Virtual Private Networks VPN Based on slides accompanying
Virtual Private Networks (VPN) Based on slides accompanying the book Network Defense and Countermeasures by Chuck Easttom (2018)
Objectives n n n Use a virtual private network (VPN) Use Point-to-Point Tunneling Protocol (PPTP) as an encryption tool for VPNs Use Layer 2 Tunneling Protocol (L 2 TP) as an encryption tool for VPNs Add security and privacy to a communication using IPSec Understand evaluate VPN solutions © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 2
Introduction Virtual private networks (VPNs) provide users of your network the ability to establish a secure remote connection to the network as if they were connecting locally. VPNs provide a solution to the administrator’s need for security in remote connections while solving the user’s need to connect from virtually anywhere. © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 3
Basic VPN Technology n n n Data is encapsulated with a header and transmitted over the Internet Does not require additional technologies Multiple methods of connection are available: q q Dial-up and modem bank High-speed (DSL, cable modem, fiber optic. ) © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 4
Basic VPN Technology n n n Remote users are not the only beneficiaries Site-to-site connections can also be made Enables an organization to move away from expensive dedicated data lines © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 5
Protocols for VPN Encryption n PPTP L 2 TP IPSec © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 6
Point-to-Point Tunneling Protocol (PPTP) n n n Older technology than L 2 TP or IPSec but still widely used Near universal support among VPN equipment vendors Consumes fewer resources than L 2 TP and IPSec n n n Operates at Layer 2 of OSI model Supports IPX and Net. BEUI transmissions Supports two generic types of tunneling q q © 2019 by Pearson Education, Inc. Voluntary Compulsory Chapter 7 Virtual Private Networks 7
