Lab on iptables 392017 CSC 4430 LAB ON
Lab on iptables 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 1
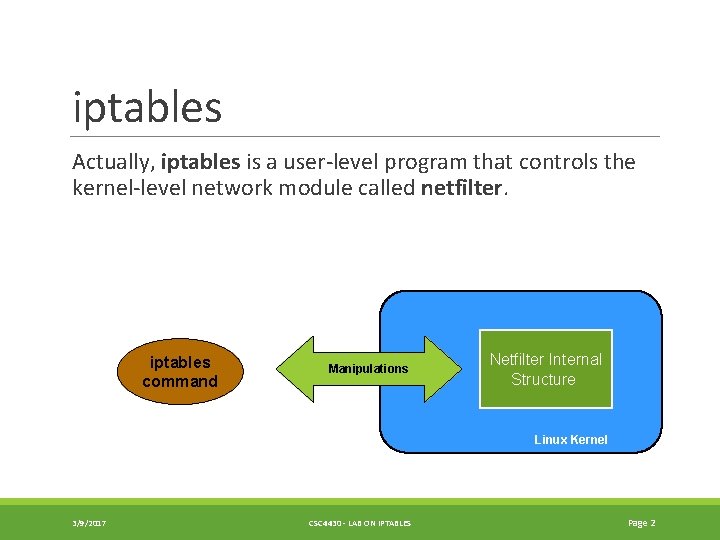
iptables Actually, iptables is a user-level program that controls the kernel-level network module called netfilter. iptables command Manipulations Netfilter Internal Structure Linux Kernel 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 2
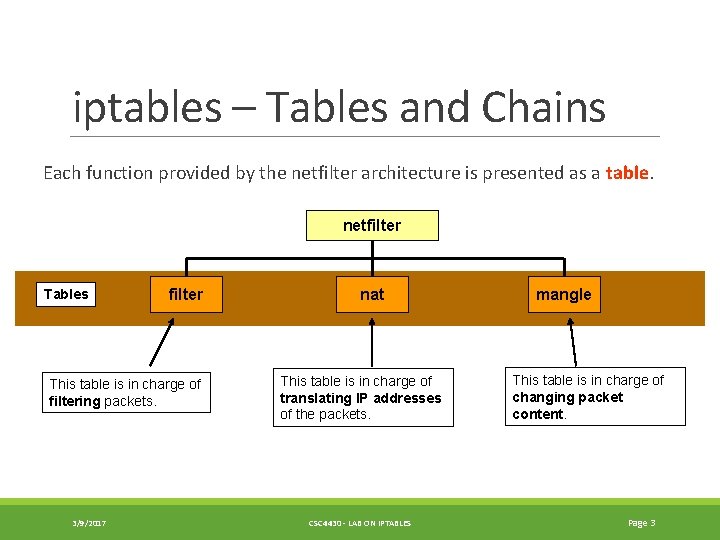
iptables – Tables and Chains Each function provided by the netfilter architecture is presented as a table. netfilter Tables filter This table is in charge of filtering packets. 3/9/2017 nat This table is in charge of translating IP addresses of the packets. CSC 4430 - LAB ON IPTABLES mangle This table is in charge of changing packet content. Page 3
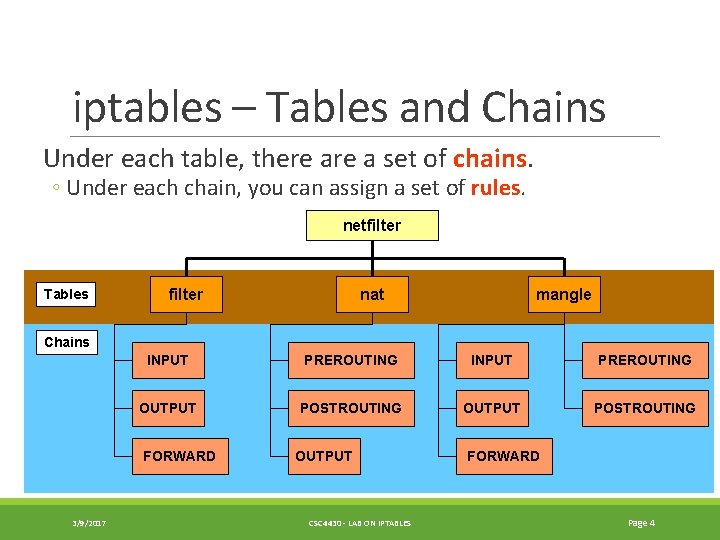
iptables – Tables and Chains Under each table, there a set of chains. ◦ Under each chain, you can assign a set of rules. netfilter Tables filter nat mangle Chains INPUT PREROUTING OUTPUT POSTROUTING FORWARD 3/9/2017 OUTPUT CSC 4430 - LAB ON IPTABLES FORWARD Page 4
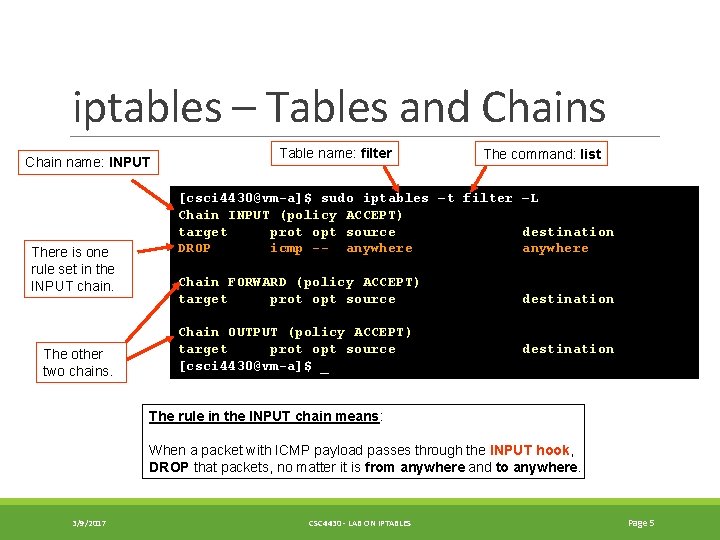
