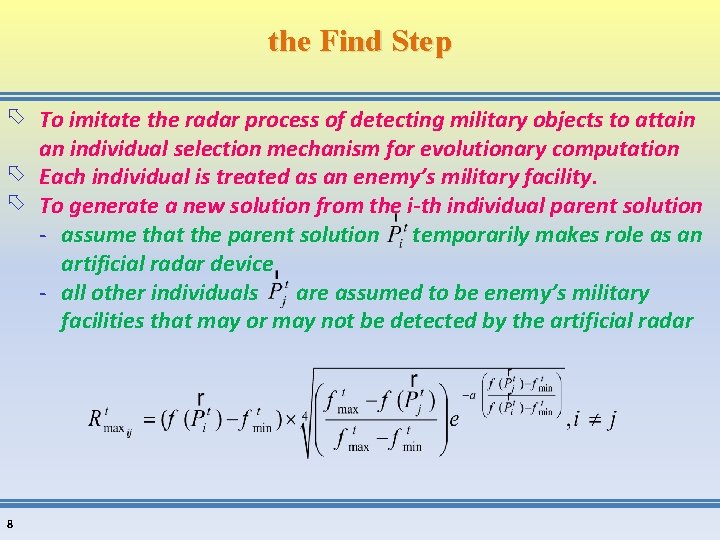
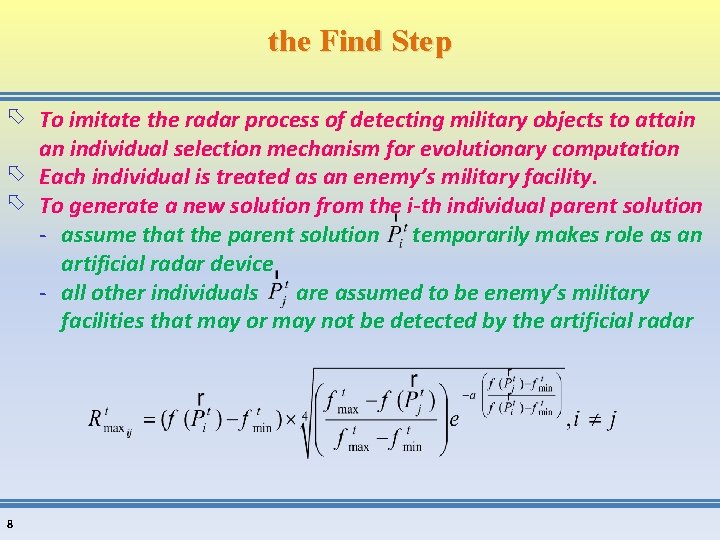
the Find Step To imitate the radar process of detecting military objects to attain an individual selection mechanism for evolutionary computation Each individual is treated as an enemy’s military facility. To generate a new solution from the i-th individual parent solution - assume that the parent solution temporarily makes role as an artificial radar device - all other individuals are assumed to be enemy’s military facilities that may or may not be detected by the artificial radar 8
