Zig Bee and 802 15 4 Copyright 2002
Zig. Bee and 802. 15. 4 Copyright 2002 The Zig. Bee Alliance, Inc.
Copyright 2002 The Zig. Bee Alliance, Inc.
IEEE 802. 15. 4 Standard Copyright 2002 The Zig. Bee Alliance, Inc.
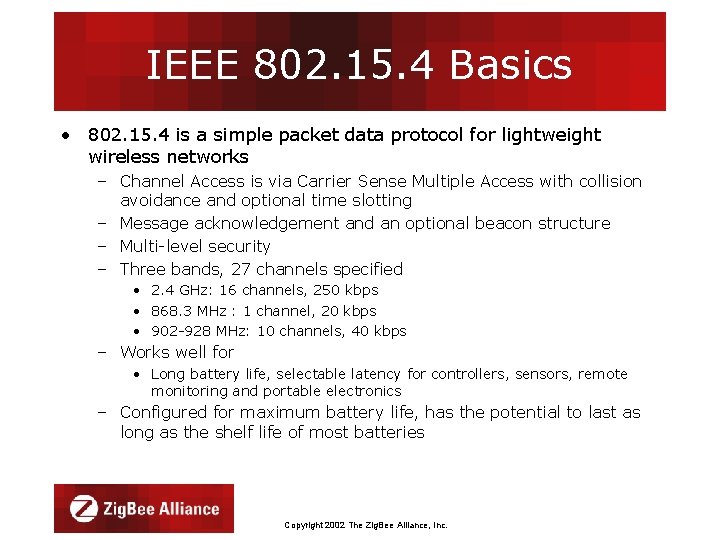
IEEE 802. 15. 4 Basics • 802. 15. 4 is a simple packet data protocol for lightweight wireless networks – Channel Access is via Carrier Sense Multiple Access with collision avoidance and optional time slotting – Message acknowledgement and an optional beacon structure – Multi-level security – Three bands, 27 channels specified • 2. 4 GHz: 16 channels, 250 kbps • 868. 3 MHz : 1 channel, 20 kbps • 902 -928 MHz: 10 channels, 40 kbps – Works well for • Long battery life, selectable latency for controllers, sensors, remote monitoring and portable electronics – Configured for maximum battery life, has the potential to last as long as the shelf life of most batteries Copyright 2002 The Zig. Bee Alliance, Inc.
Introduction to the IEEE 802. 15. 4 Standard • IEEE 802. 15. 4 standard released May 2003 – Semiconductor manufacturers • Sampling Transceiver ICs and platform hardware/software to Alpha Customers now – Users of the technology • Defining application profiles for the first products, an effort organized by the Zig. Bee Alliance Copyright 2002 The Zig. Bee Alliance, Inc.
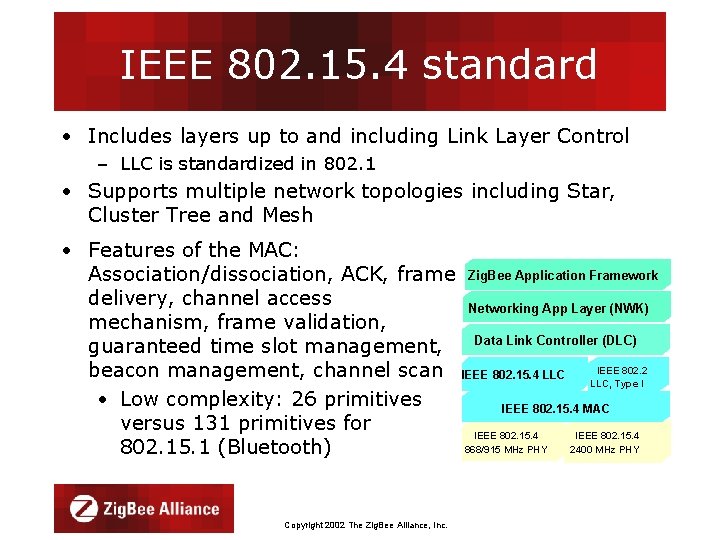
IEEE 802. 15. 4 standard • Includes layers up to and including Link Layer Control – LLC is standardized in 802. 1 • Supports multiple network topologies including Star, Cluster Tree and Mesh • Features of the MAC: Association/dissociation, ACK, frame delivery, channel access mechanism, frame validation, guaranteed time slot management, beacon management, channel scan • Low complexity: 26 primitives versus 131 primitives for 802. 15. 1 (Bluetooth) Copyright 2002 The Zig. Bee Alliance, Inc. Zig. Bee Application Framework Networking App Layer (NWK) Data Link Controller (DLC) IEEE 802. 15. 4 LLC IEEE 802. 2 LLC, Type I IEEE 802. 15. 4 MAC IEEE 802. 15. 4 868/915 MHz PHY IEEE 802. 15. 4 2400 MHz PHY
IEEE 802. 15. 4 MAC Overview • Employs 64 -bit IEEE & 16 -bit short addresses – Ultimate network size can reach 264 nodes (more than we’ll probably need…) – Using local addressing, simple networks of more than 65, 000 (2^16) nodes can be configured, with reduced address overhead • Three devices specified – Network Coordinator – Full Function Device (FFD) – Reduced Function Device (RFD) • • Simple frame structure Reliable delivery of data Association/disassociation AES-128 security CSMA-CA channel access Optional superframe structure with beacons GTS mechanism Copyright 2002 The Zig. Bee Alliance, Inc.
