Behavior Based Access Control Michael J Mayhew Cross
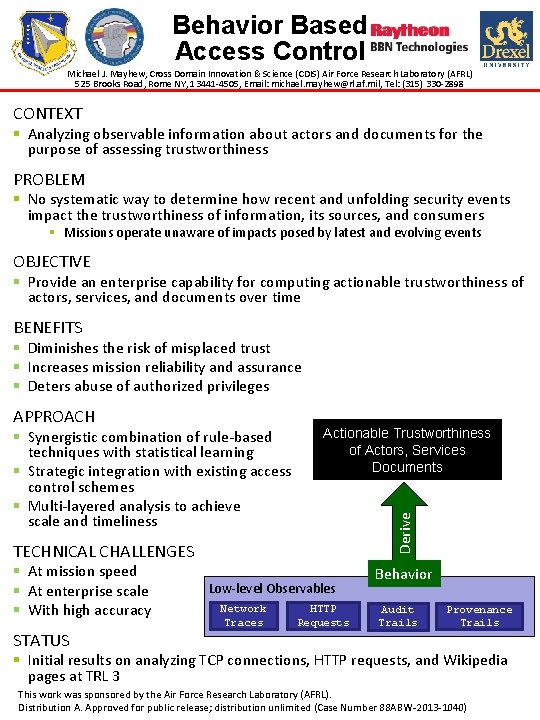
Behavior Based Access Control Michael J. Mayhew, Cross Domain Innovation & Science (CDIS) Air Force Research Laboratory (AFRL) 525 Brooks Road, Rome NY, 13441 -4505, Email: michael. mayhew@rl. af. mil, Tel: (315) 330 -2898 CONTEXT § Analyzing observable information about actors and documents for the purpose of assessing trustworthiness PROBLEM § No systematic way to determine how recent and unfolding security events impact the trustworthiness of information, its sources, and consumers § Missions operate unaware of impacts posed by latest and evolving events OBJECTIVE § Provide an enterprise capability for computing actionable trustworthiness of actors, services, and documents over time BENEFITS § Diminishes the risk of misplaced trust § Increases mission reliability and assurance § Deters abuse of authorized privileges § Synergistic combination of rule-based techniques with statistical learning § Strategic integration with existing access control schemes § Multi-layered analysis to achieve scale and timeliness Actionable Trustworthiness of Actors, Services Documents Derive APPROACH TECHNICAL CHALLENGES § At mission speed § At enterprise scale § With high accuracy STATUS Low-level Observables Network Traces HTTP Requests Behavior Audit Trails Provenance Trails § Initial results on analyzing TCP connections, HTTP requests, and Wikipedia pages at TRL 3 This work was sponsored by the Air Force Research Laboratory (AFRL). Distribution A. Approved for public release; distribution unlimited (Case Number 88 ABW-2013 -1040)
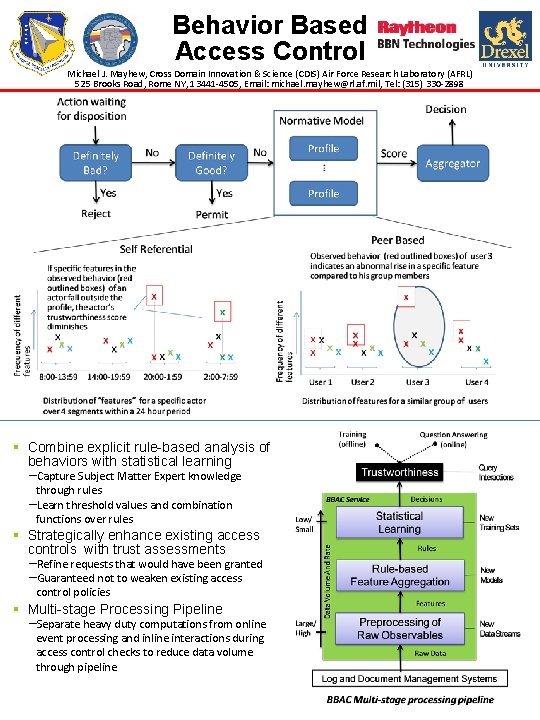
Behavior Based Access Control Michael J. Mayhew, Cross Domain Innovation & Science (CDIS) Air Force Research Laboratory (AFRL) 525 Brooks Road, Rome NY, 13441 -4505, Email: michael. mayhew@rl. af. mil, Tel: (315) 330 -2898 § Combine explicit rule-based analysis of behaviors with statistical learning −Capture Subject Matter Expert knowledge through rules −Learn threshold values and combination functions over rules § Strategically enhance existing access controls with trust assessments −Refine requests that would have been granted −Guaranteed not to weaken existing access control policies § Multi-stage Processing Pipeline −Separate heavy duty computations from online event processing and inline interactions during access control checks to reduce data volume through pipeline
- Slides: 2