ServerSide Web Programming with Active Server Pages ASP
Server-Side Web Programming with Active Server Pages ASP Security Alternatives 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 1
Web Security • Web security is resource intensive (servers, staff, money) due to rapid pace of technology and fundamentally “open” nature of TCP/IP • Implementing secure web transactions is complex and costly. • Avoid implementing security when possible. • ALWAYS use security for financial transactions. • Remember: password security is based upon the trustworthiness and precautions taken by then password’s user. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 2
ASP Security—No Security • No security is the easiest option! • Obviously not feasible for financial and other sensitive transactions. • However, question the business need for security on less clear requests. User’s tend to overstate security needs. • In government settings, most posted information is public information unless specifically protected by law. Don’t give a false sense of security to users. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 3
Database-driven Security • Use ASP pages to pass login information to a database (similar to SHOP database). • Users/passwords must be managed. • Can easily build ASP-based front-ends for administering passwords. • Requires user to remember another username/password combination. • Ok security, but any semi-knowledgeable hacker with freeware tools can trap user’s password and information. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 4
Server-driven Security • Use the security features provided by IIS/Windows to limit access to specified users. • Users must have Windows user accounts on the server or NT domain. • Windows user accounts must be managed. • More difficult to program web-based user management using server security. • Several different types of server-driven security provided by Windows/IIS. Some more secure than others. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 5
Server-driven Security IIS Authentication/Impersonation • IIS takes HTTP requests and first attempts to figure out who you are – i. e. authenticate you. • Then, IIS assumes your identity – i. e. impersonates you and processes your request like you were logged on to the server’s console screen. • Thus, all users "logon" to the webserver. • This approach allows IIS to take advantage of native NT security and protection features without having to provide its own security functions. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 6