IEEE 802. 15. 4 Device Types • Three device types – Network Coordinator • Maintains overall network knowledge; most sophisticated of the three types; most memory and computing power – Full Function Device • Carries full 802. 15. 4 functionality and all features specified by the standard • Additional memory, computing power make it ideal for a network router function • Could also be used in network edge devices (where the network touches the real world) – Reduced Function Device • Carriers limited (as specified by the standard) functionality to control cost and complexity • General usage will be in network edge devices • All of these devices can be no more complicated than the transceiver, a simple 8 -bit MCU and a pair of AAA batteries! Copyright 2002 The Zig. Bee Alliance, Inc.
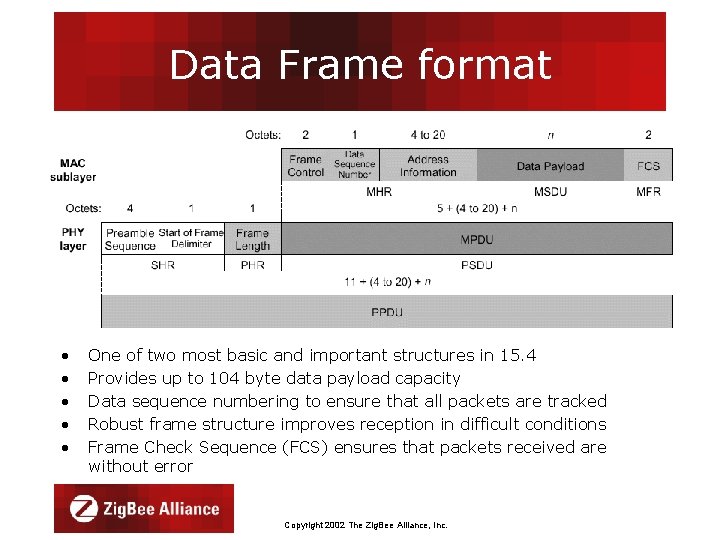
Data Frame format • • • One of two most basic and important structures in 15. 4 Provides up to 104 byte data payload capacity Data sequence numbering to ensure that all packets are tracked Robust frame structure improves reception in difficult conditions Frame Check Sequence (FCS) ensures that packets received are without error Copyright 2002 The Zig. Bee Alliance, Inc.
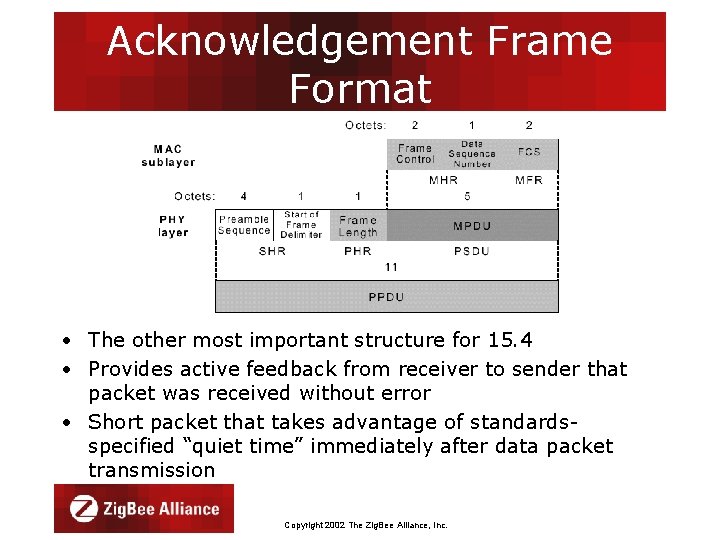
Acknowledgement Frame Format • The other most important structure for 15. 4 • Provides active feedback from receiver to sender that packet was received without error • Short packet that takes advantage of standardsspecified “quiet time” immediately after data packet transmission Copyright 2002 The Zig. Bee Alliance, Inc.
