Understanding and Preventing Buffer Overflow Attacks in Unix
Understanding and Preventing Buffer Overflow Attacks in Unix Alan Cox Appalachian State University April 29, 2002
Introduction What are buffer overflow attacks? How much of a threat do they pose? How do they work? What do you do to prevent them?
What are buffer overflow attacks? Provide an opportunity for a nonprivileged user to execute arbitrary code as a privileged user. Attack can be made remotely using the Internet, or locally by a user with a shell account, etc.
How much of a threat do they pose? One of the most common security vulnerability over the past ten years. Many operating systems vulnerable. It is possible for an attacker to take complete control of a host.
Background UNIX permissions UNIX processes and stack
UNIX Permissions Multi-user operating system. One user ‘root’ is super-user and can do anything. Processes usually run with privilege of the user who started it. ‘Sticky bit’ allows a program to run with privilege of user who owns executable.
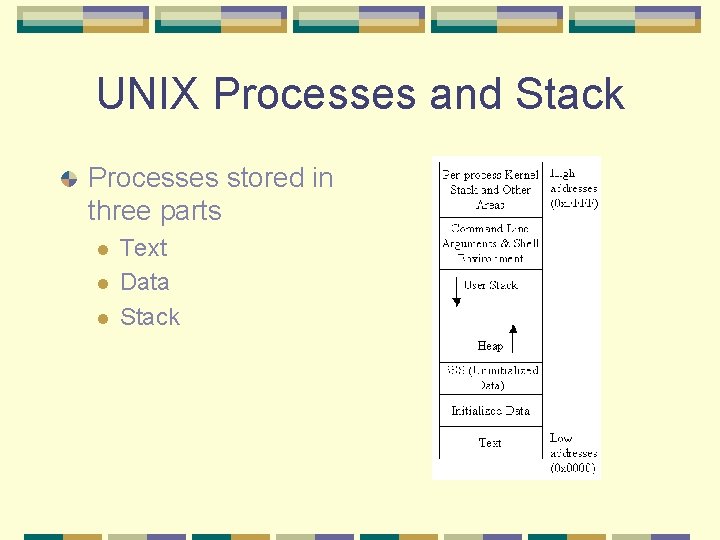
UNIX Processes and Stack Processes stored in three parts l l l Text Data Stack
Exploiting Buffer Overflows Buffer overflows are common in C/C++. This gives a segmentation fault. What happens?
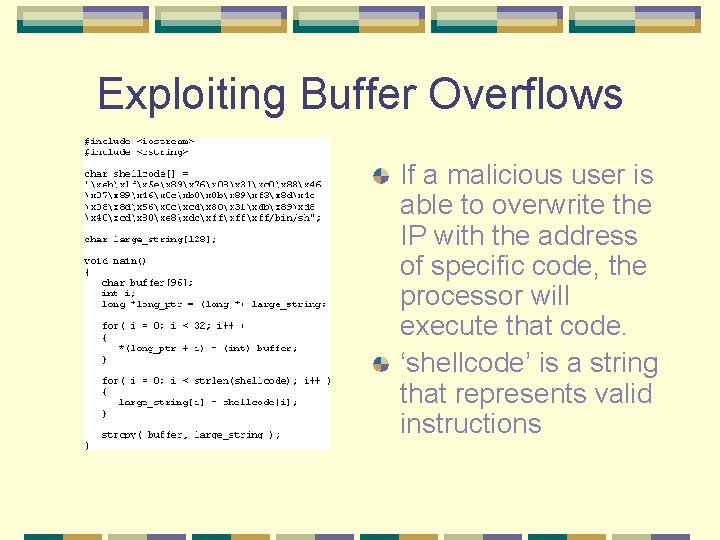
Exploiting Buffer Overflows If a malicious user is able to overwrite the IP with the address of specific code, the processor will execute that code. ‘shellcode’ is a string that represents valid instructions
Exploiting Buffer Overflows Previous example not very realistic – programmers shouldn’t put something like ‘shellcode’ in their programs. How, then, does an attacker get ‘shellcode’ into memory? Manipulating command-line arguments l Manipulating environmental variables l Interactive input l
Preventing Buffer Overflows Reduce number of programs SUID root. Writing better programs Use strncat() rather than strcat(), etc. l Check all user input l Modify compilers (i. e. Stack. Guard) Use development tools such as LCLint
- Slides: 11