Introducing Cryptography For Voting Introduction to Cryptography for
- Slides: 13
Introducing Cryptography For Voting
Introduction to Cryptography for voting 617 Cryptography and Security Vanessa Teague vteague@csse. unimelb. edu. au
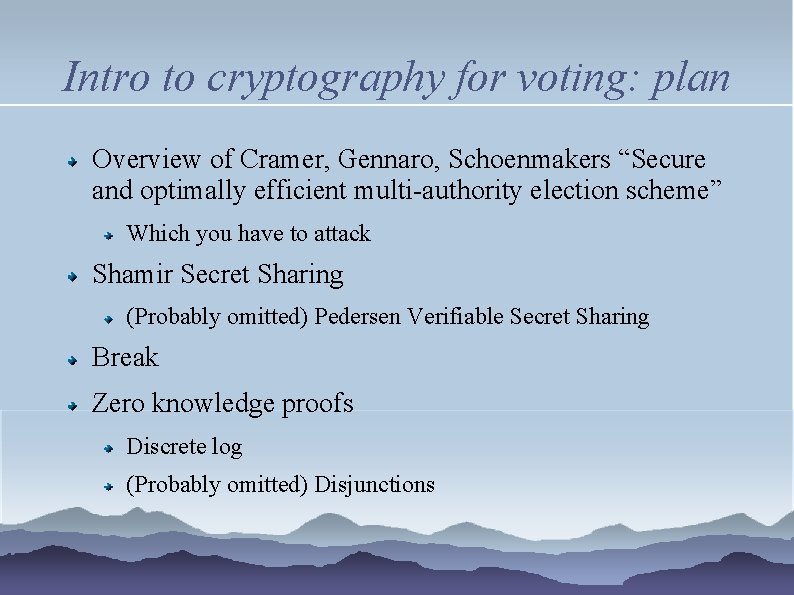
Intro to cryptography for voting: plan Overview of Cramer, Gennaro, Schoenmakers “Secure and optimally efficient multi-authority election scheme” Which you have to attack Shamir Secret Sharing (Probably omitted) Pedersen Verifiable Secret Sharing Break Zero knowledge proofs Discrete log (Probably omitted) Disjunctions
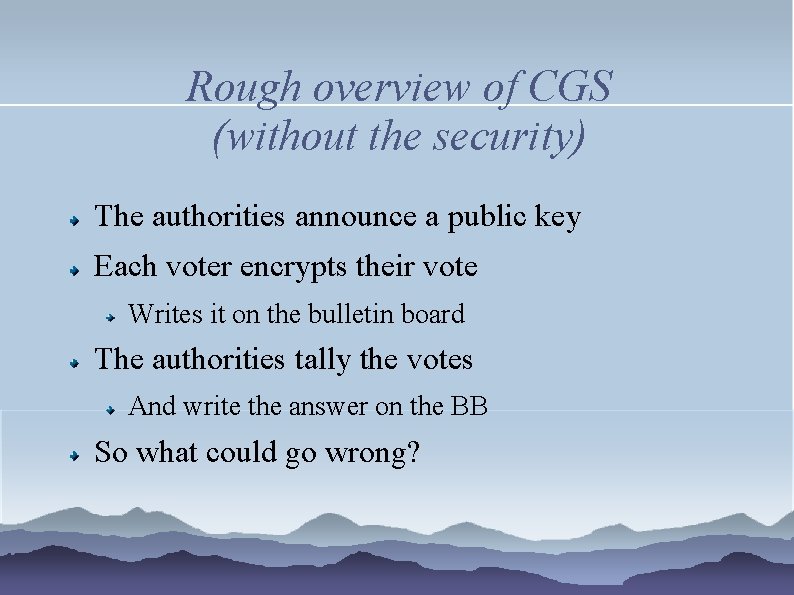
Rough overview of CGS (without the security) The authorities announce a public key Each voter encrypts their vote Writes it on the bulletin board The authorities tally the votes And write the answer on the BB So what could go wrong?
