Monitoring Reporting 6192021 Planning a Monitoring and Reporting
- Slides: 12
Monitoring- Reporting ¡ ¡ 6/19/2021 Planning a Monitoring and Reporting Strategy Intrusion Detection System Monitoring ISA Server Activity Demo Configuration Faculty : Trần Thị Ngọc Hoa 1
Monitoring and Reporting Strategy Design a plan for archiving the logs Create a schedule for regular review of the logs Create a strategy for how to respond to critical events Document your strategy Determine the information that is the most critical Categorize the information that you need to collect 6/19/2021 Faculty : Trần Thị Ngọc Hoa 2
Intrusion Detection System ¡ ¡ ¡ 6/19/2021 ISA Server software’s feature When the IDS dectects an attack or a specific system event An alert can be triggered Send email to the administrator Stop the Firewall service Write to the system event log Run a program or a script Implementation : l Packet level l Application level Faculty : Trần Thị Ngọc Hoa 3
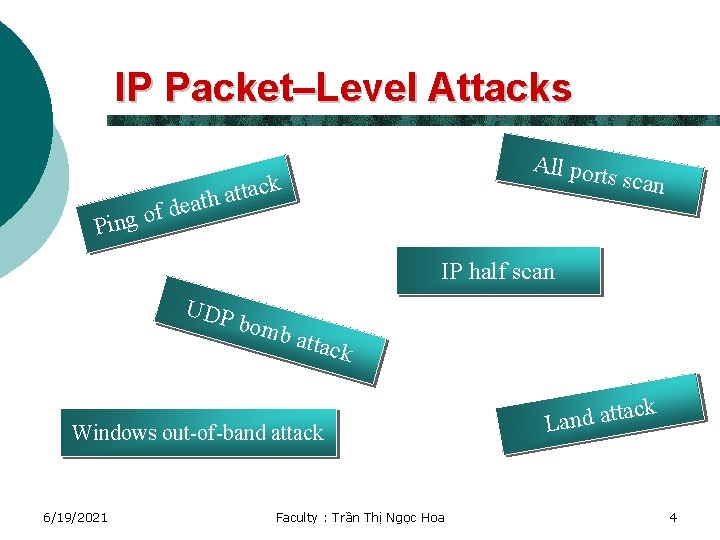
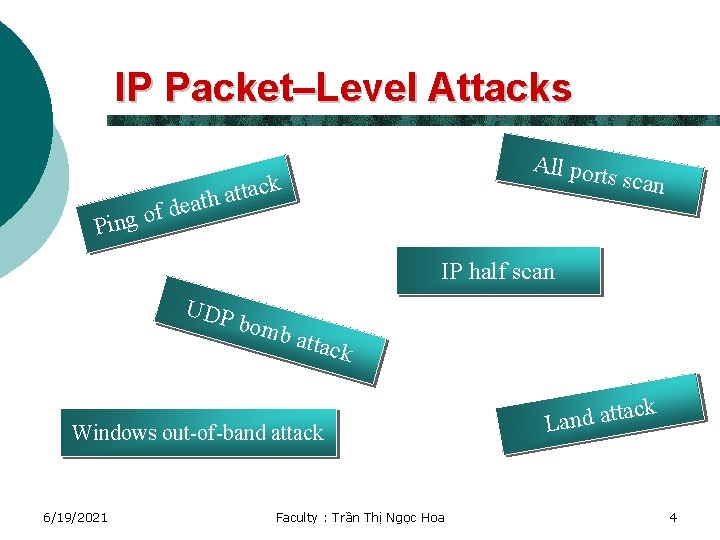
IP Packet–Level Attacks ea d f o Ping All port s scan ck a t t a h t IP half scan UDP bomb attac k Windows out-of-band attack 6/19/2021 Faculty : Trần Thị Ngọc Hoa k c a t t a d Lan 4
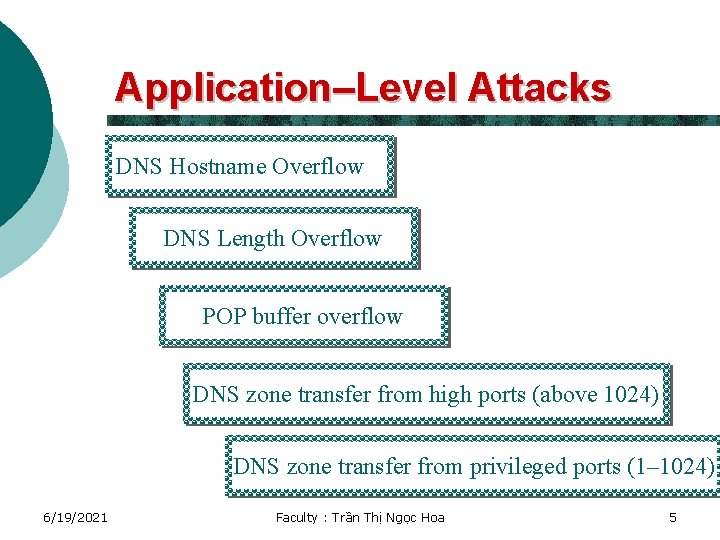
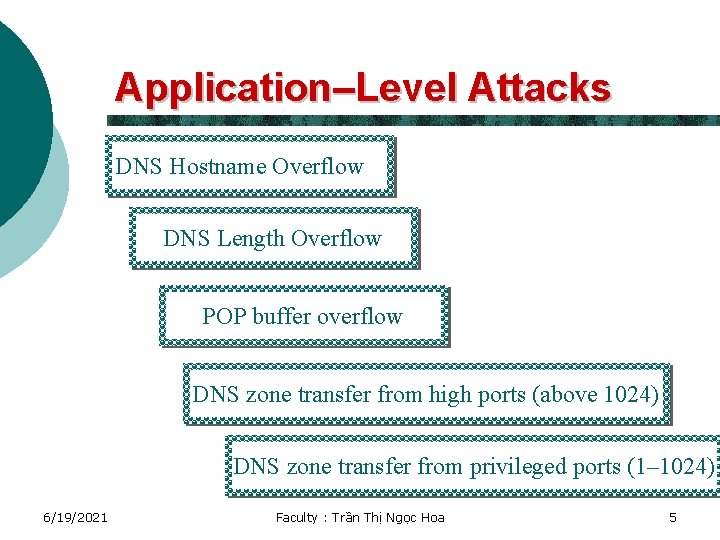
Application–Level Attacks DNS Hostname Overflow DNS Length Overflow POP buffer overflow DNS zone transfer from high ports (above 1024) DNS zone transfer from privileged ports (1– 1024) 6/19/2021 Faculty : Trần Thị Ngọc Hoa 5
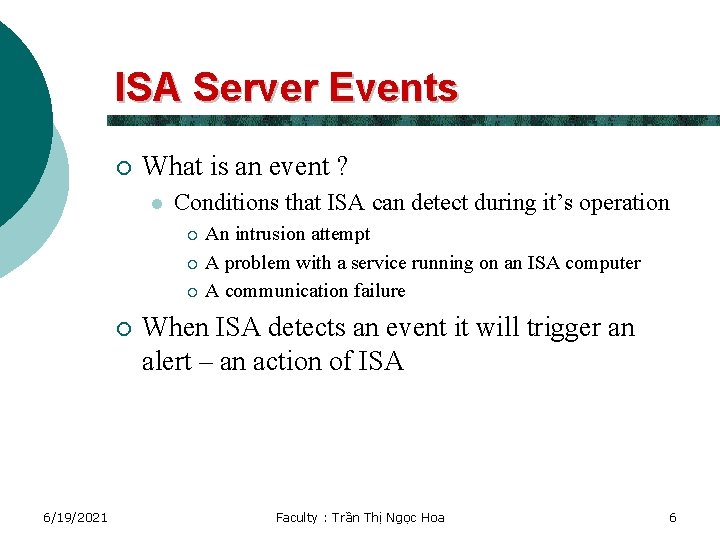
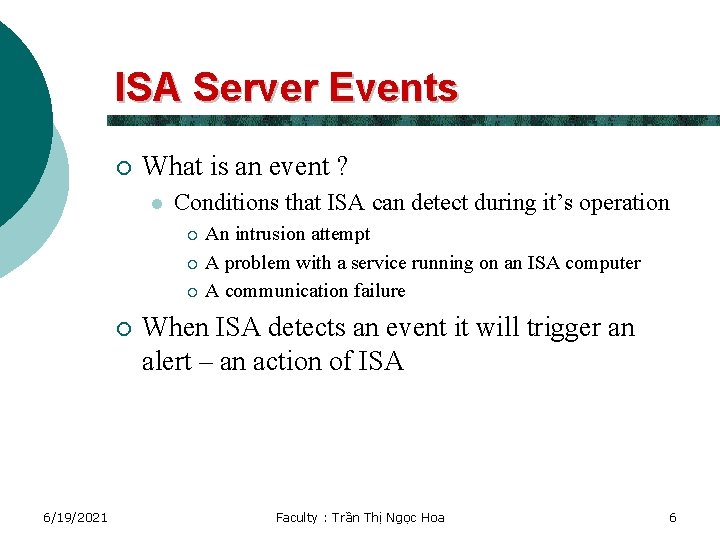
