Disposable VMs Qubes OS Adrian Mc Clure 3
Disposable VM’s & Qubes OS Adrian Mc. Clure
3 TYPES OF APPROACHES TO SECURITY BY CORRECTNESS (IDEAL) ▸ Software that is bug free and has no possible or known exploits ▸ Rare case ▸ Hard to implement since all possible flaws need to be found addressed ▸ No sure way to tell the “correctness” of code
3 TYPES OF APPROACHES TO SECURITY BY OBSCURITY (RANDOMIZATION) ▸ Flaws in code are unavoidable, so make those flaws difficult to exploit ▸ If a person doesn’t know how to exploit the system then they are considered not dangerous. ▸ Never fix the problem, and hope for the best ▸ Example ASLR (Address Space Layout Randomization)
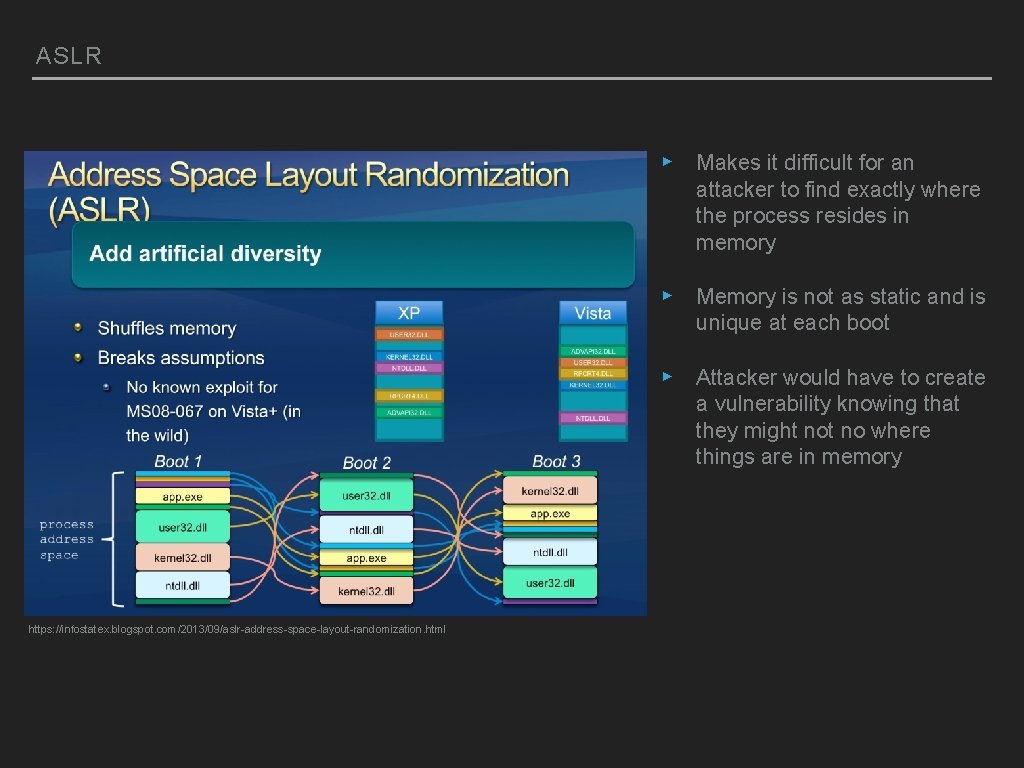
ASLR ▸ Makes it difficult for an attacker to find exactly where the process resides in memory ▸ Memory is not as static and is unique at each boot ▸ Attacker would have to create a vulnerability knowing that they might no where things are in memory https: //infostatex. blogspot. com/2013/09/aslr-address-space-layout-randomization. html
3 TYPES OF APPROACHES TO SECURITY BY ISOLATION OR COMPARTMENTALIZATION ▸ Separate a system into many pieces and make it so that these pieces only communicate necessary info with each other. ▸ If a piece becomes compromised, the entire system is not ▸ Can become inefficient if processes cant share resources and need to have their own copies of data ▸ i. e. sandboxing
