RSA publickey encryption Each participant has a public
RSA public-key encryption • Each participant has a public key and a private key • Both keys specify 1 -to-1 functions from a message D to itself; let SA apply the secret key for user A and PA apply the public key - these functions are inverses, as seen here M = SA(PA (M)) and M = PA (SA (M)) • Only user A (Alice) should be able to compute SA ( ) is a reasonable length of time; everyone knows PA and can compute PA ( ) efficiently • The next slides describe how this system works
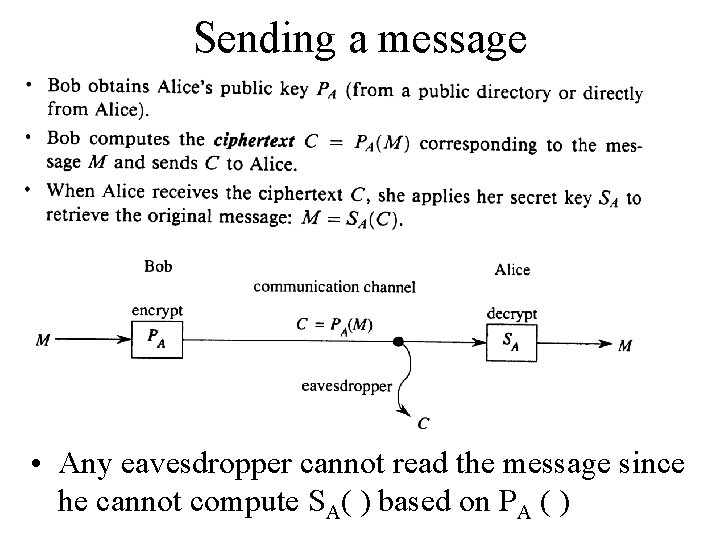
Sending a message • Any eavesdropper cannot read the message since he cannot compute SA( ) based on PA ( )
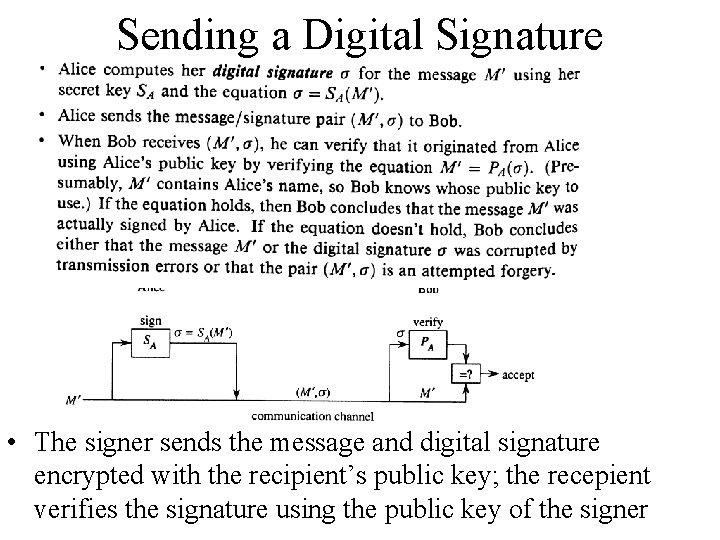
Sending a Digital Signature • The signer sends the message and digital signature encrypted with the recipient’s public key; the recepient verifies the signature using the public key of the signer
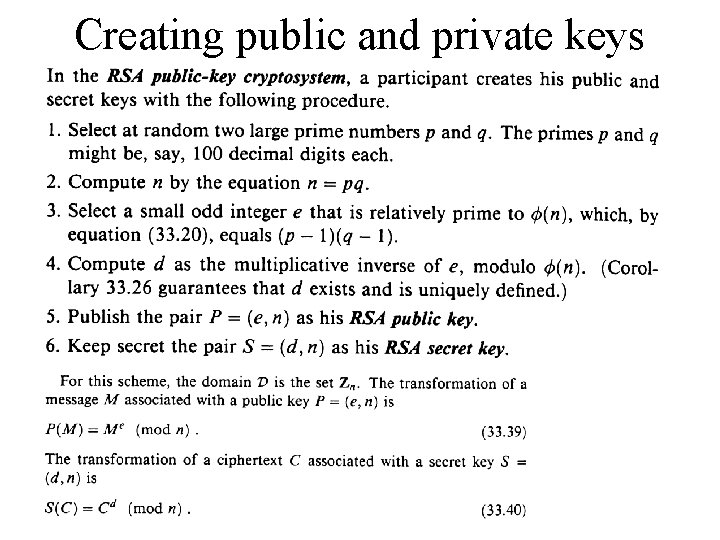
Creating public and private keys
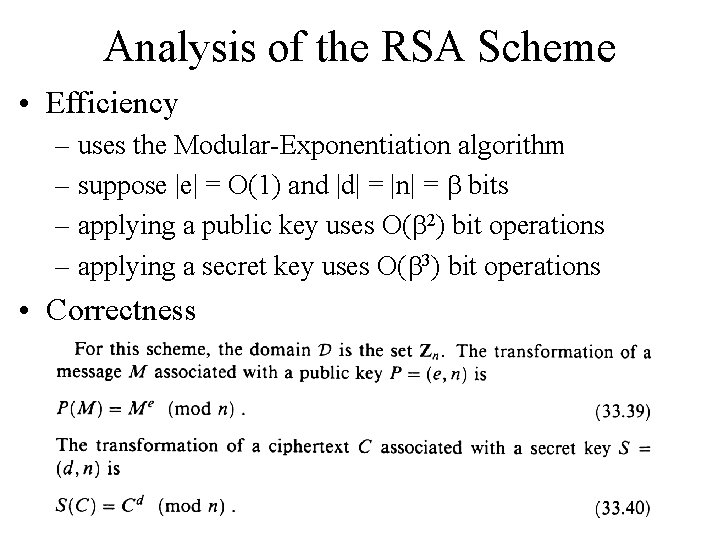
Analysis of the RSA Scheme • Efficiency – uses the Modular-Exponentiation algorithm – suppose |e| = O(1) and |d| = |n| = b bits – applying a public key uses O(b 2) bit operations – applying a secret key uses O(b 3) bit operations • Correctness
Is it really secure? • The prime numbers must be large – usually 100 -200 digits in length, methods for testing primality are discussed in the next section – the product is impractical to factor using any known technique, as we see in the final section • Alternative schemes – fast non-public key systems, both keys are identical, the sender selects a key and sends it to the recipient using the standard approach; this message is very short – the recipient decrypts the key to then be used to decrypt the larger message – one way hash functions can be used for digital signatures (see text for details)
- Slides: 6