Authors Jakub Suchorab Marcin Dudek Kinga Staszkiewicz Joanna

Authors: Jakub Suchorab Marcin Dudek Kinga Staszkiewicz Joanna Walkiewicz Co-author: Jacek Gajewski R E T 0 I N 0 2 2 N A Vienna, February 2020 T IO N A L C O N F E R E N C E O N N U C L E A R S E C U R IT Y EFFECTIVE FUZZ TESTING FOR PROGRAMMABLE LOGIC CONTROLLERS VULNERABILITY RESEARCH TO ENSURE NUCLEAR SAFETY IAEA-CN-278/619 Paper presentation
Presentation outline ► Introduction ► Fuzz testing ► Laboratory configuration ► Research on methodology ► Found zero-day vulnerability ► Results ► Summary 2
Introduction • Programmable Logic Controllers (PLCs) plays an important role in Industrial Control Systems (ICS); • Examples of incidents involving PLCs: • Stuxnet worm attack on Iranian nuclear facilities – reprogrammed PLC damaged centrifuges (2010), • Malfunctioning PLC led to shut down of reactor in the Browns Ferry nuclear power plant (2006); • The security of communication of PLCs should be tested; • In was decided to create a specialized laboratory in order to define an efficient fuzz testing methodology for PLCs. 3
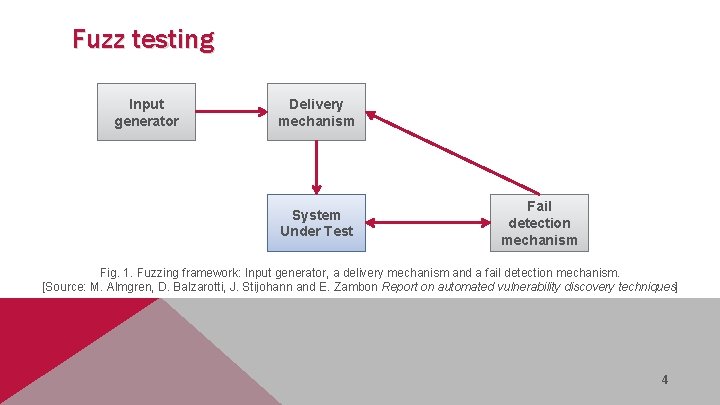
Fuzz testing Input generator Delivery mechanism System Under Test Fail detection mechanism Fig. 1. Fuzzing framework: Input generator, a delivery mechanism and a fail detection mechanism. [Source: M. Almgren, D. Balzarotti, J. Stijohann and E. Zambon Report on automated vulnerability discovery techniques] 4
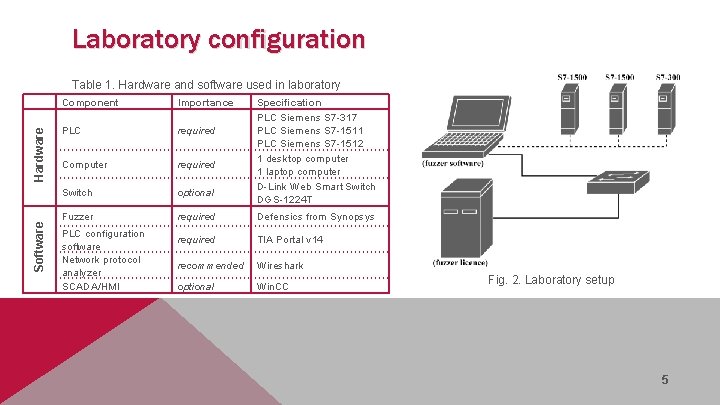
Laboratory configuration Software Hardware Table 1. Hardware and software used in laboratory Component Importance PLC required Computer required Switch optional Fuzzer required Defensics from Synopsys required TIA Portal v 14 recommended Wireshark optional Win. CC PLC configuration software Network protocol analyzer SCADA/HMI Specification PLC Siemens S 7 -317 PLC Siemens S 7 -1511 PLC Siemens S 7 -1512 1 desktop computer 1 laptop computer D-Link Web Smart Switch DGS-1224 T Fig. 2. Laboratory setup 5
