Bachir Babale CSEPtu 590 382006 Crypto Graphics Cryptography
Bachir Babale CSEPtu 590 3/8/2006 Crypto. Graphics: Cryptography using Graphics Processing Units
Outline Motivations n GPU Operations n Stream Ciphers n Block Ciphers (omitted) n Building a Secure System n PVP-UAB n Conclusion n 3/9/2006 Bachir Babale 2
Motivations New CPU performance model: parallelism n GPUs are already highly parallel n 24 fragment shading pipes n 100 s of hardware threads n 150 Giga FLOPS (Nvidia’s G 70) n 3/9/2006 Bachir Babale 3
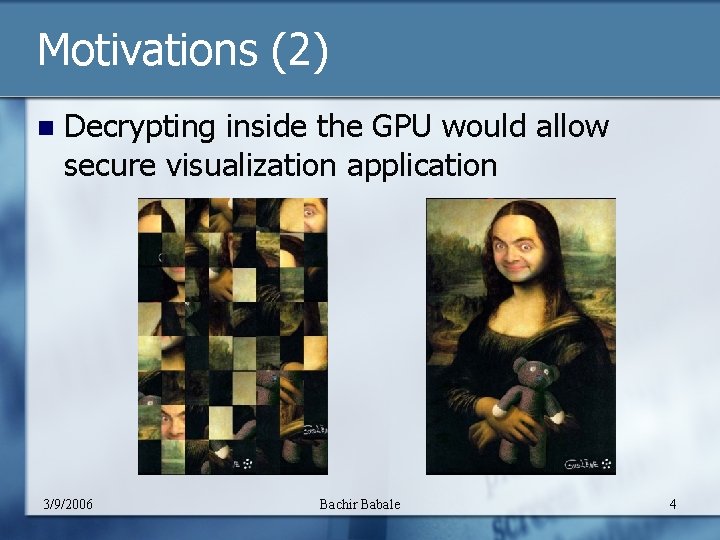
Motivations (2) n Decrypting inside the GPU would allow secure visualization application 3/9/2006 Bachir Babale 4
GPU Operations 32 bit pixels processed as floating points n RGB or RGBA formats in front/back buffer n Operations used for cryptography: n Copying pixels between coordinates n Color maps n Logical XOR n Slowest operations in GPU n n No modular arithmetic for large integers 3/9/2006 Bachir Babale 5
Stream Ciphers n Synchronous Binary Additive Stream Cipher n n Stream of pseudorandom digits XOR plaintext/ciphertext n n Algorithm for GPU n n n 3/9/2006 Pre-compute keystream Load into GPU memory Load ciphertext into memory area with XOR enabled Bachir Babale Benefits of parallel processing diminished if data is too small XOR rate of 105. 0 MB/s for a 600 x 600 area (75. 5% of CPU) 6
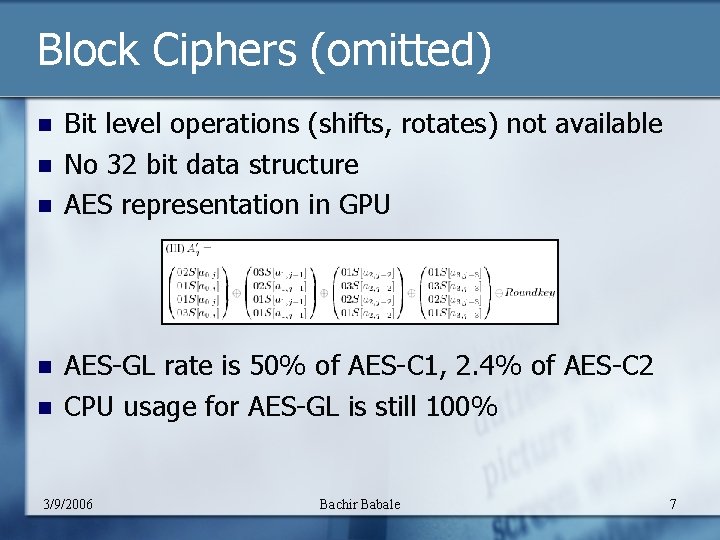
Block Ciphers (omitted) n n n Bit level operations (shifts, rotates) not available No 32 bit data structure AES representation in GPU AES-GL rate is 50% of AES-C 1, 2. 4% of AES-C 2 CPU usage for AES-GL is still 100% 3/9/2006 Bachir Babale 7
Building a secure system Server, Proxy, Client over an untrusted network n GPU contains pre-installed certificate n The data remains encrypted until in the GPU n Dynamic session key -> Need for authentication n Close to ideal 24 fps for videoconferencing n 500 updates/s for thin client application n 3/9/2006 Bachir Babale 8
PVP-UAB n n Content Output Path Protected Video Path - User Accessible Bus n n OS must verify valid subsystem n n n Encrypts premium content on the bus to prevent hardware snoop hacks Unique keys A challenge that leverages the complex arrangement of a large number of gates and a complex state model in the GPU 128 bit AES MPG 2 and Windows Media 9 compression 2048 bit Diffie Hellman 3/9/2006 Bachir Babale 9
Conclusion GPUs can be used to offload the CPUs to apply stream ciphers on large segments n GPU can serve as the base for a trusted computing visualization platform n PVP-UAB brings authentication and compression n Need to develop ciphers that can better exploit the capabilities of modern GPUs n 3/9/2006 Bachir Babale 10
References n Crypto. Graphics: Secret Key Cryptography Using Graphics Cards n http: //www 1. cs. columbia. edu/~dcook/pubs/CTRSA-corrected. pdf Remotely Keyed Cryptographics. Secure Remote Display Access Using. (Mostly) Untrusted Hardware Debra L. Cook. , John Ioannidis. , Angelos D. Keromytis. , Jake Luck Debra L. Cook. , Ricardo Baratto. , Angelos D. Keromytis n n n http: //www. ncl. cs. columbia. edu/publications/icics 2005. pdf Protected Interactive 3 D Graphics Via Remote Rendering David Koller, Michael Turitzin, Marc Levoy), Marco Tarini, Giuseppe Croccia http: //graphics. stanford. edu/papers/protected. pdf GPGPU IEEE Visualization 2005 TUTORIAL http: //www. gpgpu. org/vis 2005/ (03/05/2006) Output Content Protection and Windows Longhorn http: //www. microsoft. com/whdc/device/stream/output_protect. mspx (03/05/2006) 3/9/2006 Bachir Babale 11
- Slides: 11