PPTP Authentication n Extensible Authentication Protocol (EAP) q n Designed specifically with PPTP, works from within PPP’s authentication protocol Challenge Handshake Authentication Protocol (CHAP) q Three-part handshaking procedure n n n Server sends a challenge message to the originating client Client sends back a value calculated using a one-way hash function Server checks the response against its own calculation © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 8
Layer 2 Tunneling Protocol (L 2 TP) n n New and improved version of PPTP Considered less secure than IPSec Not uncommon to be used with IPSec L 2 TP Authentication q q Supports EAP, CHAP (as PPTP does) Also supports MS-CHAP, PAP, SPAP, and Kerberos © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 9
L 2 TP Authentication n MS-CHAP Versus CHAP q q Response packet formatted for Windows compatibility Does not require the authenticator to store a cleartext or reversibly encrypted password Provides retry and password changing mechanisms Defines a set of reason-for-failure codes © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 10
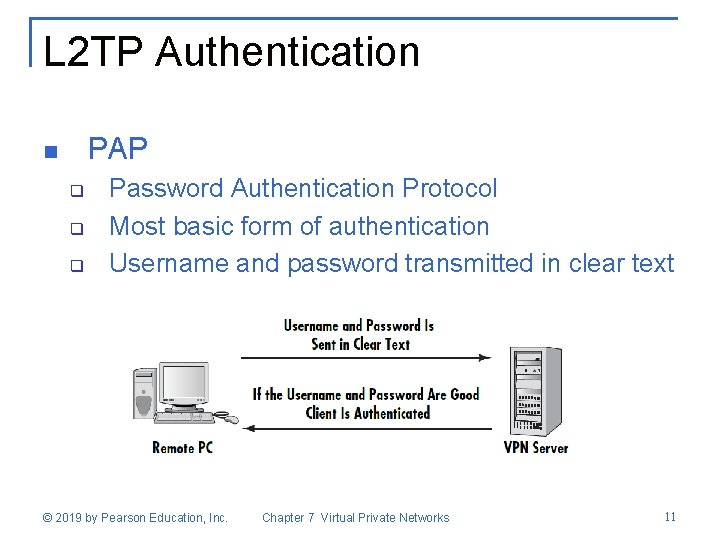
L 2 TP Authentication PAP n q q q Password Authentication Protocol Most basic form of authentication Username and password transmitted in clear text © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 11
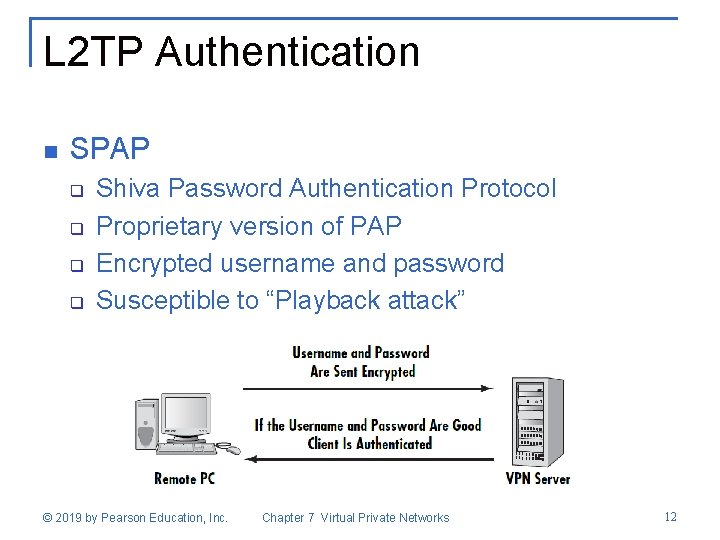
L 2 TP Authentication n SPAP q q Shiva Password Authentication Protocol Proprietary version of PAP Encrypted username and password Susceptible to “Playback attack” © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 12
Kerberos n n Very well-known network authentication protocol Sends messages between client and server The actual password is never sent, even as a hash Server uses the stored hash of the password as an encryption key to encrypt data and send it back to the client © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 13
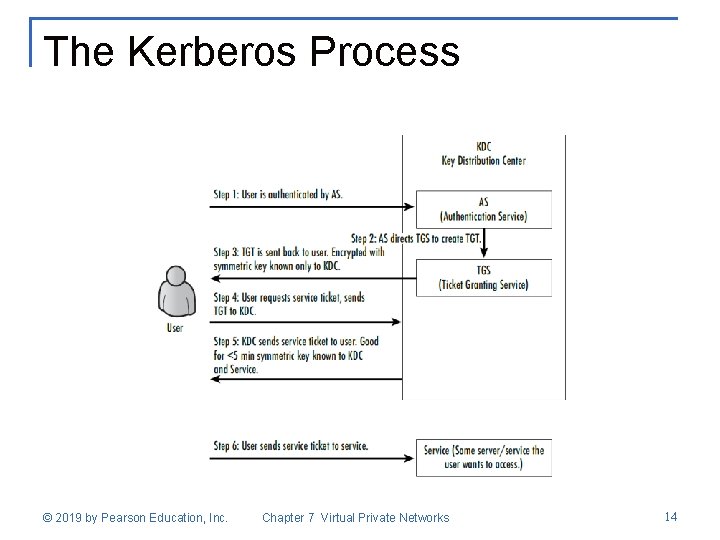
