Hardware Support for Embedded Operating System Security Arman
Hardware Support for Embedded Operating System Security Arman Pouraghily, Tilman Wolf, and Russell Tessier Department of Electrical and Computer Engineering University of Massachusetts Amherst Department of Electrical and Computer Engineering University of Massachusetts, Amherst
Introduction § Pervasive use of embedded systems § Serious security requirements • Software based solutions not suitable for embedded systems § Hardware monitoring as a solution • Dedicated hardware co-located with the main processor • Ensuring the safe behavior of the main processor at run-time • Signaling the main processor upon detecting a deviation Department of Electrical and Computer Engineering University of Massachusetts, Amherst 2/13
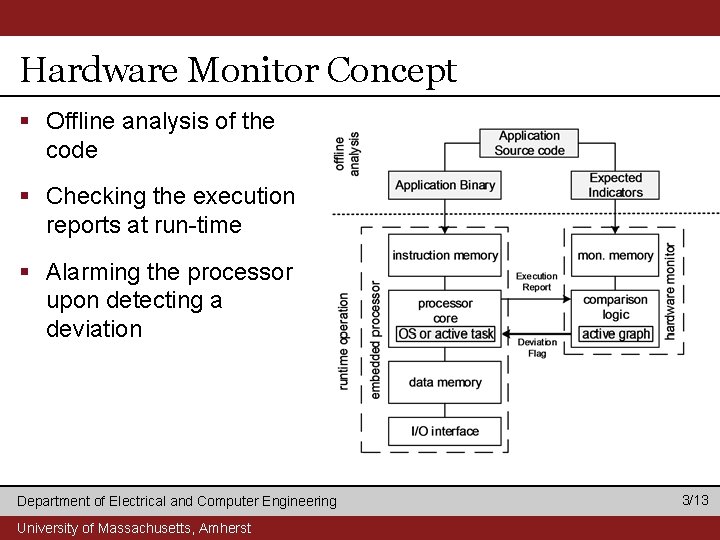
Hardware Monitor Concept § Offline analysis of the code § Checking the execution reports at run-time § Alarming the processor upon detecting a deviation Department of Electrical and Computer Engineering University of Massachusetts, Amherst 3/13
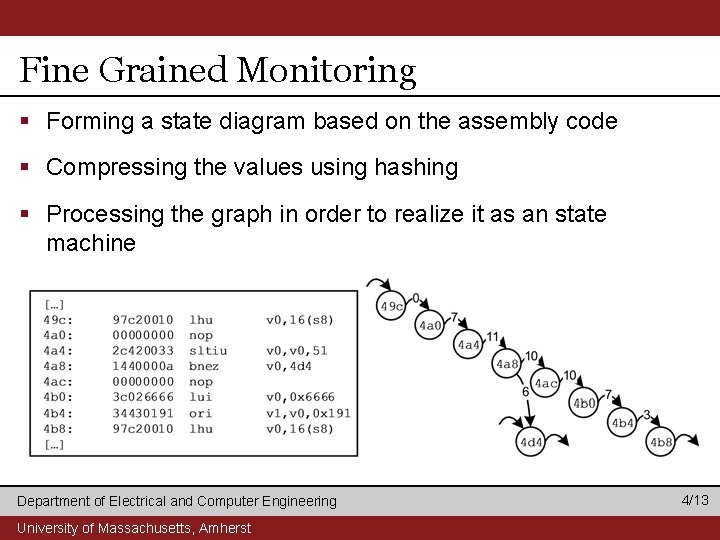
Fine Grained Monitoring § Forming a state diagram based on the assembly code § Compressing the values using hashing § Processing the graph in order to realize it as an state machine Department of Electrical and Computer Engineering University of Massachusetts, Amherst 4/13
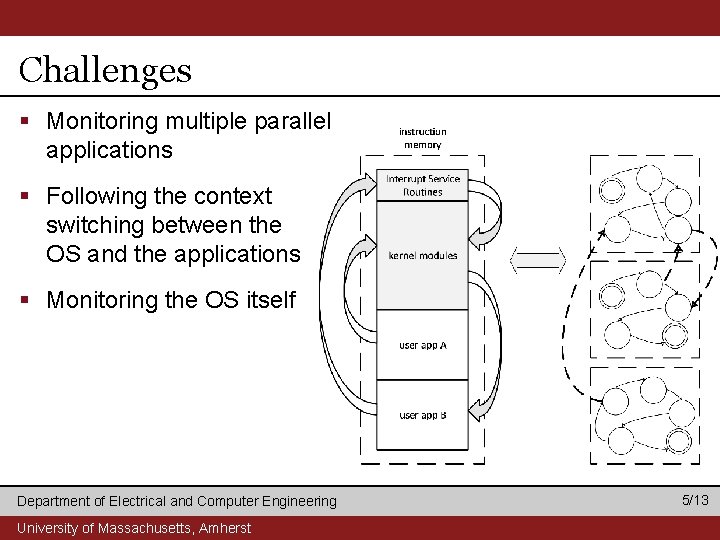
