Chapter 23 Vulnerability Analysis Dr Wayne Summers Department
Chapter 23: Vulnerability Analysis Dr. Wayne Summers Department of Computer Science Columbus State University Summers_wayne@colstate. edu http: //csc. colstate. edu/summers
Penetration Studies ¨ Test for evaluating strengths of all security controls on the computer system (tiger team attack, red team attack) ¨ Authorized attempt to violate constraints stated in security policy ¨ Layering of Tests – External attacker with no knowledge of system – External attacker with access to the system – Internal attacker with access to the system 2
Penetration Studies ¨ Flaw Hypothesis Methodology – Information Gathering – Flaw Hypothesis – Flaw Testing – Flaw Generalization – Flaw Elimination 3
Vulnerability Classification ¨ Goal of vulnerability analysis is to develop methodologies that provide – Ability to specify, design, and implement a computer system without vulnerabilities – Ability to analyze a computer system to detect vulnerabilities – Ability to address any vulnerabilities introduced during the operation of the computer system – Ability to detect attempted exploitations of vulnerabilities 4
Frameworks ¨ Research Into Secure Operating Systems (RISOS) – classified flaws – – Incomplete parameter validation (buffer overflow) Inconsistent parameter validation Implicit sharing of privileged/confidential data Asynchronous validation/inadequate serialization (race conditions/time-of-check to time-of-use) – Inadequate identification/authentication/authorization – Violable prohibition/limit (bound conditions) – Exploitable logic error 5
Frameworks ¨ Protection Analysis Model (pattern-directed protection evaluation) – Improper protection domain initialization and enforcement • • • Improper choice of initial protection domain Improper isolation of implementation detail Improper change Improper naming Improper deallocation or deletion – Improper validation – Improper sychronization • Improper indivisibility • Improper sequencing – Improper choice of operand / operation 6
Frameworks ¨ NRL Taxonomy – Flaws by genesis • Intentional – Malicious • Trojan horse • Trapdoor • Logic/time bomb – Nonmalicious • Covert channel • Other • Unintentional (RISOS taxonomy) 7
Frameworks ¨ NRL Taxonomy – Flaws by time of introduction • Development – Requirement/specification/design – Source code – Object code • Maintenance • Operation 8
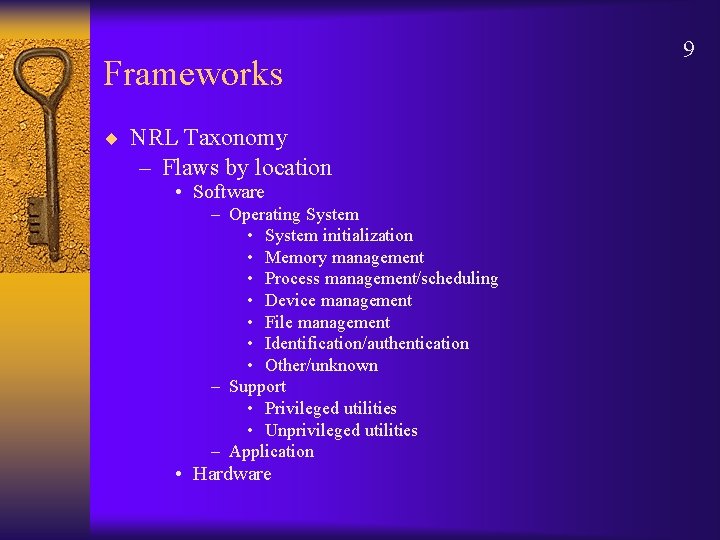
Frameworks ¨ NRL Taxonomy – Flaws by location • Software – Operating System • System initialization • Memory management • Process management/scheduling • Device management • File management • Identification/authentication • Other/unknown – Support • Privileged utilities • Unprivileged utilities – Application • Hardware 9
- Slides: 9