the Find Step Among all detectable individuals by , one can be selected based on any logic to generate a new solution in the so-called Finish step of the F 3 EA algorithm. 9
The Finish step During this step, an artificial rocket is launched from towards and the explosion position which is determined via the projectile motion equations, forms a new solution in the domain. To develop the model of the Finish step, we need to assume that: - The artificial rocket is a time bomb which will be exploded a certain duration after its launch. - Neglecting the air or wind drag, the explosion time is equal to theoretic rocket’s time of fight. - When the rocket is launched, it is subjected to an air drag force. Wind also blows which produces a force. 10
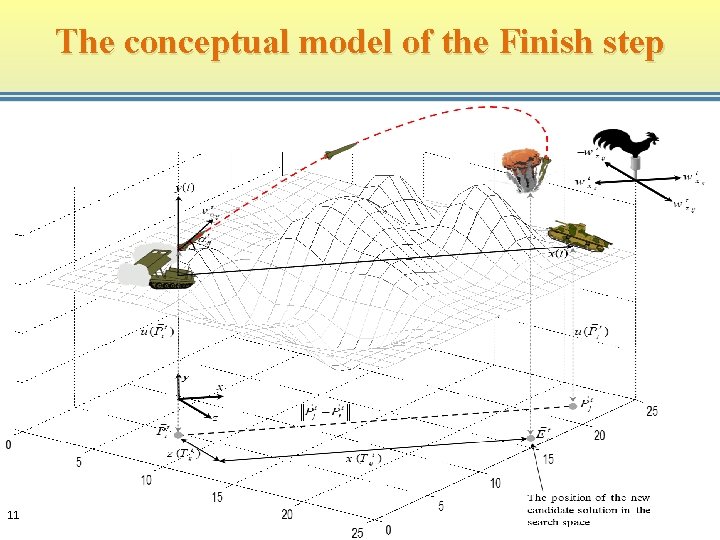
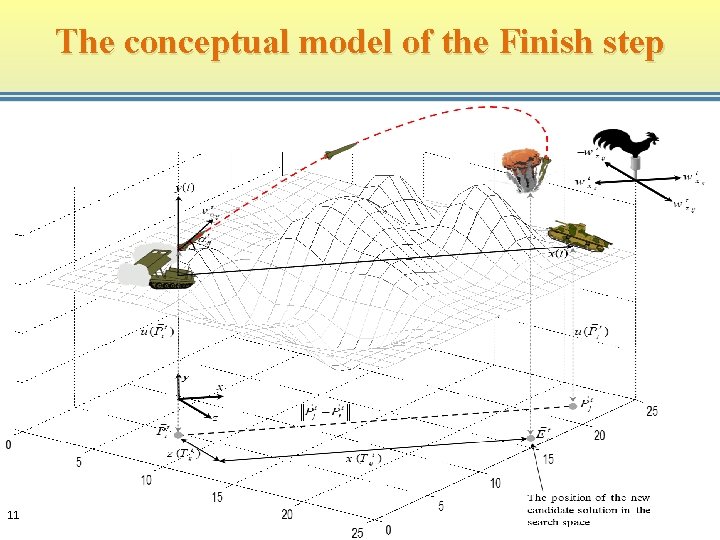
The conceptual model of the Finish step 11
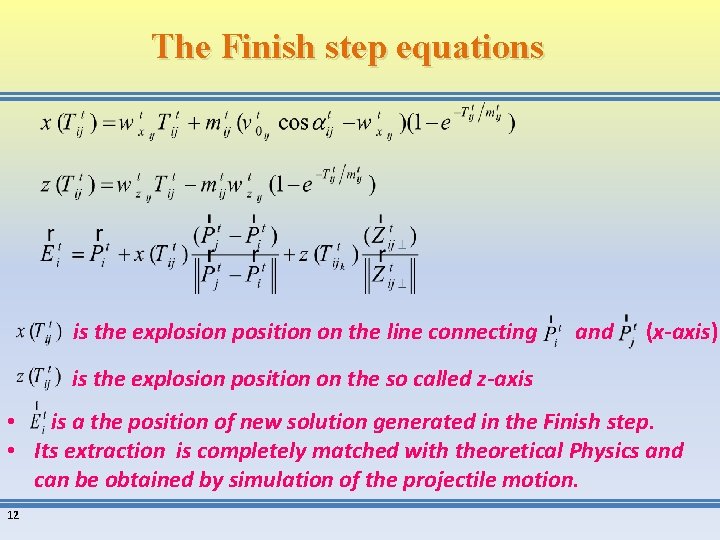
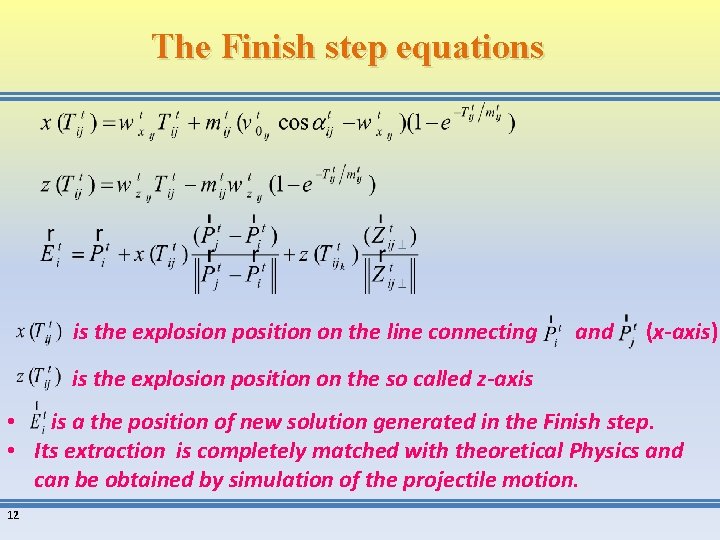
The Finish step equations is the explosion position on the line connecting and (x-axis) is the explosion position on the so called z-axis • is a