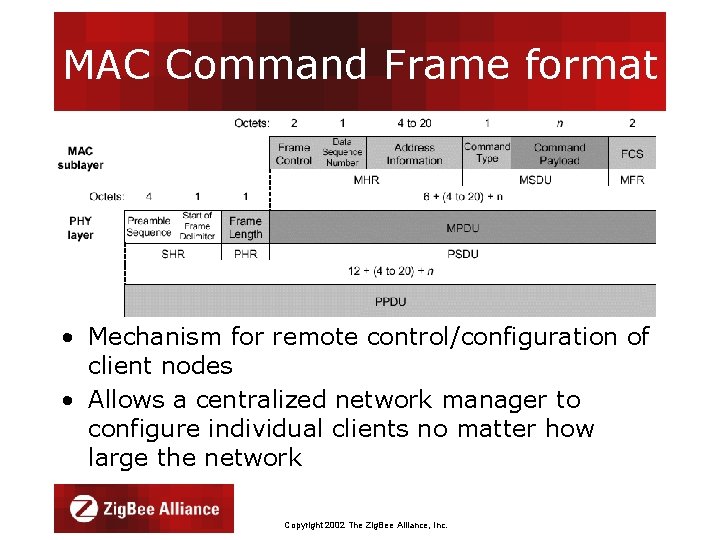
MAC Command Frame format • Mechanism for remote control/configuration of client nodes • Allows a centralized network manager to configure individual clients no matter how large the network Copyright 2002 The Zig. Bee Alliance, Inc.
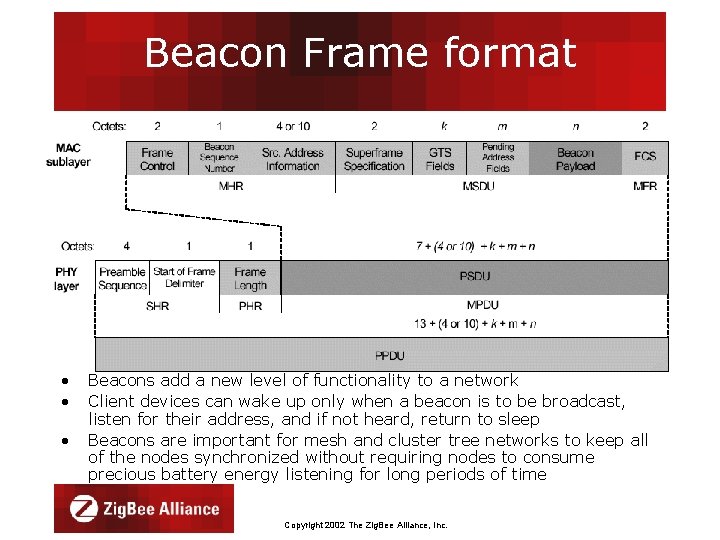
Beacon Frame format • • • Beacons add a new level of functionality to a network Client devices can wake up only when a beacon is to be broadcast, listen for their address, and if not heard, return to sleep Beacons are important for mesh and cluster tree networks to keep all of the nodes synchronized without requiring nodes to consume precious battery energy listening for long periods of time Copyright 2002 The Zig. Bee Alliance, Inc.
Copyright 2002 The Zig. Bee Alliance, Inc.

