2 12 Cryptography Javascript Cryptography Backend Cryptography Frontend
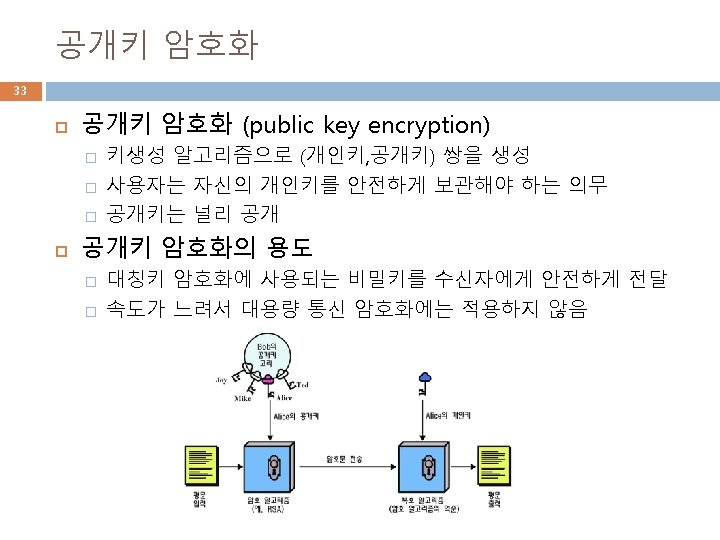
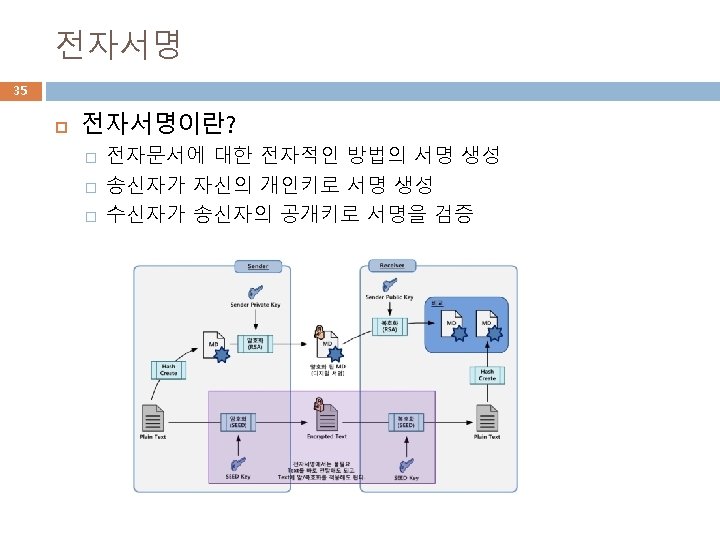
2 12. Cryptography 자바스크립트 암호(Javascript Cryptography) 서버측 암호 (Backend Cryptography) 클라이언트측 암호 (Frontend Cryptography) 해쉬함수, 대칭키암호, 공개키암호, 전자서명, 인증서 등
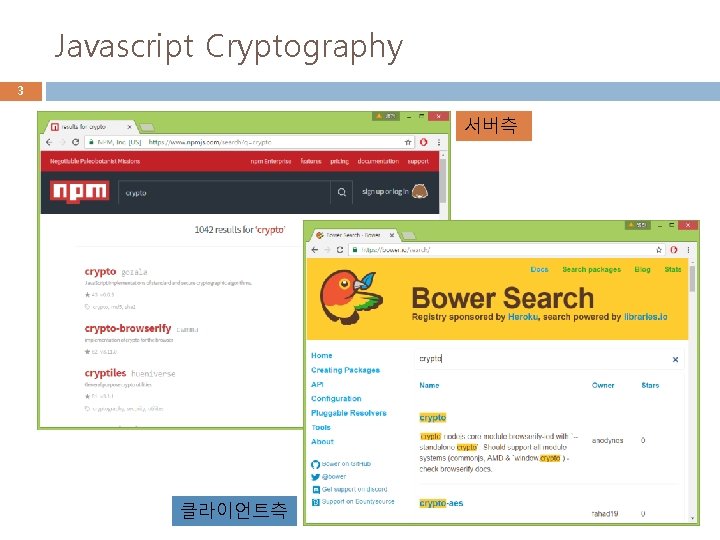
Javascript Cryptography 3 서버측 클라이언트측
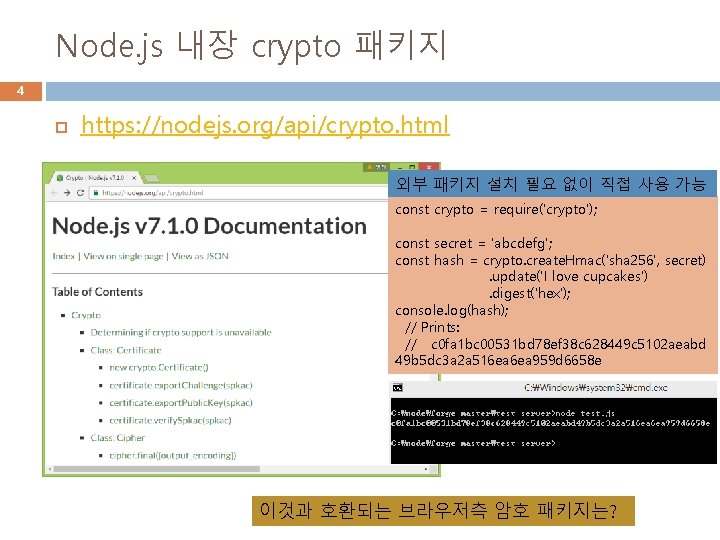
Node. js 내장 crypto 패키지 4 https: //nodejs. org/api/crypto. html 외부 패키지 설치 필요 없이 직접 사용 가능 const crypto = require('crypto'); const secret = 'abcdefg'; const hash = crypto. create. Hmac('sha 256', secret). update('I love cupcakes'). digest('hex'); console. log(hash); // Prints: // c 0 fa 1 bc 00531 bd 78 ef 38 c 628449 c 5102 aeabd 49 b 5 dc 3 a 2 a 516 ea 959 d 6658 e 이것과 호환되는 브라우저측 암호 패키지는?

Node-forge API 7 사용 방법은 온라인 API 참조 � https: //www. npmjs. com/package/node-forge 예: SHA-1 해쉬 함수 사용법
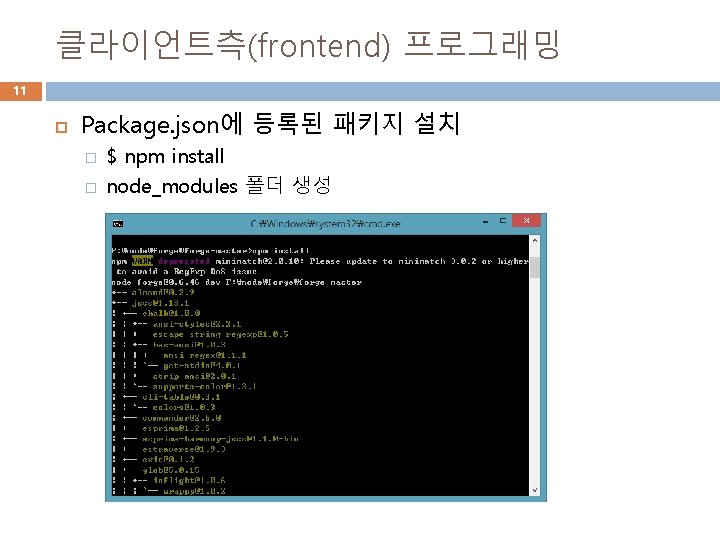
서버측(backend) 프로그래밍 8 Node-forge 패키지 설치 � � $ npm install node-forge node_modules 폴더에 node-forge 설치 서버 프로그래밍에 활용 � � Require를 이용하여 패키지를 불러와서 사용 var forge = require(‘node-forge’);
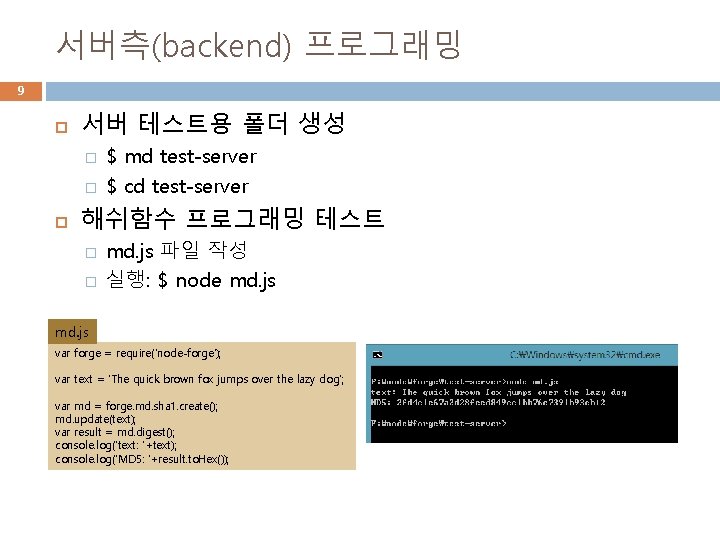
서버측(backend) 프로그래밍 9 서버 테스트용 폴더 생성 � � $ md test-server $ cd test-server 해쉬함수 프로그래밍 테스트 � � md. js 파일 작성 실행: $ node md. js var forge = require('node-forge'); var text = 'The quick brown fox jumps over the lazy dog'; var md = forge. md. sha 1. create(); md. update(text); var result = md. digest(); console. log('text: '+text); console. log('MD 5: '+result. to. Hex());

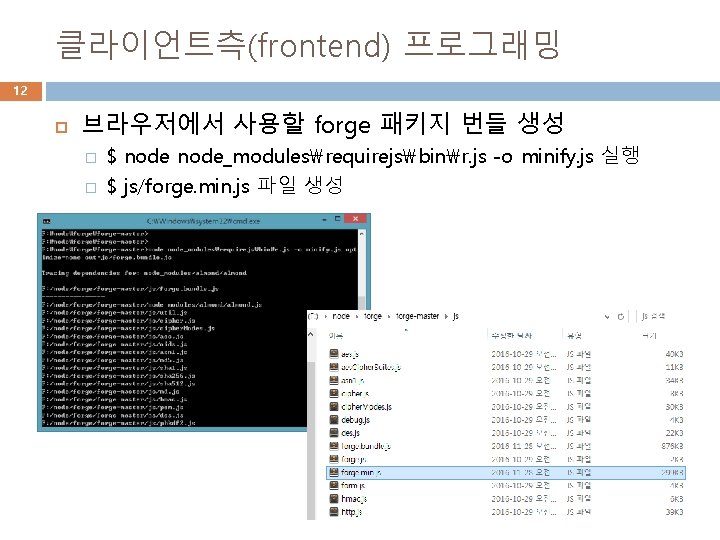
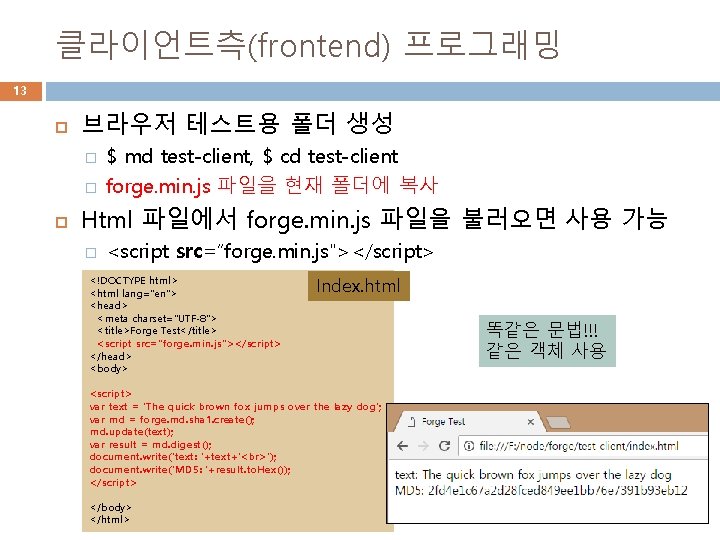
클라이언트측(frontend) 프로그래밍 13 브라우저 테스트용 폴더 생성 � � $ md test-client, $ cd test-client forge. min. js 파일을 현재 폴더에 복사 Html 파일에서 forge. min. js 파일을 불러오면 사용 가능 � <script src=“forge. min. js"></script> <!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> <title>Forge Test</title> <script src="forge. min. js"></script> </head> <body> Index. html <script> var text = 'The quick brown fox jumps over the lazy dog'; var md = forge. md. sha 1. create(); md. update(text); var result = md. digest(); document. write('text: '+text+' '); document. write('MD 5: '+result. to. Hex()); </script> </body> </html> 똑같은 문법!!! 같은 객체 사용
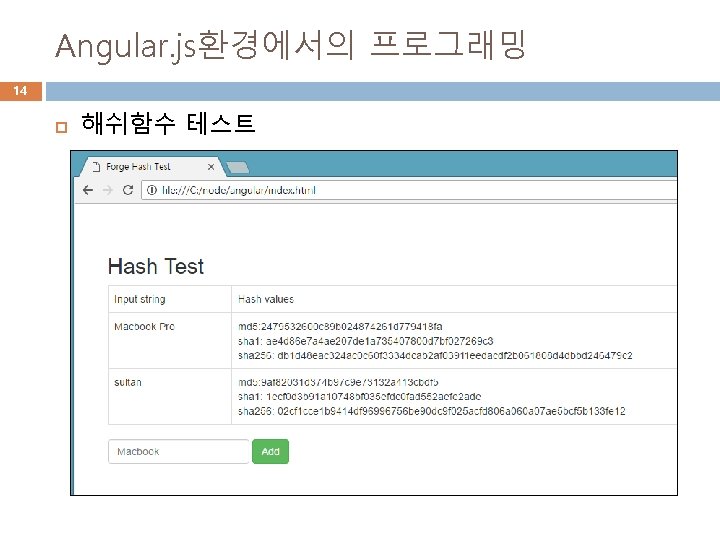
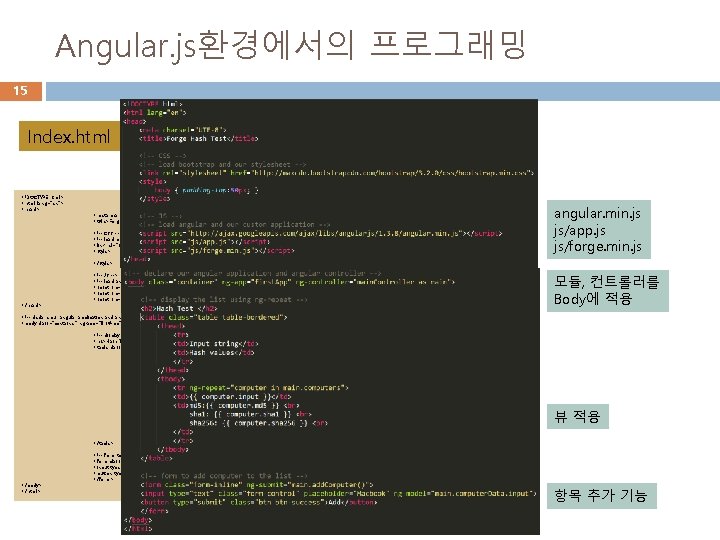
Angular. js환경에서의 프로그래밍 15 Index. html <!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> <title>Forge Hash Test</title> <!-- CSS --> <!-- load bootstrap and our stylesheet --> <link rel="stylesheet" href="http: //maxcdn. bootstrapcdn. com/bootstrap/3. 2. 0/css/bootstrap. min. css"> <style> body { padding-top: 50 px; } </style> </head> <!-- JS --> <!-- load angular and our custom application --> <script src="http: //ajax. googleapis. com/ajax/libs/angularjs/1. 3. 8/angular. min. js"></script> <script src="js/app. js"></script> <script src="js/forge. min. js"></script> angular. min. js js/app. js js/forge. min. js 모듈, 컨트롤러를 Body에 적용 <!-- declare our angular application and angular controller --> <body class="container" ng-app="first. App" ng-controller="main. Controller as main"> <!-- display the list using ng-repeat --> <h 2>Hash Test </h 2> <table class="table-bordered"> <thead> </thead> <tbody> </table> </body> </html> </tbody> <tr> <td>Input string</td> <td>Hash values</td> </tr> <tr ng-repeat="computer in main. computers"> <td>{{ computer. input }}</td> <td>md 5: {{ computer. md 5 }} sha 1: {{ computer. sha 1 }} sha 256: {{ computer. sha 256 }} </td> </tr> 뷰 적용 <!-- form to add computer to the list --> <form class="form-inline" ng-submit="main. add. Computer()"> <input type="text" class="form-control" placeholder="Macbook" ng-model="main. computer. Data. input"> <button type="submit" class="btn btn-success">Add</button> </form> 항목 추가 기능