iptables – Tables and Chains Chain name: INPUT There is one rule set in the INPUT chain. The other two chains. Table name: filter The command: list [csci 4430@vm-a]$ sudo iptables –t filter –L Chain INPUT (policy ACCEPT) target prot opt source destination DROP icmp -- anywhere Chain FORWARD (policy ACCEPT) target prot opt source Chain OUTPUT (policy ACCEPT) target prot opt source [csci 4430@vm-a]$ _ destination The rule in the INPUT chain means: When a packet with ICMP payload passes through the INPUT hook, DROP that packets, no matter it is from anywhere and to anywhere. 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 5
![iptables – Tables and Chains [csci 4430@vm-a]$ sudo iptables -t filter -A INPUT --protocol iptables – Tables and Chains [csci 4430@vm-a]$ sudo iptables -t filter -A INPUT --protocol](http://slidetodoc.com/presentation_image/1311bfba8406ef2a2fabf3cb1fbd6f62/image-6.jpg)
iptables – Tables and Chains [csci 4430@vm-a]$ sudo iptables -t filter -A INPUT --protocol icmp --jump DROP [csci 4430@vm-a]$ sudo iptables –t filter –L Chain INPUT (policy ACCEPT) target prot opt source destination DROP icmp -- anywhere Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source [csci 4430@vm-a]$ _ destination Add a new rule to the INPUT chain. This entry shows that a new rule is added to the INPUT chain of the filter table successfully. 