Mobile Cloud Service Enterprise Single Sign On SSO

Mobile Cloud Service Enterprise Single Sign On (SSO) and Backend Integration Security Geoff Poremba Senior Principal Product Manager Oracle Mobile March 2016 Copyright © 2014 Oracle and/or its affiliates. All rights reserved. |
Topics • Enterprise SSO – Intro – Benefits – Process Flow • Scenarios and Architectural Diagrams – Enterprise SSO – Backend Integration • Caveats Copyright © 2014 Oracle and/or its affiliates. All rights reserved. | 2
MCS Security MCS 16. 1. 3 (v 1. 2) Introduces Enterprise SSO • Enabled per Mobile Backend (MBE) - Requires OAuthentication for APIs • Users can Authenticate with MCS using credentials from an external identity provider • Users must still be provisioned into the Shared Identity Manager (SIM) - Passwords do not need to be provisioned Copyright © 2014 Oracle and/or its affiliates. All ri
MCS Security Enterprise SSO Benefits • Simplifies Administration • Removes need for duplicate credentials • Authentication strategies are transparent to MCS, for example: - Password strength - Multi-factor Authentication Copyright © 2014 Oracle and/or its affiliates. All ri
Mobile Cloud Service Enterprise SSO Process Flow 1. 2. 3. 4. 5. Mobile Application makes an access token request to MCS (can be done through an embedded browser) and instructs it to send a user access token request to MCS The user access token request is intercepted by the Oracle Access Manager (OAM) Web. Gate, and is redirected to Shared Identity Manager (SIM), which in turn redirects the request to the on-premise (or Cloud) Identity Provider (Id. P) The on-premise Id. P collects the user’s credentials via the embedded browser, and once the user is authenticated, redirects the request back to SIM along with a SAML token. SIM validates the SAML token then redirects the request to MCS obtains a user access token from the SIM OAuth Server and returns it to the Mobile Application Mobile application utilizes the OAuth user access token to call Mobile Cloud Service REST APIs Copyright © 2014 Oracle and/or its affiliates. All ri
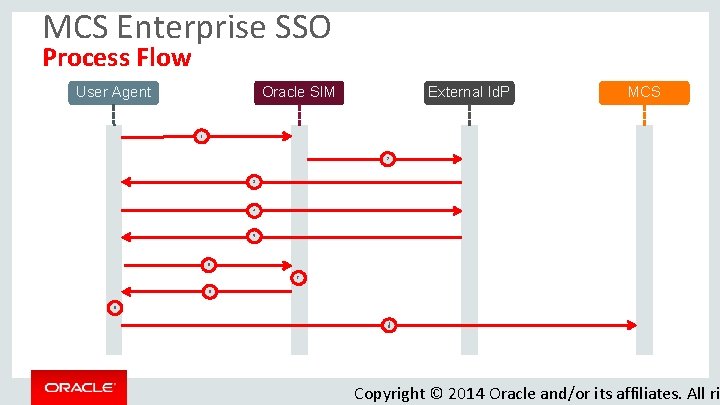