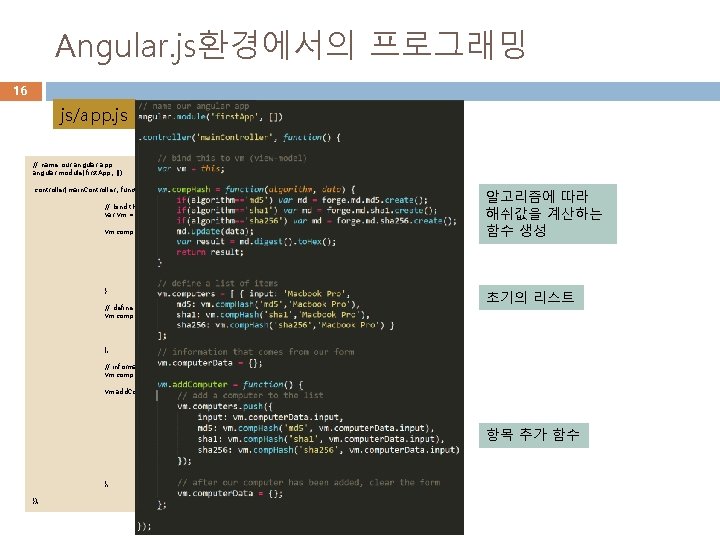
Angular. js환경에서의 프로그래밍 16 js/app. js // name our angular app angular. module('first. App', []). controller('main. Controller', function() { // bind this to vm (view-model) var vm = this; vm. comp. Hash = function(algorithm, data) { if(algorithm=='md 5') var md = forge. md 5. create(); if(algorithm=='sha 1') var md = forge. md. sha 1. create(); if(algorithm=='sha 256') var md = forge. md. sha 256. create(); md. update(data); var result = md. digest(). to. Hex(); return result; } // define a list of items vm. computers = [ { input: 'Macbook Pro', md 5: vm. comp. Hash('md 5', 'Macbook Pro'), sha 1: vm. comp. Hash('sha 1', 'Macbook Pro'), sha 256: vm. comp. Hash('sha 256', 'Macbook Pro') } ]; 알고리즘에 따라 해쉬값을 계산하는 함수 생성 초기의 리스트 // information that comes from our form vm. computer. Data = {}; vm. add. Computer = function() { // add a computer to the list vm. computers. push({ input: vm. computer. Data. input, md 5: vm. comp. Hash('md 5', vm. computer. Data. input), sha 1: vm. comp. Hash('sha 1', vm. computer. Data. input), sha 256: vm. comp. Hash('sha 256', vm. computer. Data. input) }); }; }); // after our computer has been added, clear the form vm. computer. Data = {}; 항목 추가 함수
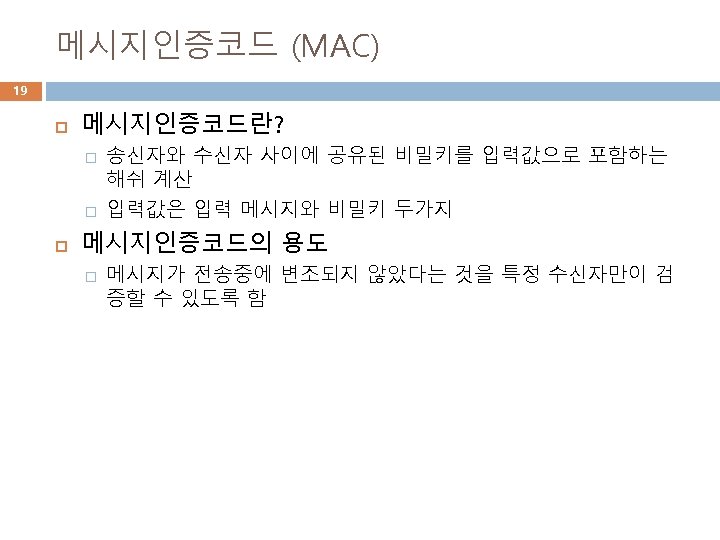
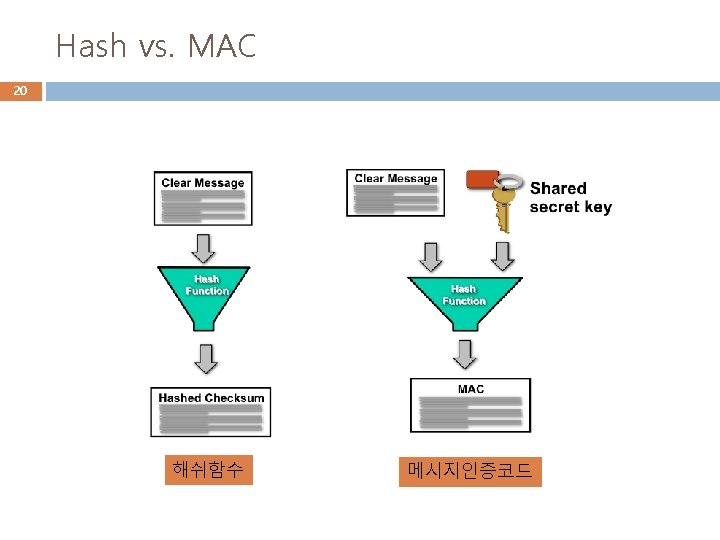
17 Hash and MAC
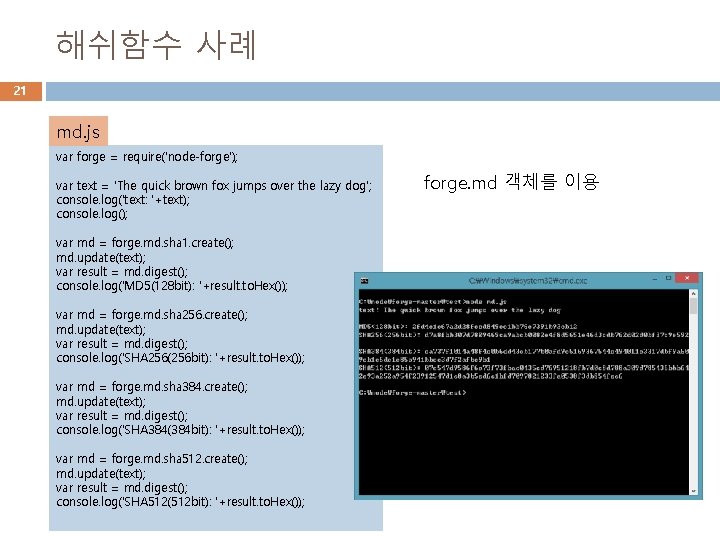
해쉬함수 사례 21 md. js var forge = require('node-forge'); var text = 'The quick brown fox jumps over the lazy dog'; console. log('text: '+text); console. log(); var md = forge. md. sha 1. create(); md. update(text); var result = md. digest(); console. log('MD 5(128 bit): '+result. to. Hex()); var md = forge. md. sha 256. create(); md. update(text); var result = md. digest(); console. log('SHA 256(256 bit): '+result. to. Hex()); var md = forge. md. sha 384. create(); md. update(text); var result = md. digest(); console. log('SHA 384(384 bit): '+result. to. Hex()); var md = forge. md. sha 512. create(); md. update(text); var result = md. digest(); console. log('SHA 512(512 bit): '+result. to. Hex()); forge. md 객체를 이용
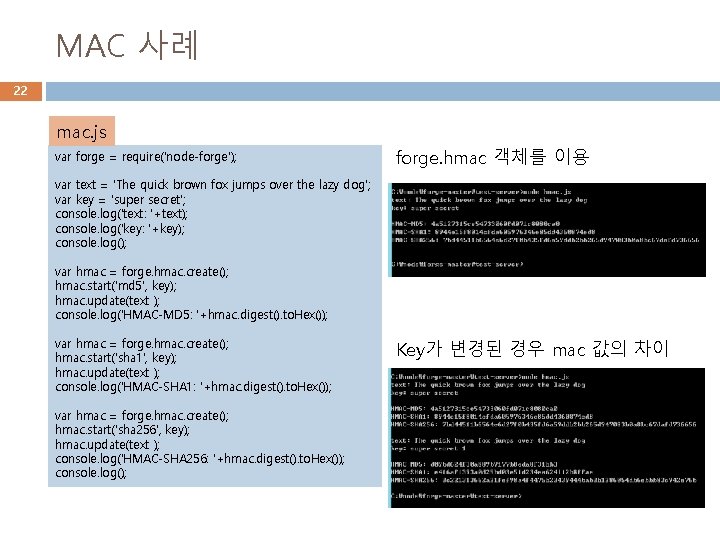
MAC 사례 22 mac. js var forge = require('node-forge'); forge. hmac 객체를 이용 var text = 'The quick brown fox jumps over the lazy dog'; var key = 'super secret'; console. log('text: '+text); console. log('key: '+key); console. log(); var hmac = forge. hmac. create(); hmac. start('md 5', key); hmac. update(text ); console. log('HMAC-MD 5: '+hmac. digest(). to. Hex()); var hmac = forge. hmac. create(); hmac. start('sha 1', key); hmac. update(text ); console. log('HMAC-SHA 1: '+hmac. digest(). to. Hex()); var hmac = forge. hmac. create(); hmac. start('sha 256', key); hmac. update(text ); console. log('HMAC-SHA 256: '+hmac. digest(). to. Hex()); console. log(); Key가 변경된 경우 mac 값의 차이
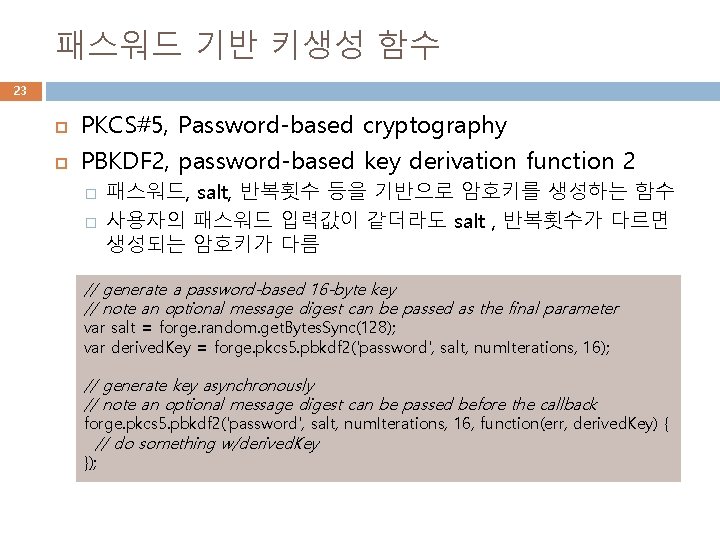
패스워드 기반 키생성 함수 23 PKCS#5, Password-based cryptography PBKDF 2, password-based key derivation function 2 � � 패스워드, salt, 반복횟수 등을 기반으로 암호키를 생성하는 함수 사용자의 패스워드 입력값이 같더라도 salt , 반복횟수가 다르면 생성되는 암호키가 다름 // generate a password-based 16 -byte key // note an optional message digest can be passed as the final parameter var salt = forge. random. get. Bytes. Sync(128); var derived. Key = forge. pkcs 5. pbkdf 2('password', salt, num. Iterations, 16); // generate key asynchronously // note an optional message digest can be passed before the callback forge. pkcs 5. pbkdf 2('password', salt, num. Iterations, 16, function(err, derived. Key) { // do something w/derived. Key });
