Software Watermarking Deterring Software Piracy Beaux Sharifi CS
Software Watermarking Deterring Software Piracy Beaux Sharifi CS 591 Fall 2005 CS 591 Software Watermarking Beaux Sharifi
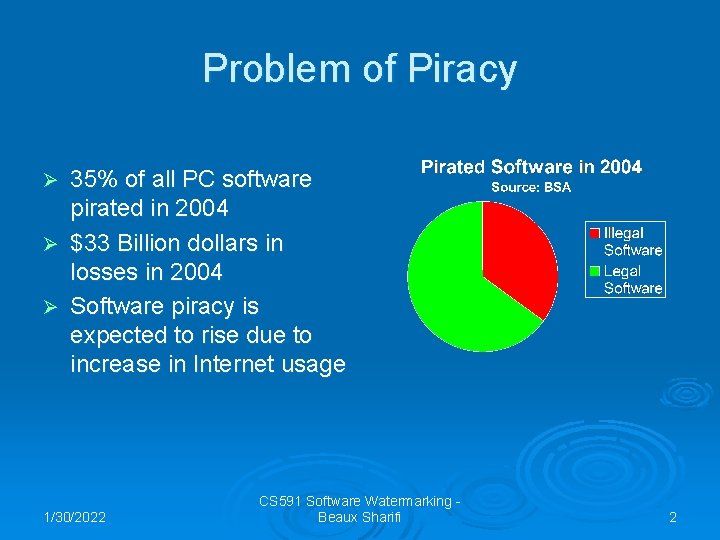
Problem of Piracy 35% of all PC software pirated in 2004 Ø $33 Billion dollars in losses in 2004 Ø Software piracy is expected to rise due to increase in Internet usage Ø 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 2
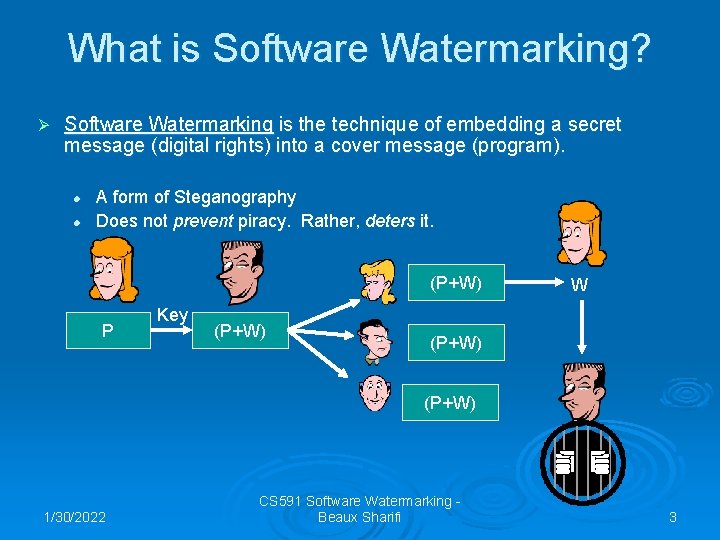
What is Software Watermarking? Ø Software Watermarking is the technique of embedding a secret message (digital rights) into a cover message (program). l l A form of Steganography Does not prevent piracy. Rather, deters it. (P+W) P Key (P+W) W (P+W) 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 3
Software Watermarking Types Ø Static Software Watermarks: l Embedded within the static structure of the program. • Static Data Watermarks • Static Code Watermarks Ø Dynamic Software Watermarks l Embedded within the execution state of the program. • Easter Eggs • Execution Trace • Dynamic Data Structure 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 4
![Example Static Watermark Static Data Watermark: char copyright[] = “Property of XYZ Corporation, 2004”; Example Static Watermark Static Data Watermark: char copyright[] = “Property of XYZ Corporation, 2004”;](http://slidetodoc.com/presentation_image_h2/97e34e299b0ded76ae9f1ae2286973ba/image-5.jpg)
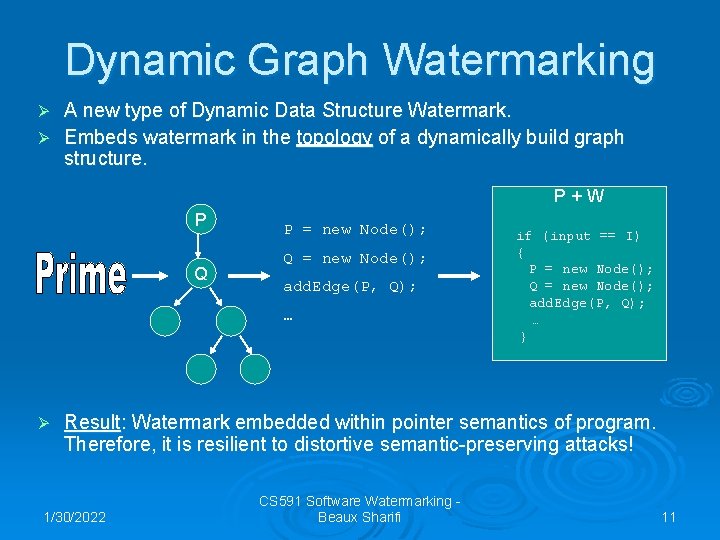
Example Static Watermark Static Data Watermark: char copyright[] = “Property of XYZ Corporation, 2004”; Can Extract using GNU Strings: $> strings program. exe | grep XYZ $> Property of XYZ Corporation, 2004 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 5
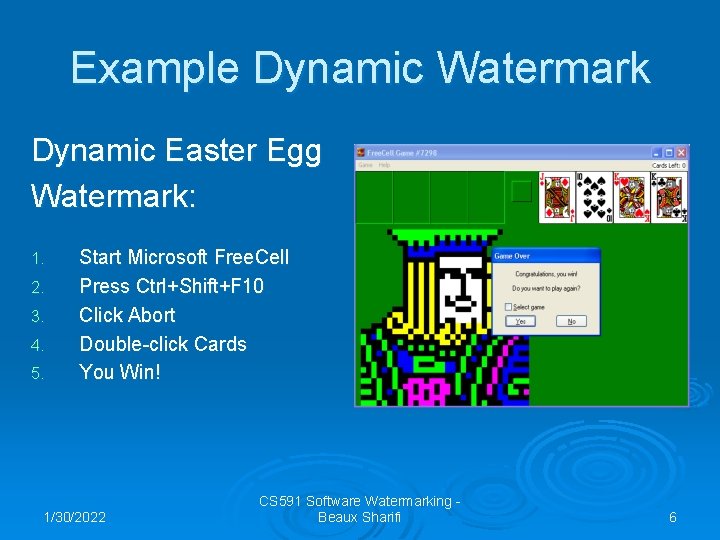