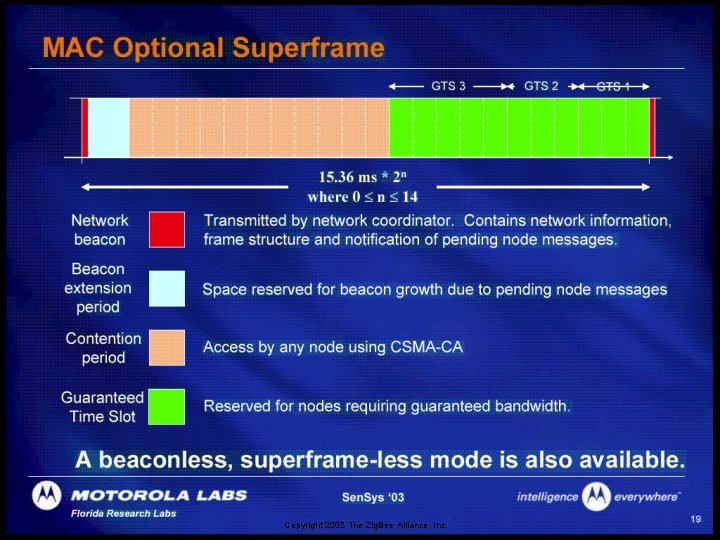
MAC Options • Two channel access mechanisms – Non-beacon network • Standard ALOHA CSMA-CA communications • Positive acknowledgement for successfully received packets – Beacon-enabled network • Superframe structure – For dedicated bandwidth and low latency – Set up by network coordinator to transmit beacons at predetermined intervals » 15 ms to 252 sec (15. 38 ms*2 n where 0 n 14) » 16 equal-width time slots between beacons » Channel access in each time slot is contention free – Three security levels specified • None • Access control lists • Symmetric key employing AES-128 Copyright 2002 The Zig. Bee Alliance, Inc.

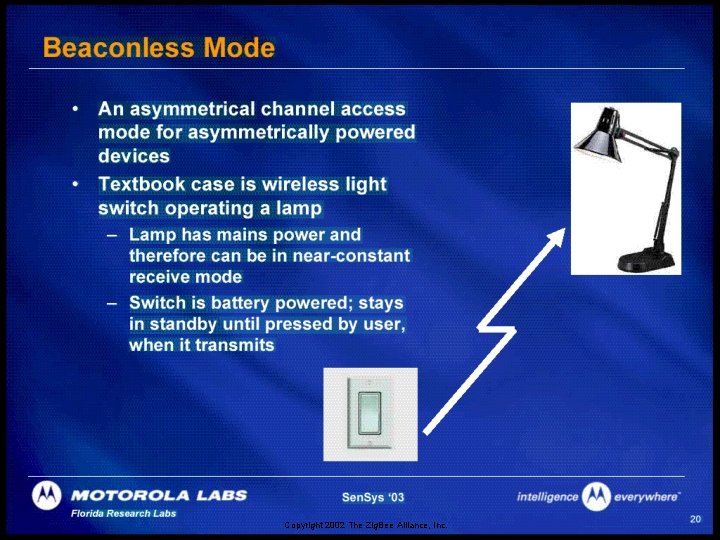
Non-Beacon vs Beacon Modes • Non-Beacon Mode – A simple, traditional multiple access system used in simple peer and near-peer networks – Think of it like a two-way radio network, where each client is autonomous and can initiate a conversation at will, but could interfere with others unintentionally – However, the recipient may not hear the call or the channel might already be in use • Beacon Mode – A very powerful mechanism for controlling power consumption in extended networks like cluster tree or mesh – Allows all clients in a local piece of the network the ability to know when to communicate with each other – Here, the two-way radio network has a central dispatcher who manages the channel and arranges the calls • As you’ll see, the primary value will be in system power consumption Copyright 2002 The Zig. Bee Alliance, Inc.
Copyright 2002 The Zig. Bee Alliance, Inc.