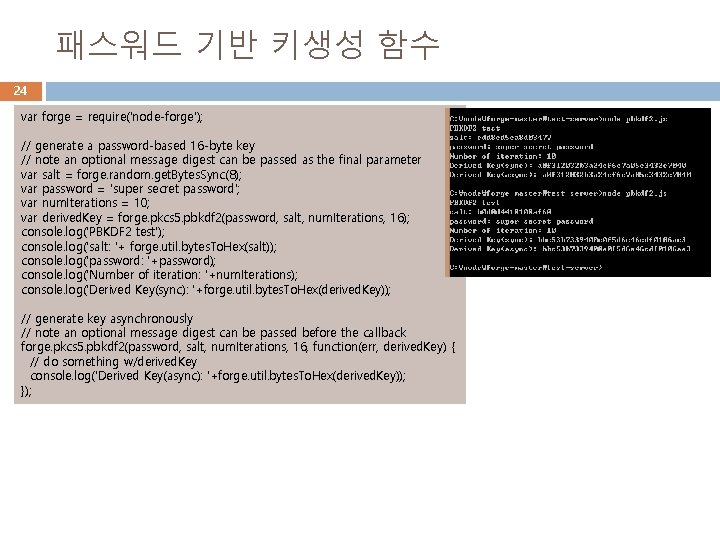
패스워드 기반 키생성 함수 24 var forge = require('node-forge'); // generate a password-based 16 -byte key // note an optional message digest can be passed as the final parameter var salt = forge. random. get. Bytes. Sync(8); var password = 'super secret password'; var num. Iterations = 10; var derived. Key = forge. pkcs 5. pbkdf 2(password, salt, num. Iterations, 16); console. log('PBKDF 2 test'); console. log('salt: '+ forge. util. bytes. To. Hex(salt)); console. log('password: '+password); console. log('Number of iteration: '+num. Iterations); console. log('Derived Key(sync): '+forge. util. bytes. To. Hex(derived. Key)); // generate key asynchronously // note an optional message digest can be passed before the callback forge. pkcs 5. pbkdf 2(password, salt, num. Iterations, 16, function(err, derived. Key) { // do something w/derived. Key console. log('Derived Key(async): '+forge. util. bytes. To. Hex(derived. Key)); });
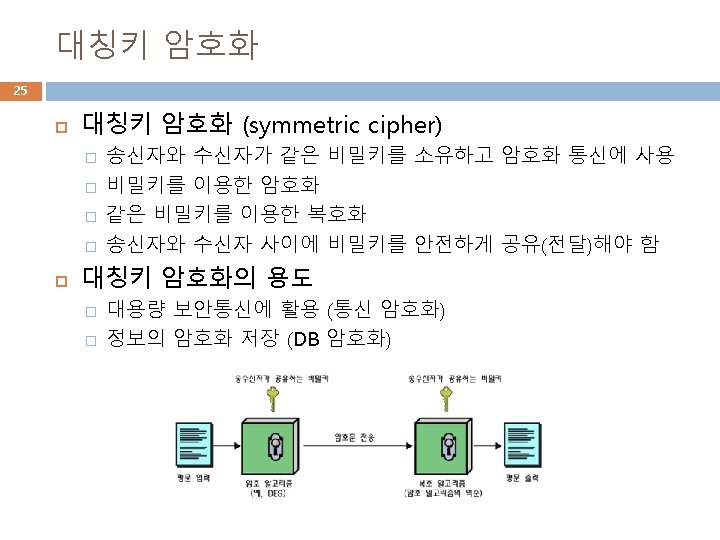
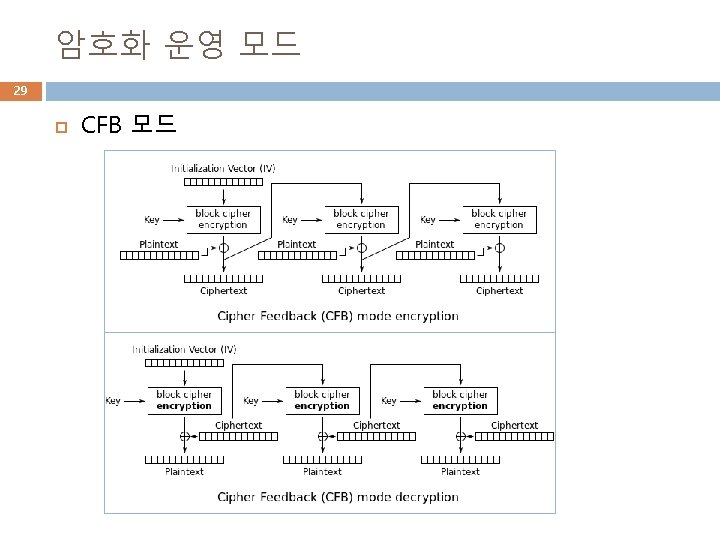
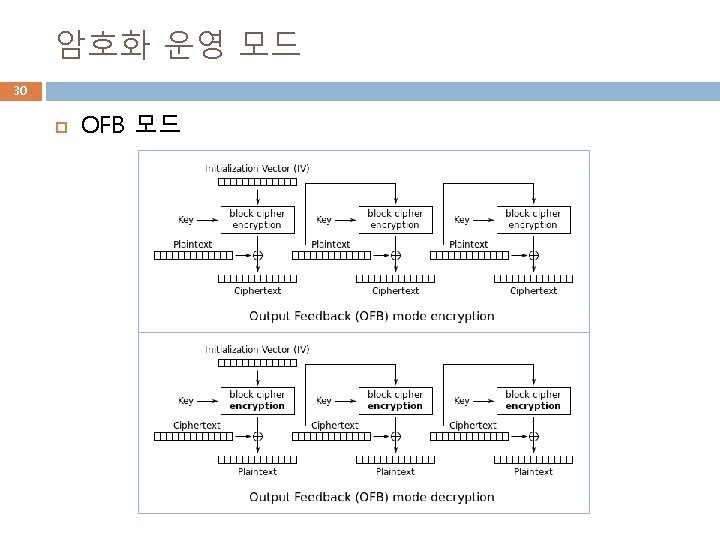
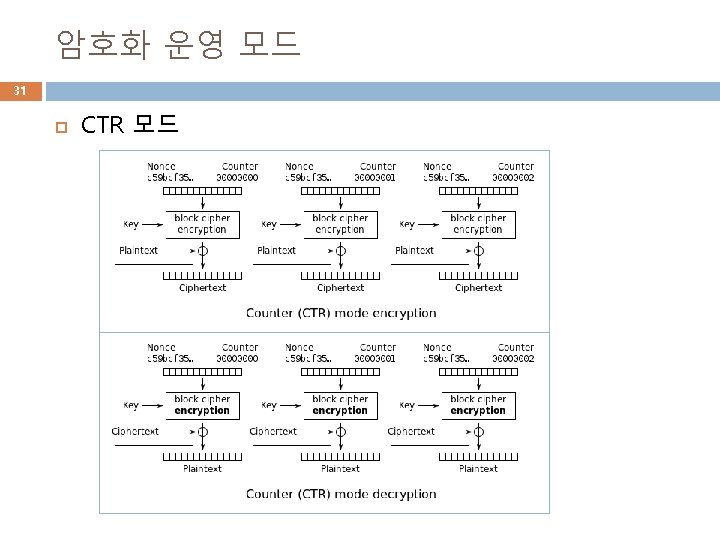
Forge 에서 제공하는 대칭키 암호 26 암호 알고리즘: AES, DES, 3 DES 암호화 운영 모드: ECB, CBC, CFB, OFB, CTR, GCM 사용 가능한 키워드 � � � AES-ECB, AES-CBC, AES-CFB, AES-OFB, AES-CTR, AES-GCM 3 DES-ECB, 3 DES-CBC DES-ECB, DES-CBC


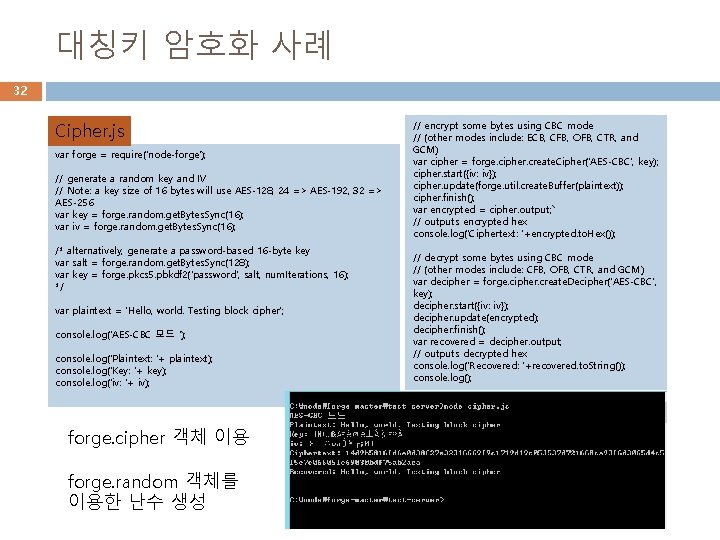
대칭키 암호화 사례 32 Cipher. js var forge = require('node-forge'); // generate a random key and IV // Note: a key size of 16 bytes will use AES-128, 24 => AES-192, 32 => AES-256 var key = forge. random. get. Bytes. Sync(16); var iv = forge. random. get. Bytes. Sync(16); /* alternatively, generate a password-based 16 -byte key var salt = forge. random. get. Bytes. Sync(128); var key = forge. pkcs 5. pbkdf 2('password', salt, num. Iterations, 16); */ var plaintext = 'Hello, world. Testing block cipher'; console. log('AES-CBC 모드 '); console. log('Plaintext: '+ plaintext); console. log('Key: '+ key); console. log('iv: '+ iv); forge. cipher 객체 이용 forge. random 객체를 이용한 난수 생성 // encrypt some bytes using CBC mode // (other modes include: ECB, CFB, OFB, CTR, and GCM) var cipher = forge. cipher. create. Cipher('AES-CBC', key); cipher. start({iv: iv}); cipher. update(forge. util. create. Buffer(plaintext)); cipher. finish(); var encrypted = cipher. output; ` // outputs encrypted hex console. log('Ciphertext: '+encrypted. to. Hex()); // decrypt some bytes using CBC mode // (other modes include: CFB, OFB, CTR, and GCM) var decipher = forge. cipher. create. Decipher('AES-CBC', key); decipher. start({iv: iv}); decipher. update(encrypted); decipher. finish(); var recovered = decipher. output; // outputs decrypted hex console. log('Recovered: '+recovered. to. String()); console. log();
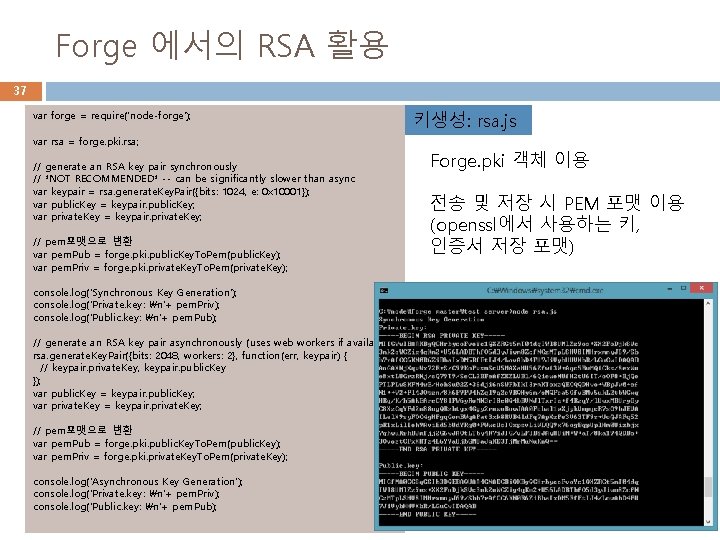
Forge 에서의 RSA 활용 37 var forge = require('node-forge'); var rsa = forge. pki. rsa; // generate an RSA key pair synchronously // *NOT RECOMMENDED* -- can be significantly slower than async var keypair = rsa. generate. Key. Pair({bits: 1024, e: 0 x 10001}); var public. Key = keypair. public. Key; var private. Key = keypair. private. Key; // pem포맷으로 변환 var pem. Pub = forge. pki. public. Key. To. Pem(public. Key); var pem. Priv = forge. pki. private. Key. To. Pem(private. Key); console. log('Synchronous Key Generation'); console. log('Private. key: n'+ pem. Priv); console. log('Public. key: n'+ pem. Pub); // generate an RSA key pair asynchronously (uses web workers if available) rsa. generate. Key. Pair({bits: 2048, workers: 2}, function(err, keypair) { // keypair. private. Key, keypair. public. Key }); var public. Key = keypair. public. Key; var private. Key = keypair. private. Key; // pem포맷으로 변환 var pem. Pub = forge. pki. public. Key. To. Pem(public. Key); var pem. Priv = forge. pki. private. Key. To. Pem(private. Key); console. log('Asynchronous Key Generation'); console. log('Private. key: n'+ pem. Priv); console. log('Public. key: n'+ pem. Pub); 키생성: rsa. js Forge. pki 객체 이용 전송 및 저장 시 PEM 포맷 이용 (openssl에서 사용하는 키, 인증서 저장 포맷)
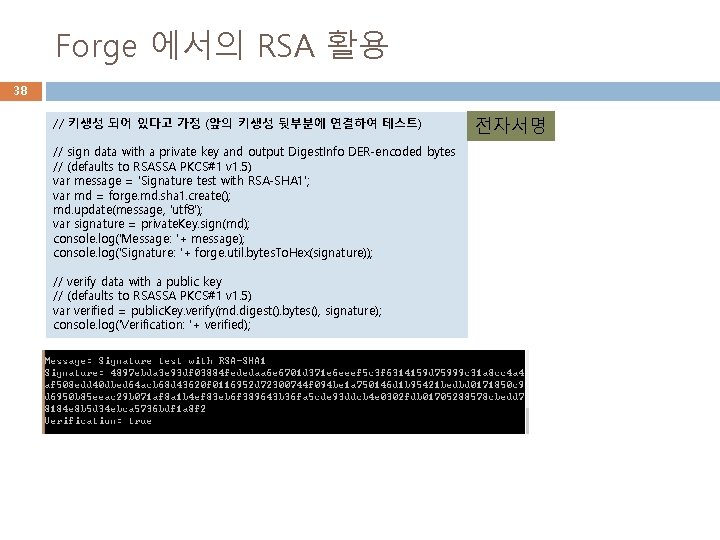
Forge 에서의 RSA 활용 38 // 키생성 되어 있다고 가정 (앞의 키생성 뒷부분에 연결하여 테스트) // sign data with a private key and output Digest. Info DER-encoded bytes // (defaults to RSASSA PKCS#1 v 1. 5) var message = 'Signature test with RSA-SHA 1'; var md = forge. md. sha 1. create(); md. update(message, 'utf 8'); var signature = private. Key. sign(md); console. log('Message: '+ message); console. log('Signature: '+ forge. util. bytes. To. Hex(signature)); // verify data with a public key // (defaults to RSASSA PKCS#1 v 1. 5) var verified = public. Key. verify(md. digest(). bytes(), signature); console. log('Verification: '+ verified); 전자서명
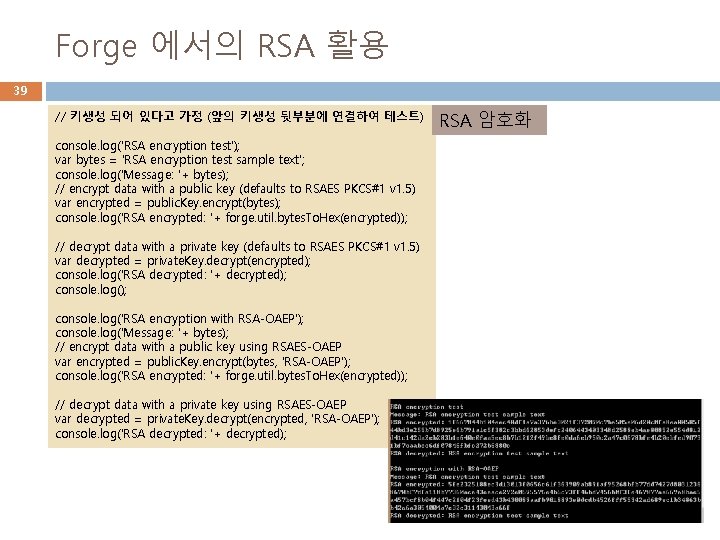
Forge 에서의 RSA 활용 39 // 키생성 되어 있다고 가정 (앞의 키생성 뒷부분에 연결하여 테스트) console. log('RSA encryption test'); var bytes = 'RSA encryption test sample text'; console. log('Message: '+ bytes); // encrypt data with a public key (defaults to RSAES PKCS#1 v 1. 5) var encrypted = public. Key. encrypt(bytes); console. log('RSA encrypted: '+ forge. util. bytes. To. Hex(encrypted)); // decrypt data with a private key (defaults to RSAES PKCS#1 v 1. 5) var decrypted = private. Key. decrypt(encrypted); console. log('RSA decrypted: '+ decrypted); console. log('RSA encryption with RSA-OAEP'); console. log('Message: '+ bytes); // encrypt data with a public key using RSAES-OAEP var encrypted = public. Key. encrypt(bytes, 'RSA-OAEP'); console. log('RSA encrypted: '+ forge. util. bytes. To. Hex(encrypted)); // decrypt data with a private key using RSAES-OAEP var decrypted = private. Key. decrypt(encrypted, 'RSA-OAEP'); console. log('RSA decrypted: '+ decrypted); RSA 암호화
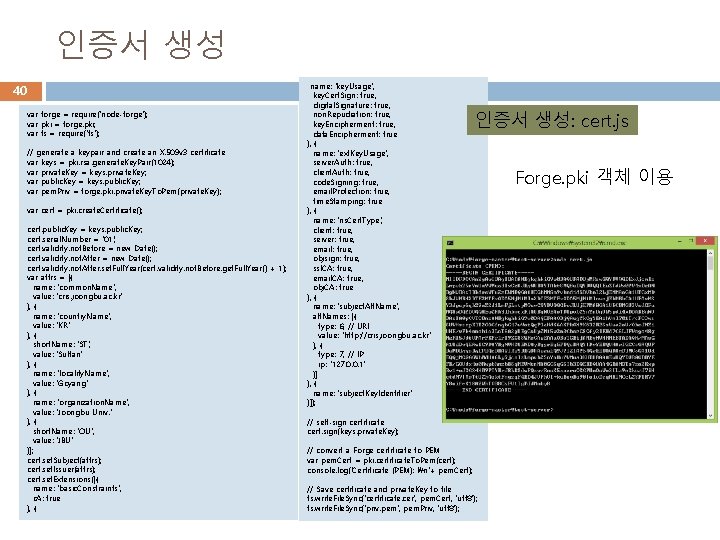
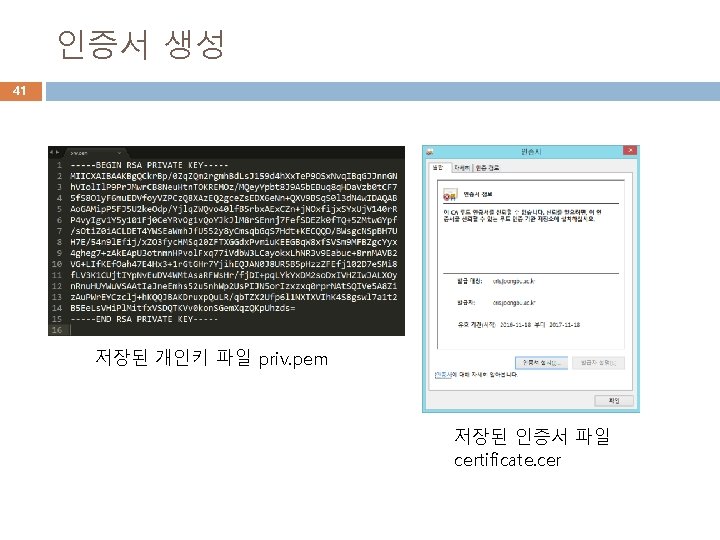
인증서 생성 40 var forge = require('node-forge'); var pki = forge. pki; var fs = require('fs'); // generate a keypair and create an X. 509 v 3 certificate var keys = pki. rsa. generate. Key. Pair(1024); var private. Key = keys. private. Key; var public. Key = keys. public. Key; var pem. Priv = forge. pki. private. Key. To. Pem(private. Key); var cert = pki. create. Certificate(); cert. public. Key = keys. public. Key; cert. serial. Number = '01'; cert. validity. not. Before = new Date(); cert. validity. not. After. set. Full. Year(cert. validity. not. Before. get. Full. Year() + 1); var attrs = [{ name: 'common. Name', value: 'cris. joongbu. ac. kr' }, { name: 'country. Name', value: 'KR' }, { short. Name: 'ST', value: 'Sultan' }, { name: 'locality. Name', value: 'Goyang' }, { name: 'organization. Name', value: 'Joongbu Univ. ' }, { short. Name: 'OU', value: 'JBU' }]; cert. set. Subject(attrs); cert. set. Issuer(attrs); cert. set. Extensions([{ name: 'basic. Constraints', c. A: true }, { name: 'key. Usage', key. Cert. Sign: true, digital. Signature: true, non. Repudiation: true, key. Encipherment: true, data. Encipherment: true }, { name: 'ext. Key. Usage', server. Auth: true, client. Auth: true, code. Signing: true, email. Protection: true, time. Stamping: true }, { name: 'ns. Cert. Type', client: true, server: true, email: true, objsign: true, ssl. CA: true, email. CA: true, obj. CA: true }, { name: 'subject. Alt. Name', alt. Names: [{ type: 6, // URI value: 'http: //cris. joongbu. ac. kr' }, { type: 7, // IP ip: '127. 