Carnegie Mellon Worcester Polytechnic Institute Lab Project 2
Carnegie Mellon Worcester Polytechnic Institute Lab Project #2: Bomblab Professor Hugh C. Lauer CS-2011, Machine Organization and Assembly Language (Slides include copyright materials from Computer Systems: A Programmer’s Perspective, by Bryant and O’Hallaron, and from The C Programming Language, by Kernighan and Ritchie) CS-20113, D-Term 2013 Bomblab 1
Carnegie Mellon Worcester Polytechnic Institute Binary Bomb ¢ A binary program compiled from C ¢ Six phases ¢ Each phase expects a particular string on stdin ¢ Incorrect string causes bomb to “explode” ¢ ¢ Correct string “defuses” that phases, allows you to move on to next phase Increasing difficulty with each phase CS-20113, D-Term 2013 Bomblab 2
Carnegie Mellon Worcester Polytechnic Institute Your Bomb ¢ ¢ ¢ Bomblab server: – § http: //cs 2011 b. cs. wpi. edu: 15213 to download a new bomb § http: //cs 2011 b. cs. wpi. edu: 15213/scoreboard to view progress Each student gets a different bomb! § Similar phases § Different strings Each bomb records its own Grading: – § 10 points each for phases 1 -4 § 15 points each for phases 5 -6 progress with server! § -0. 5 point each time you explode bomb! CS-20113, D-Term 2013 Bomblab 3
Carnegie Mellon Worcester Polytechnic Institute Bomblab – D-term 2013 ¢ ¢ ¢ Must run on generic 32 -bit Linux E. g. , the virtual machine announced last week § Runs on VMware Player, VMware Fusion, or Virtual Box Unsuccessful in making it run on CCC Linux § As it did last year CS-20113, D-Term 2013 Bomblab 4
Carnegie Mellon Worcester Polytechnic Institute How to Defuse a Bomb Use the debugging tools! CS-20113, D-Term 2013 Bomblab 5
Carnegie Mellon Worcester Polytechnic Institute Tools ¢ ¢ ¢ gdb — the Gnu Debugger § Introduced in CS-2301 & CS-2303 ddd — Data Display Debugger § A GUI front-end for gdb strings — Linux/Unix “strings” utility § Prints out all ASCII strings in a file objdump — Linux/Unix “object file dump” utility § Displays lots of useful information about a binary “object” file Any other tools you can find CS-20113, D-Term 2013 Bomblab 6
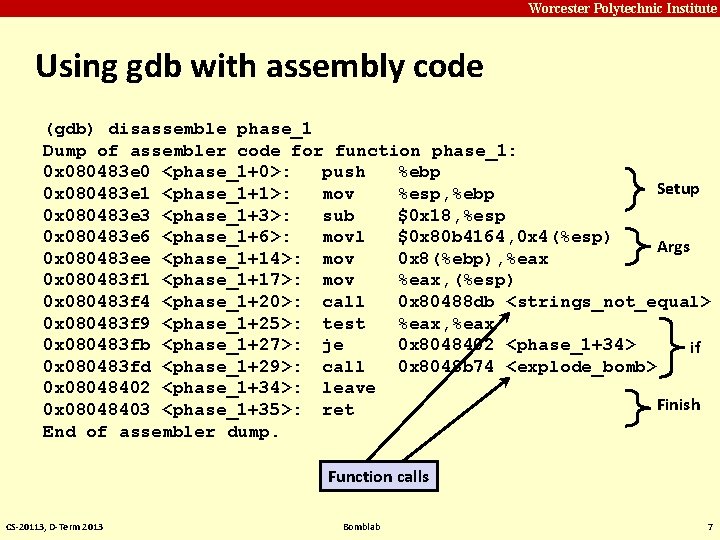
Carnegie Mellon Worcester Polytechnic Institute Using gdb with assembly code (gdb) disassemble phase_1 Dump of assembler code for function phase_1: 0 x 080483 e 0 <phase_1+0>: push %ebp Setup 0 x 080483 e 1 <phase_1+1>: mov %esp, %ebp 0 x 080483 e 3 <phase_1+3>: sub $0 x 18, %esp 0 x 080483 e 6 <phase_1+6>: movl $0 x 80 b 4164, 0 x 4(%esp) Args 0 x 080483 ee <phase_1+14>: mov 0 x 8(%ebp), %eax 0 x 080483 f 1 <phase_1+17>: mov %eax, (%esp) 0 x 080483 f 4 <phase_1+20>: call 0 x 80488 db <strings_not_equal> 0 x 080483 f 9 <phase_1+25>: test %eax, %eax 0 x 080483 fb <phase_1+27>: je 0 x 8048402 <phase_1+34> if 0 x 080483 fd <phase_1+29>: call 0 x 8048 b 74 <explode_bomb> 0 x 08048402 <phase_1+34>: leave Finish 0 x 08048403 <phase_1+35>: ret End of assembler dump. Function calls CS-20113, D-Term 2013 Bomblab 7
Carnegie Mellon Worcester Polytechnic Institute A learning exercise ¢ ¢ Study the assembly code Bryant & O’Hallaron — Chapter 3 § Reverse engineer the C code! § A little bit of each kind of C statement Setting breakpoints Single step through the assembly code § stepi — one machine instruction § nexti — same as stepi but skips over function calls § disassemble — dump out a fragment of machine code § examine — look at an area of memory (pointed to be a register) CS-20113, D-Term 2013 Bomblab 8
Carnegie Mellon Worcester Polytechnic Institute Strongly recommend ¢ ddd — The Data Display Debugger ¢ Graphic user interface ¢ ¢ Can see multiple pieces of information at the same time in separate windows § Automatically updates Already installed on Virtual Machine CS-20113, D-Term 2013 Bomblab 9
Carnegie Mellon Worcester Polytechnic Institute Questions? CS-20113, D-Term 2013 Bomblab 10
- Slides: 10