DISPOSABLE VM SECURITY BY ISOLATION TO THE NEXT LEVEL ▸ Have a lightweight VM that boots in a short time with the purpose of hosting one application, i. e. text editor or media player. ▸ VM cannot store or access data that is not allowed by user. ▸ Once tasks are done the instance of this VM is disposed ▸ If the file you opened in the disposable VM was compromised, it only damages the VM ▸ Every time you run a disposable VM you are getting a clean environment
QUBES OS COMPONENTS ▸ FOSS (Free and Open-Source Software) ▸ Built around a type-1 hypervisor (Xen) ▸ Type 2 hyper visor used for more consumer friendly VM’s i. e. Virtual Box or Parallels ▸ Uses a Microkernel instead of a monolithic kernel ▸ Extremely light weight, smallest amount of libraries needed
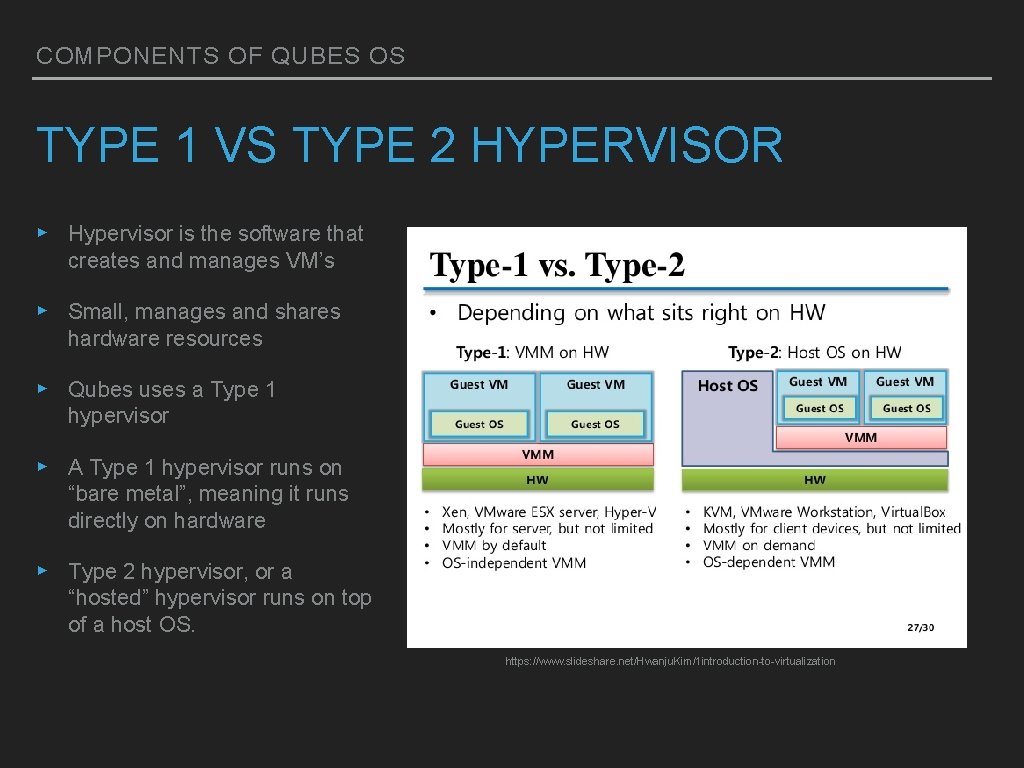
COMPONENTS OF QUBES OS TYPE 1 VS TYPE 2 HYPERVISOR ▸ Hypervisor is the software that creates and manages VM’s ▸ Small, manages and shares hardware resources ▸ Qubes uses a Type 1 hypervisor ▸ A Type 1 hypervisor runs on “bare metal”, meaning it runs directly on hardware ▸ Type 2 hypervisor, or a “hosted” hypervisor runs on top of a host OS. https: //www. slideshare. net/Hwanju. Kim/1 introduction-to-virtualization
TYPE 1 VS TYPE 2 HYPERVISOR ▸ A type 1 hypervisor like Qubes uses does not rely on an underlying OS. Better security ▸ Attacker has to exploit the hypervisor in type 1 to compromise Qubes. In type 2 Attacker can exploit host OS ▸ A type 2 hypervisor used in software such as Virtual Box can be more convenient ▸ Type 2 more efficient, resources shared more effiecently but less secure
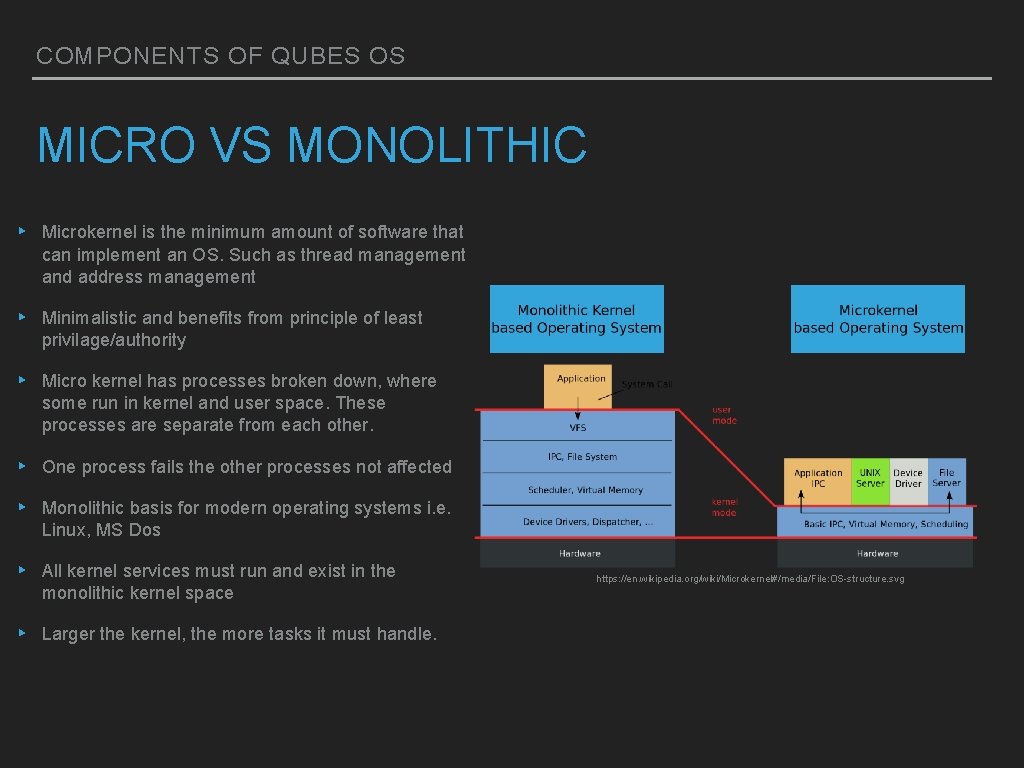