Server-driven Security “Anonymous” access • Default setting for IIS. • Default is that users are authenticated and logged on to the NT server using the “anonymous user” account created by IIS. • Requires the least server resources. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 7
Server-driven Security Basic Authentication • Use NT, IIS, or Front. Page to limit access to specific Windows user accounts. • User prompted for username/password when accesses a secured page. • Username and password are transmitted via HTTP as unencrypted, clear text. • Supported by virtually all browsers. • Ok security, but any semi-knowledgeable hacker with freeware tools can trap user’s password and information. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 8
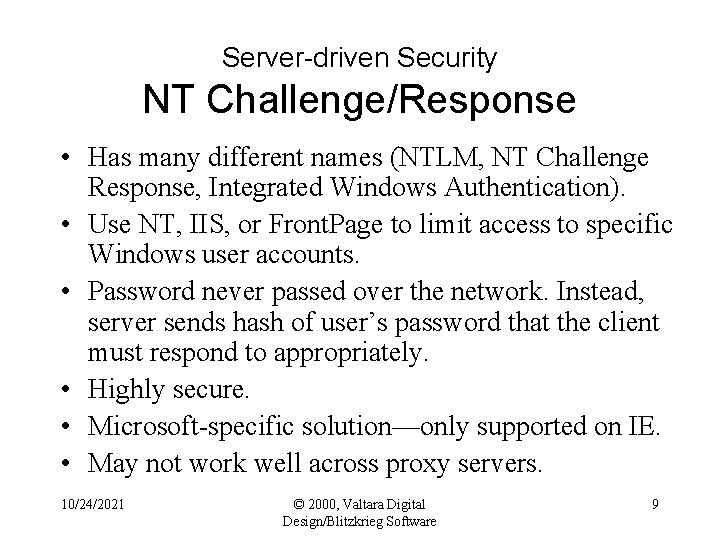
Server-driven Security NT Challenge/Response • Has many different names (NTLM, NT Challenge Response, Integrated Windows Authentication). • Use NT, IIS, or Front. Page to limit access to specific Windows user accounts. • Password never passed over the network. Instead, server sends hash of user’s password that the client must respond to appropriately. • Highly secure. • Microsoft-specific solution—only supported on IE. • May not work well across proxy servers. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 9
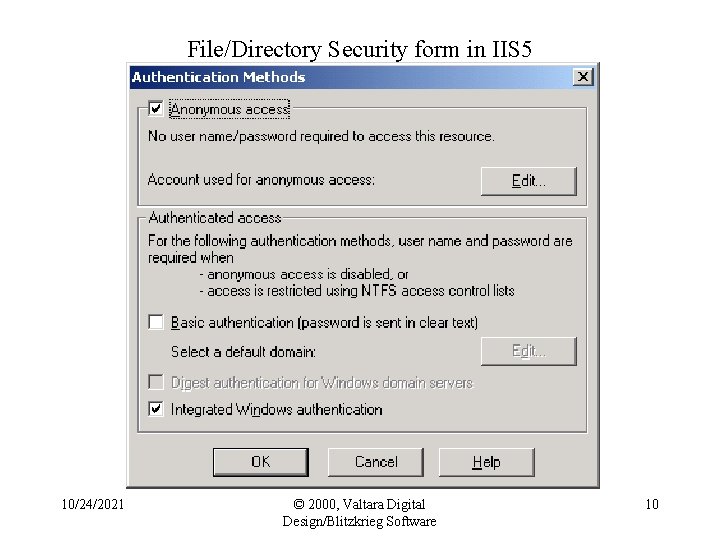
File/Directory Security form in IIS 5 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 10
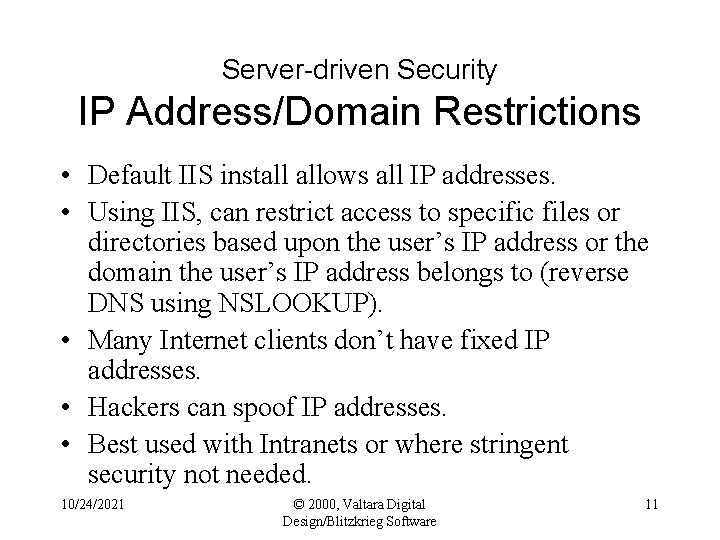
Server-driven Security IP Address/Domain Restrictions • Default IIS install allows all IP addresses. • Using IIS, can restrict access to specific files or directories based upon the user’s IP address or the domain the user’s IP address belongs to (reverse DNS using NSLOOKUP). • Many Internet clients don’t have fixed IP addresses. • Hackers can spoof IP addresses. • Best used with Intranets or where stringent security not needed. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 11
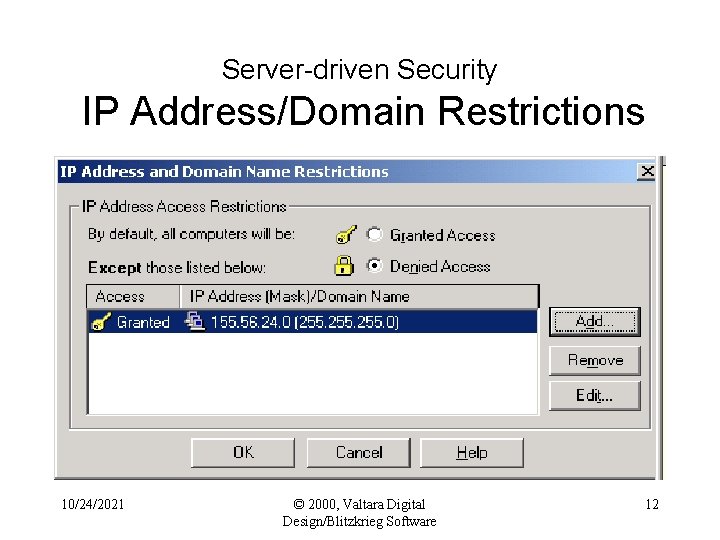
Server-driven Security IP Address/Domain Restrictions 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 12