ISA Server Events ¡ What is an event ? l Conditions that ISA can detect during it’s operation An intrusion attempt ¡ A problem with a service running on an ISA computer ¡ A communication failure ¡ ¡ 6/19/2021 When ISA detects an event it will trigger an alert – an action of ISA Faculty : Trần Thị Ngọc Hoa 6
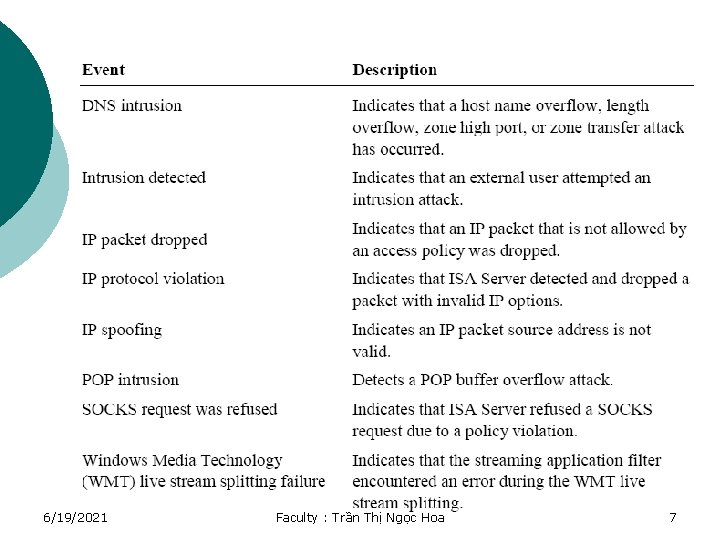
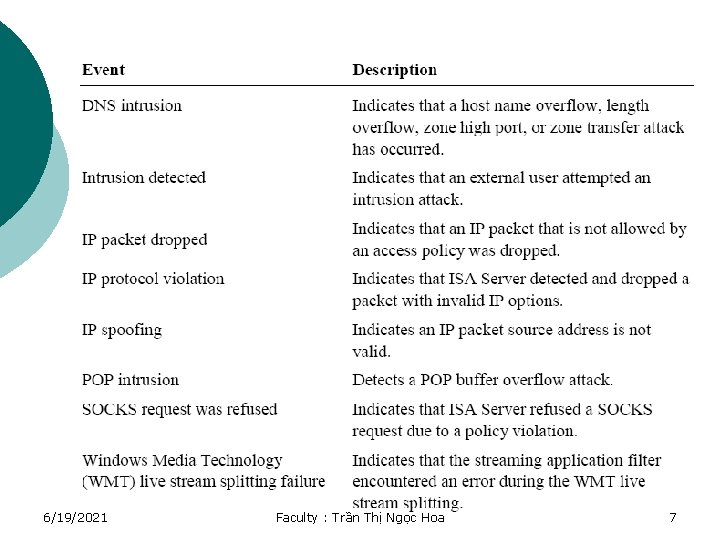
6/19/2021 Faculty : Trần Thị Ngọc Hoa 7
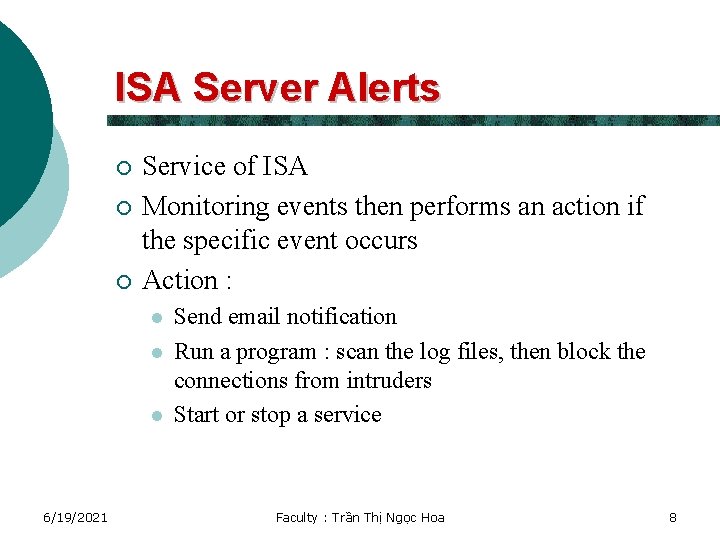
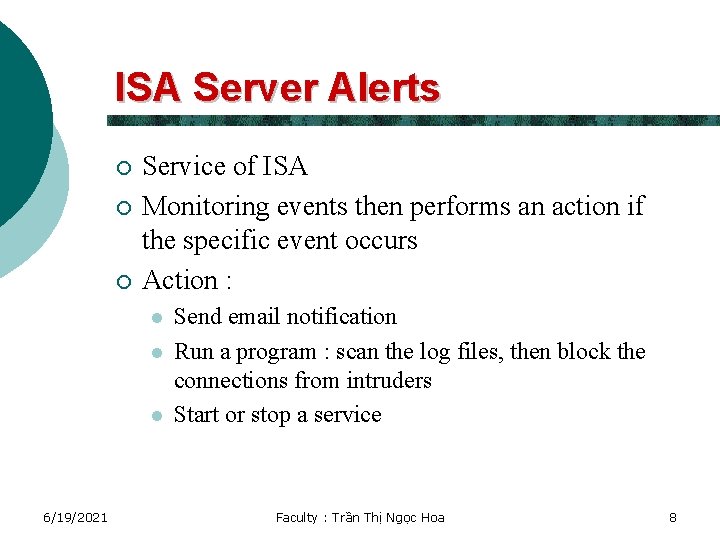
ISA Server Alerts ¡ ¡ ¡ Service of ISA Monitoring events then performs an action if the specific event occurs Action : l l l 6/19/2021 Send email notification Run a program : scan the log files, then block the connections from intruders Start or stop a service Faculty : Trần Thị Ngọc Hoa 8
Monitoring ISA Server Activity ¡ ¡ By Logging Purpose : l ¡ Packet filter logs : l ¡ record attempts to communicate by using the Firewall service Web Proxy service logs : l 6/19/2021 record attempts to pass packets through ISA server Firewall service logs : l ¡ Analyze the usage, performance and security monitoring record attempts to communicate by using the Web Proxy service Faculty : Trần Thị Ngọc Hoa 9
Monitoring ISA Server Activity ¡ Log format : l l ¡ By default, ISA Server can only log dropped packets. l l 6/19/2021 %ISAinstallfolderISALogs W 3 C ISA ODBC Disable dropped packet logging to reduce server load. Disable logging for dropped packets only if your security policy does not require this information. Faculty : Trần Thị Ngọc Hoa 10
Analyzing ISA Server Activity by Using Reports ¡ 6/19/2021 Reports are generated from a database that includes the collected data from the ISA log files. Faculty : Trần Thị Ngọc Hoa 11
Demo Configuration 6/19/2021 Faculty : Trần Thị Ngọc Hoa 12