0. 0. 1' }] }, { name: 'subject. Key. Identifier' }]); 인증서 생성: cert. js // self-sign certificate cert. sign(keys. private. Key); // convert a Forge certificate to PEM var pem. Cert = pki. certificate. To. Pem(cert); console. log('Certificate (PEM): n'+ pem. Cert); // Save certificate and private. Key to file fs. write. File. Sync('certificate. cer', pem. Cert, 'utf 8'); fs. write. File. Sync('priv. pem', pem. Priv, 'utf 8'); Forge. pki 객체 이용
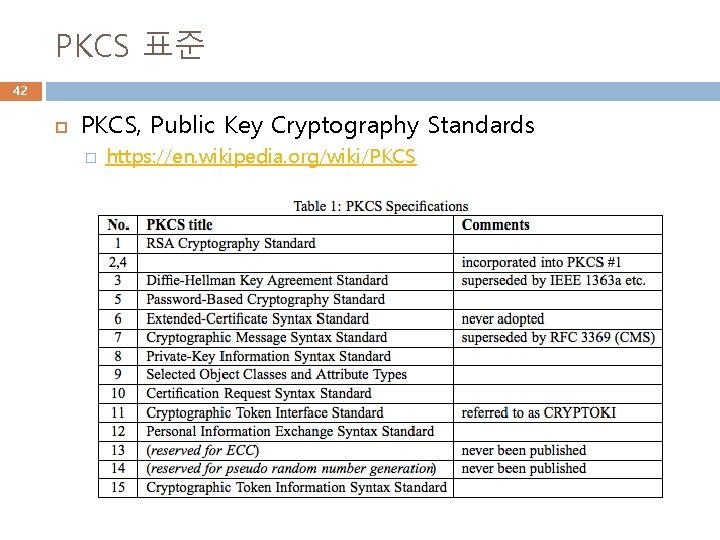
PKCS 표준 42 PKCS, Public Key Cryptography Standards � https: //en. wikipedia. org/wiki/PKCS
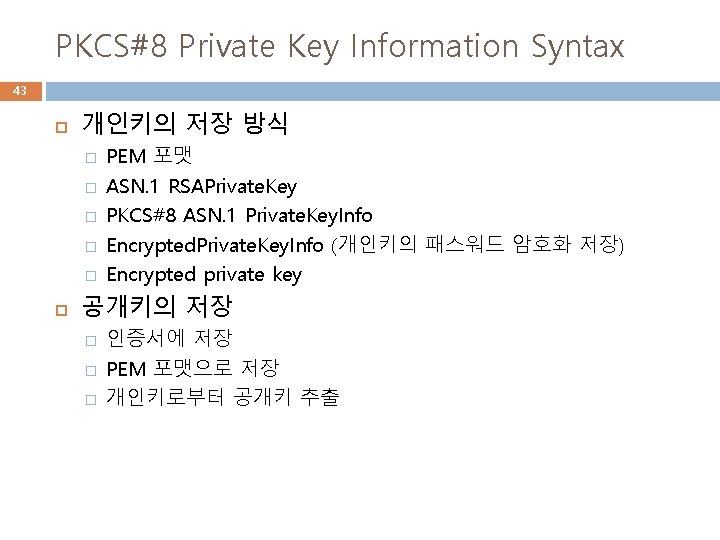
PKCS#8 Private Key Information Syntax 43 개인키의 저장 방식 � � � PEM 포맷 ASN. 1 RSAPrivate. Key PKCS#8 ASN. 1 Private. Key. Info Encrypted. Private. Key. Info (개인키의 패스워드 암호화 저장) Encrypted private key 공개키의 저장 � � � 인증서에 저장 PEM 포맷으로 저장 개인키로부터 공개키 추출
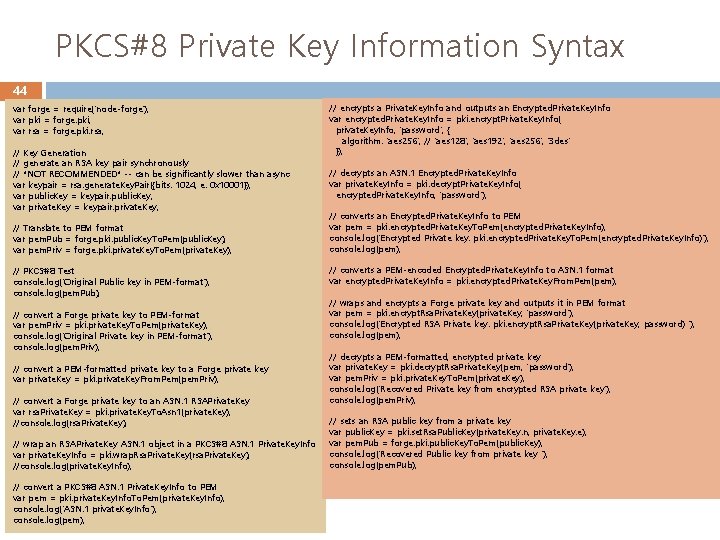
PKCS#8 Private Key Information Syntax 44 var forge = require('node-forge'); var pki = forge. pki; var rsa = forge. pki. rsa; // Key Generation // generate an RSA key pair synchronously // *NOT RECOMMENDED* -- can be significantly slower than async var keypair = rsa. generate. Key. Pair({bits: 1024, e: 0 x 10001}); var public. Key = keypair. public. Key; var private. Key = keypair. private. Key; // Translate to PEM format var pem. Pub = forge. pki. public. Key. To. Pem(public. Key); var pem. Priv = forge. pki. private. Key. To. Pem(private. Key); // PKCS#8 Test console. log('Original Public key in PEM-format'); console. log(pem. Pub); // convert a Forge private key to PEM-format var pem. Priv = pki. private. Key. To. Pem(private. Key); console. log('Original Private key in PEM-format'); console. log(pem. Priv); // convert a PEM-formatted private key to a Forge private key var private. Key = pki. private. Key. From. Pem(pem. Priv); // convert a Forge private key to an ASN. 1 RSAPrivate. Key var rsa. Private. Key = pki. private. Key. To. Asn 1(private. Key); //console. log(rsa. Private. Key); // wrap an RSAPrivate. Key ASN. 1 object in a PKCS#8 ASN. 1 Private. Key. Info var private. Key. Info = pki. wrap. Rsa. Private. Key(rsa. Private. Key); //console. log(private. Key. Info); // convert a PKCS#8 ASN. 1 Private. Key. Info to PEM var pem = pki. private. Key. Info. To. Pem(private. Key. Info); console. log('ASN. 1 private. Key. Info'); console. log(pem); // encrypts a Private. Key. Info and outputs an Encrypted. Private. Key. Info var encrypted. Private. Key. Info = pki. encrypt. Private. Key. Info( private. Key. Info, 'password', { algorithm: 'aes 256', // 'aes 128', 'aes 192', 'aes 256', '3 des' }); // decrypts an ASN. 1 Encrypted. Private. Key. Info var private. Key. Info = pki. decrypt. Private. Key. Info( encrypted. Private. Key. Info, 'password'); // converts an Encrypted. Private. Key. Info to PEM var pem = pki. encrypted. Private. Key. To. Pem(encrypted. Private. Key. Info); console. log('Encrypted Private key: pki. encrypted. Private. Key. To. Pem(encrypted. Private. Key. Info)'); console. log(pem); // converts a PEM-encoded Encrypted. Private. Key. Info to ASN. 1 format var encrypted. Private. Key. Info = pki. encrypted. Private. Key. From. Pem(pem); // wraps and encrypts a Forge private key and outputs it in PEM format var pem = pki. encrypt. Rsa. Private. Key(private. Key, 'password'); console. log('Encrypted RSA Private key: pki. encrypt. Rsa. Private. Key(private. Key, password) '); console. log(pem); // decrypts a PEM-formatted, encrypted private key var private. Key = pki. decrypt. Rsa. Private. Key(pem, 'password'); var pem. Priv = pki. private. Key. To. Pem(private. Key); console. log('Recovered Private key from encrypted RSA private key'); console. log(pem. Priv); // sets an RSA public key from a private key var public. Key = pki. set. Rsa. Public. Key(private. Key. n, private. Key. e); var pem. Pub = forge. pki. public. Key. To. Pem(public. Key); console. log('Recovered Public key from private key '); console. log(pem. Pub);
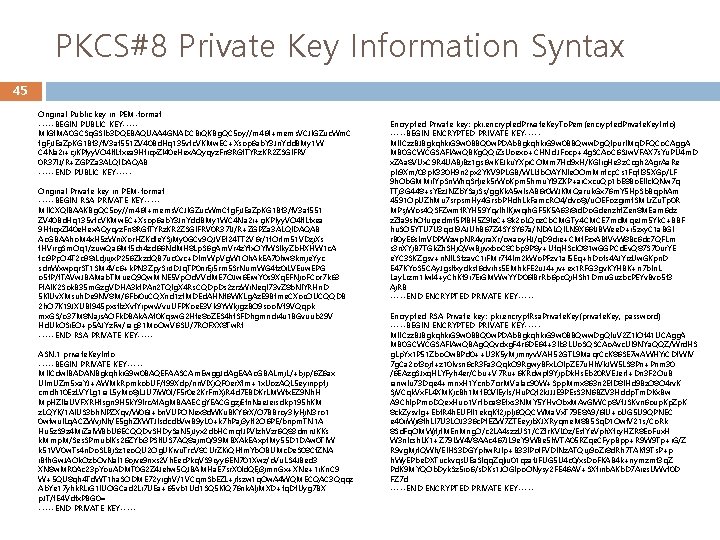
PKCS#8 Private Key Information Syntax 45 Original Public key in PEM-format -----BEGIN PUBLIC KEY----MIGf. MA 0 GCSq. GSIb 3 DQEBAQUAA 4 GNADCBi. QKBg. QC 5 oy//m 46 f+mems. VCJl. GZuc. Wm. C fg. Fj. JEa. Zp. KG 1 Bf 3/f. V 3 af 551 ZV 40 Bd. Hq 135 vtc. VKMw. EC+Xsop 6 ab. Y 3 Jn. Ydd. BMy 1 W C 4 Na 2 i+cj. KPIyy. VO 4 lt. Lfxea 9 Htiqx. Zl 40 e. Hex. AQyqyz. Fn 8 RGf. TYRz. KR 2 ZSGl. FRV 0 R 37 IJ/R+ZGPZa 3 ALQIDAQAB -----END PUBLIC KEY----Original Private key in PEM-format -----BEGIN RSA PRIVATE KEY----MIICXQIBAAKBg. QC 5 oy//m 46 f+mems. VCJl. GZuc. Wm. Cfg. Fj. JEa. Zp. KG 1 Bf 3/f. V 3 af 551 ZV 40 Bd. Hq 135 vtc. VKMw. EC+Xsop 6 ab. Y 3 Jn. Ydd. BMy 1 WC 4 Na 2 i+cj. KPIyy. VO 4 lt. Lfxea 9 Htiqx. Zl 40 e. Hex. AQyqyz. Fn 8 RGf. TYRz. KR 2 ZSGl. FRV 0 R 37 IJ/R+ZGPZa 3 ALQIDAQAB Ao. GBAAho. M 4 x. H 5 z. Wni. Xor. HZKdfe. YSj. My 0 GCv 9 QJVEt 24 TT 2 V 6 r/1 t. Oifm 51 VDzj. Xs f. HVirg. Sm. Oq 1/zuw. Qa 6 Mt 5 ch 4 zd 66 Nd. MH 8 Lp. S 6 g. Am. Vr 4 z. Yfx. OYIWSlky. Zb. HXHW 1 c. A fci 9 Pp. O 4 T 2 o 98 i. Ldjujx. P 256 Zkzd. QB 7 uc 0 vc+DIm. Wp. Vg. W 1 Oh. Ak. EA 70 hw 8 kmje. Yyc sdn. Wxwpqr. ST 1 SM 4 Vc 6+k. PN 3 Zpy. Sir. JDJq. TP 0 nr. Ej 5 rm 5 Sr. Num. WG 4 tz 0 i. LVEuw. EPG o 5 t. P/f. TAVw. JBAMab. TMue. Q 9 Qw. MNE 5 Vp. Od. VVd. ME 7 OJw 6 Eiw. Y 0 s 9 Xq. EFNjo. FCor 7 k 63 Ff. Al. K 2 Sok. B 35 m. Gzg. VDHA 3 kt. PAn 2 TQIg. X 4 Rs. CQDp. Ds 2 zrz. Wi. Neq. I 73 v. Z 8 b. Nl. YRHn. D 5 Kl. Uv. XMsuh. De 9 NV 8 M/6 Fbi 0 u. CQXnd 1 zf. MDEd. AHNt 6 WKLg. Az. E 9 Btme. CXoc. OUCQQDB 2 h. O 7 K 19 JXUBI 945 pxsflz. Xvt. Yipwv. Vvu. UFPKoe. E 3 Vk 9 YWkjgz. BO 9 soo. IVf 9 VQqpk mx. GS/o 37 M 8 Najs. AOFk. DBAk. AAt 0 Kqsw. G 2 Hte 8 o. ZES 4 ht. SFDhgmndi 4 u 1 BGvuub 29 V Hd. Uk. OSi. EO+p 5 AJYz. Fw/rag 31 Mo. Ow. V 6 SU/7 ROFXX 8 Tw. Rt -----END RSA PRIVATE KEY----ASN. 1 private. Key. Info -----BEGIN PRIVATE KEY----MIICdw. IBADANBgkqhki. G 9 w 0 BAQEFAASCAm. Ewgg. Jd. Ag. EAAo. GBALmj. L/+bjp/6 Z 6 ax UIm. UZm 5 xa. YJ+AWMk. Rpmkob. UF/f 99 Xdp/nn. Vl. Xj. QF 0 er. Xfm+1 x. Uoz. AQL 5 eyinpptj cmdh 10 Ez. LVYLg 1 ra. L 5 y. Mo 8 j. LJU 7 i. W 0 t/F 5 r 0 e 2 Kr. Fm. Xj. R 4 d 7 EBDKr. LMWfx. EZ 9 Nh. H Mp. HZl. Ia. UVFXRHfsgn 9 H 5 k. Y 9 lrc. At. Ag. MBAAECg. YEACGgzj. Efn. Nae. Jeisdkp 195 h. KM z. LQYK/1 Al. US 3 bh. NPZXqv/W 06 J+bn. VUPONex 8 d. WKu. BKY 6 r. X/O 7 BBroy 3 ly. Hj. N 3 ro 1 0 wfwul. Lq. ACZWvj. Nh/E 5 gh. ZKWTJlsdcdb. Vw. B 9 y. L 0+k 7 h. Paj 3 y. It 2 O 6 PE/bnpm. TN 1 A Hu 5 z. S 9 z 4 Mi. Zal. WBb. U 6 ECQQDv. SHDy. Sa. N 5 j. Jyx 2 db. HCmqt. JPVIzh. Vzr 6 Q 83 dmn. JKKs k. Mmp. M/Ses. SPmubl. Ks 26 ZYbi 3 PSIt. US 7 AQ 8 ajm 0/99 MBXAk. EAxpt. My 55 D 1 DAw 0 Tl. W k 51 VV 0 w. Ts 4 