Server-driven Security What do you do? • Financial and sensitive transactions must be secure… • Database-driven security and Basic Authentication support all platforms but have limited security. • NT Challenge/Response is highly secure but Microsoft specific. • IP addresses can be spoofed by hackers. • The answer is… 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 13
Secure Sockets Layer • SSL (HTTPS) is the basis of secure exchange of sensitive e -commerce information. • Clients and servers establish a secure link, or "pipe" across the Internet – the pipe is encrypted HTTP packets. • SSL does end-to-end encryption of the HTTP stream using public key encryption by digital certificate. • Requirements: – Both browser and server must support HTTPS (3. x+) – Requires a digital certificate from “trusted” third party like Verisign (http: //www. verisign. com). • Serious configuration and ongoing maintenance issues. http: //developer. netscape. com/tech/security/ssl/howitworks. html 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 14
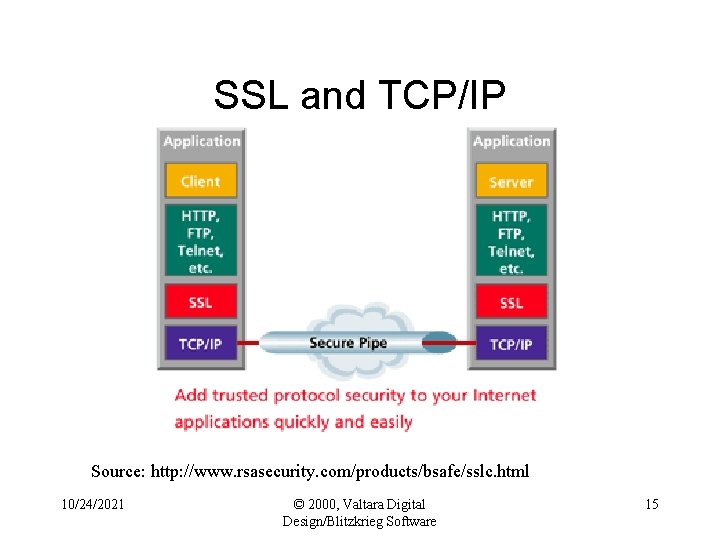
SSL and TCP/IP Source: http: //www. rsasecurity. com/products/bsafe/sslc. html 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 15
Digital Server Certificate • To use SSL, your sever must have a digital server certificate (an electronic file). • Communicates your site's authenticity to visitors' web browsers, confirming to visitor they are working with you instead of a fraudulent site pretending to be you. • Used to encrypt data exchanged between client and your server interception or tampering. • Your webserver should have tools to generate a “public” and “private” key for your server. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 16
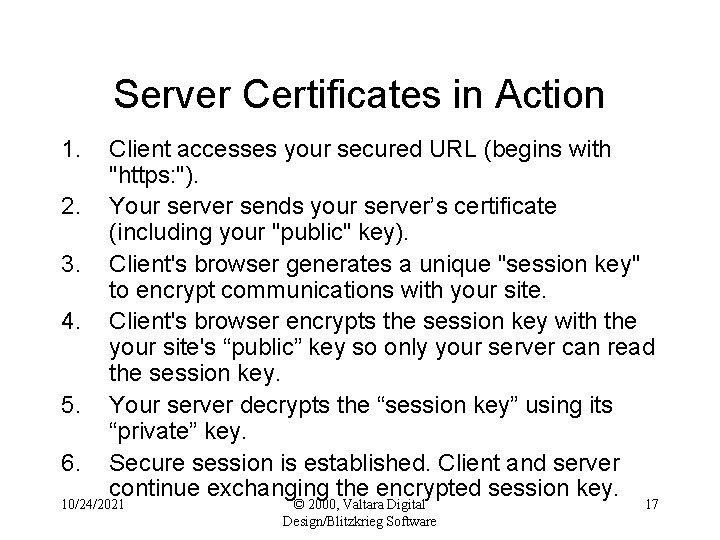
Server Certificates in Action 1. 2. 3. 4. 5. 6. Client accesses your secured URL (begins with "https: "). Your server sends your server’s certificate (including your "public" key). Client's browser generates a unique "session key" to encrypt communications with your site. Client's browser encrypts the session key with the your site's “public” key so only your server can read the session key. Your server decrypts the “session key” using its “private” key. Secure session is established. Client and server continue exchanging the encrypted session key. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 17
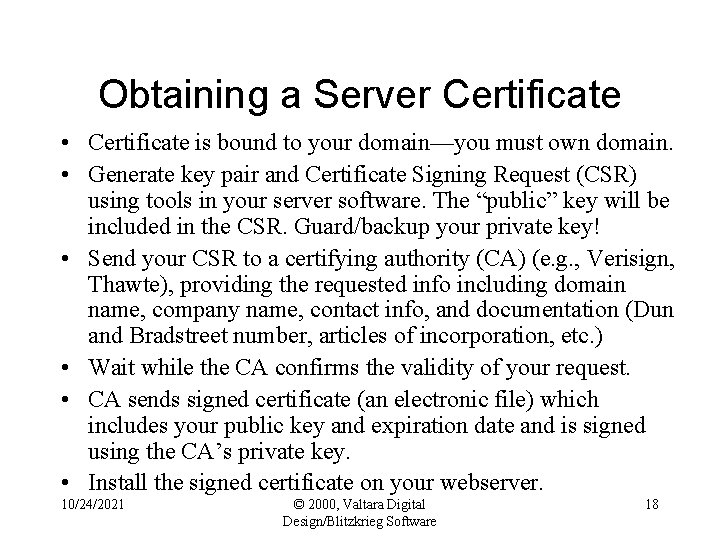
