Synchronization CSCI 47806780 Mutual Exclusion Concurrency and collaboration
Synchronization CSCI 4780/6780
Mutual Exclusion • Concurrency and collaboration are fundamental to distributed systems • Simultaneous access to resources • Concurrency control prevents resource corruption due to simultaneous access • Correctness – Mutual exclusion – No deadlocks – No starvation
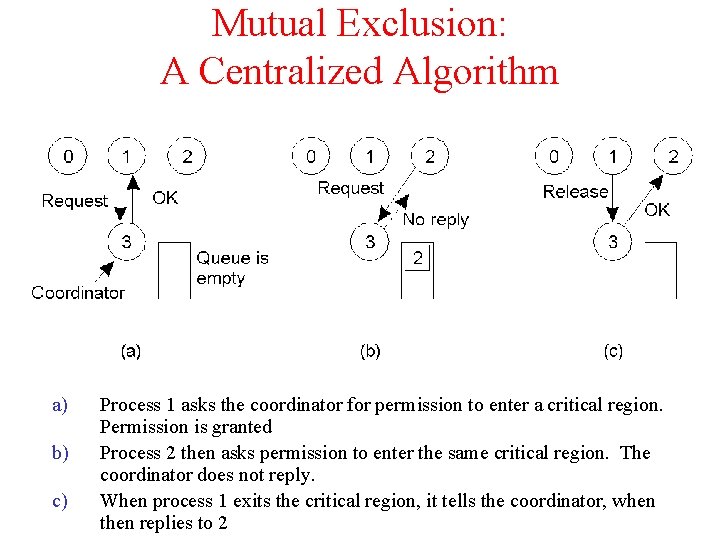
Mutual Exclusion: A Centralized Algorithm a) b) c) Process 1 asks the coordinator for permission to enter a critical region. Permission is granted Process 2 then asks permission to enter the same critical region. The coordinator does not reply. When process 1 exits the critical region, it tells the coordinator, when then replies to 2
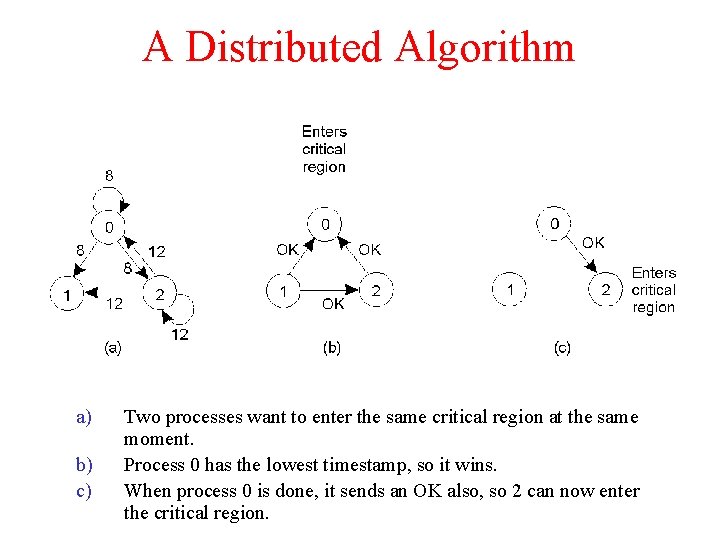
A Distributed Algorithm a) b) c) Two processes want to enter the same critical region at the same moment. Process 0 has the lowest timestamp, so it wins. When process 0 is done, it sends an OK also, so 2 can now enter the critical region.