Example Dynamic Watermark Dynamic Easter Egg Watermark: 1. 2. 3. 4. 5. Start Microsoft Free. Cell Press Ctrl+Shift+F 10 Click Abort Double-click Cards You Win! 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 6
De-watermarking Attacks Ø Several types: l l l Distortive: Subtractive: Additive: Collusive: Statistical: 1/30/2022 Destroy the watermark Remove the watermark Add additional watermarks Compare the watermark Analyze the watermark CS 591 Software Watermarking Beaux Sharifi 7
![Example Attack Distortive Attack: char copyright[] = “Property of XYZ Corporation, 2004”; char a[] Example Attack Distortive Attack: char copyright[] = “Property of XYZ Corporation, 2004”; char a[]](http://slidetodoc.com/presentation_image_h2/97e34e299b0ded76ae9f1ae2286973ba/image-8.jpg)
Example Attack Distortive Attack: char copyright[] = “Property of XYZ Corporation, 2004”; char a[] = “Prop”; char b[] = “erty”; char c[] = “ of “; char d[] = “XY”; char e[] = “Z”; … char m[] = “ 04”; char copyright[MAX]; copyright = a + b + … + m; Can no longer extract using GNU Strings: $> strings program. exe | grep XYZ $> 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 8
Desirable Properties Ø Desirable Properties of Watermarks: l l l Resilient to Attacks Stealthy Efficient Have a High Data Rate Easy to Embed & Retrieve Mathematically Deliberate 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 9
Limitations of Software Watermarks Ø Problem: All traditional software watermarking techniques except easter eggs are susceptible to distortive attacks. 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 10
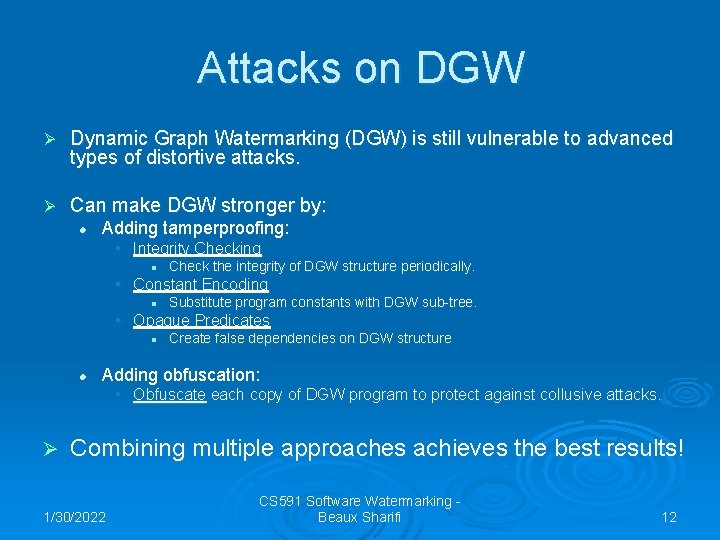
Dynamic Graph Watermarking A new type of Dynamic Data Structure Watermark. Ø Embeds watermark in the topology of a dynamically build graph structure. Ø P+W P Q P = new Node(); Q = new Node(); add. Edge(P, Q); … Ø if (input == I) { P = new Node(); Q = new Node(); add. Edge(P, Q); … } Result: Watermark embedded within pointer semantics of program. Therefore, it is resilient to distortive semantic-preserving attacks! 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 11