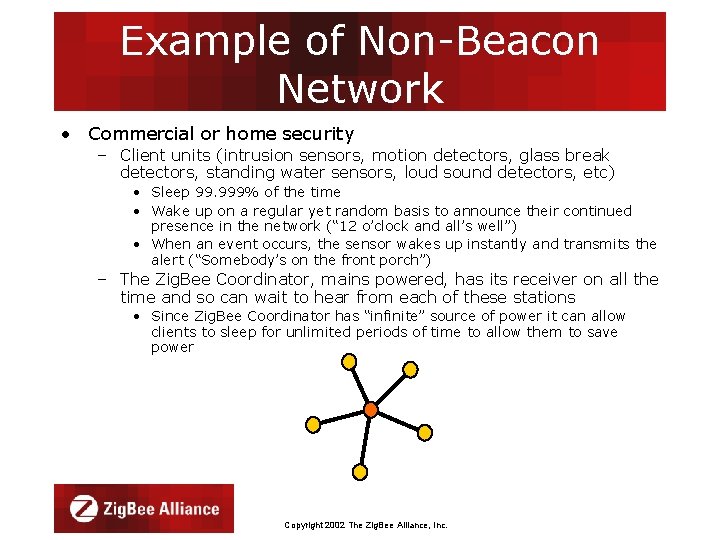
Example of Non-Beacon Network • Commercial or home security – Client units (intrusion sensors, motion detectors, glass break detectors, standing water sensors, loud sound detectors, etc) • Sleep 99. 999% of the time • Wake up on a regular yet random basis to announce their continued presence in the network (“ 12 o’clock and all’s well”) • When an event occurs, the sensor wakes up instantly and transmits the alert (“Somebody’s on the front porch”) – The Zig. Bee Coordinator, mains powered, has its receiver on all the time and so can wait to hear from each of these stations • Since Zig. Bee Coordinator has “infinite” source of power it can allow clients to sleep for unlimited periods of time to allow them to save power Copyright 2002 The Zig. Bee Alliance, Inc.
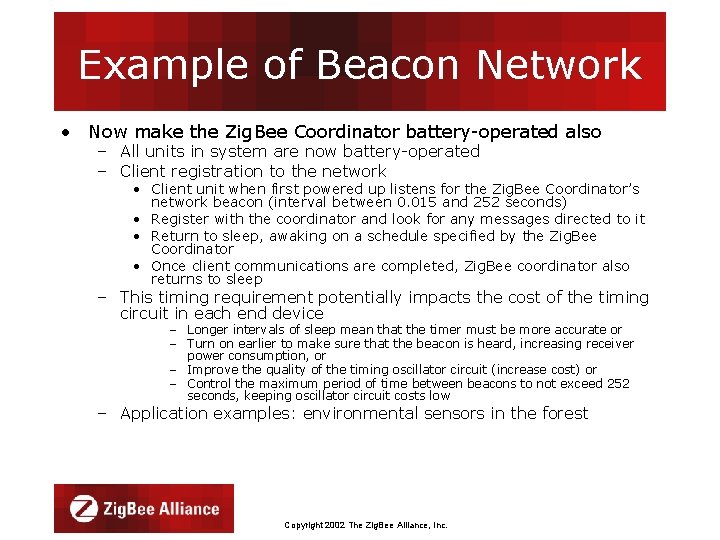
Example of Beacon Network • Now make the Zig. Bee Coordinator battery-operated also – All units in system are now battery-operated – Client registration to the network • Client unit when first powered up listens for the Zig. Bee Coordinator’s network beacon (interval between 0. 015 and 252 seconds) • Register with the coordinator and look for any messages directed to it • Return to sleep, awaking on a schedule specified by the Zig. Bee Coordinator • Once client communications are completed, Zig. Bee coordinator also returns to sleep – This timing requirement potentially impacts the cost of the timing circuit in each end device – Longer intervals of sleep mean that the timer must be more accurate or – Turn on earlier to make sure that the beacon is heard, increasing receiver power consumption, or – Improve the quality of the timing oscillator circuit (increase cost) or – Control the maximum period of time between beacons to not exceed 252 seconds, keeping oscillator circuit costs low – Application examples: environmental sensors in the forest Copyright 2002 The Zig. Bee Alliance, Inc.