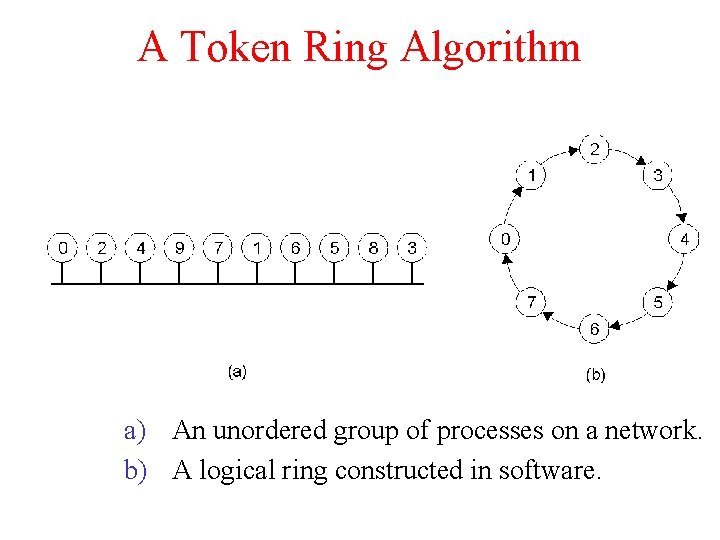
A Token Ring Algorithm a) An unordered group of processes on a network. b) A logical ring constructed in software.
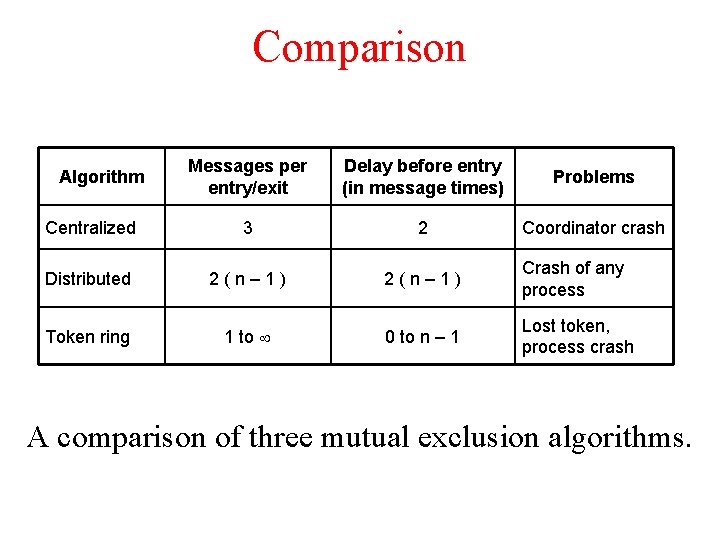
Comparison Messages per entry/exit Delay before entry (in message times) Problems Centralized 3 2 Coordinator crash Distributed 2(n– 1) Crash of any process Token ring 1 to 0 to n – 1 Lost token, process crash Algorithm A comparison of three mutual exclusion algorithms.
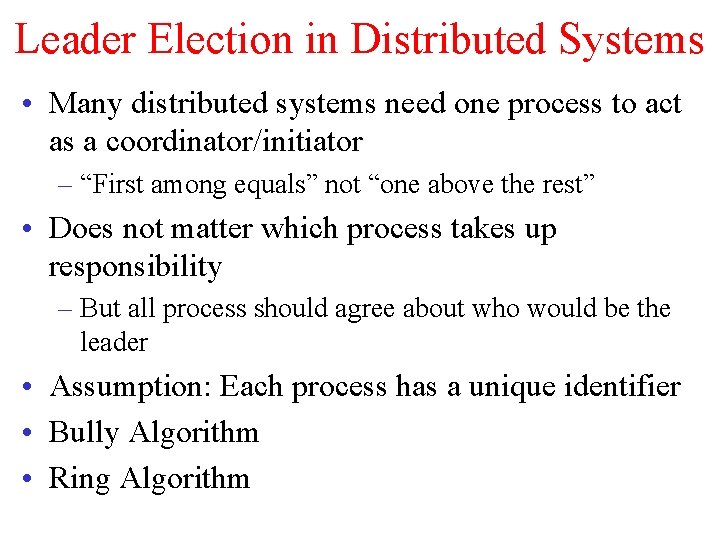
Leader Election in Distributed Systems • Many distributed systems need one process to act as a coordinator/initiator – “First among equals” not “one above the rest” • Does not matter which process takes up responsibility – But all process should agree about who would be the leader • Assumption: Each process has a unique identifier • Bully Algorithm • Ring Algorithm
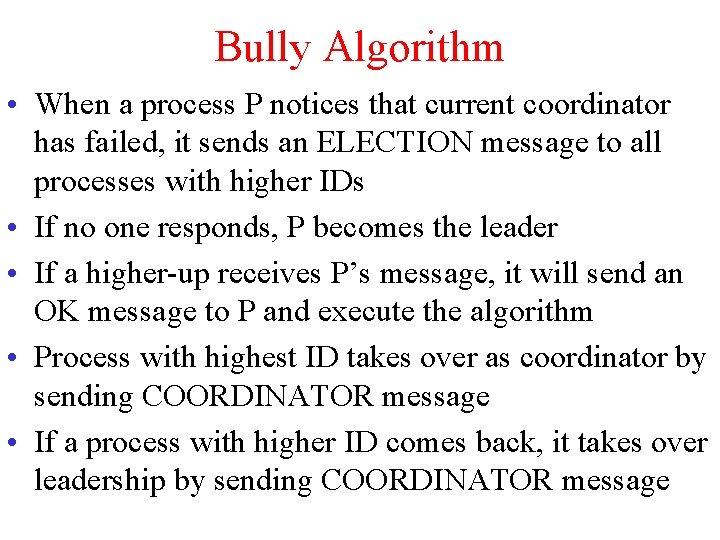
Bully Algorithm • When a process P notices that current coordinator has failed, it sends an ELECTION message to all processes with higher IDs • If no one responds, P becomes the leader • If a higher-up receives P’s message, it will send an OK message to P and execute the algorithm • Process with highest ID takes