Bees A Secure ResourceControlled JavaBased Execution Environment Tim
Bees: A Secure, Resource-Controlled, Java-Based Execution Environment Tim Stack Eric Eide Jay Lepreau University of Utah April 5, 2003 1
What is Bees? l Mobile code system that is – Realistically deployable because it addresses needs of node administrators – Realistically usable because it provides rich interface needed by service authors l We believe may be the first such environment 2
Key Features l Flexible security primitives l Resource control l Flexible protocol composition l Flexible control of packet propagation l Isolates interaction with end-user apps Bees integrates them all 3
A Motivating Application l Motherboard sensor monitor – Spreads over network – Reports to server – Shuts down faulty nodes l Ideal for active protocol – Flexible access to sensors – Not speed-critical Health Reports Node 4
ANTS: Implementation l Capsule – Packet associated with Java class through MD 5 hash l Protocol – Collection of capsule classes l Application – Includes copy of protocol – Source of all capsules 5
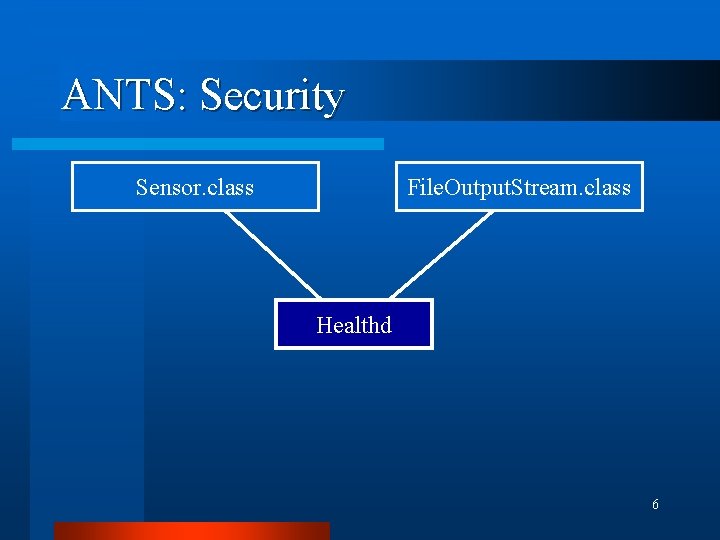
ANTS: Security Sensor. class File. Output. Stream. class Healthd 6
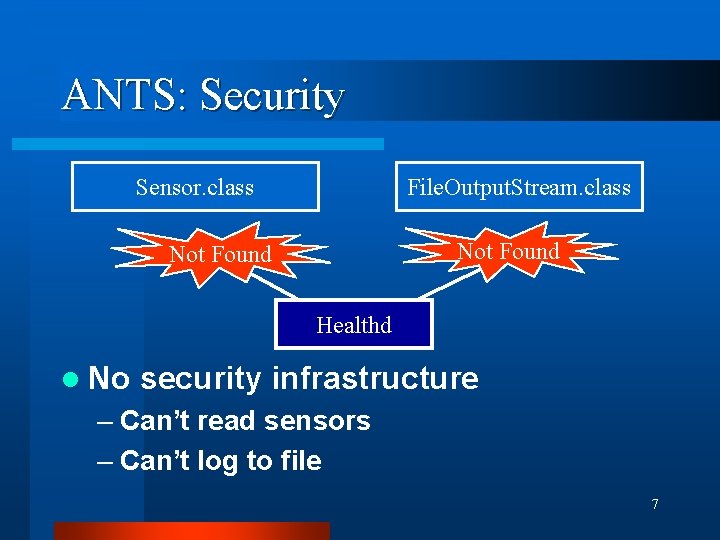
ANTS: Security Sensor. class File. Output. Stream. class Not Found Healthd l No security infrastructure – Can’t read sensors – Can’t log to file 7
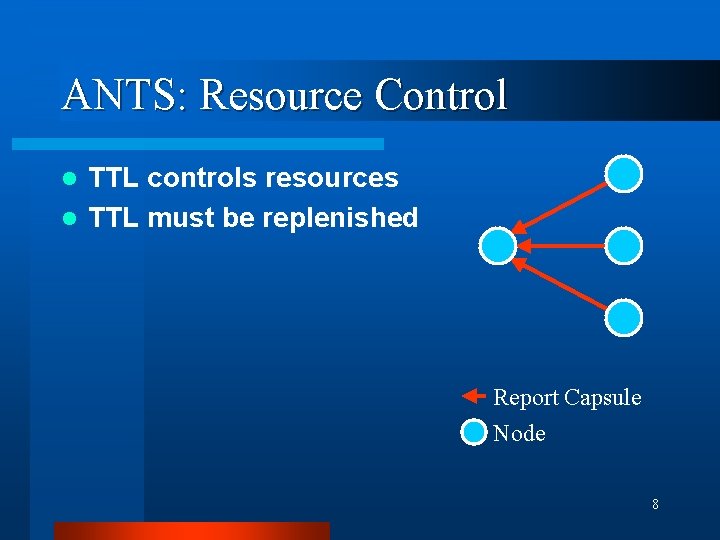
ANTS: Resource Control TTL controls resources l TTL must be replenished l Report Capsule Node 8
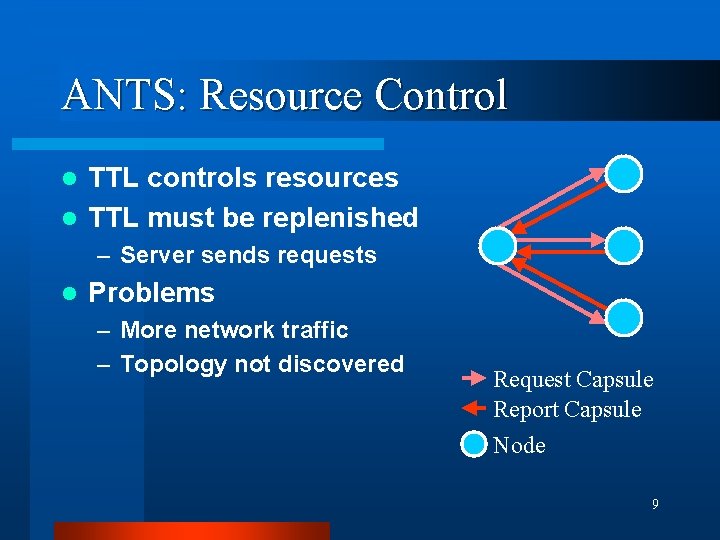
ANTS: Resource Control TTL controls resources l TTL must be replenished l – Server sends requests l Problems – More network traffic – Topology not discovered Request Capsule Report Capsule Node 9
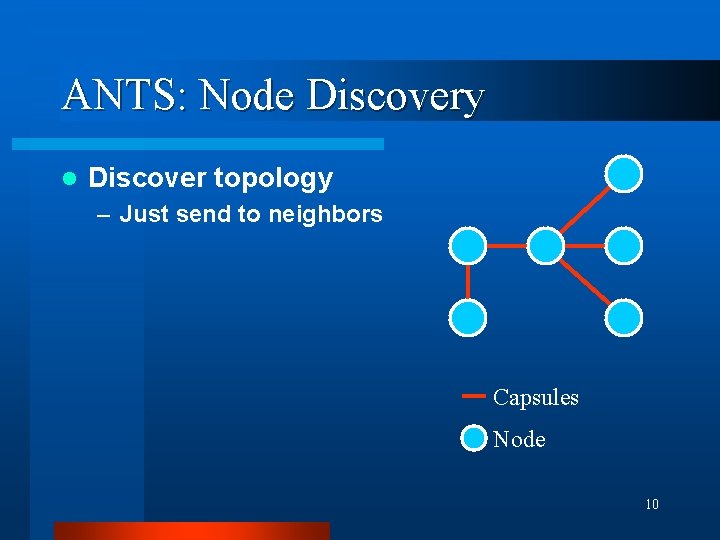
ANTS: Node Discovery l Discover topology – Just send to neighbors Capsules Node 10
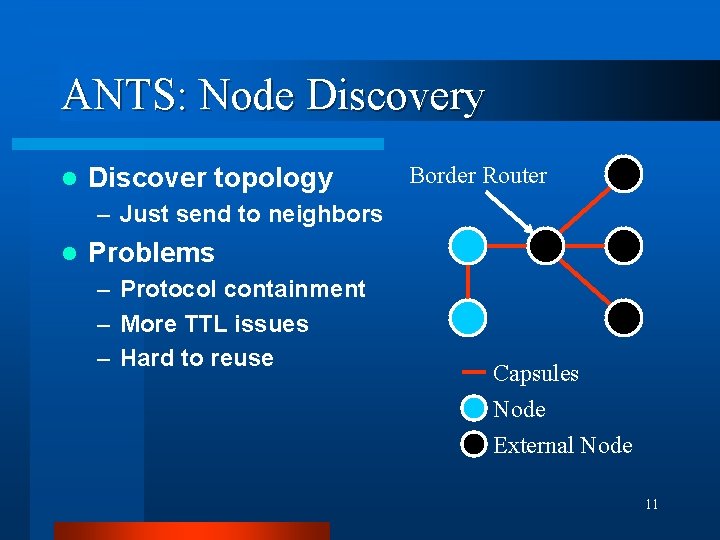