The Kerberos Process © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 14
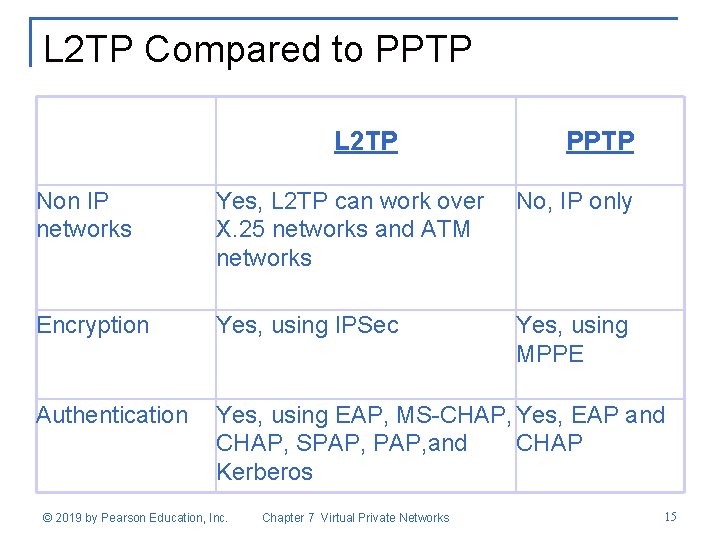
L 2 TP Compared to PPTP L 2 TP PPTP Non IP networks Yes, L 2 TP can work over X. 25 networks and ATM networks No, IP only Encryption Yes, using IPSec Yes, using MPPE Authentication Yes, using EAP, MS-CHAP, Yes, EAP and CHAP, SPAP, and CHAP Kerberos © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 15
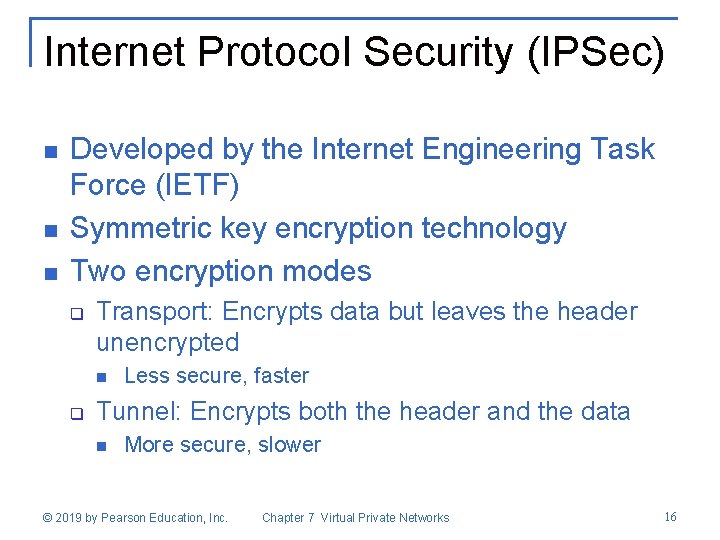
Internet Protocol Security (IPSec) n n n Developed by the Internet Engineering Task Force (IETF) Symmetric key encryption technology Two encryption modes q Transport: Encrypts data but leaves the header unencrypted n q Less secure, faster Tunnel: Encrypts both the header and the data n More secure, slower © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 16
Other Protocols Used with IPSec n Authentication Header (AH) q n Encapsulated Security Payload (ESP) q n Authentication only Both data confidentiality and authentication Internet Key Exchange (IKE) q Sets up security associations © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 17
SSL/TLS n Protocols used to secure websites q q n SSL: Secure Sockets Layer TLS: Transport Layer Security A new type of firewall uses them to provide VPN access through a web portal © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 18
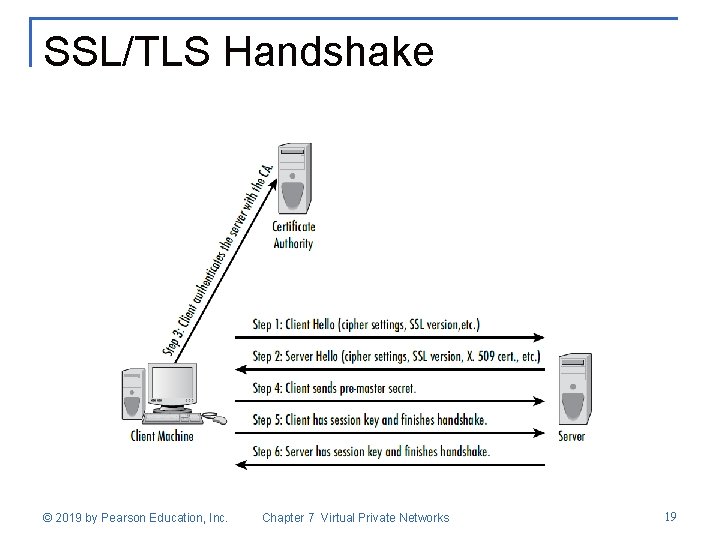
SSL/TLS Handshake © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 19
Implementing VPN Solutions n n n Built-in solutions Cisco Solutions Service Solutions Openswan Other Solutions © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 20
Summary n n n VPNs provide a secure way of connecting remote users to the network L 2 TP, PPTP, and IPSec are protocols that can be used PPTP is based on the PPP SSL/TLS can be used to secure a VPN connection via web access Solutions built into an operating system may not provide adequate features for large companies © 2019 by Pearson Education, Inc. Chapter 7 Virtual Private Networks 21
- Slides: 21