over as coordinator by sending COORDINATOR message • If a process with higher ID comes back, it takes over leadership by sending COORDINATOR message
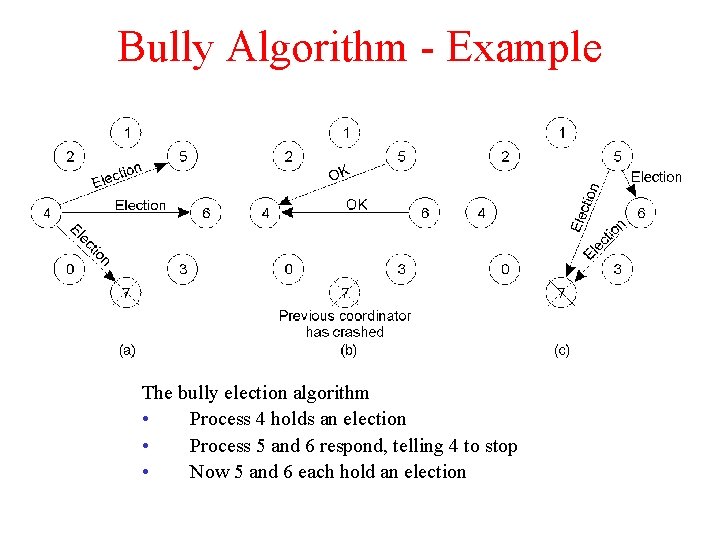
Bully Algorithm - Example The bully election algorithm • Process 4 holds an election • Process 5 and 6 respond, telling 4 to stop • Now 5 and 6 each hold an election
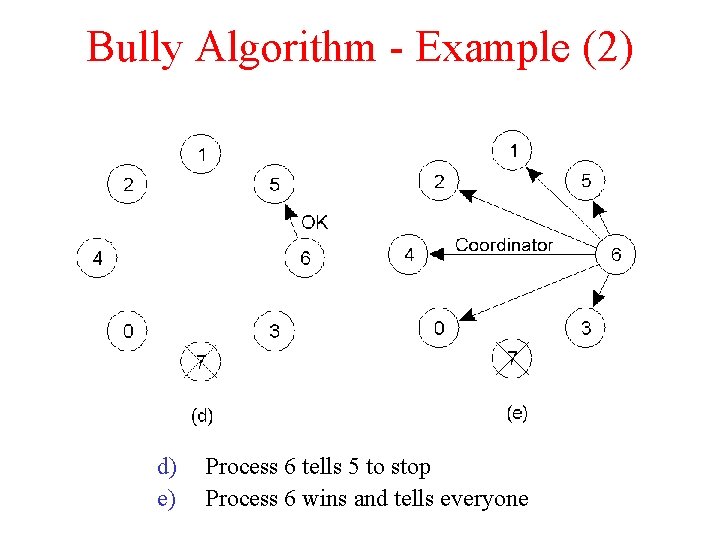
Bully Algorithm - Example (2) d) e) Process 6 tells 5 to stop Process 6 wins and tells everyone
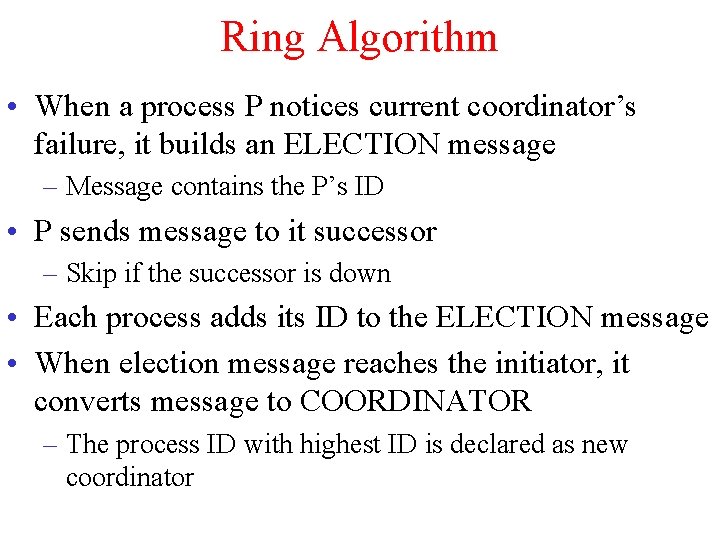
