Keep Your Enemies Close Distance Bounding Against Smartcard
Keep Your Enemies Close: Distance Bounding Against Smartcard Relay Attacks SAAR DRIMER A ND STEVEN J. MURDOCH COMPUTER LABORATORY, UNIVERSITY OF CAMBRIDGE PUBLISHED: 16 TH USENIX SECURITY SYMPOSIUM Presentation by: Scott Conrad
Relay attacks Cross between a man-in-the-middle and a replay attack Chess master analogy: how to beat a Grandmaster at chess without knowing the rules to chess Challenge two Grandmasters, G 1 and G 2, to a game of chess Forward any moves received from one Grandmaster to the other G 1 and G 2 will be playing each other without realizing it In the end you will either beat one Grandmaster or tie against both
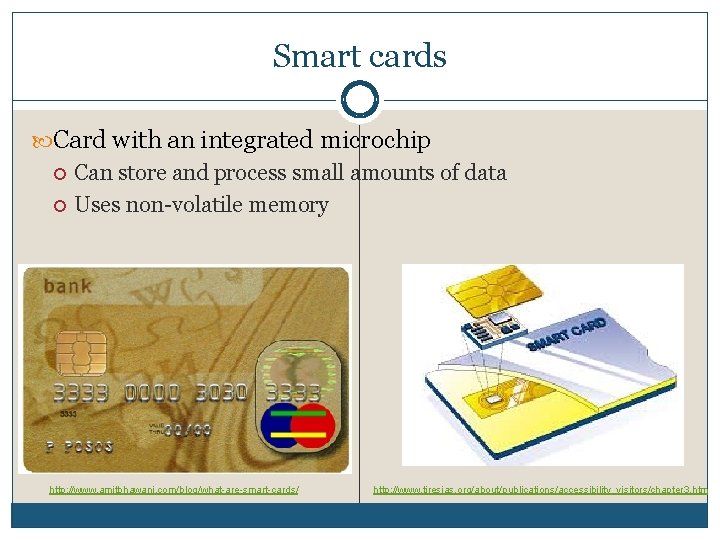
Smart cards Card with an integrated microchip Can store and process small amounts of data Uses non-volatile memory http: //www. amitbhawani. com/blog/what-are-smart-cards/ http: //www. tiresias. org/about/publications/accessibility_visitors/chapter 3. htm
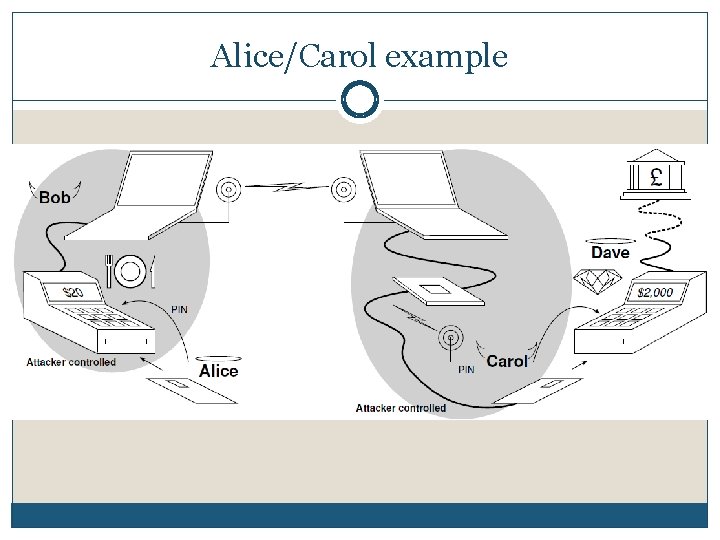
Alice/Carol example
Practical use of these attacks Alice/Carol example Alice (victim) uses her smart card at a terminal in a restaurant Waiter Bob (culprit) signals his accomplice Carol (culprit) that Alice is about to use the terminal Carol inserts her counterfeit card into a legitimate terminal The data from Carol’s terminal is relayed to Alice’s card The terminal is actually fake and is connected to a laptop instead of a bank When Alice enters her PIN number, the fake terminal records this and sends it to Carol When the attack is over, Alice gets a free meal but paid for Carol’s purchase
Another attack A thief discovers the PIN to a smart card and steals it Normally the card can either be used in the same place it was stolen, or it can be shipped elsewhere If the card is mailed it drastically shrinks the time window of when the card will be reported lost/stolen With this attack, one thief can steal the card and take it to his own fake terminal Another thief in another country can then use his counterfeit card as if it was the stolen card The time window is virtually unaffected
Why these attacks work No way to detect a mismatch between the data displayed on the terminal and the data authorized by the card Existing smartcard systems are tolerant to very high latencies A three second delay was introduced into transactions, and the attack was still successful