Challenges § Monitoring multiple parallel applications § Following the context switching between the OS and the applications § Monitoring the OS itself Department of Electrical and Computer Engineering University of Massachusetts, Amherst 5/13
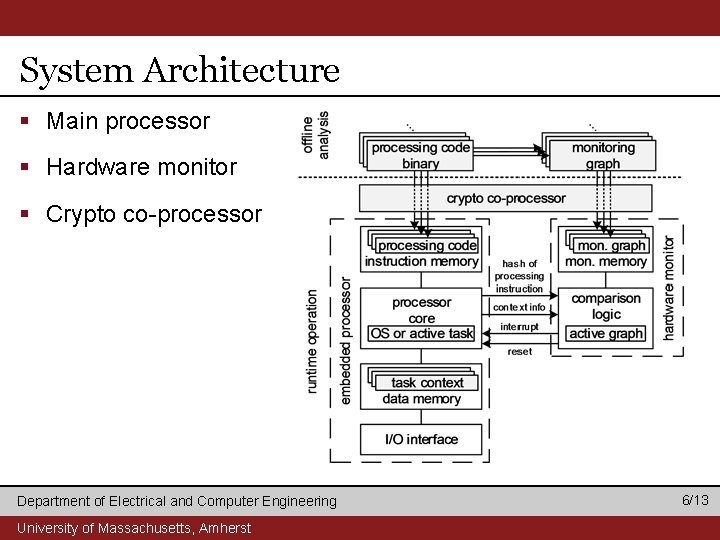
System Architecture § Main processor § Hardware monitor § Crypto co-processor Department of Electrical and Computer Engineering University of Massachusetts, Amherst 6/13
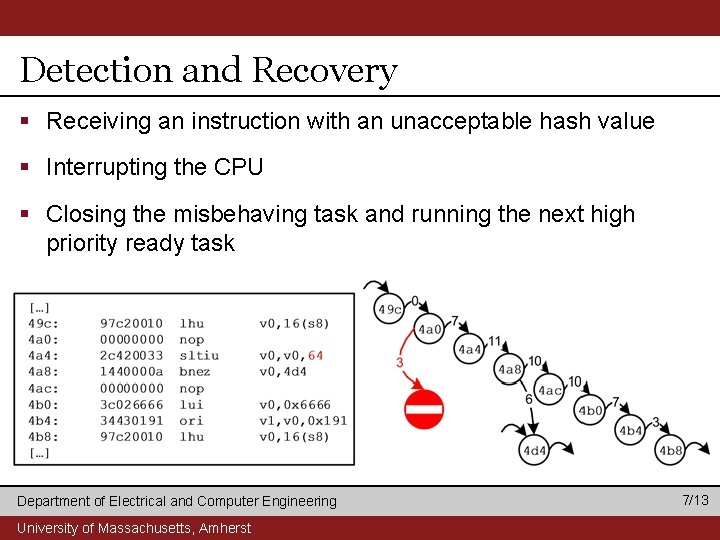
Detection and Recovery § Receiving an instruction with an unacceptable hash value § Interrupting the CPU § Closing the misbehaving task and running the next high priority ready task Department of Electrical and Computer Engineering University of Massachusetts, Amherst 7/13
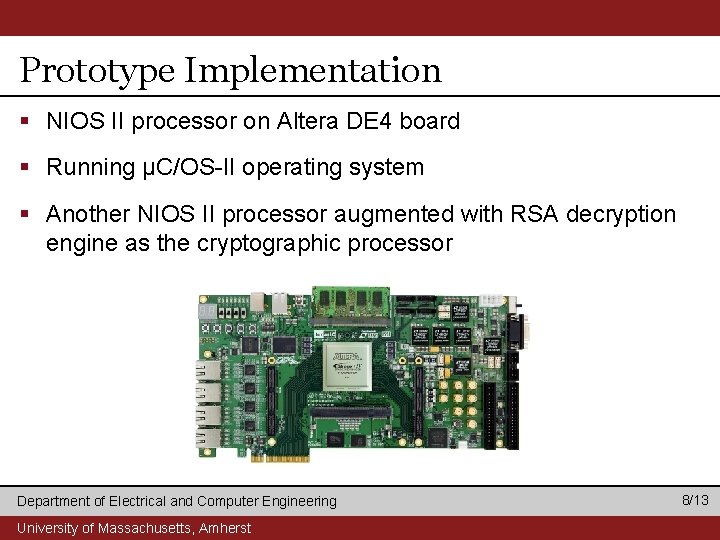
Prototype Implementation § NIOS II processor on Altera DE 4 board § Running µC/OS-II operating system § Another NIOS II processor augmented with RSA decryption engine as the cryptographic processor Department of Electrical and Computer Engineering University of Massachusetts, Amherst 8/13
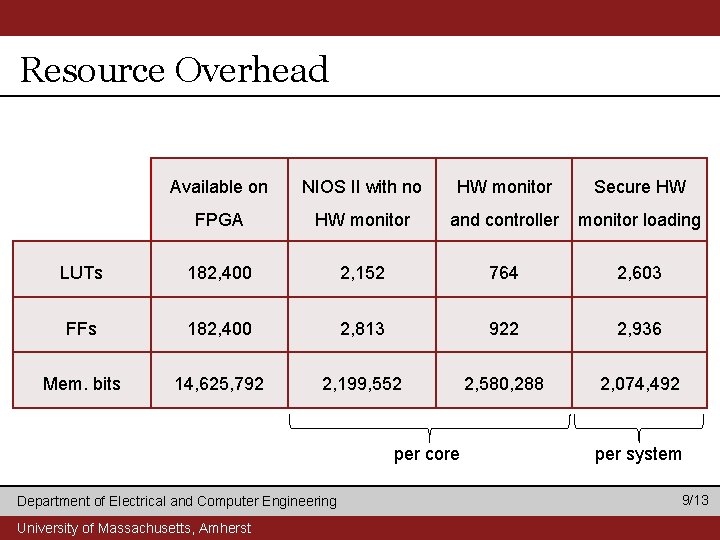
Resource Overhead Available on NIOS II with no HW monitor Secure HW FPGA HW monitor and controller monitor loading LUTs 182, 400 2, 152 764 2, 603 FFs 182, 400 2, 813 922 2, 936 Mem. bits 14, 625, 792 2, 199, 552 2, 580, 288 2, 074, 492 per core Department of Electrical and Computer Engineering University of Massachusetts, Amherst per system 9/13