the position of new solution generated in the Finish step. • Its extraction is completely matched with theoretical Physics and can be obtained by simulation of the projectile motion. 12
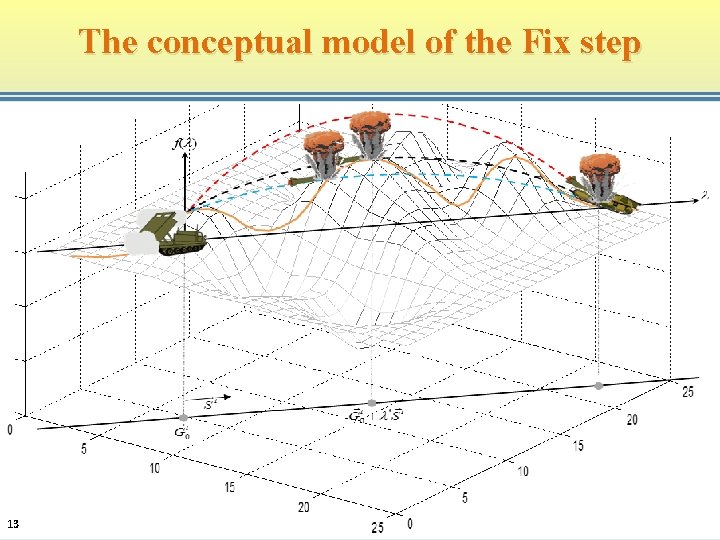
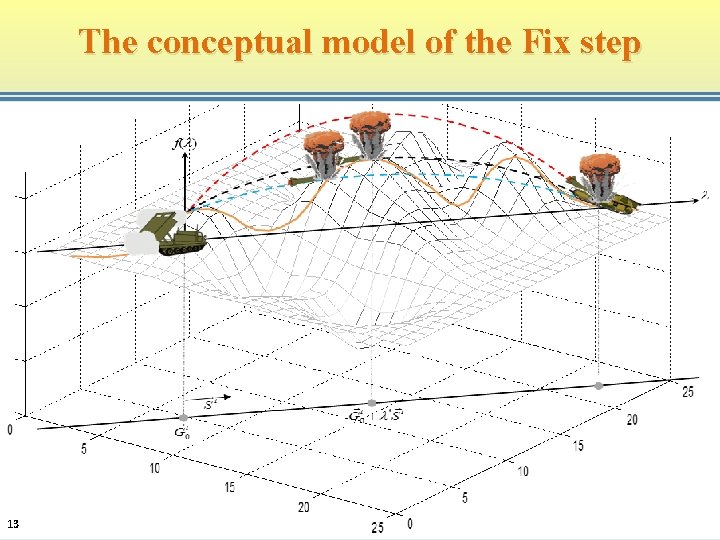
The conceptual model of the Fix step 13
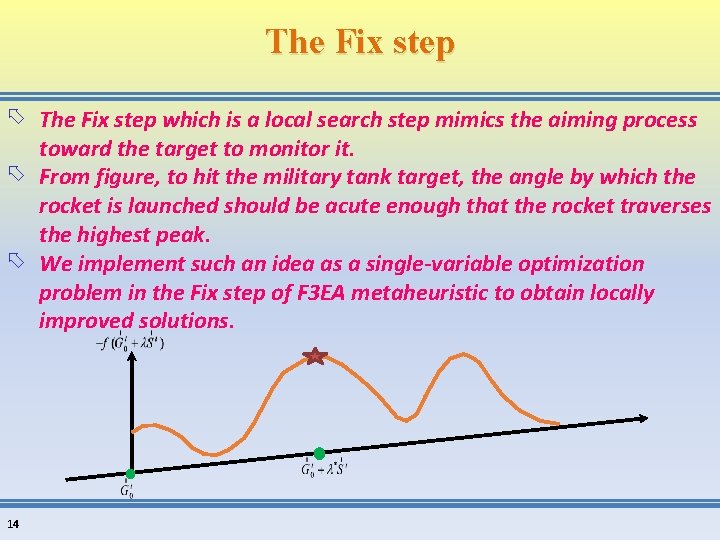
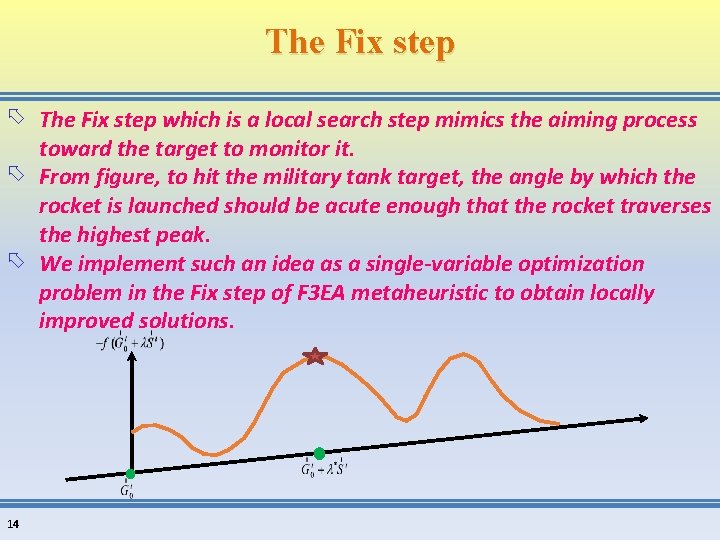
The Fix step which is a local search step mimics the aiming process toward the target to monitor it. From figure, to hit the military tank target, the angle by which