Introduction to Information Security Reverse Engineering and Binary
Introduction to Information Security Reverse Engineering and Binary Patching
Reverse Engineering • Restructuring the execution flow of a binary file • What for? • Understanding proprietary code • React. OS • Cryptographic algorithms • Looking for exploits
Reverse Engineering • The problem • Compilation is like a one-way function: comments, names and some structure are lost • Solutions • Look for anchors: constants (especially strings), standard library functions, etc. • Somewhat of an art form • Most of the code is inessential • Programmers are pretty predictable • Compilers are also pretty predictable
IDA • Interactive Dis. Assembler • Navigation • Strings • Standard library functions • Cross references (xrefs) • Documentation • Comments • Variable and function names
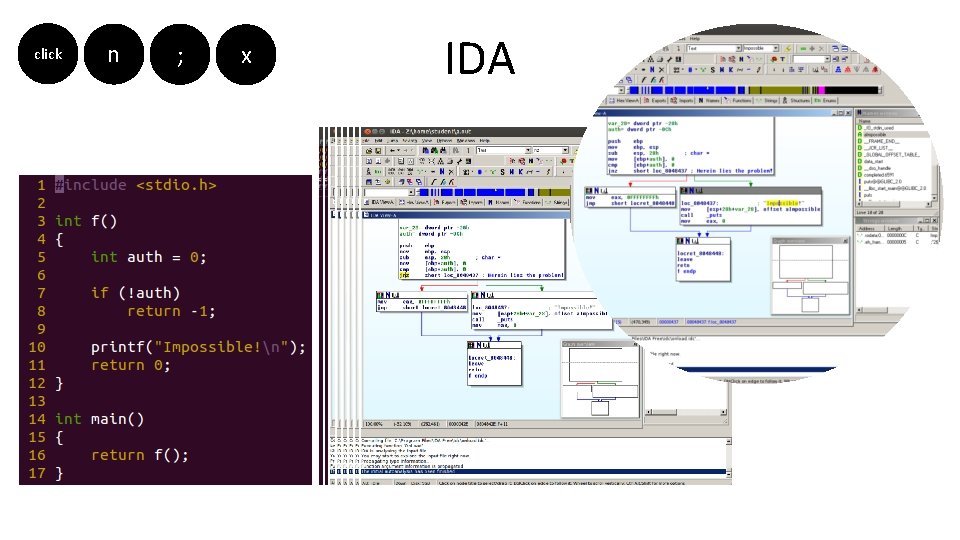
click n ; x IDA
Patching • Changing the execution flow of a binary file • What for? • Small changes • Big changes, when recompilation is not possible (no source code or build environment) • How? • Changing instructions to other instructions • Chaining instructions to redirect to "Dead Zones", and adding more instructions there
![Patching if (!auth) return -1; . . . MOV EAX, [EBP-4] CMP EAX, 0 Patching if (!auth) return -1; . . . MOV EAX, [EBP-4] CMP EAX, 0](http://slidetodoc.com/presentation_image_h/28b2ea4be84222bf00cf5c41f2cd4c6b/image-7.jpg)
Patching if (!auth) return -1; . . . MOV EAX, [EBP-4] CMP EAX, 0 JNE JE _AUTH MOV EAX, -1 RET _AUTH: . . . 8 b 44 24 fc 83 f 8 00 75 74 06 b 8 ff ff c 3
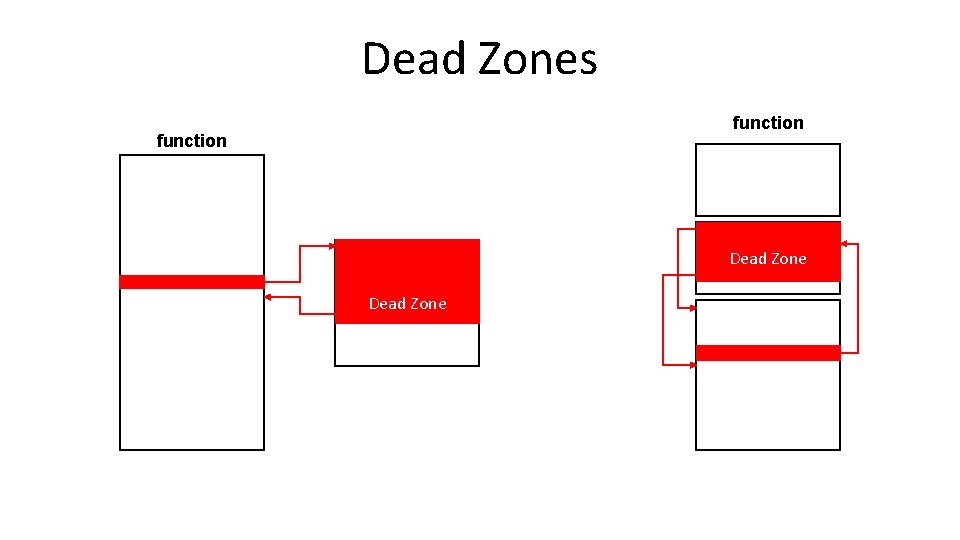
Dead Zones function Dead Zone
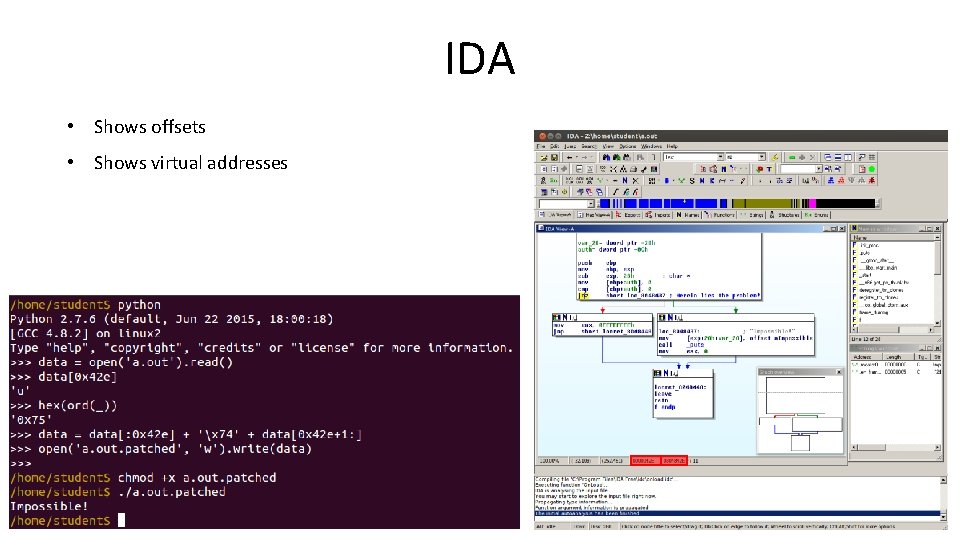
IDA • Shows offsets • Shows virtual addresses
- Slides: 9