What could go wrong (a. k. a. why all those ZKPs? )
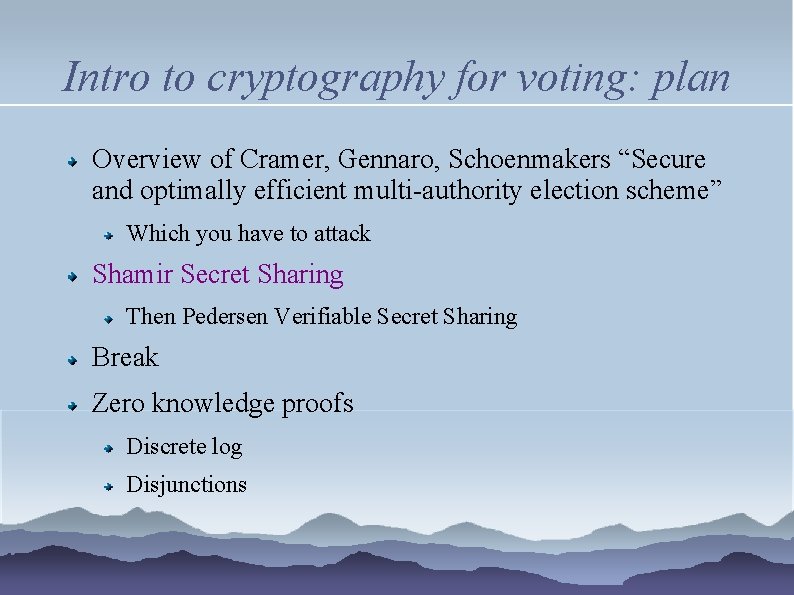
Intro to cryptography for voting: plan Overview of Cramer, Gennaro, Schoenmakers “Secure and optimally efficient multi-authority election scheme” Which you have to attack Shamir Secret Sharing Then Pedersen Verifiable Secret Sharing Break Zero knowledge proofs Discrete log Disjunctions
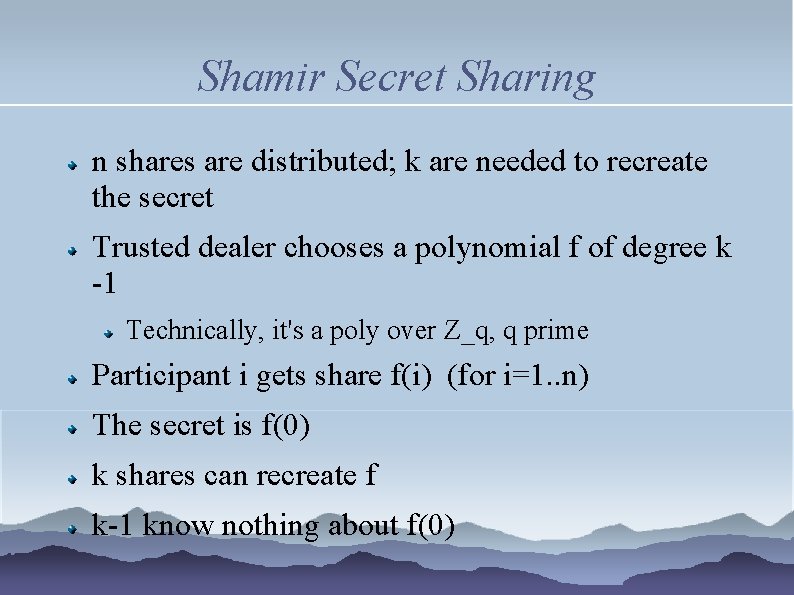
Shamir Secret Sharing n shares are distributed; k are needed to recreate the secret Trusted dealer chooses a polynomial f of degree k -1 Technically, it's a poly over Z_q, q prime Participant i gets share f(i) (for i=1. . n) The secret is f(0) k shares can recreate f k-1 know nothing about f(0)
Pedersen Verifiable Secret Sharing Avoiding a trusted dealer for the shares Everyone needs to know at the end of the distributed dealing protocol that they got a valid share Commitments: background on next slide
Commitments Commit to a message m using a (randomised) function C(m, r) Open C(m, r) by provably revealing m e. g. by revealing r C should be Binding, i. e. you can't open C with m' ≠ m Private, i. e. nobody can compute m from C
Intro to cryptography for voting: plan Overview of Cramer, Gennaro, Schoenmakers “Secure and optimally efficient multi-authority election scheme” Which you have to attack Shamir Secret Sharing Then Pedersen Verifiable Secret Sharing Break Zero knowledge proofs Discrete log Disjunctions
Intro to cryptography for voting: plan Overview of Cramer, Gennaro, Schoenmakers “Secure and optimally efficient multi-authority election scheme” Which you have to attack Shamir Secret Sharing Then Pedersen Verifiable Secret Sharing Break Zero knowledge proofs Discrete log Disjunctions
Zero knowledge proof of equality of discrete log Fig 1 of CGS. The Prover is trying to convince the verifier that there exists α s. t. x = gα and y = hα mod p Rough informal requirements: Completeness: A truthful prover always succeeds Soundness: A cheating prover usually fails (honest verifier) Zero knowledge: If the verifier follows the protocol, it learns nothing but the truth of the fact.
ZKPs for disjunctions Exercise: In countries where voting is compulsory, the right to abstain secretly is important. Extend CGS's proof of vote validity (Fig 3, p. 9) into a proof that your vote is either valid or an abstention (v=0).