Lecture 7 Key Distribution secret keys public keys
Lecture 7: Key Distribution secret keys public keys 1
Secret Keys Distribution Problem • in the system where there are n users and potentially any user can communicate with any other? • one scheme: each user knows the keys of all the others – needs n 2 keys • Key Distribution Center – each user has a key – The KDC has all keys – The KDC assigns a (new) key to any pair who need to talk 2
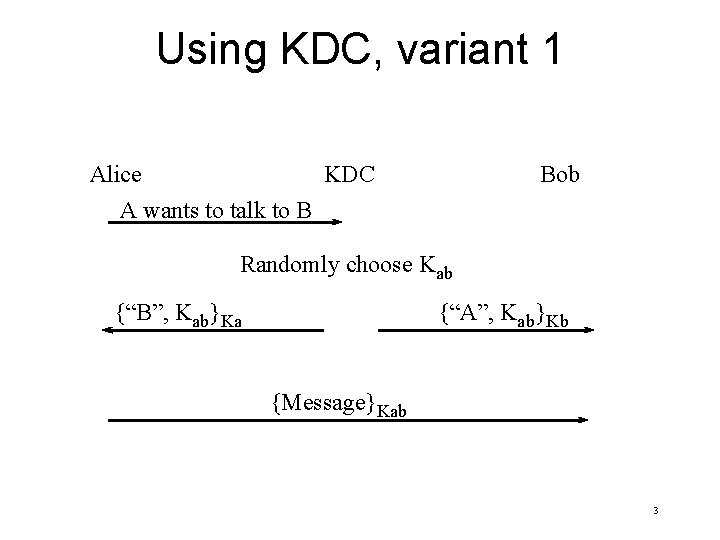
Using KDC, variant 1 KDC Alice A wants to talk to B Bob Randomly choose Kab {“B”, Kab}Ka {“A”, Kab}Kb {Message}Kab 3
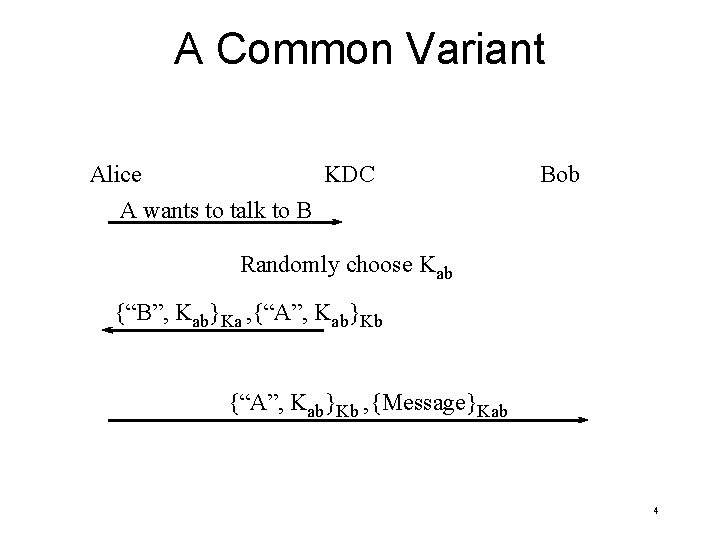
A Common Variant KDC Alice A wants to talk to B Bob Randomly choose Kab {“B”, Kab}Ka , {“A”, Kab}Kb , {Message}Kab 4
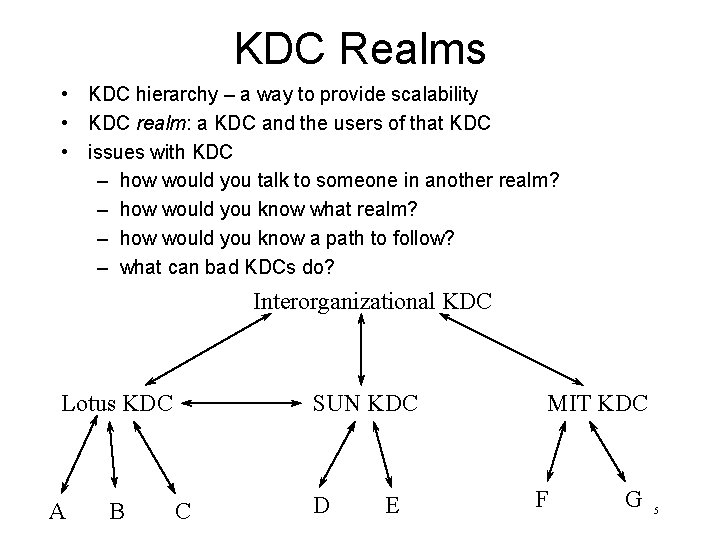
KDC Realms • KDC hierarchy – a way to provide scalability • KDC realm: a KDC and the users of that KDC • issues with KDC – how would you talk to someone in another realm? – how would you know what realm? – how would you know a path to follow? – what can bad KDCs do? Interorganizational KDC Lotus KDC A B SUN KDC C D E MIT KDC F G 5
Public Key Distribution • Certification Authority (CA) signs “Certificates” – Certificate: a signed message saying “I, the CA, vouch that 489024729 is Mikhail’s public key” • If everyone has a certificate, a private key, and the CA’s public key, they can authenticate • CA vs. KDC – what if KDC database is stolen? CA private key? – what needs to be done if CA compromised? If KDC compromised? – What if KDC or CA down temporarily? 6
Strategies for CA Hierarchies • strategies – One universally trusted organization – Top-Down, starting from a universally trusted organization’s well-known key – No rules. Anyone signs anything. End users decide who to trust – Many independent CA’s. Configure which ones to trust • more on that later when we cover PKI 7
- Slides: 7