the rocket is launched should be acute enough that the rocket traverses the highest peak. We implement such an idea as a single-variable optimization problem in the Fix step of F 3 EA metaheuristic to obtain locally improved solutions. 14
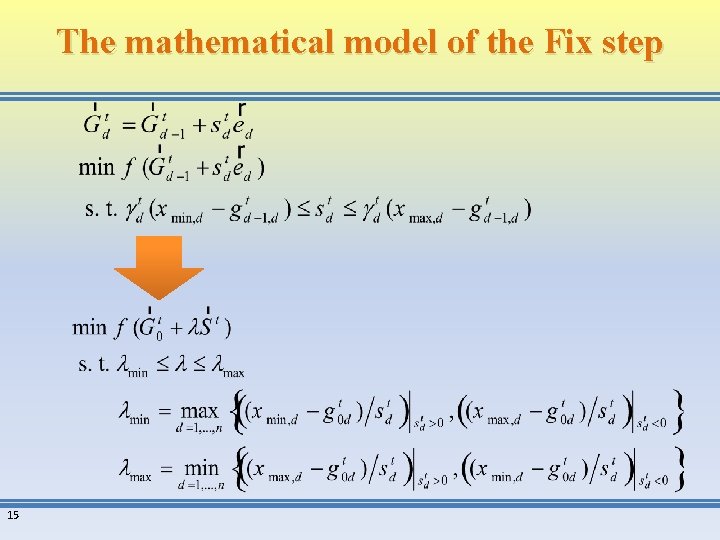
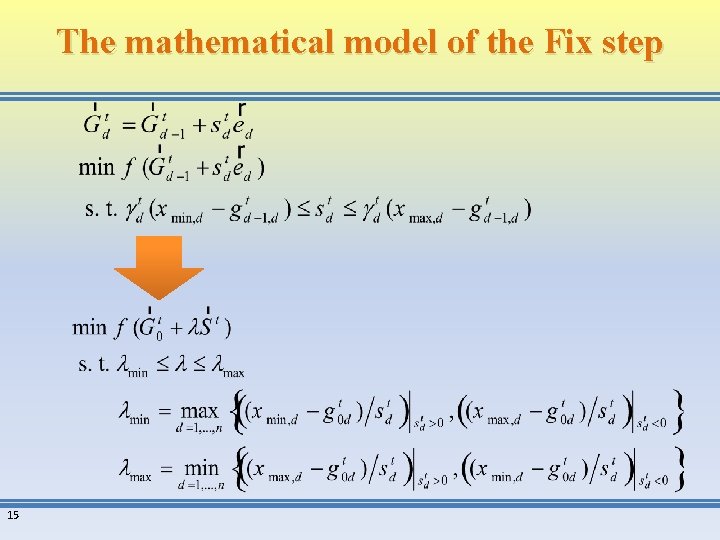
The mathematical model of the Fix step 15
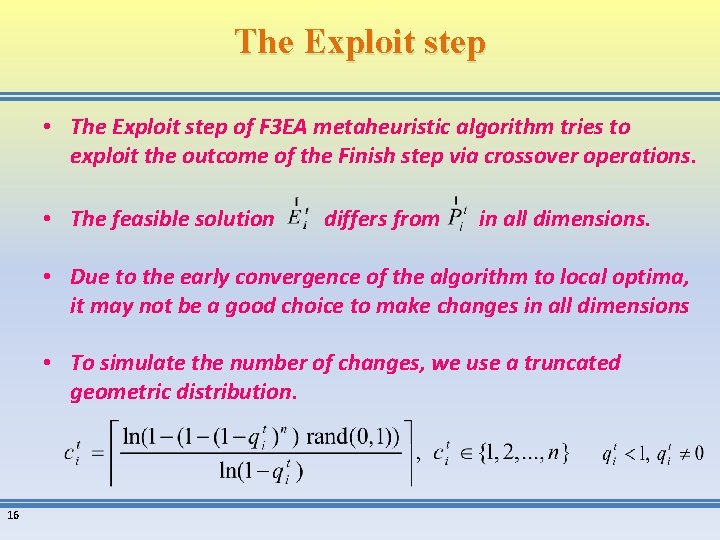
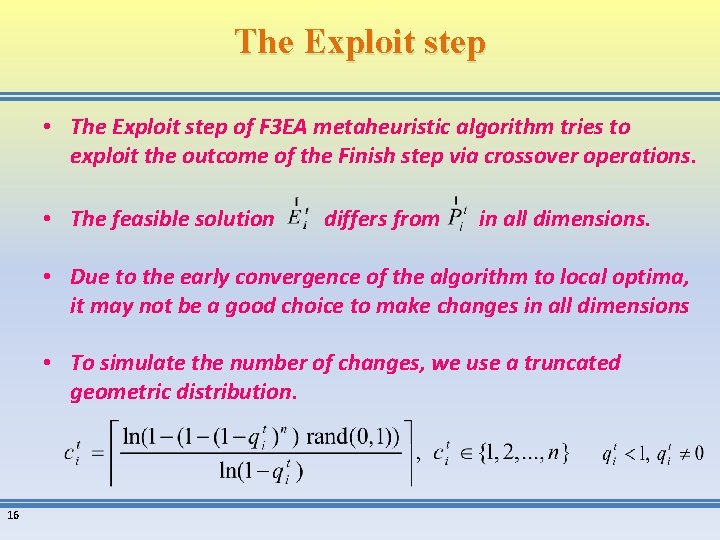
The Exploit step • The Exploit step of F 3 EA metaheuristic algorithm tries to exploit the outcome of the Finish