Obtaining a Server Certificate • Certificate is bound to your domain—you must own domain. • Generate key pair and Certificate Signing Request (CSR) using tools in your server software. The “public” key will be included in the CSR. Guard/backup your private key! • Send your CSR to a certifying authority (CA) (e. g. , Verisign, Thawte), providing the requested info including domain name, company name, contact info, and documentation (Dun and Bradstreet number, articles of incorporation, etc. ) • Wait while the CA confirms the validity of your request. • CA sends signed certificate (an electronic file) which includes your public key and expiration date and is signed using the CA’s private key. • Install the signed certificate on your webserver. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 18
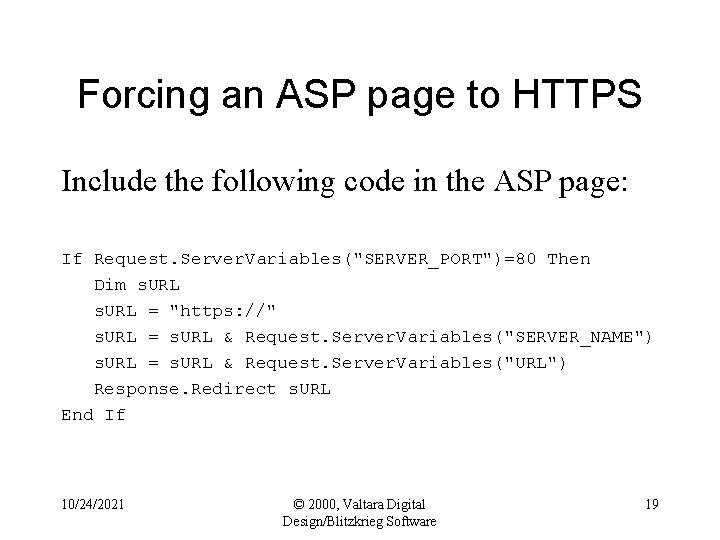
Forcing an ASP page to HTTPS Include the following code in the ASP page: If Request. Server. Variables("SERVER_PORT")=80 Then Dim s. URL = "https: //" s. URL = s. URL & Request. Server. Variables("SERVER_NAME") s. URL = s. URL & Request. Server. Variables("URL") Response. Redirect s. URL End If 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 19
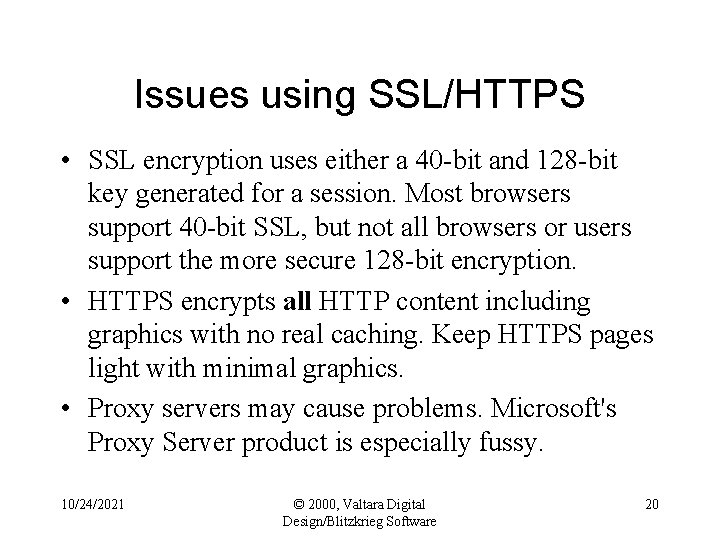
Issues using SSL/HTTPS • SSL encryption uses either a 40 -bit and 128 -bit key generated for a session. Most browsers support 40 -bit SSL, but not all browsers or users support the more secure 128 -bit encryption. • HTTPS encrypts all HTTP content including graphics with no real caching. Keep HTTPS pages light with minimal graphics. • Proxy servers may cause problems. Microsoft's Proxy Server product is especially fussy. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 20
Increasing HTTPS Performance • Many low-cost web hosting accounts only provide “shared” access to an HTTPS directory with others —HTTPS URL will not be in your domain. • Good practice is to put HTTPS in a separate virtual webserver. • Best practice is to put HTTPS on a separate server, ideally with an encryption co-processor board. • Very best practice is to do hardware SSL on a special router between the webserver and the Internet (very expensive). 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 21
SSL/HTTPS Issues • At least 20 -30% performance hit on encrypted pages. • Set Response. Expires on all pages (e. g. , Response. Expires. Absolute = Now() - 1 ) • Serious administrative overhead to monitor attacks and keep it running smooth. Plan resources or outsource. 10/24/2021 © 2000, Valtara Digital Design/Blitzkrieg Software 22
- Slides: 22