Why these attacks work Merchants generally do not handle smart cards Customers are often told to not to allow anyone but themselves to handle the cards Merchants rarely check the number on the card with the card number of the receipt Merchants that sell products at a low-margin have little incentive to help prevent attacks The costs of an attack are almost always borne by the customer and/or bank
EMV protocol Named after Europay, Mastercard, and Visa The primary protocol for debit and credit card payments in Europe UK’s ‘chip & pin’ system
Countermeasures/Defenses Tamper-resistant terminals Imposing additional timing constraints Hardware alterations Distance bounding
Tamper resistance terminals Terminals could be produced so that customers would be able to tell if they were tampered with Unrealistic in practice Tamper-resistant seals have been shown that they can be trivially bypassed As of May 2007 there were 304 VISA approved terminal designs from 88 vendors Consumers would have to be able to identify all of the designs as well as the signs of tampering This also assumes that criminals are unable to fabricate their own terminals
Addition timing restraints Assuming signals propagate at the speed of light, a 3 second delay gives an attack a 450 000 km range Terminals could be designed to ensure that a card responds to commands promptly Problems with this: The terminal’s behavior is very predictable An attacker could preemptively request details from the genuine card and then buffer them for the counterfeit card Over-clocking the genuine card by 1% can give around a 300 km distance
![Hardware alterations Use of an electronic attorney[2] A trusted device brought by the consumer Hardware alterations Use of an electronic attorney[2] A trusted device brought by the consumer](http://slidetodoc.com/presentation_image/b1c4d55510f4e9683a606678f03fa66d/image-14.jpg)
Hardware alterations Use of an electronic attorney[2] A trusted device brought by the consumer that acts as a “manin-the-middle defense” The user enters the PIN into the attorney, safeguarding the PIN The attorney then parses thought the data from the terminal allowing the user to verify the charge Why this is ineffective The increase complexity may keep banks from approving such devices Attackers may discourage their use explicitly or by making their use difficult
Hardware alterations Integrating a smartcard into a mobile/cell phone Uses a wireless, customer-controlled device Weaknesses Cell phones are targetable by malware The authors question whether wireless communication in this manner is secure enough