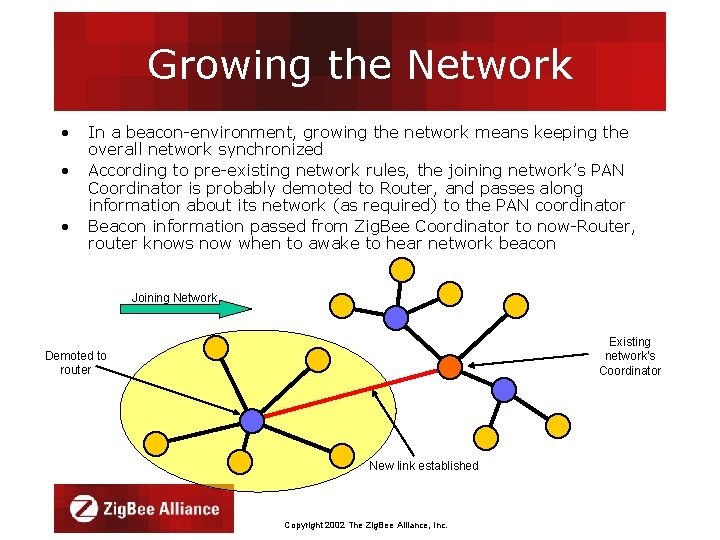
Growing the Network • • • In a beacon-environment, growing the network means keeping the overall network synchronized According to pre-existing network rules, the joining network’s PAN Coordinator is probably demoted to Router, and passes along information about its network (as required) to the PAN coordinator Beacon information passed from Zig. Bee Coordinator to now-Router, router knows now when to awake to hear network beacon Joining Network Existing network’s Coordinator Demoted to router New link established Copyright 2002 The Zig. Bee Alliance, Inc.
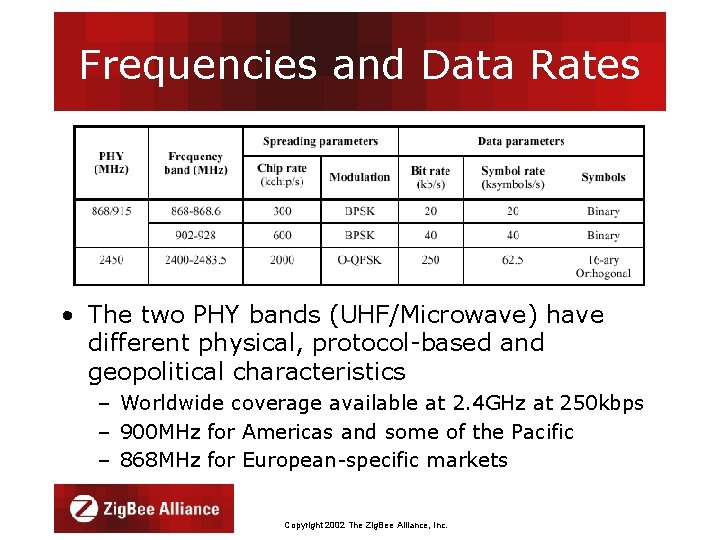
Frequencies and Data Rates • The two PHY bands (UHF/Microwave) have different physical, protocol-based and geopolitical characteristics – Worldwide coverage available at 2. 4 GHz at 250 kbps – 900 MHz for Americas and some of the Pacific – 868 MHz for European-specific markets Copyright 2002 The Zig. Bee Alliance, Inc.

ISM Band Interference and Coexistence • Potential for interference exists in every ISM band, not just 2. 4 GHz • IEEE 802. 11 and 802. 15. 2 committees are addressing coexistence issues • Zig. Bee/802. 15. 4 Protocol is very robust – Clear channel checking before transmission – Backoff and retry if no acknowledgement received – Duty cycle of a Zig. Bee-compliant device is usually extremely low – It’s the “cockroach that survives the nuclear war” • Waits for an opening in otherwise busy RF spectrum • Waits for acknowledgements to verify packet reception at other end Copyright 2002 The Zig. Bee Alliance, Inc.
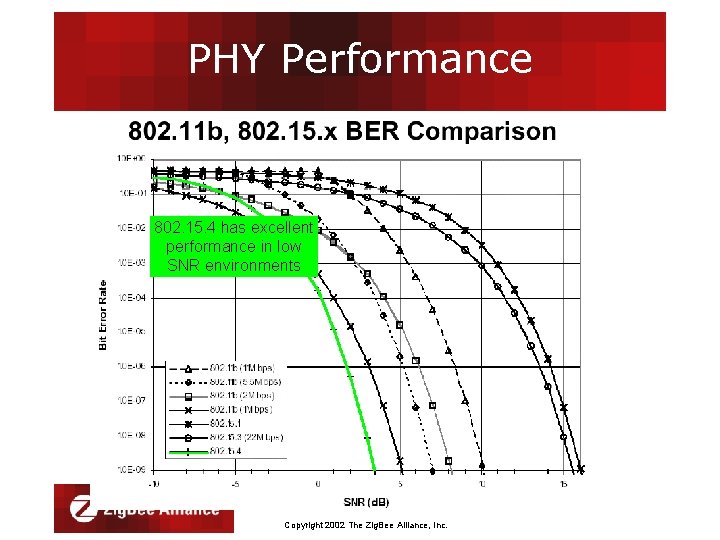
PHY Performance 802. 15. 4 has excellent performance in low SNR environments Copyright 2002 The Zig. Bee Alliance, Inc.