3/9/2017 The protocol of the packets in which this rule is interested is ICMP. If a packet (1) passes through the INPUT hook, and (2) is an ICMP packet, then the packet jumps to the target DROP – to discard the packet. CSC 4430 - LAB ON IPTABLES Page 6
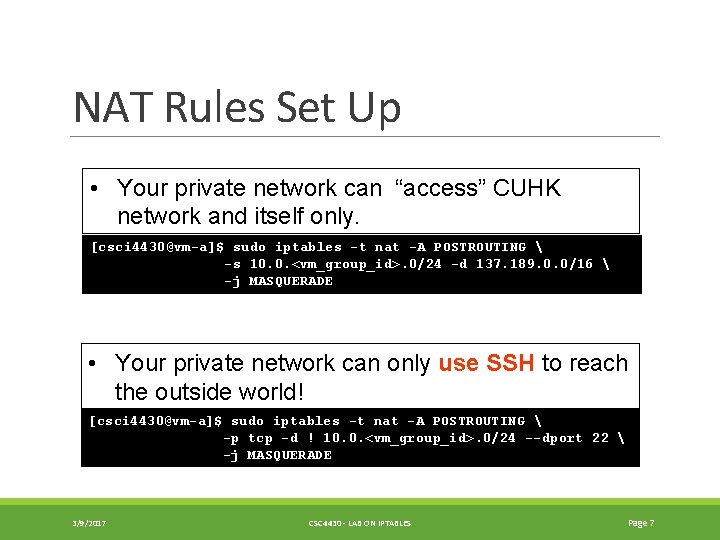
NAT Rules Set Up • Your private network can “access” CUHK network and itself only. [csci 4430@vm-a]$ sudo iptables -t nat -A POSTROUTING -s 10. 0. <vm_group_id>. 0/24 -d 137. 189. 0. 0/16 -j MASQUERADE • Your private network can only use SSH to reach the outside world! [csci 4430@vm-a]$ sudo iptables -t nat -A POSTROUTING -p tcp -d ! 10. 0. <vm_group_id>. 0/24 --dport 22 -j MASQUERADE 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 7
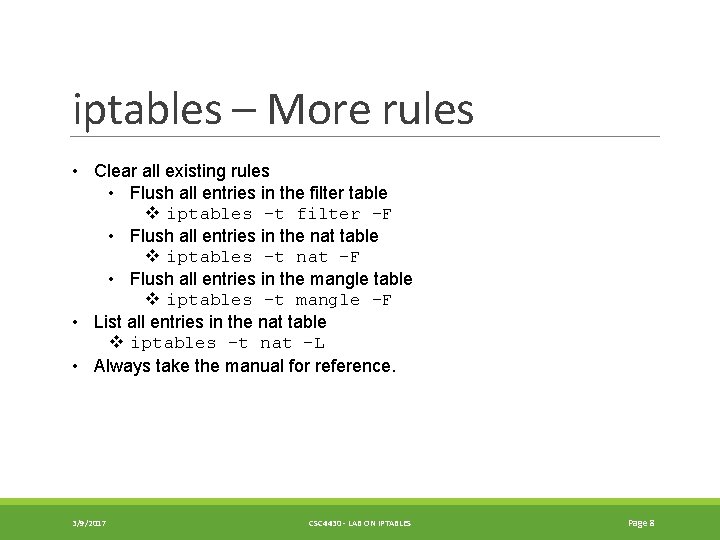
iptables – More rules • Clear all existing rules • Flush all entries in the filter table v iptables –t filter –F • Flush all entries in the nat table v iptables –t nat -F • Flush all entries in the mangle table v iptables –t mangle –F • List all entries in the nat table v iptables –t nat –L • Always take the manual for reference. 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 8
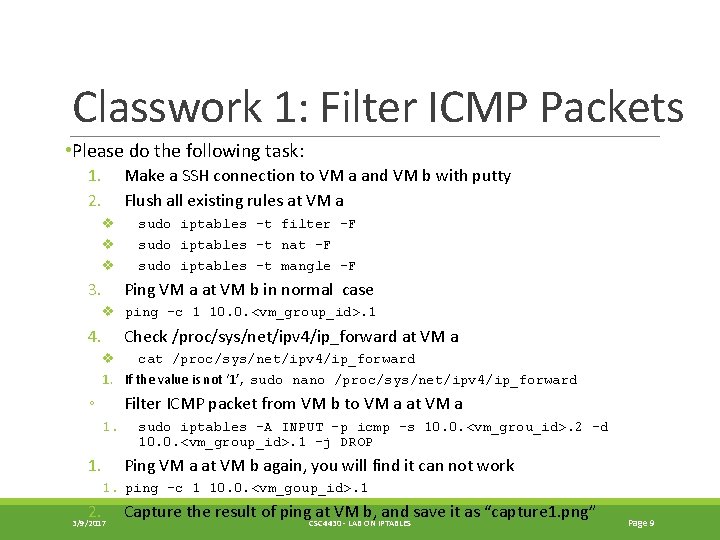