n. Do. SLBj. Sz 1 eo. QU 2 Og. UKivu. Trc. V 8 CUr. ZKi. QHfm. Yb. OBUMc. De. S 08 Cf. ZNA i. Bfh. Gw. JAOk. Ozb. Ov. Na. I 16 ojve 9 nxs 2 Vh. Eec. Pkq. VS 9 cyy 6 EN 701 Xwz/o. Vu. LS 4 JBed 3 XN 8 w. MR 0 Ac 23 p. You. ADMT 0 G 2 Z 4 Jehw 5 QJBAMHa. E 7 sr. X 0 ld. QEj 3 jmn. Gx+XNe+1 i. Kn. C 9 W+5 QU 8 qh 4 Td. WT 1 ha. SODME 72 yigh. V/1 VCqm. Sb. EZL+jfszw 1 q. Ow. A 4 WQMECQAC 3 Qqqz Ab. Ye 17 yhk. RLi. G 1 IUOGCad 2 Li 7 UEa+65 vb 1 Ud 1 SQ 5 KIQ 76 nk. Alj. MXD+tq. Df. Uyg 7 BX p. JT/t. E 4 Vdfx. PBG 0= -----END PRIVATE KEY----- Encrypted Private key: pki. encrypted. Private. Key. To. Pem(encrypted. Private. Key. Info) -----BEGIN ENCRYPTED PRIVATE KEY----MIICzz. BJBgkqhki. G 9 w 0 BBQ 0 w. PDAb. Bgkqhki. G 9 w 0 BBQww. Dg. QIpur. IMq. DFQCo. CAgg. A MB 0 GCWCGSAFl. Aw. QBKg. QQi. Zs. Uoexo+CHNcf. JFocp+4 g. SCAo. C 6 SJw. VFAX 7 s. Yu. PU 4 m. D x. ZAa 8 VUx. C 9 R 4 UABj. Bz 1 gs 6 w. KEJku. YXpi. COMm 7 Hd 9 x. H/KGIig. He 3 z. Ccgh 2 Agr. Aa. Re pli 9 Xm/03 p. K 330 H 9 n 2 px 2 YKV 9 PLGB/WLLfb. OAYNle. OOm. Mnfcp. Cs 1 Fqtl 35 XGp/LF 9 h. Ob. GMMi. IYp. Sn. Whq. Srtjek 5 r. Wo. Kpm 5 hmu. YI 9 ZKP+ai. Cxcu. Qp 1 b. E 8 Bo. EIlcl. QNw 7 q TTj 3 G 448+s. YEz. JNZb. YSaj. Ss/gg. Kk. A 5 wls. AB 6 r 0 WJKMQaruk. Gx 76 m. Y 5 Hp. Sb. Bqph. Am 4591 Op. UZh. Mu 7 srpsm. Hy 4 Grsb. PHdh. Lk. Famc. RO 4/dvo 8 j/u. OEFozgjmf. SMLr. Zu. Tp 0 R MPsj. Wos 4 QSFZwmf. RYH 59 Yqvlh. IKjwqih. GF 5 K 5 A 63 i 8 id. Do. Gdenzht. Zen 8 MEam 6 dz z. Zfa 9 sh. Ofucjedmf 5 PIBH 5 Z 9 le. C+8 k 2 o. LQoz. Cb. CMGTy 4 CMCE 7 md. Mqe. Jm 5 Yk. C+BBF hu. SO 5 YTU 7 U 3 qc. JI 9 AJUh. B 67 Z 4 SYSY 67 a/NDALQILN 9 X 66 f. JBWee. D+i 5 zxy. C 1 a. BGI r. B 0 y. E 6 slm. VDPWzwp. NR 4 vjra. Xr/cwaoy. HJ/q. D 9 die+CMf. Fzx. ABf. Vv. W 8 Bc 6 dc 7 QFLm s 3 n. XYj. B 7 TGk. Zh. SHj. QVw. Bjjvxbo. C 8 Cbp 9 P 8 y+Utq. HScl. O 81 w. GGPCd. Ev. Q 87 S 70 ur. YE e. YC 3 SKZgsv+n. NILSfzav. C 1 i. FMr 7 f 4 Im 2 k. Wo. PFzv 1 al 5 Eq+h. Dofs 4 AJYiz. Uw. GKpn. D E 47 KYo. S 5 CAy. Jgslfxydksf 6 dvihs 5 EMhk. FE 2 u. J 4+jv+ex 1 RFG 3 gv. KYHBK+n 7 b. In. L Lay. Lrzm 1 lwl 4+y. Ch. Kt 9 i 7 Ei. GMWw. YYD 06 IBr. Rb 6 pc. Qj. HSh 1 Dmu. Guzbc. PEYv. Bvo 5 f 3 Aj. RB -----END ENCRYPTED PRIVATE KEY----Encrypted RSA Private key: pki. encrypt. Rsa. Private. Key(private. Key, password) -----BEGIN ENCRYPTED PRIVATE KEY----MIICzz. BJBgkqhki. G 9 w 0 BBQ 0 w. PDAb. Bgkqhki. G 9 w 0 BBQww. Dg. QIu. V 2 Z 1 l. Of 41 UCAgg. A MB 0 GCWCGSAFl. Aw. QBAg. QQvdxg. F 4 r 6 DE 64+3 lb 3 LUo. SQSCAo. Avc. Ul 9 NYa. QQZ/Wrd. HS g. Lp. Yx 1 P 51 Zbo. Ow. BPd 0++U 3 K 5 y. Mjmnyv. VAH 52 GTL 9 Maqr. Cc. K 86 SE 7 w. AWHYi. CDt. WIV 7 g. Ca 2 of 3 ojf+z 10 lvsn 6 c. R 3 Fa 3 Qqk. O 9 Rgwy. BFx. LOlp. ZE 7 u. Hh. Vk. JW 5 LS 8 Pn+Pnm 30 /6 EAzg. SJxq. HLYFyh 4 er/Cbu+V 7 Ru+6 KRdwpf 9 Yjp. Dk. Hs. Eb 20 RVEJerf+Dn 3 F 2 Ou. B ianw. Iu 73 Dqe 4+mnx. H 1 Ycnb 7 cir. MVa. Iac 90 W+Spp. Mmx 863 n 2 Ef. D 8 IHd 9 Bz. O 8 O 4 rv. K Sj. VCqk. Vx. FL 4 XMKjc. Bh 1 Mt. E 0 Vl. Eyls/Hu. PQt 2 k. JJJE 9 PEs. S 3 N 6 BZV 3 Hddp. Tm. DKx. Bw A 9 Ch. Ip. Pmo. DQex. Huo 1 Vrtboa 8 Efxs 3 NMY 5 YHv. Obx. MAv. Gl. WCp 8 Vf. JSKvn 6 oup. Kp. Zp. K 8 ck. Zysv. Ig+Ebf. R 4 h. EUFtl 1 ekq. Kt 2 jp. Ij 6 QQCWMa. Vx. T 79 E 8 A 9/6 IU+o. UG 5 U 9 QPNEC e 40 ii. Wji 8 fh. LI 7 U 3 LOJ 336 c. Pt. EZW 7 ZTEeyjb. XJXRyqme. M 8 B 5 Sq. D 1 Owf. V 21 s/Co. Rk 8 Sd. Fq. OMWjfjt. MEn. Mng. O/c 2 LA 4 szz. US 1/CZfr. KVL 0 z/Est. Ye. Vph. Xfcy. HZR 8 Eo. Fux. H W 3 n. Icsh. LK 1+Z 79 LW 4 V 8 AAc 467 JL 9 e. Y 9 WBe 5 h. VTA 05 RZqe. CFyp. Bpp+R 9 W 9 Tp+i. G/Z R 9 vg. Mjt. QWh/El. HS 3 DGYphw. RJIp+B 33 l. Pot. FVDINz. ATQuj 9 o. Zi 8 d. Rh 7 TAKt 9 Ts. P+p h. Wy. EPbe. DXTuckvqs. UEa. Slqq. Zqlju 01 qzat. JFUG 5 U 4 c 0/xs. Do. FKAB 4 k+nymzmt 3 q. Z Pd. K 9 MYQOb. Dyk. Sz 5 io 6/s. DKs 1 JOGlpo. ONysy 2 FE 46 AV+SXtinb. AKb. D 7 Aies. UWvt 0 D FZ 7 d -----END ENCRYPTED PRIVATE KEY-----
