Network Centric Warfare Cyber Warfare KSCO Nort Fowler
Network Centric Warfare, Cyber Warfare, & KSCO Nort Fowler AFRL/IF 26 Electronic parkway, Rome NY 13441 Email: fowlern@rl. af. mil Tel: (315) 330 -4512
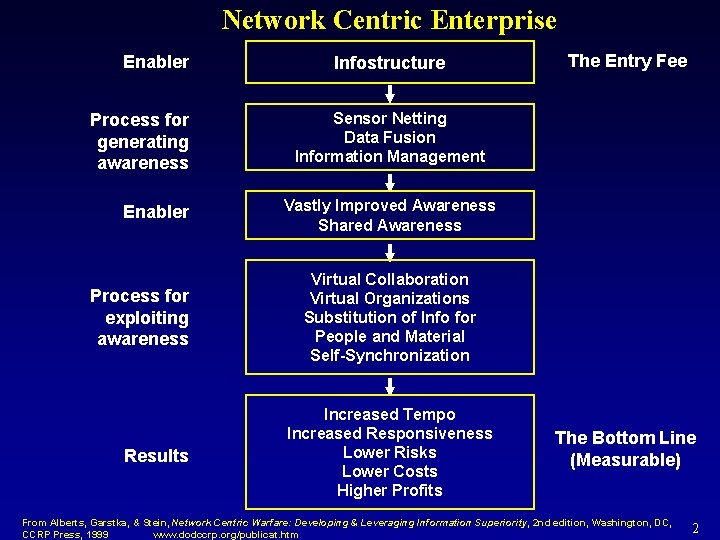
Network Centric Enterprise Enabler Process for generating awareness Enabler Process for exploiting awareness Results Infostructure The Entry Fee Sensor Netting Data Fusion Information Management Vastly Improved Awareness Shared Awareness Virtual Collaboration Virtual Organizations Substitution of Info for People and Material Self-Synchronization Increased Tempo Increased Responsiveness Lower Risks Lower Costs Higher Profits The Bottom Line (Measurable) From Alberts, Garstka, & Stein, Network Centric Warfare: Developing & Leveraging Information Superiority, 2 nd edition, Washington, DC, CCRP Press, 1999 www. dodccrp. org/publicat. htm 2
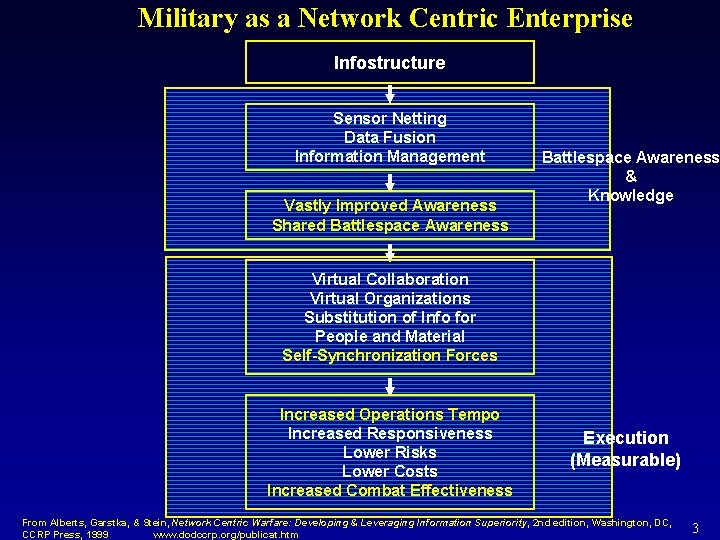
Military as a Network Centric Enterprise Infostructure Sensor Netting Data Fusion Information Management Vastly Improved Awareness Shared Battlespace Awareness & Knowledge Virtual Collaboration Virtual Organizations Substitution of Info for People and Material Self-Synchronization Forces Increased Operations Tempo Increased Responsiveness Lower Risks Lower Costs Increased Combat Effectiveness Execution (Measurable) From Alberts, Garstka, & Stein, Network Centric Warfare: Developing & Leveraging Information Superiority, 2 nd edition, Washington, DC, CCRP Press, 1999 www. dodccrp. org/publicat. htm 3
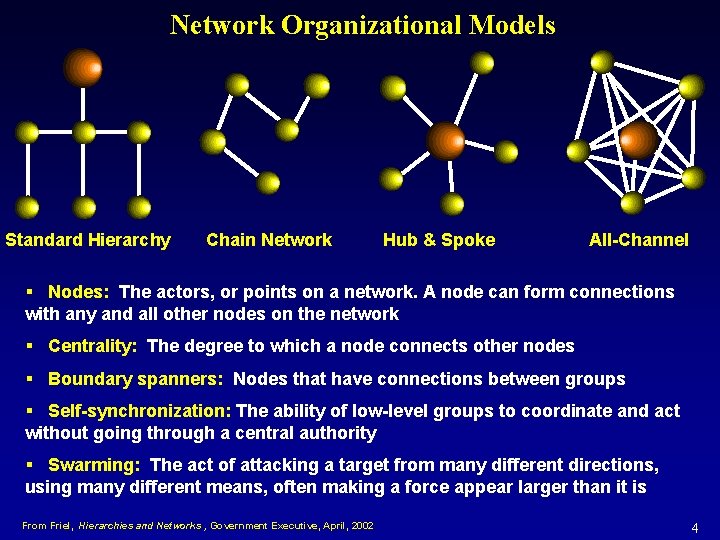
Network Organizational Models Standard Hierarchy Chain Network Hub & Spoke All-Channel § Nodes: The actors, or points on a network. A node can form connections with any and all other nodes on the network § Centrality: The degree to which a node connects other nodes § Boundary spanners: Nodes that have connections between groups § Self-synchronization: The ability of low-level groups to coordinate and act without going through a central authority § Swarming: The act of attacking a target from many different directions, using many different means, often making a force appear larger than it is From Friel, Hierarchies and Networks , Government Executive, April, 2002 4