MCS Enterprise SSO Process Flow Oracle SIM User Agent External Id. P MCS 1 2 3 4 5 6 7 8 9 1 0 Copyright © 2014 Oracle and/or its affiliates. All ri
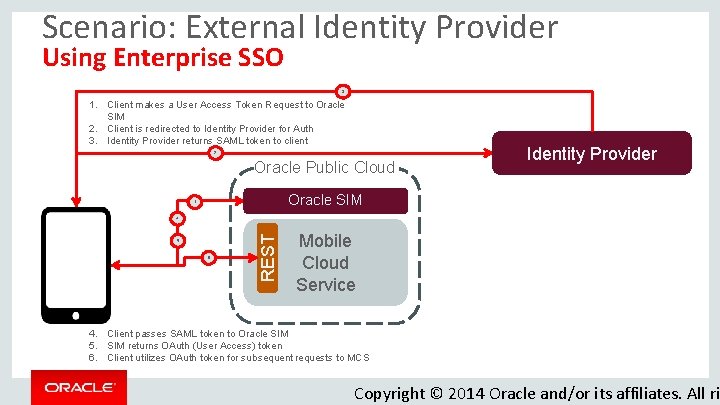
Scenario: External Identity Provider Using Enterprise SSO 3 1. Client makes a User Access Token Request to Oracle SIM 2. Client is redirected to Identity Provider for Auth 3. Identity Provider returns SAML token to client 2 Oracle Public Cloud Identity Provider Oracle SIM 1 5 6 REST 4 Mobile Cloud Service 4. Client passes SAML token to Oracle SIM 5. SIM returns OAuth (User Access) token 6. Client utilizes OAuth token for subsequent requests to MCS Copyright © 2014 Oracle and/or its affiliates. All ri
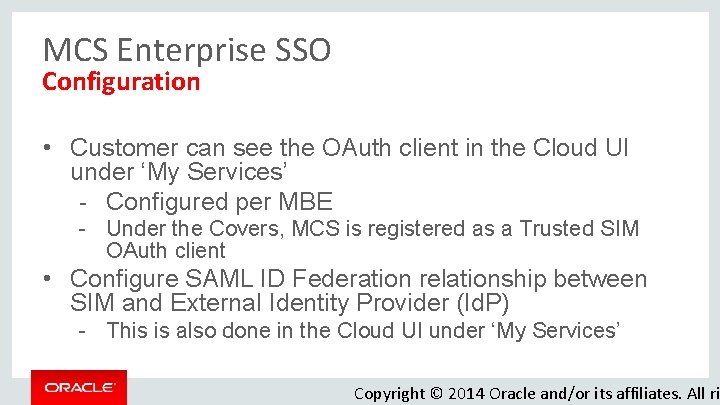
MCS Enterprise SSO Configuration • Customer can see the OAuth client in the Cloud UI under ‘My Services’ - Configured per MBE - Under the Covers, MCS is registered as a Trusted SIM OAuth client • Configure SAML ID Federation relationship between SIM and External Identity Provider (Id. P) - This is also done in the Cloud UI under ‘My Services’ Copyright © 2014 Oracle and/or its affiliates. All ri
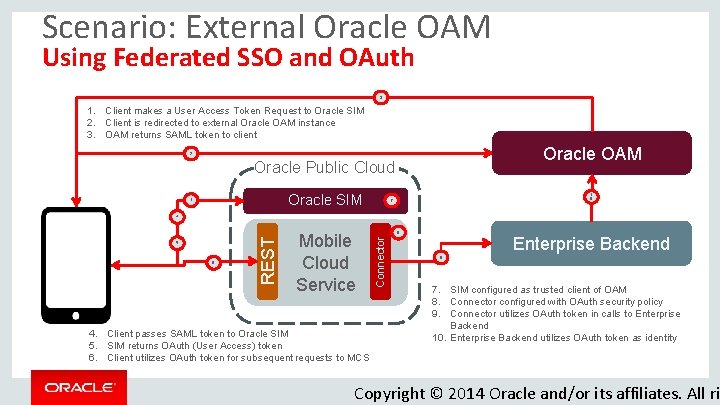
Scenario: External Oracle OAM Using Federated SSO and OAuth 3 1. Client makes a User Access Token Request to Oracle SIM 2. Client is redirected to external Oracle OAM instance 3. OAM returns SAML token to client Oracle OAM 2 Oracle Public Cloud Oracle SIM 1 1 0 7 6 Mobile Cloud Service 4. Client passes SAML token to Oracle SIM 5. SIM returns OAuth (User Access) token 6. Client utilizes OAuth token for subsequent requests to MCS 8 Connector 5 REST 4 Enterprise Backend 9 7. SIM configured as trusted client of OAM 8. Connector configured with OAuth security policy 9. Connector utilizes OAuth token in calls to Enterprise Backend 10. Enterprise Backend utilizes OAuth token as identity Copyright © 2014 Oracle and/or its affiliates. All ri
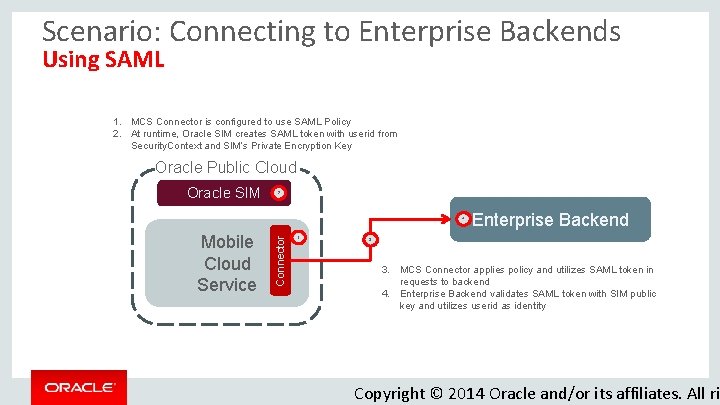