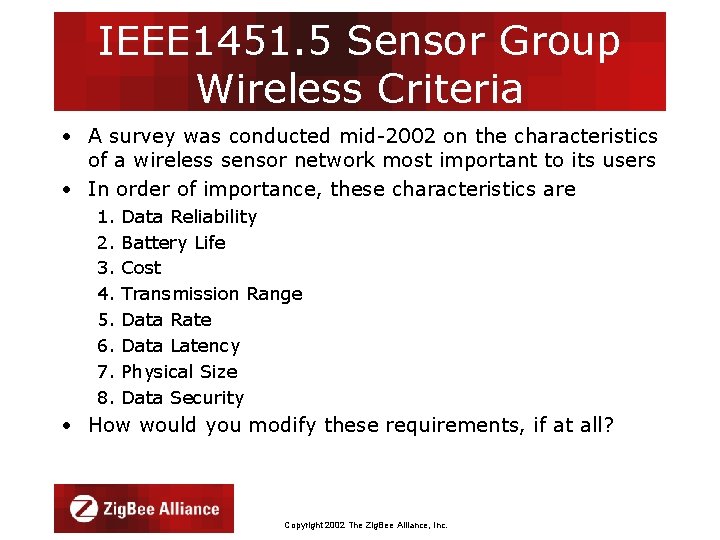
IEEE 1451. 5 Sensor Group Wireless Criteria • A survey was conducted mid-2002 on the characteristics of a wireless sensor network most important to its users • In order of importance, these characteristics are 1. 2. 3. 4. 5. 6. 7. 8. Data Reliability Battery Life Cost Transmission Range Data Rate Data Latency Physical Size Data Security • How would you modify these requirements, if at all? Copyright 2002 The Zig. Bee Alliance, Inc.
802. 15. 4 and the • IEEE 802. 15. 4 – Composed of many of the individuals and companies that make up the Zig. Bee Alliance – Developed the basic PHY and MAC standard with the requirement that 15. 4 be simple and manageable and that high-level functionality (networking, security key management, applications) be considered • The Zig. Bee Alliance is – A consortium of end users and solution providers, primarily responsible for the development of the 802. 15. 4 standard – Developing applications and network capability utilizing the 802. 15. 4 packet delivery mechanism – Addresses application and interoperability needs of a substantial part of the market Copyright 2002 The Zig. Bee Alliance, Inc.

Mission Statement Zig. Bee Alliance members are defining global standards for reliable, costeffective, low power wireless applications. The Zig. Bee Alliance is a rapidly growing, non-profit industry consortium of leading semiconductor manufacturers, technology providers, OEMs and end users worldwide. Copyright 2002 The Zig. Bee Alliance, Inc.
What is the Zig. Bee Alliance? • Organization defining global standards for reliable, cost-effective, low power wireless applications • A rapidly growing, worldwide, non-profit industry consortium of – – Leading semiconductor manufacturers Technology providers OEMs End-users • Sensors are one of the reasons for Zig. Bee! Copyright 2002 The Zig. Bee Alliance, Inc.
What is Zig. Bee technology? • Cost-effective, standards-based wireless networking solution • Developed for and targets applications that need – – Low to moderate data rates and low duty cycles Low average power consumption / long battery life Security and reliability Flexible and dynamic network topologies • Star, cluster tree and mesh networks – Interoperable application frameworks controlled by an industry alliance to ensure interoperability/compatibility Copyright 2002 The Zig. Bee Alliance, Inc.
The Zig. Bee Alliance Solution • Targeted at – – – Industrial and Commercial control/monitoring systems Wireless sensor systems Home and Building automation and controls Medical monitoring Consumer electronics PC peripherals • Industry standard through application profiles • Primary drivers – – – Simplicity Long battery life Networking capabilities Reliability Low cost • Alliance member companies provide interoperability and certification testing Copyright 2002 The Zig. Bee Alliance, Inc.