ANTS: Node Discovery l Discover topology Border Router – Just send to neighbors l Problems – Protocol containment – More TTL issues – Hard to reuse Capsules Node External Node 11
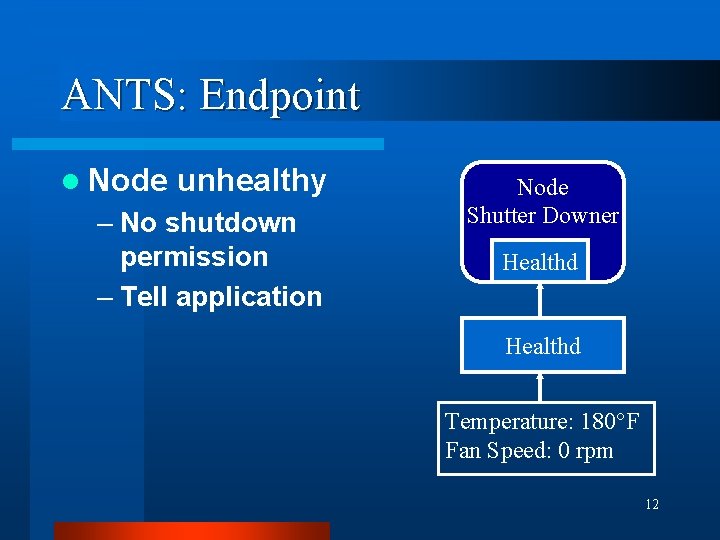
ANTS: Endpoint l Node unhealthy – No shutdown permission – Tell application Node Shutter Downer Healthd Temperature: 180°F Fan Speed: 0 rpm 12
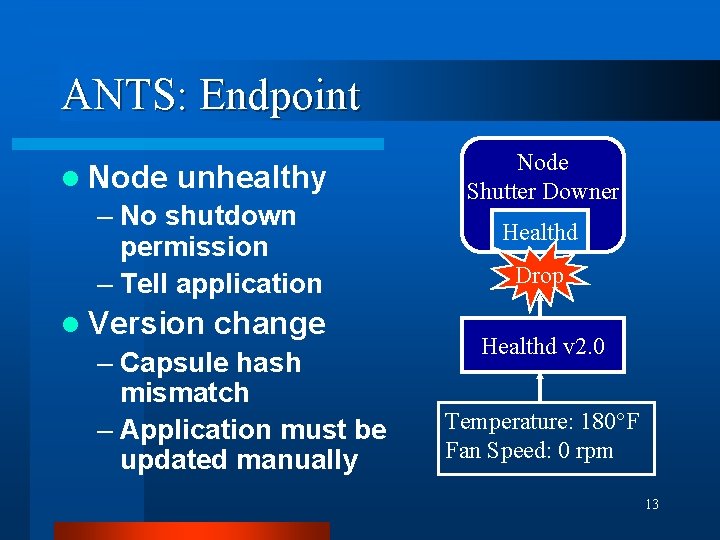
ANTS: Endpoint l Node unhealthy – No shutdown permission – Tell application l Version change – Capsule hash mismatch – Application must be updated manually Node Shutter Downer Healthd Drop Healthd v 2. 0 Temperature: 180°F Fan Speed: 0 rpm 13
ANTS: Assessment l Reality intervenes l What is wrong? l Wrong type of EE l Richer EE needed 14
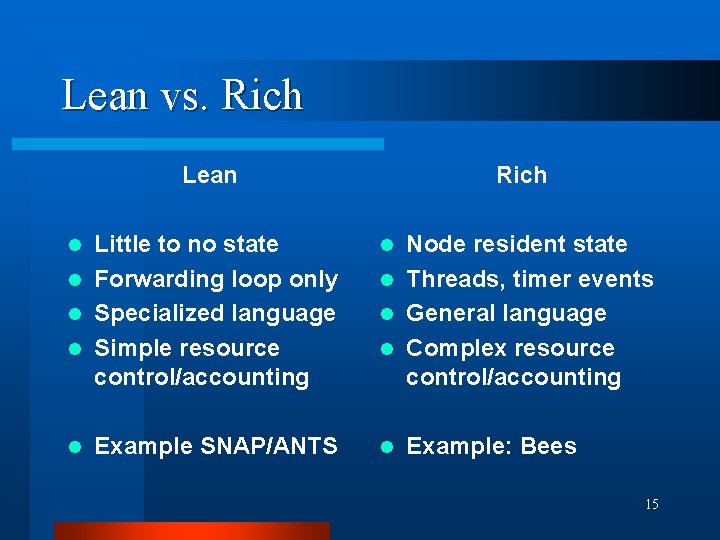
Lean vs. Rich Lean Rich Little to no state l Forwarding loop only l Specialized language l Simple resource control/accounting l Example SNAP/ANTS l l l Node resident state l Threads, timer events l General language l Complex resource control/accounting Example: Bees 15