Research on methodology 1. Initial configuration and interoperability testing; 2. Encountered false positive error caused by faulty Profinet DCP protocol test suite; 3. Full-scale tests of available protocols; 4. PLC failure encountered during IPv 4 protocol testing. 6
Found zero-day vulnerability • IP packet with modified header sent to S 7 -1500 PLC about 33000 times; • In result, no communication with the target using IP-based protocols; • Report including proof sent to Siemens CERT; • Vulnerability was classified as not previously known; • The code CVE-2018 -13805 was assigned to the vulnerability; 7
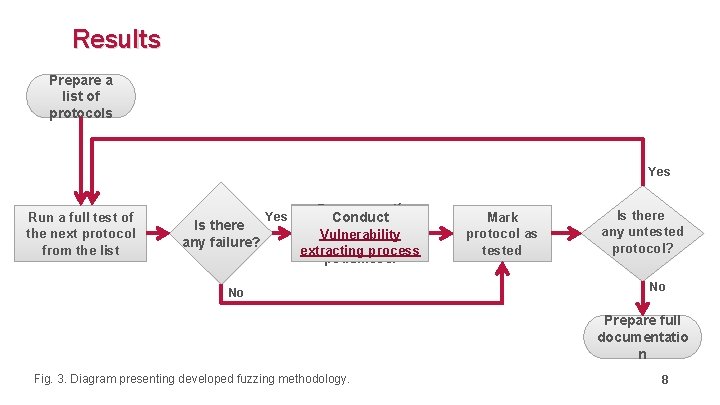
Results Prepare a list of protocols Yes Run a full test of the next protocol from the list Is there any failure? Yes Przeprowadź Conduct proces Vulnerability wyodrębniania extracting process podatności No Mark protocol as tested Is there any untested protocol? No Prepare full documentatio n Fig. 3. Diagram presenting developed fuzzing methodology. 8
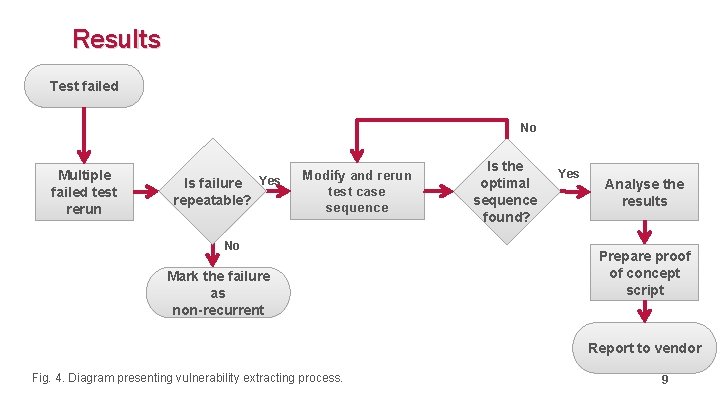
Results Test failed No Multiple failed test rerun Is failure Yes repeatable? Modify and rerun test case sequence No Mark the failure as non-recurrent Is the optimal sequence found? Yes Analyse the results Prepare proof of concept script Report to vendor 9 Fig. 4. Diagram presenting vulnerability extracting process. 9
Summary • The proposed systematic approach to fuzz testing of PLCs allows the examination of new and existing devices in order to find vulnerabilities associated with incorrect protocol processing; • No testing can cover every single possible combination of test cases, so the goal is to find as many vulnerabilities as possible in a systematic way, thus reducing a threat of undetected ones. 10

R E T 0 I N 0 2 2 N A Vienna, February 2020 T IO N A L C O N F E R E N C E O N N U C L E A R S E C U R IT Y Thank you for your attention!
- Slides: 11