Key Observations l The World has become a network of networks, filled with actors who behave in increasingly interconnected ways and with wide-reaching and rapid consequences l One major component of a network centric enterprise is speed…. The payoff is in the initial very high rate of change l A Northern Alliance commander suggested bombing Taliban positions. Nineteen minutes later the positions were struck l The critical functions of a network centric enterprise are NOT tied to any one platform; multiple new pathways to delivering capabilities, shifting in time l The swarming technique requires a key feature of networks -- adaptability l Swarming behavior visible in the war on terrorism 5
One Vision of Future Cyber Warfare • Two competing all-channel network “organizations” dueling in Cyberspace. • Each of these “organizations” might have many multiple ways they can deliver fatal blows • No longer "platform centric", their lethality is now multi-threaded • Multiple pathways imply that no single asset is on the critical path • The number of network pathways is growing exponentially. • Cyberwar might involve identifying and managing the network means of delivery in such a way that the adversary never has a lethal combination of delivery mechanisms for massed effects. • Once the adversary achieves just one such combination, the swarming strike will come at the speed of electrons. • A large scale, fast paced, distributed, deadly game of Cyber chess with missing or unknown pieces (capabilities, vulnerabilities). 6
Active Defense in Cyberspace Future Cyberwars will be fought to defend / destroy, not just the individual assets of the computer network, but the future combat capabilities achieved through a networked force 7
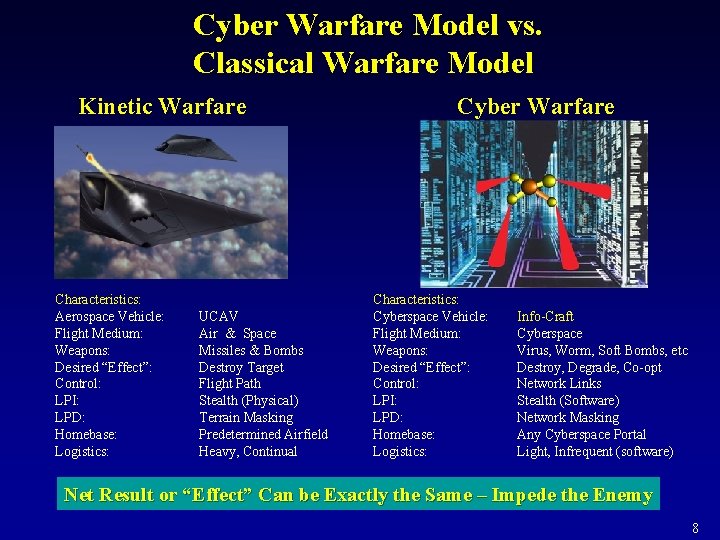