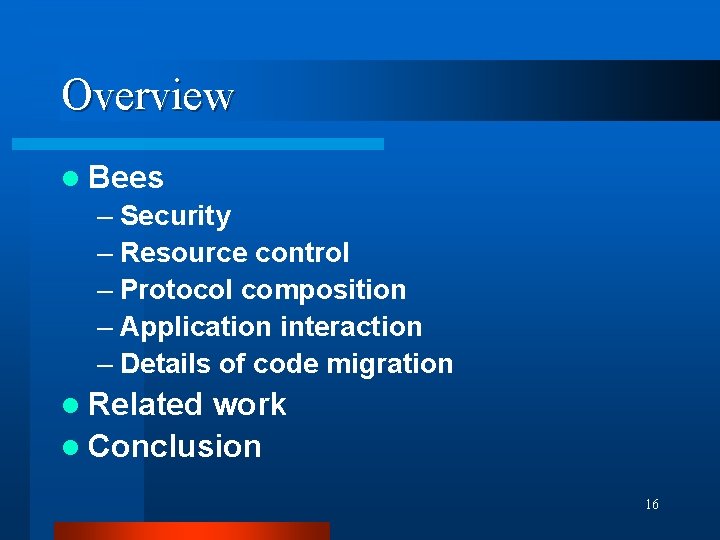
Overview l Bees – Security – Resource control – Protocol composition – Application interaction – Details of code migration l Related work l Conclusion 16
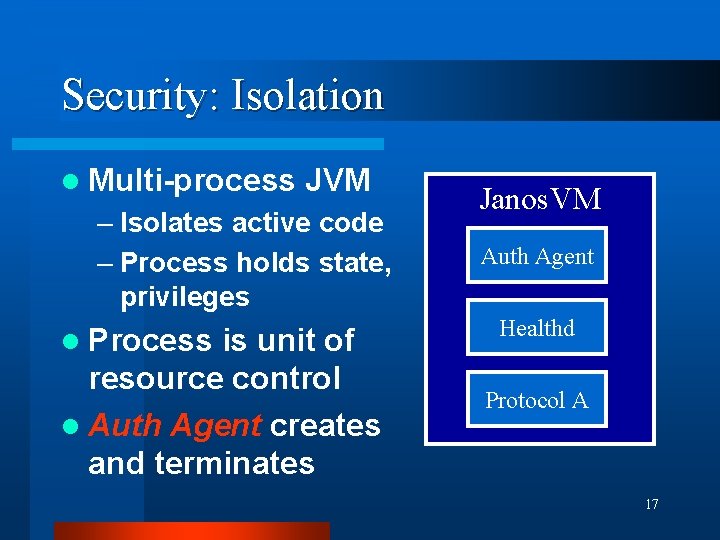
Security: Isolation l Multi-process JVM – Isolates active code – Process holds state, privileges l Process is unit of resource control l Auth Agent creates and terminates Janos. VM Auth Agent Healthd Protocol A 17
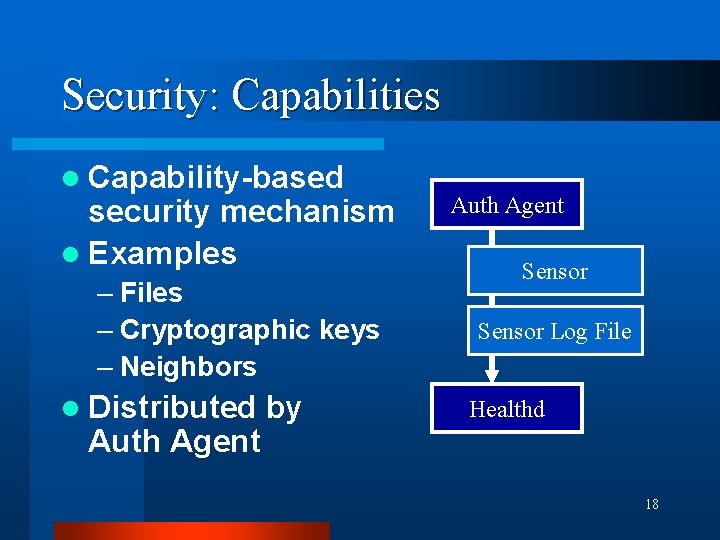
Security: Capabilities l Capability-based security mechanism l Examples – Files – Cryptographic keys – Neighbors l Distributed Auth Agent by Auth Agent Sensor Log File Healthd 18
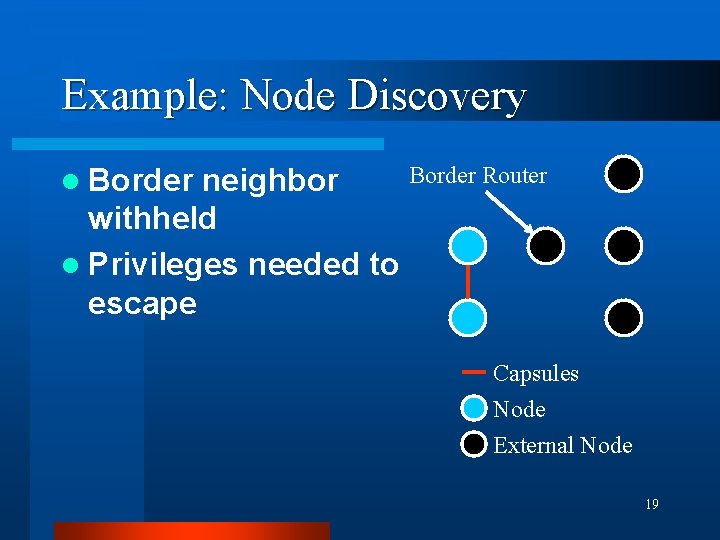
Example: Node Discovery l Border neighbor withheld l Privileges needed to escape Border Router Capsules Node External Node 19
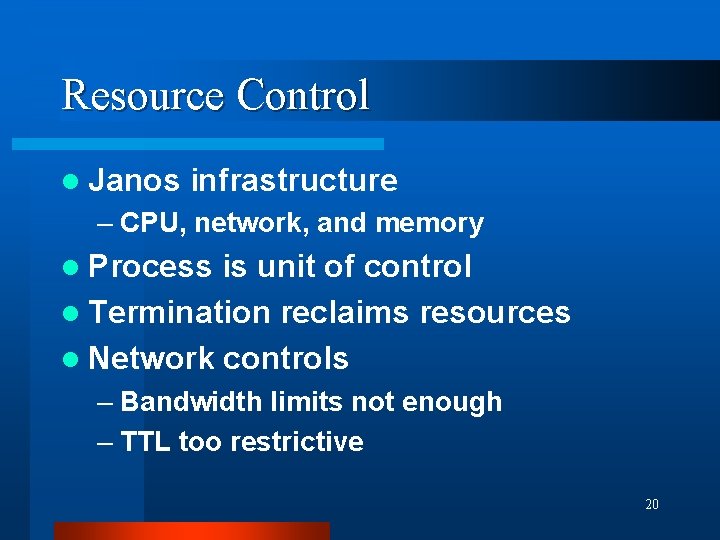