Scenario: Connecting to Enterprise Backends Using SAML 1. MCS Connector is configured to use SAML Policy 2. At runtime, Oracle SIM creates SAML token with userid from Security. Context and SIM’s Private Encryption Key Oracle Public Cloud Oracle SIM 2 Mobile Cloud Service Connector 4 1 Enterprise Backend 3 3. MCS Connector applies policy and utilizes SAML token in requests to backend 4. Enterprise Backend validates SAML token with SIM public key and utilizes userid as identity Copyright © 2014 Oracle and/or its affiliates. All ri
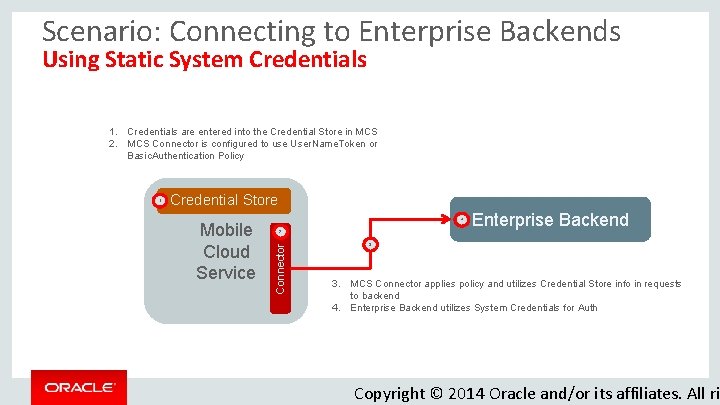
Scenario: Connecting to Enterprise Backends Using Static System Credentials 1. Credentials are entered into the Credential Store in MCS 2. MCS Connector is configured to use User. Name. Token or Basic. Authentication Policy Credential Store Mobile Cloud Service 4 2 Connector 1 Enterprise Backend 3 3. MCS Connector applies policy and utilizes Credential Store info in requests to backend 4. Enterprise Backend utilizes System Credentials for Auth Copyright © 2014 Oracle and/or its affiliates. All ri
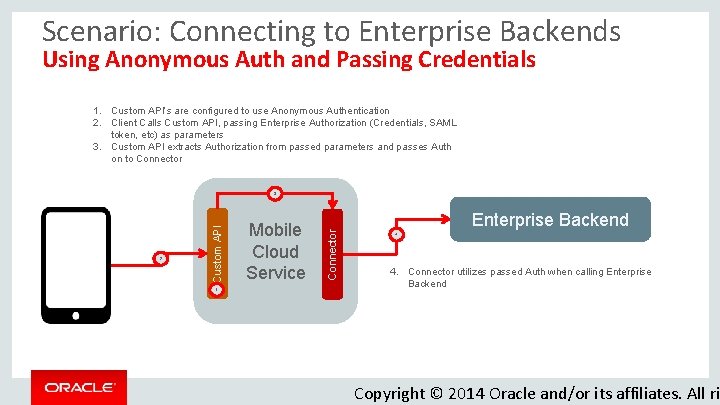
Scenario: Connecting to Enterprise Backends Using Anonymous Auth and Passing Credentials 1. Custom API’s are configured to use Anonymous Authentication 2. Client Calls Custom API, passing Enterprise Authorization (Credentials, SAML token, etc) as parameters 3. Custom API extracts Authorization from passed parameters and passes Auth on to Connector 1 Mobile Cloud Service Connector 2 Custom API 3 Enterprise Backend 4 4. Connector utilizes passed Auth when calling Enterprise Backend Copyright © 2014 Oracle and/or its affiliates. All ri
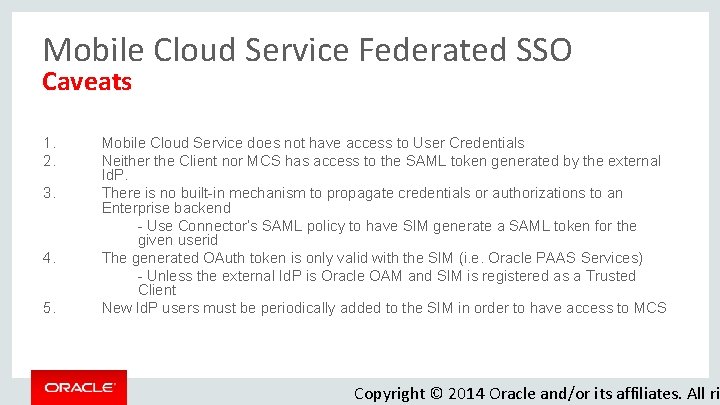
Mobile Cloud Service Federated SSO Caveats 1. 2. 3. 4. 5. Mobile Cloud Service does not have access to User Credentials Neither the Client nor MCS has access to the SAML token generated by the external Id. P. There is no built-in mechanism to propagate credentials or authorizations to an Enterprise backend - Use Connector’s SAML policy to have SIM generate a SAML token for the given userid The generated OAuth token is only valid with the SIM (i. e. Oracle PAAS Services) - Unless the external Id. P is Oracle OAM and SIM is registered as a Trusted Client New Id. P users must be periodically added to the SIM in order to have access to MCS Copyright © 2014 Oracle and/or its affiliates. All ri
- Slides: 13