step via crossover operations. • The feasible solution differs from in all dimensions. • Due to the early convergence of the algorithm to local optima, it may not be a good choice to make changes in all dimensions • To simulate the number of changes, we use a truncated geometric distribution. 16
The Analyze step • The Analyze step, is a replacement step. • New solutions which are generated during the Fix or Exploit steps may enter to population or update the global best solution. 17
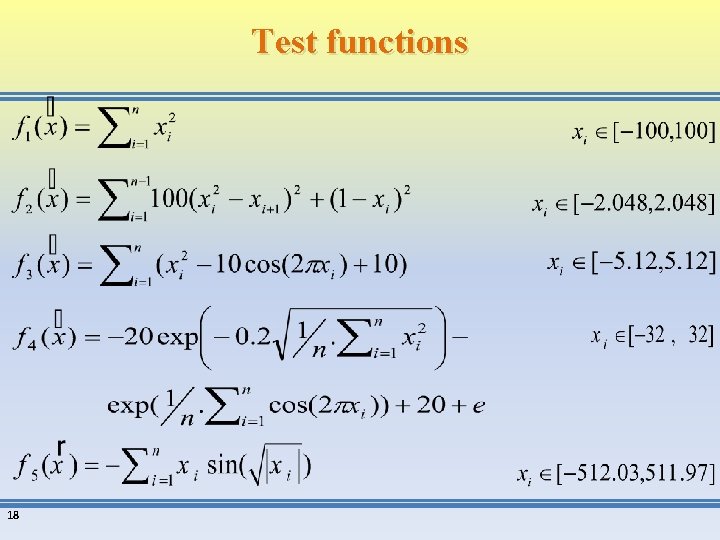
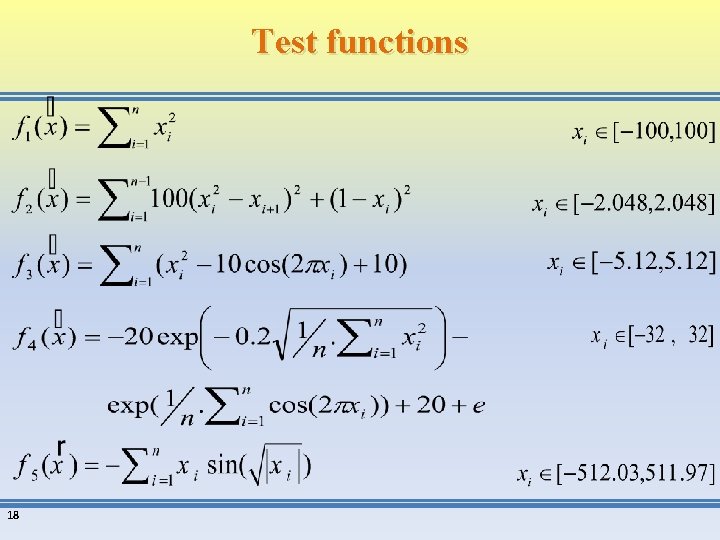