Classwork 1: Filter ICMP Packets • Please do the following task: 1. 2. Make a SSH connection to VM a and VM b with putty Flush all existing rules at VM a v v v 3. sudo iptables –t filter –F sudo iptables –t nat –F sudo iptables –t mangle –F Ping VM a at VM b in normal case v ping -c 1 10. 0. <vm_group_id>. 1 4. Check /proc/sys/net/ipv 4/ip_forward at VM a v cat /proc/sys/net/ipv 4/ip_forward 1. If the value is not ‘ 1’, sudo nano /proc/sys/net/ipv 4/ip_forward ◦ Filter ICMP packet from VM b to VM a at VM a 1. sudo iptables –A INPUT –p icmp –s 10. 0. <vm_grou_id>. 2 –d 10. 0. <vm_group_id>. 1 –j DROP Ping VM a at VM b again, you will find it can not work 1. ping -c 1 10. 0. <vm_goup_id>. 1 2. 3/9/2017 Capture the result of ping. CSC 4430 at VM b, and save it as “capture 1. png” - LAB ON IPTABLES Page 9
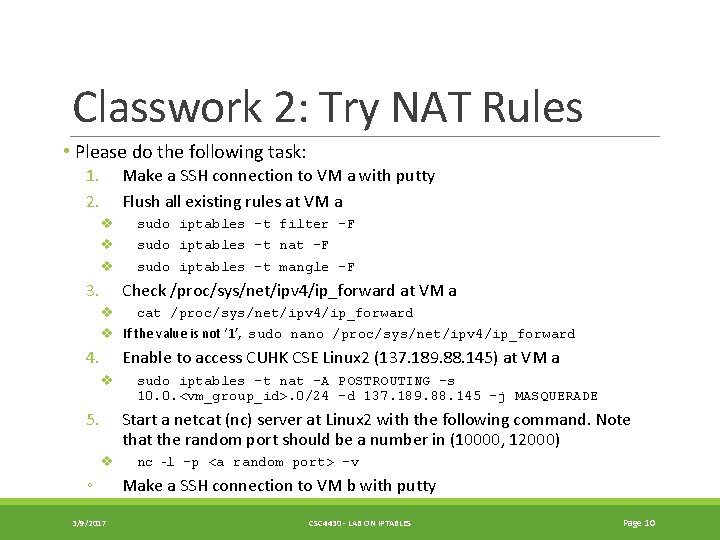
Classwork 2: Try NAT Rules • Please do the following task: 1. 2. Make a SSH connection to VM a with putty Flush all existing rules at VM a v v v 3. sudo iptables –t filter –F sudo iptables –t nat –F sudo iptables –t mangle –F Check /proc/sys/net/ipv 4/ip_forward at VM a v cat /proc/sys/net/ipv 4/ip_forward v If the value is not ‘ 1’, sudo nano /proc/sys/net/ipv 4/ip_forward 4. Enable to access CUHK CSE Linux 2 (137. 189. 88. 145) at VM a v 5. sudo iptables -t nat -A POSTROUTING -s 10. 0. <vm_group_id>. 0/24 -d 137. 189. 88. 