Attacks on DGW Ø Dynamic Graph Watermarking (DGW) is still vulnerable to advanced types of distortive attacks. Ø Can make DGW stronger by: l Adding tamperproofing: • Integrity Checking l Check the integrity of DGW structure periodically. • Constant Encoding l Substitute program constants with DGW sub-tree. • Opaque Predicates l l Create false dependencies on DGW structure Adding obfuscation: • Obfuscate each copy of DGW program to protect against collusive attacks. Ø Combining multiple approaches achieves the best results! 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 12
Future Work No software watermarking technique is immune to all types of attacks. Ø There are no known defenses against Additive Attacks. Ø 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 13
References Ø Business Software Alliance, “Sixth Annual BSA global software piracy study”, http: //www. bsa. org/globalstudy/upload/2005 -Global. Study-English. pdf, undated, (Accessed: 7 Dec, 2005) Ø C. Collberg and C. Thomborson, “Software Watermarking: Models and Dynamic Embeddings”, presented at POPL ’ 99. 26 th ACM SIGPLAN-SIGACT. Symposium on Principles of Programming Languages. ACM, New York, NY, USA, 1999. Ø Y. He, “Tamperproofing a Software Watermark by Encoding Constants”, Masters Thesis, University of Auckland, 2002. Ø J. Palsberg, S. Krishnaswamy, K. Minseok, D. Ma, S. Qiuyun, and Y. Zhang, “Experience with Software Watermarking”, presented at 16 th Annual Computer Security Applications Conference (ACSAC’ 00). IEEE Comput. Soc. , Los Alamitos, CA, USA, 2000 1/30/2022 CS 591 Software Watermarking Beaux Sharifi 14
- Slides: 14