Test functions 18
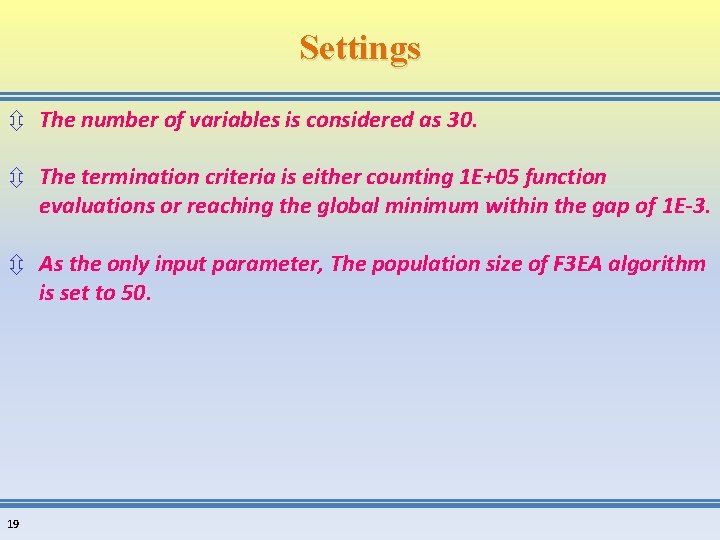
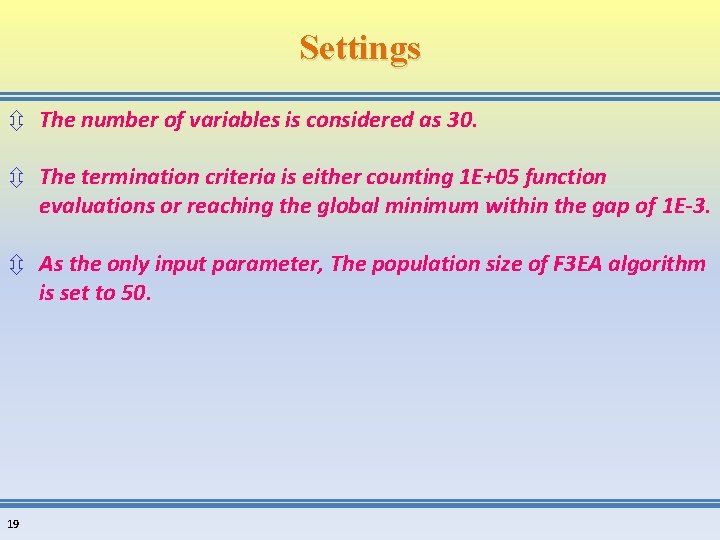
Settings ô The number of variables is considered as 30. ô The termination criteria is either counting 1 E+05 function evaluations or reaching the global minimum within the gap of 1 E-3. ô As the only input parameter, The population size of F 3 EA algorithm is set to 50. 19
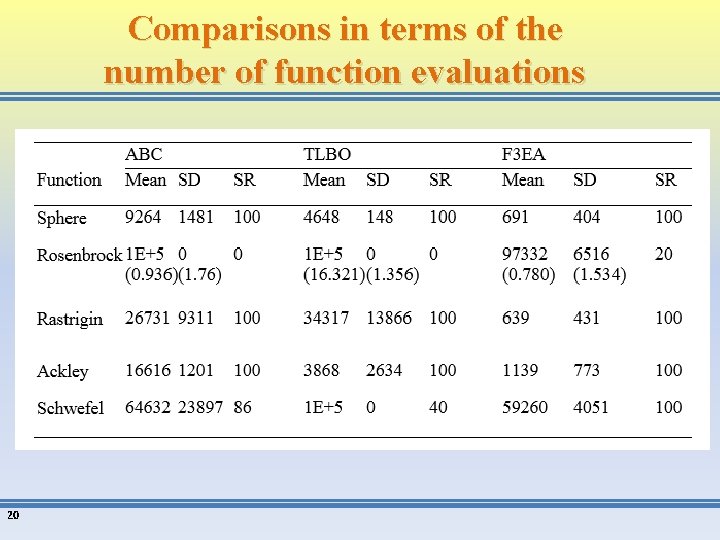
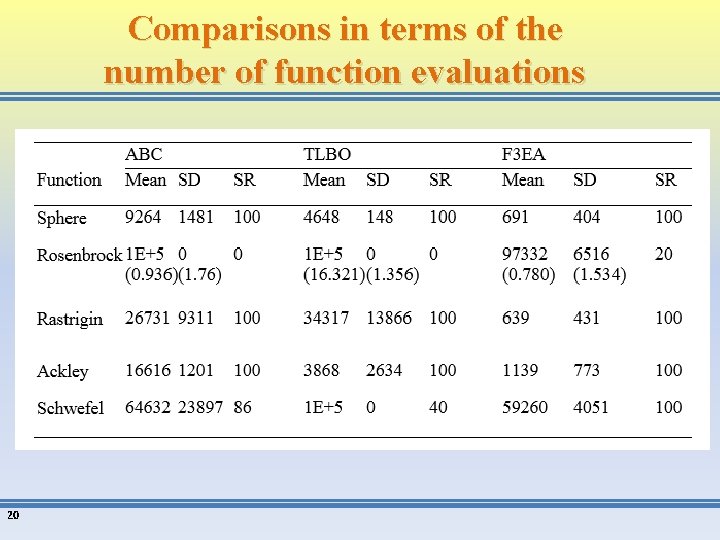
Comparisons in terms of the number of function evaluations 20

Thanks for your attention!