COMPONENTS OF QUBES OS MICRO VS MONOLITHIC ▸ Microkernel is the minimum amount of software that can implement an OS. Such as thread management and address management ▸ Minimalistic and benefits from principle of least privilage/authority ▸ Micro kernel has processes broken down, where some run in kernel and user space. These processes are separate from each other. ▸ One process fails the other processes not affected ▸ Monolithic basis for modern operating systems i. e. Linux, MS Dos ▸ All kernel services must run and exist in the monolithic kernel space ▸ Larger the kernel, the more tasks it must handle. https: //en. wikipedia. org/wiki/Microkernel#/media/File: OS-structure. svg
QUBES SPECIFICS USING QUBES ▸ Programs run in lightweight VM’s or “qubes” ▸ There is a template VM in which created Qubes are based on. They share a root file system with read only access ▸ Template cant be compromised since its read only and resources are saved with shared root ▸ Qubes can be organized into different domains to represent varying levels of importance and security ▸ One more privileged VM called “dom 0” only runs management software and has no internet connectivity ▸ When you are done, closing a qube will remove that VM instance
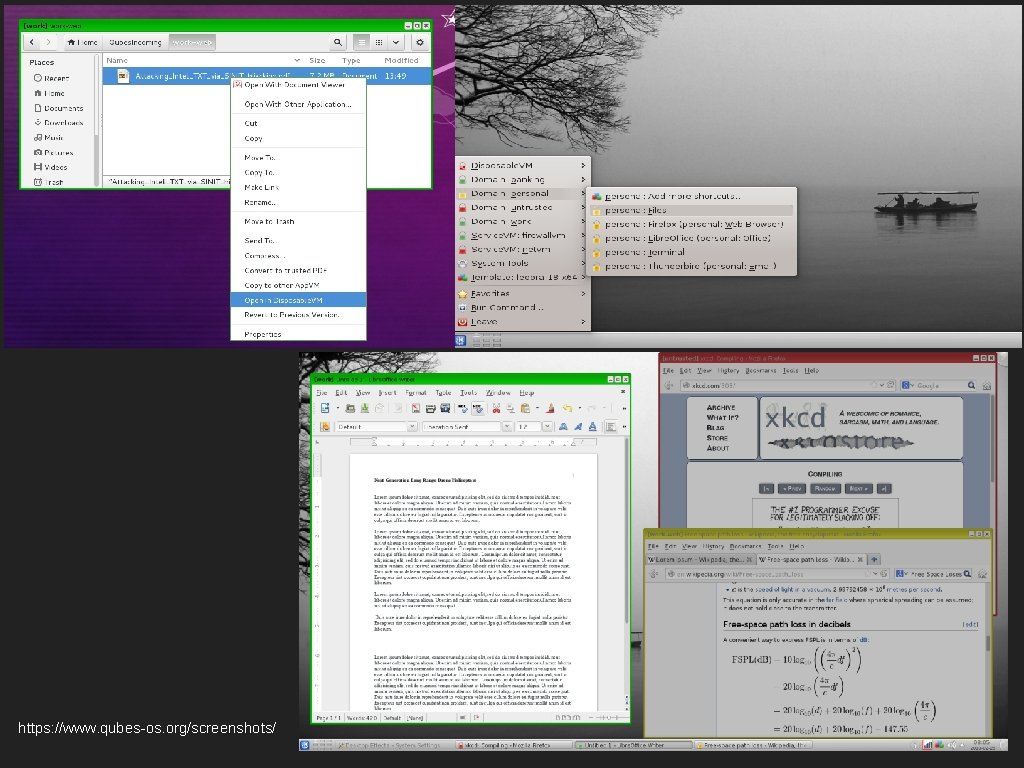
https: //www. qubes-os. org/screenshots/
BIBLIOGRAPHY ▸ https: //www. qubes-os. org ▸ https: //xenproject. org ▸ https: //infostatex. blogspot. com/2013/09/aslr-address-space-layoutrandomization. html ▸ https: //www. slideshare. net/Hwanju. Kim/1 introduction-to-virtualization ▸ https: //www. owasp. org/index. php/Security_by_Design_Principles ▸ https: //blog. invisiblethings. org/2008/09/02/three-approaches-to-computersecurity. html
- Slides: 13