145 -j MASQUERADE Start a netcat (nc) server at Linux 2 with the following command. Note that the random port should be a number in (10000, 12000) v ◦ 3/9/2017 nc –l –p <a random port> -v Make a SSH connection to VM b with putty CSC 4430 - LAB ON IPTABLES Page 10
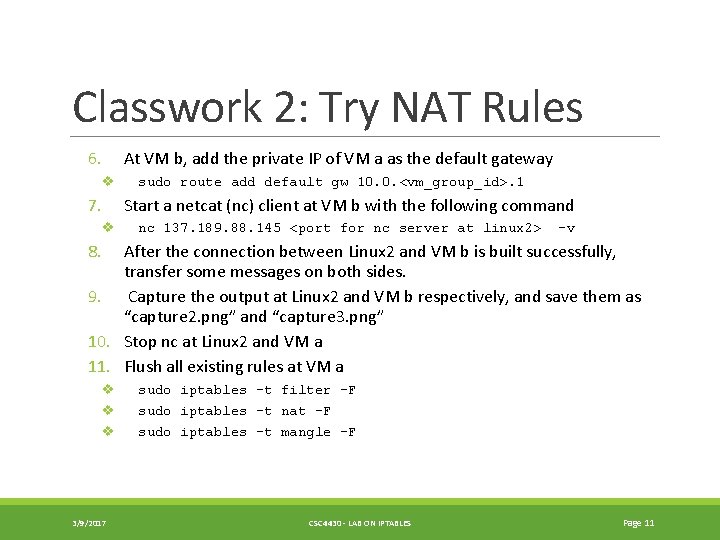
Classwork 2: Try NAT Rules 6. At VM b, add the private IP of VM a as the default gateway v 7. sudo route add default gw 10. 0. <vm_group_id>. 1 Start a netcat (nc) client at VM b with the following command v nc 137. 189. 88. 145 <port for nc server at linux 2> -v 8. After the connection between Linux 2 and VM b is built successfully, transfer some messages on both sides. 9. Capture the output at Linux 2 and VM b respectively, and save them as “capture 2. png” and “capture 3. png” 10. Stop nc at Linux 2 and VM a 11. Flush all existing rules at VM a v v v 3/9/2017 sudo iptables –t filter –F sudo iptables –t nat –F sudo iptables –t mangle –F CSC 4430 - LAB ON IPTABLES Page 11
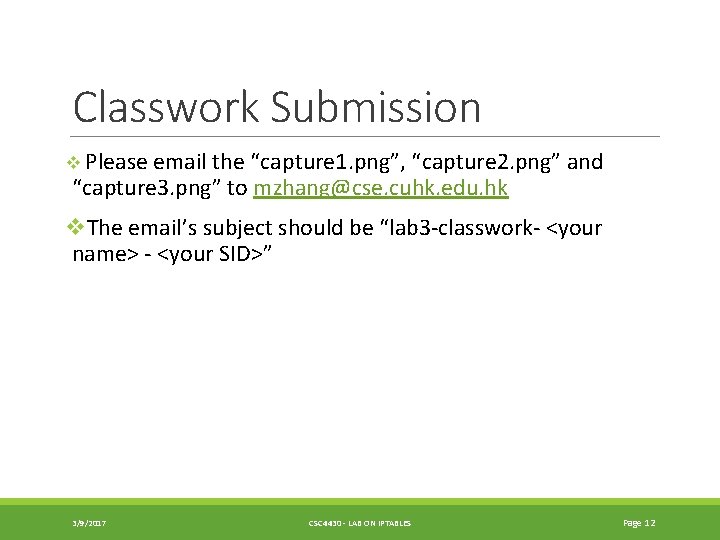
Classwork Submission v Please email the “capture 1. png”, “capture 2. png” and “capture 3. png” to mzhang@cse. cuhk. edu. hk v. The email’s subject should be “lab 3 -classwork- <your name> - <your SID>” 3/9/2017 CSC 4430 - LAB ON IPTABLES Page 12
- Slides: 12