Resource Control l Janos infrastructure – CPU, network, and memory l Process is unit of control l Termination reclaims resources l Network controls – Bandwidth limits not enough – TTL too restrictive 20
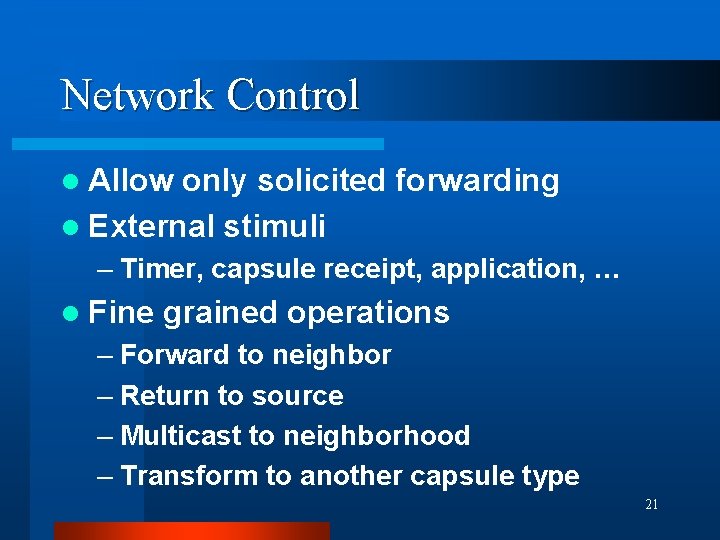
Network Control l Allow only solicited forwarding l External stimuli – Timer, capsule receipt, application, … l Fine grained operations – Forward to neighbor – Return to source – Multicast to neighborhood – Transform to another capsule type 21
Capsule Operations l Capsule operation counters – Protocol author defines initial values – Stimuli replenishes values – Decremented on use – Operations disallowed when zero l Initial values limited by Auth Agent 22
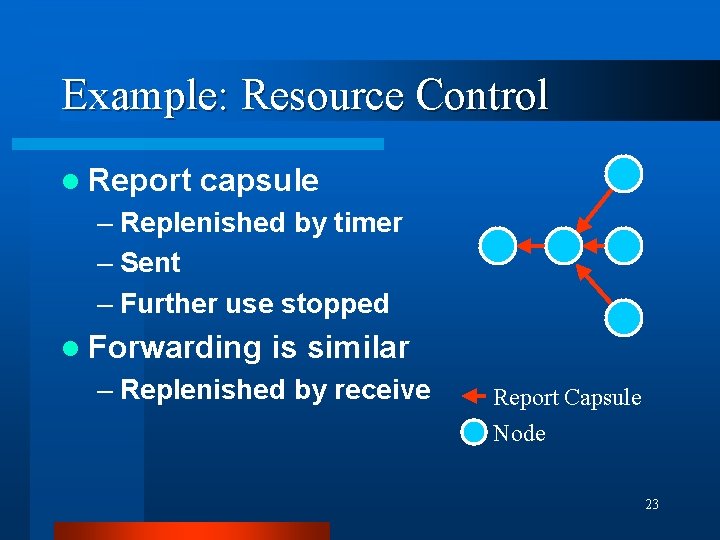
Example: Resource Control l Report capsule – Replenished by timer – Sent – Further use stopped l Forwarding is similar – Replenished by receive Report Capsule Node 23