Cyber Warfare Model vs. Classical Warfare Model Kinetic Warfare Characteristics: Aerospace Vehicle: Flight Medium: Weapons: Desired “Effect”: Control: LPI: LPD: Homebase: Logistics: UCAV Air & Space Missiles & Bombs Destroy Target Flight Path Stealth (Physical) Terrain Masking Predetermined Airfield Heavy, Continual Cyber Warfare Characteristics: Cyberspace Vehicle: Flight Medium: Weapons: Desired “Effect”: Control: LPI: LPD: Homebase: Logistics: Info-Craft Cyberspace Virus, Worm, Soft Bombs, etc Destroy, Degrade, Co-opt Network Links Stealth (Software) Network Masking Any Cyberspace Portal Light, Infrequent (software) Net Result or “Effect” Can be Exactly the Same – Impede the Enemy 8
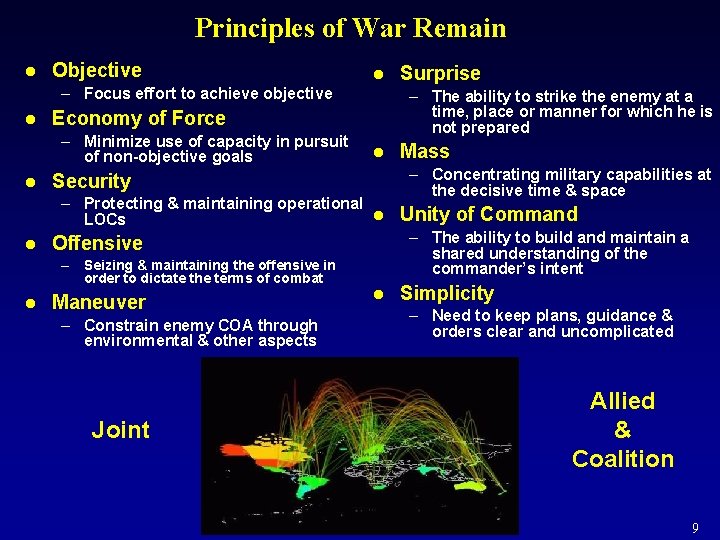
Principles of War Remain l Objective l – Focus effort to achieve objective l l – The ability to strike the enemy at a time, place or manner for which he is not prepared Economy of Force – Minimize use of capacity in pursuit of non-objective goals l Security – Protecting & maintaining operational l LOCs l l Maneuver – Constrain enemy COA through environmental & other aspects Joint Mass – Concentrating military capabilities at the decisive time & space Unity of Command – The ability to build and maintain a shared understanding of the commander’s intent Offensive – Seizing & maintaining the offensive in order to dictate the terms of combat Surprise l Simplicity – Need to keep plans, guidance & orders clear and uncomplicated Allied & Coalition 9
Some Possible Future Cyber Weapons Cyber weapons attack and control our adversary’s Information and C 3 I capabilities through intelligent use of information and controlled effects generated in Cyberspace. Stealthy Agents Network Blocking Mines Traffic Redirection (active & passive) Network Re-mapping Camouflaged Implants Sleeper Agents Adversary Finger Printing & Tracking Cyber Identity Theft Obfuscation (speed/mobility/deception) Tools Tribal Operators Remote Cyber Forensics 10
KSCO Opportunities 11
- Slides: 11