Distance bounding protocols It is possible for a terminal to determine the maximum distance a card is from it A signal’s round-trip-time between the terminal and the smartcard is measured This distance bounding is based on the Hancke- Kuhn protocol Was originally designed for ultra-wideband radio (UWB)
Distance bounding protocols Challenge-response The terminal sends out a challenge bit, and the card immediately responds with a response bit The response bit must arrive within a certain time The counterfeit card cannot randomly guess the response bit ahead of time A random guess has a 50% chance of being correct 64 consecutive guesses have about a 1 in 226 of being correct
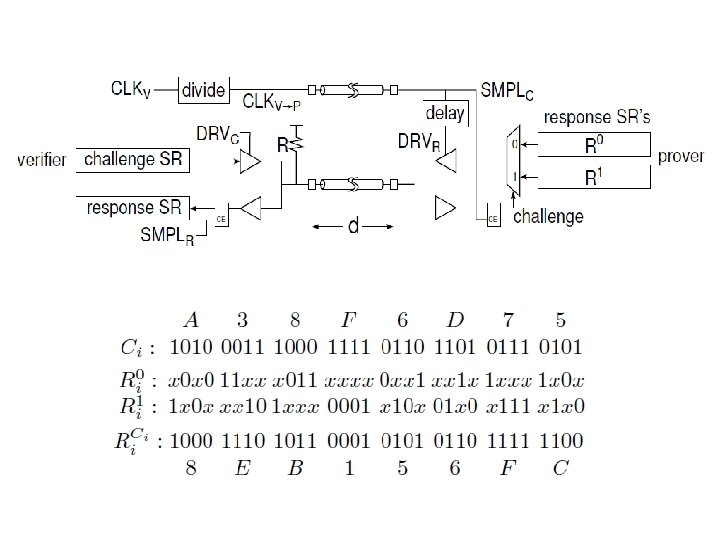
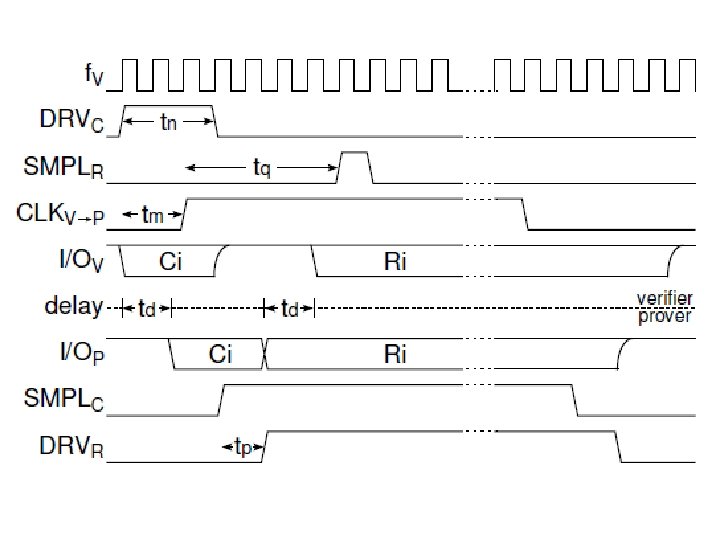
Distance bounding protocols
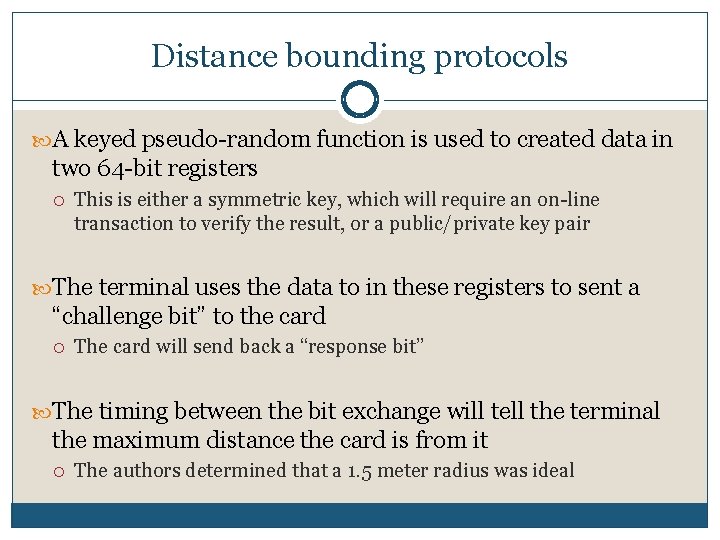
Distance bounding protocols A keyed pseudo-random function is used to created data in two 64 -bit registers This is either a symmetric key, which will require an on-line transaction to verify the result, or a public/private key pair The terminal uses the data to in these registers to sent a “challenge bit” to the card The card will send back a “response bit” The timing between the bit exchange will tell the terminal the maximum distance the card is from it The authors determined that a 1. 5 meter radius was ideal
Attacks on Distance Bounding Replay attack By including a nonce (or timestamp) into the calculation of the pseudo-random function, this can be avoided Early bit detection and deferred bit signaling With expensive equipment, the attack can read the challenge bit early and send the response bit late At best this will expand the radius, but only a few meters at most
Costs to Implement Few circuitry changes to the smartcard Costs are expected to be minor More liberal changes to the terminals Overall, the test case only used 37 flip-flops and 93 lookup tables This was for both the smartcard and the terminal
Criticisms Authors note that the distance bounding protocol lacks non-repudiation The paper gives no actual cost estimates To fully understand the protocol it requires being well versed in computer architecture Was never actually implemented, just simulated
References 1. Saar Drimer; Steven J. Murdoch. “Keep Your Enemies Close: Distance Bounding Against Smartcard Relay Attacks”. 16 th USENIX Security Symposium. 2007 2. Iulia Ion; Boris Dragovic. “Don’t trust POS terminals! Verify in-shop payments with your phone”. 3. “Smart card”. Wikipedia. http: //en. wikipedia. org/wiki/Smart_card
- Slides: 25