Protocol Composition l No protocol is an island – Protocols depend on each other l Protocol is the unit of composition – Primary paired with companions l Protocols form a hierarchy l System provided – Code downloader 24
Pathfinder l Primitive routing protocol l Routing scenarios: – Client to server – Server to all clients – Server response to client request l Implementation – Spanning tree behavior – No addresses 25
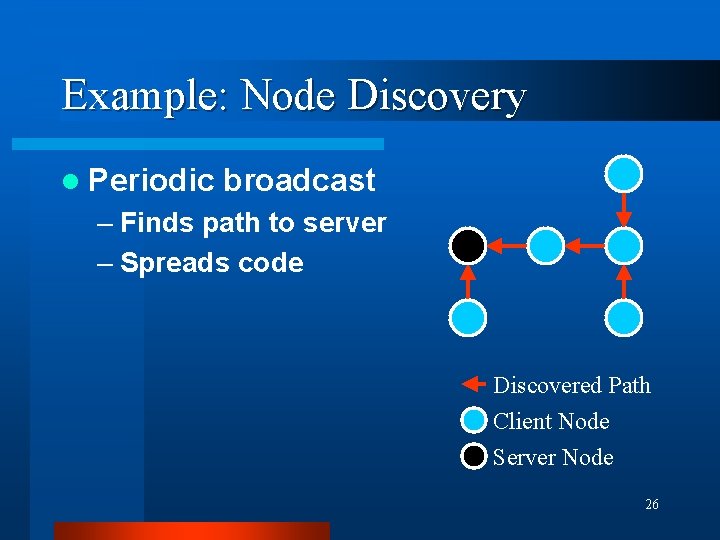
Example: Node Discovery l Periodic broadcast – Finds path to server – Spreads code Discovered Path Client Node Server Node 26
Application Interaction l Protocol Session provides application interface l Trust barrier – Only byte arrays are exchanged l Abstracts raw protocol – Insulation from versioning issues l Similar to standard socket interfaces 27
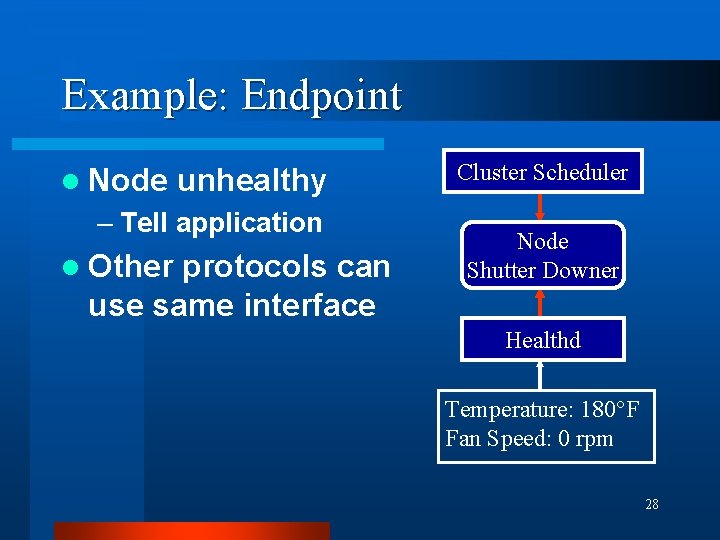
Example: Endpoint l Node unhealthy – Tell application l Other protocols can use same interface Cluster Scheduler Node Shutter Downer Healthd Temperature: 180°F Fan Speed: 0 rpm 28
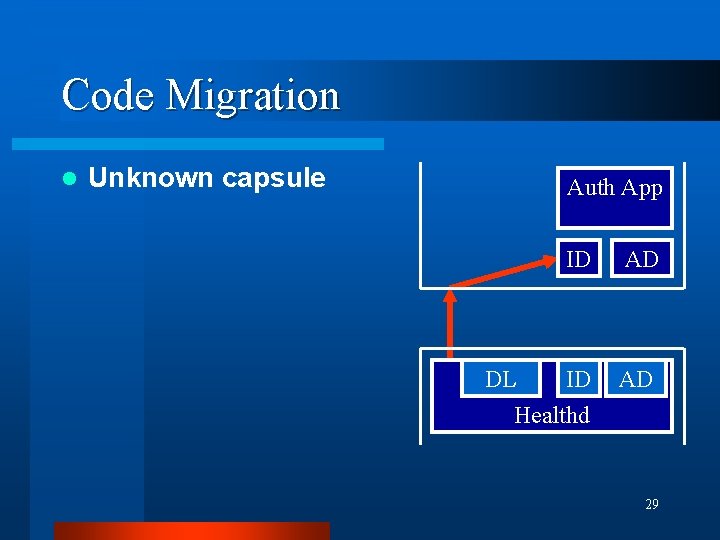