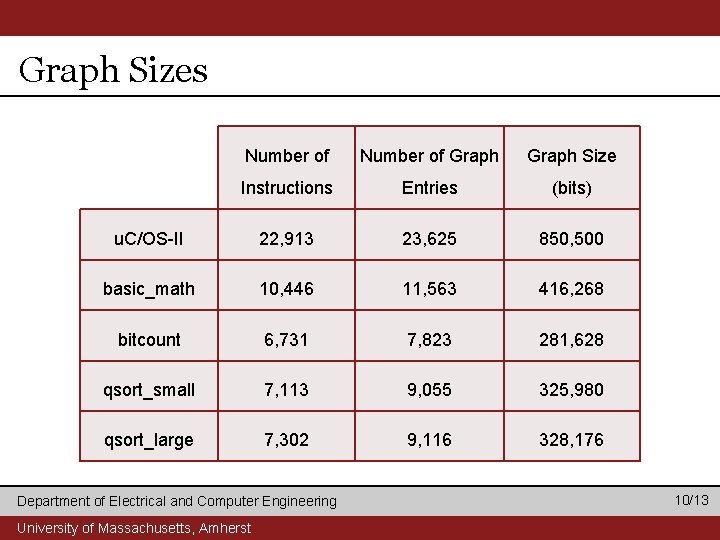
Graph Sizes Number of Graph Size Instructions Entries (bits) u. C/OS-II 22, 913 23, 625 850, 500 basic_math 10, 446 11, 563 416, 268 bitcount 6, 731 7, 823 281, 628 qsort_small 7, 113 9, 055 325, 980 qsort_large 7, 302 9, 116 328, 176 Department of Electrical and Computer Engineering University of Massachusetts, Amherst 10/13
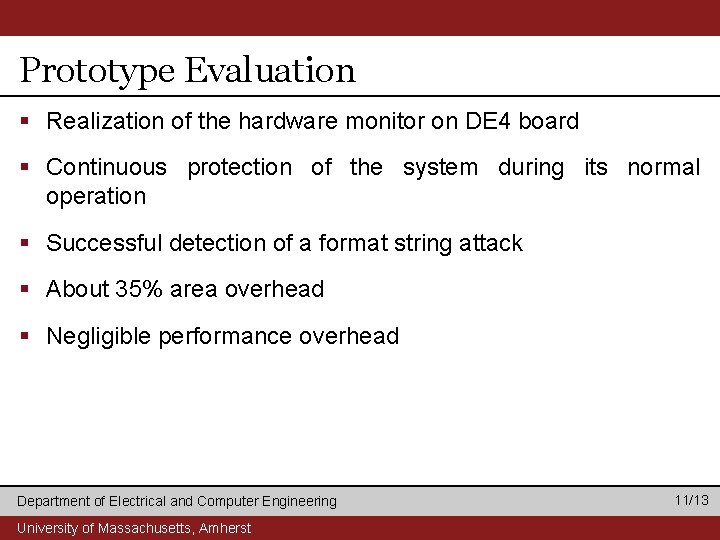
Prototype Evaluation § Realization of the hardware monitor on DE 4 board § Continuous protection of the system during its normal operation § Successful detection of a format string attack § About 35% area overhead § Negligible performance overhead Department of Electrical and Computer Engineering University of Massachusetts, Amherst 11/13
Summary § Security in embedded systems is important § We developed a hardware monitor to detect and stop attacks • Practical solution for complex OS based multitask systems • Small area overhead but memory requirement proportional to binary size • No frequency slow down imposed by the added hardware • A real world attack scenario implemented and stopped using the implemented solution § Effective approach to protecting embedded systems from attacks Department of Electrical and Computer Engineering University of Massachusetts, Amherst 12/13
Thank You Department of Electrical and Computer Engineering University of Massachusetts, Amherst 13/13
- Slides: 13