Ring Algorithm • When a process P notices current coordinator’s failure, it builds an ELECTION message – Message contains the P’s ID • P sends message to it successor – Skip if the successor is down • Each process adds its ID to the ELECTION message • When election message reaches the initiator, it converts message to COORDINATOR – The process ID with highest ID is declared as new coordinator
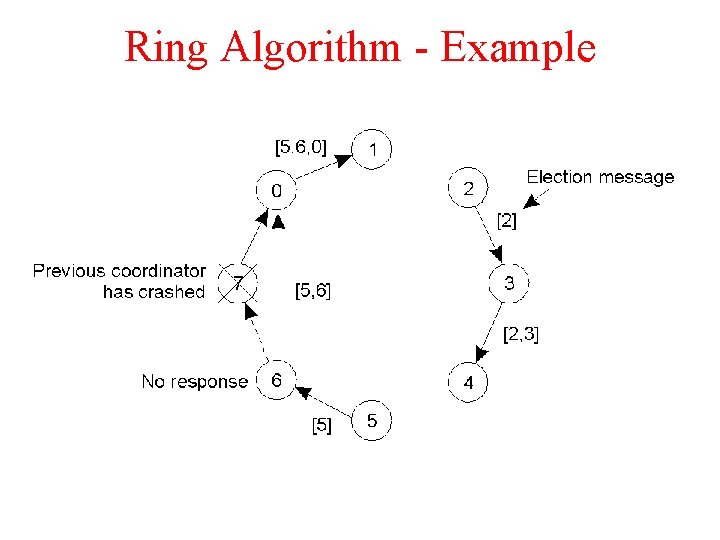
Ring Algorithm - Example
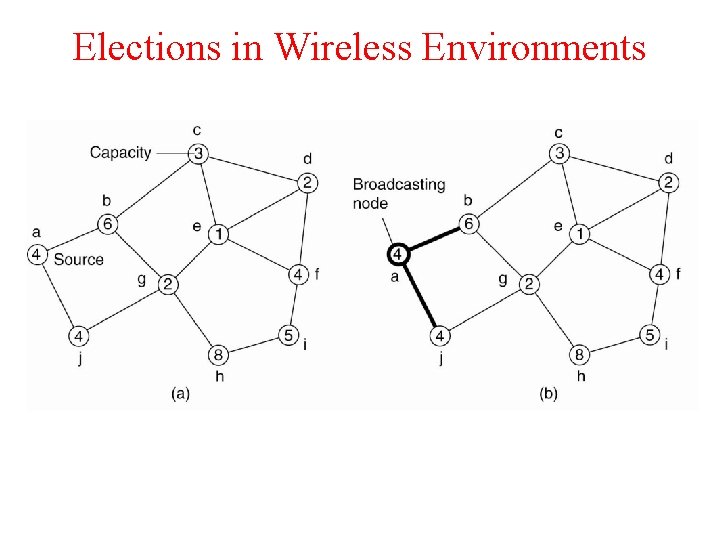
Elections in Wireless Environments
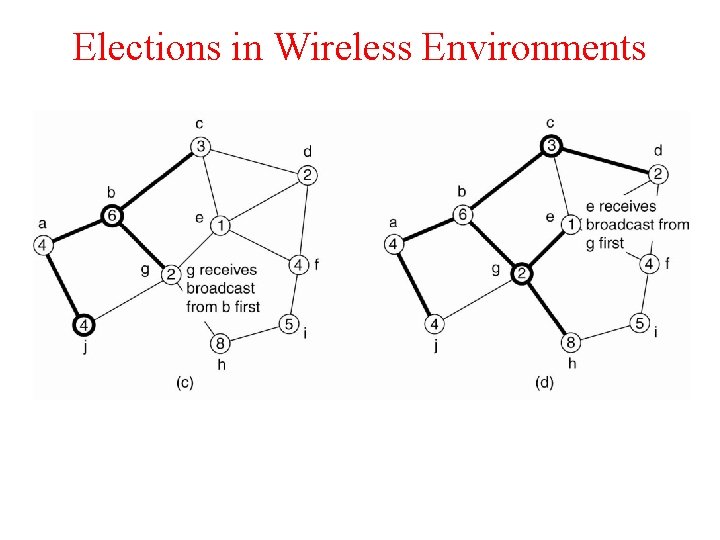
Elections in Wireless Environments
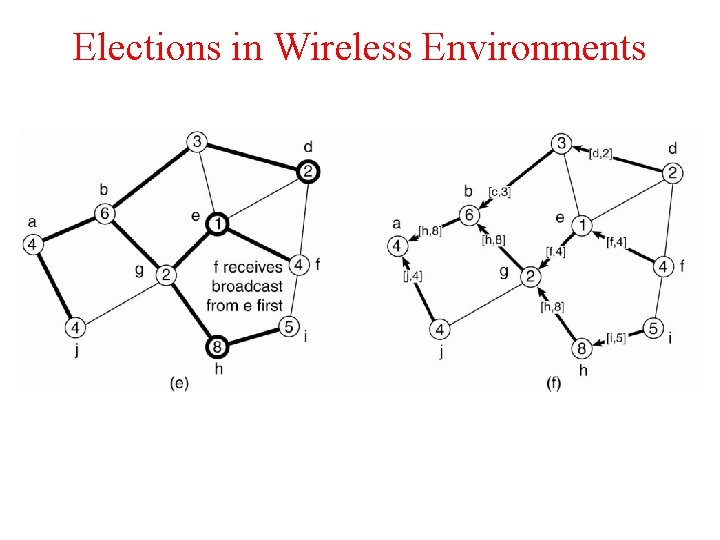
Elections in Wireless Environments
- Slides: 15