Code Migration l Unknown capsule Auth App DL ID AD Healthd 29
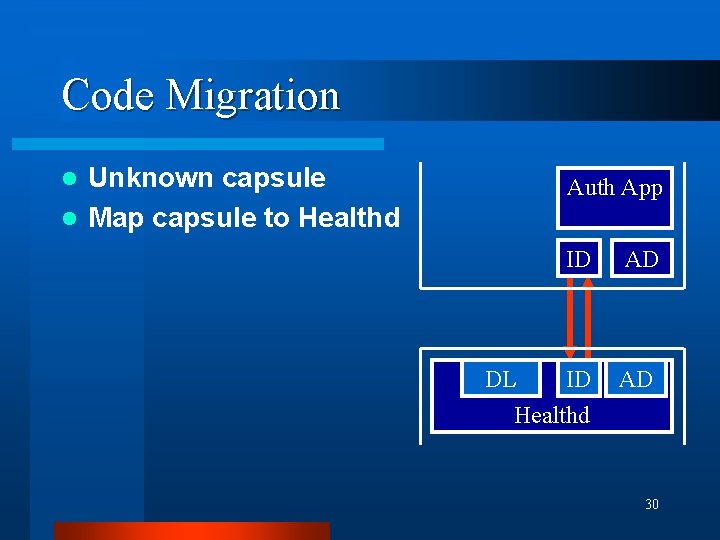
Code Migration Unknown capsule l Map capsule to Healthd l Auth App DL ID AD Healthd 30
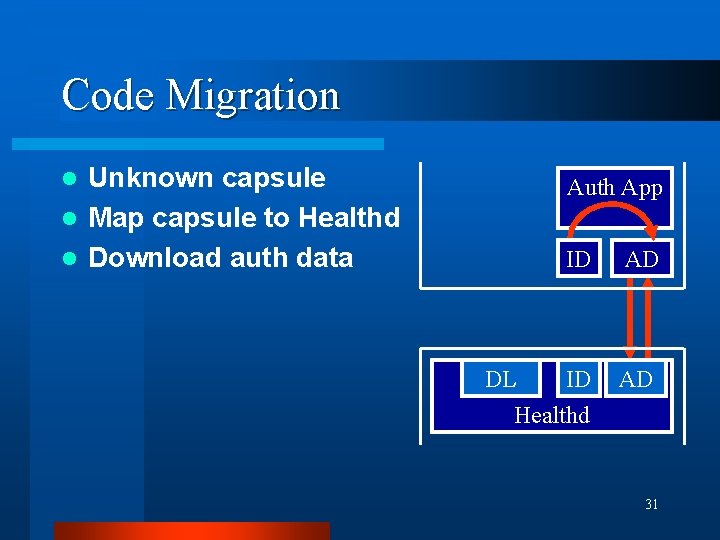
Code Migration Unknown capsule l Map capsule to Healthd l Download auth data l Auth App DL ID AD Healthd 31
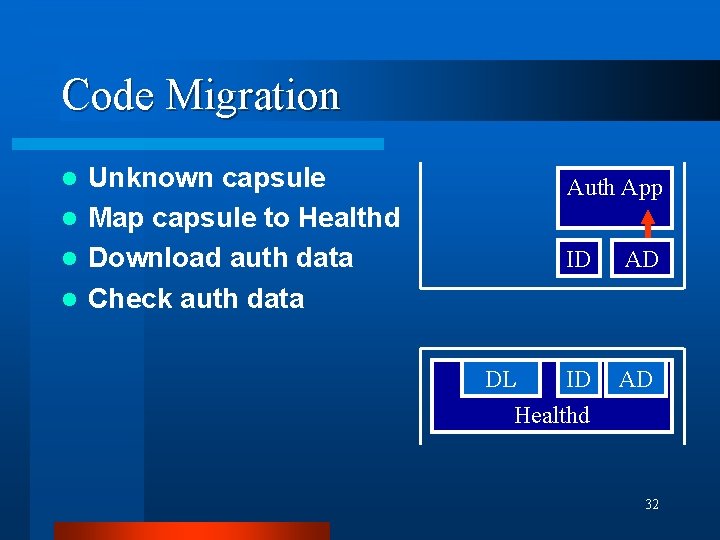
Code Migration Unknown capsule l Map capsule to Healthd l Download auth data l Check auth data l Auth App DL ID AD Healthd 32
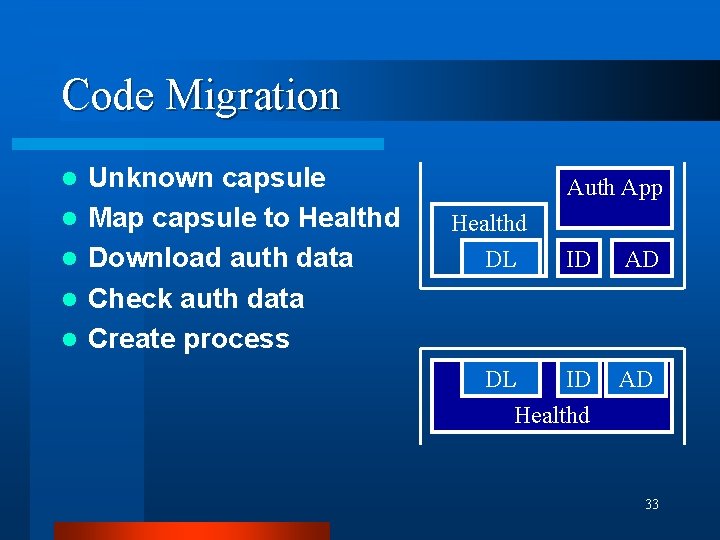
Code Migration l l l Unknown capsule Map capsule to Healthd Download auth data Check auth data Create process Auth App Healthd DL DL ID AD Healthd 33
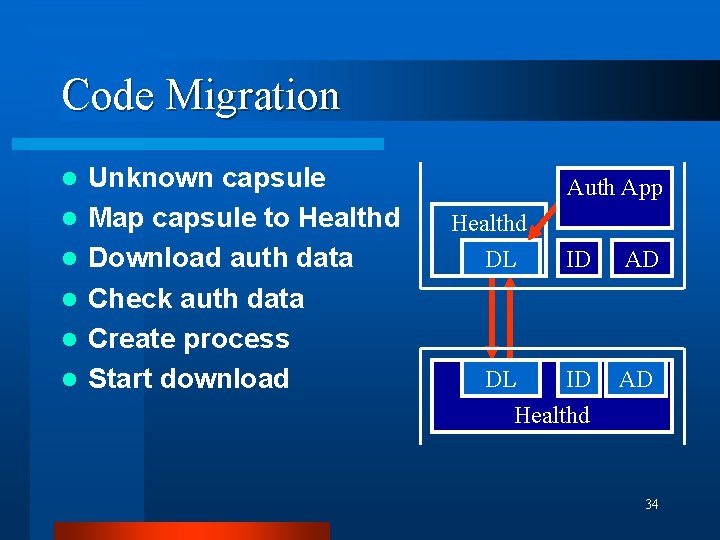
Code Migration l l l Unknown capsule Map capsule to Healthd Download auth data Check auth data Create process Start download Auth App Healthd DL DL ID AD Healthd 34
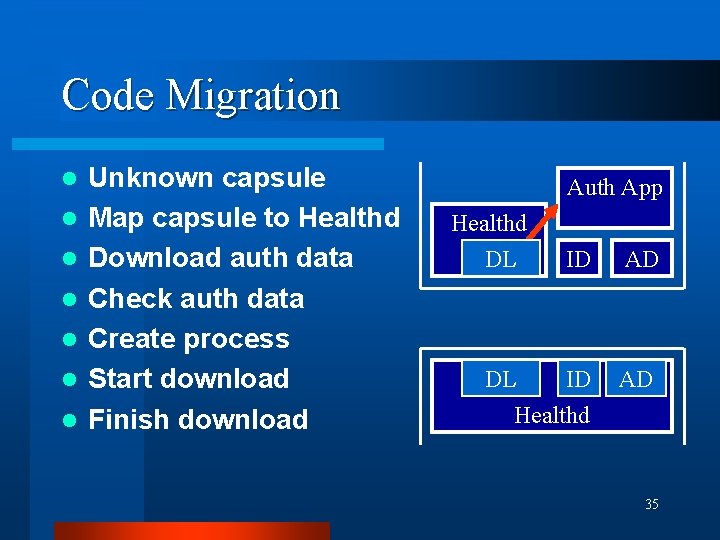
Code Migration l l l l Unknown capsule Map capsule to Healthd Download auth data Check auth data Create process Start download Finish download Auth App Healthd DL DL ID AD Healthd 35
![Related Work l Resource control – RCANE[Menage 00], SNAP[Moore 01] l Security – SANE[Alexander Related Work l Resource control – RCANE[Menage 00], SNAP[Moore 01] l Security – SANE[Alexander](http://slidetodoc.com/presentation_image/dea7f0a9c969f311043b19b3a729e206/image-36.jpg)
Related Work l Resource control – RCANE[Menage 00], SNAP[Moore 01] l Security – SANE[Alexander 98], SANTS[Murphy 01] l Protocol composition – CANES[Bhattacharjee 99] 36
Bees v 0. 5. 0 l 50, 000+ Lines of Code l 30 -page manual l Example application l Available at: www. cs. utah. edu/flux/janos 37
Conclusion l Rich environment – Support for node administrators – Support for protocol authors l Key Features – Security and resource control – Protocol composition – Isolates interaction with end-user apps 38
- Slides: 38