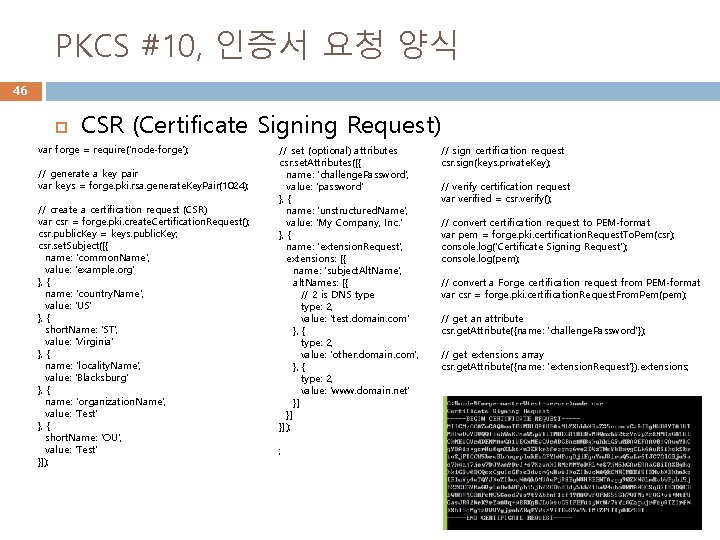
PKCS #10, 인증서 요청 양식 46 CSR (Certificate Signing Request) var forge = require('node-forge'); // generate a key pair var keys = forge. pki. rsa. generate. Key. Pair(1024); // create a certification request (CSR) var csr = forge. pki. create. Certification. Request(); csr. public. Key = keys. public. Key; csr. set. Subject([{ name: 'common. Name', value: 'example. org' }, { name: 'country. Name', value: 'US' }, { short. Name: 'ST', value: 'Virginia' }, { name: 'locality. Name', value: 'Blacksburg' }, { name: 'organization. Name', value: 'Test' }, { short. Name: 'OU', value: 'Test' }]); // set (optional) attributes csr. set. Attributes([{ name: 'challenge. Password', value: 'password' }, { name: 'unstructured. Name', value: 'My Company, Inc. ' }, { name: 'extension. Request', extensions: [{ name: 'subject. Alt. Name', alt. Names: [{ // 2 is DNS type: 2, value: 'test. domain. com' }, { type: 2, value: 'other. domain. com', }, { type: 2, value: 'www. domain. net' }] }] }]); ; // sign certification request csr. sign(keys. private. Key); // verify certification request var verified = csr. verify(); // convert certification request to PEM-format var pem = forge. pki. certification. Request. To. Pem(csr); console. log('Certificate Signing Request'); console. log(pem); // convert a Forge certification request from PEM-format var csr = forge. pki. certification. Request. From. Pem(pem); // get an attribute csr. get. Attribute({name: 'challenge. Password'}); // get extensions array csr. get. Attribute({name: 'extension. Request'}). extensions;
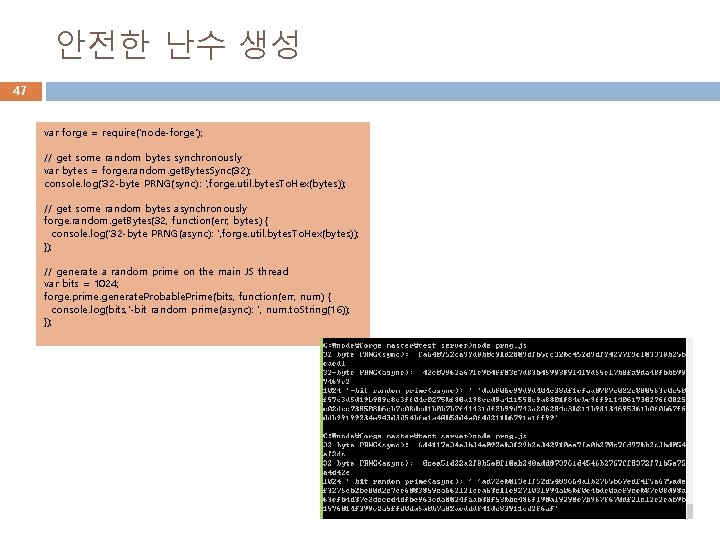
안전한 난수 생성 47 var forge = require('node-forge'); // get some random bytes synchronously var bytes = forge. random. get. Bytes. Sync(32); console. log('32 -byte PRNG(sync): ', forge. util. bytes. To. Hex(bytes)); // get some random bytes asynchronously forge. random. get. Bytes(32, function(err, bytes) { console. log('32 -byte PRNG(async): ', forge. util. bytes. To. Hex(bytes)); }); // generate a random prime on the main JS thread var bits = 1024; forge. prime. generate. Probable. Prime(bits, function(err, num) { console. log(bits, '-bit random prime(async): ', num. to. String(16)); });
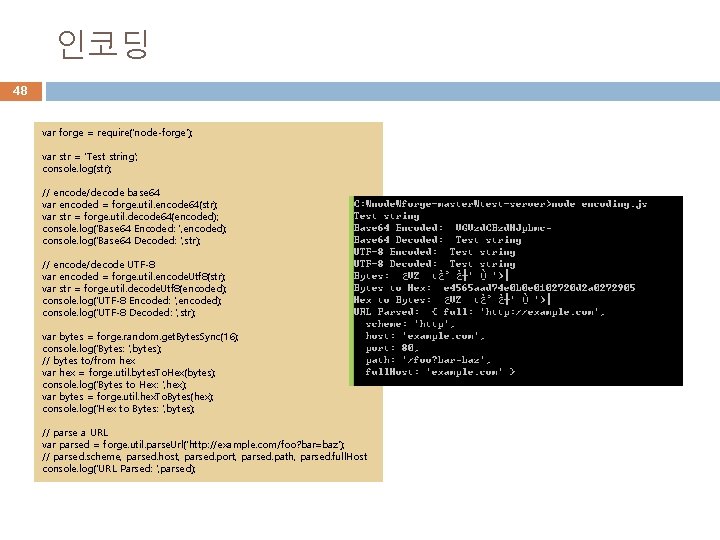
인코딩 48 var forge = require('node-forge'); var str = 'Test string'; console. log(str); // encode/decode base 64 var encoded = forge. util. encode 64(str); var str = forge. util. decode 64(encoded); console. log('Base 64 Encoded: ', encoded); console. log('Base 64 Decoded: ', str); // encode/decode UTF-8 var encoded = forge. util. encode. Utf 8(str); var str = forge. util. decode. Utf 8(encoded); console. log('UTF-8 Encoded: ', encoded); console. log('UTF-8 Decoded: ', str); var bytes = forge. random. get. Bytes. Sync(16); console. log('Bytes: ', bytes); // bytes to/from hex var hex = forge. util. bytes. To. Hex(bytes); console. log('Bytes to Hex: ', hex); var bytes = forge. util. hex. To. Bytes(hex); console. log('Hex to Bytes: ', bytes); // parse a URL var parsed = forge. util. parse. Url('http: //example. com/foo? bar=baz'); // parsed. scheme, parsed. host, parsed. port, parsed. path, parsed. full. Host console. log('URL Parsed: ', parsed);
- Slides: 48