Metasploit assignment Tools used Metasploit on Kali Metasploitable
Metasploit assignment • Tools used • • Metasploit on Kali Metasploitable – intentional vulnerable Ubuntu package NMAP – used to get IP address Nessus – scanned for vulnerabilities • Result • Found many vulnerabilities • Successfully exploited one that interested me Ahmed Alkaysi
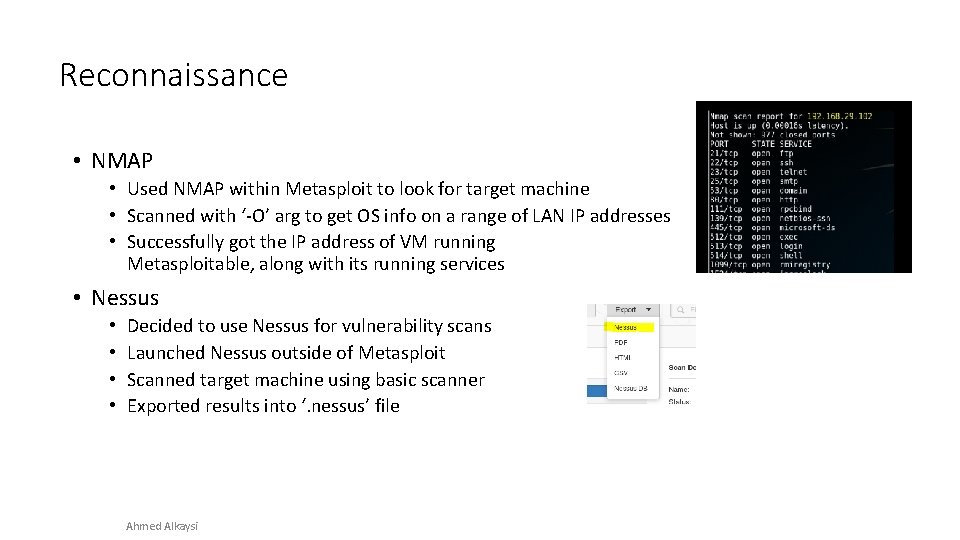
Reconnaissance • NMAP • Used NMAP within Metasploit to look for target machine • Scanned with ‘-O’ arg to get OS info on a range of LAN IP addresses • Successfully got the IP address of VM running Metasploitable, along with its running services • Nessus • • Decided to use Nessus for vulnerability scans Launched Nessus outside of Metasploit Scanned target machine using basic scanner Exported results into ‘. nessus’ file Ahmed Alkaysi
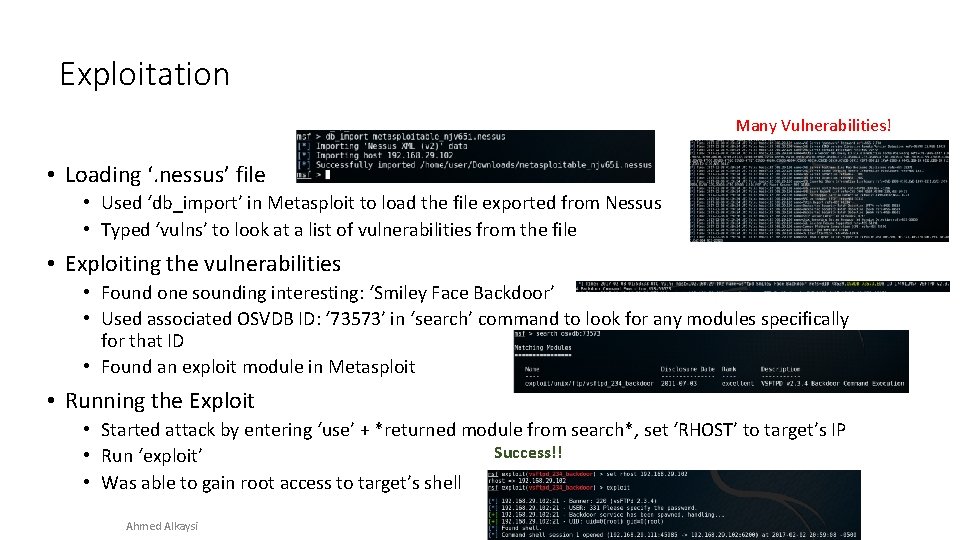
Exploitation Many Vulnerabilities! • Loading ‘. nessus’ file • Used ‘db_import’ in Metasploit to load the file exported from Nessus • Typed ‘vulns’ to look at a list of vulnerabilities from the file • Exploiting the vulnerabilities • Found one sounding interesting: ‘Smiley Face Backdoor’ • Used associated OSVDB ID: ‘ 73573’ in ‘search’ command to look for any modules specifically for that ID • Found an exploit module in Metasploit • Running the Exploit • Started attack by entering ‘use’ + *returned module from search*, set ‘RHOST’ to target’s IP Success!! • Run ‘exploit’ • Was able to gain root access to target’s shell Ahmed Alkaysi
- Slides: 3