Why do we need Zig. Bee technology? • ONLY standards-based technology that – Addresses the unique needs of most remote monitoring and control and sensory network applications – Enables the broad-based deployment of wireless networks with low cost, low power solutions – Provides the ability to run for years on inexpensive primary batteries for a typical monitoring application Copyright 2002 The Zig. Bee Alliance, Inc.
What kind of battery life can a user expect? • Zig. Bee protocol was designed from the ground up to support – very long life battery applications • Users can expect – Near-shelf life in a typical monitoring application • Battery life is ultimately a function of – battery capacity and application usage • Many industrial applications are in harsh thermal environments – Batteries may include alkalines or Li-primaries – Other forms of power generation might include solar, mechanical, piezoelectric Copyright 2002 The Zig. Bee Alliance, Inc.
The Zig. Bee Alliance Solution • Targeted at home and building automation and controls, consumer electronics, toys etc. • Industry standard (IEEE 802. 15. 4 radios) • Primary drivers are simplicity, long battery life, networking capabilities, reliability, and cost Copyright 2002 The Zig. Bee Alliance, Inc.
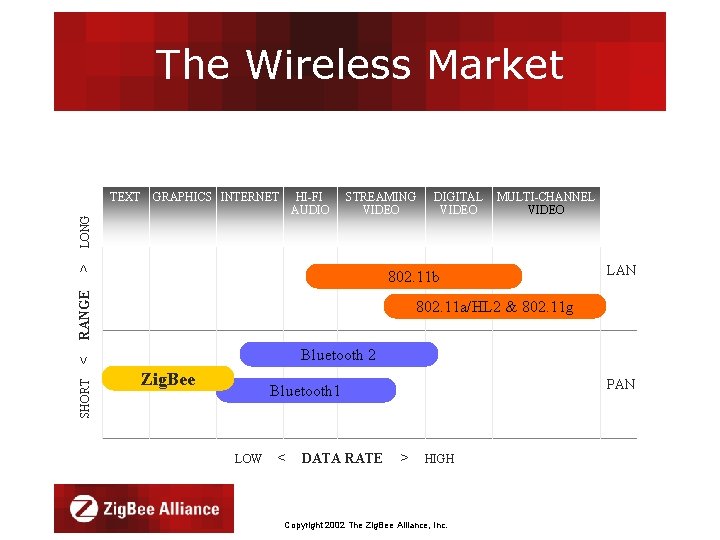
The Wireless Market GRAPHICS INTERNET HI-FI AUDIO STREAMING VIDEO > LONG TEXT MULTI-CHANNEL VIDEO RANGE 802. 11 b LAN 802. 11 a/HL 2 & 802. 11 g Bluetooth 2 < SHORT DIGITAL VIDEO Zig. Bee PAN Bluetooth 1 LOW < DATA RATE > HIGH Copyright 2002 The Zig. Bee Alliance, Inc.
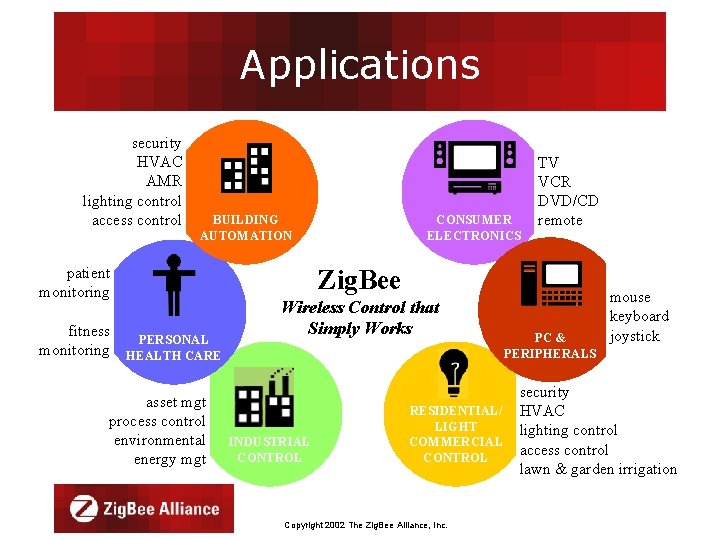
Applications security HVAC AMR lighting control access control BUILDING AUTOMATION patient monitoring fitness PERSONAL monitoring HEALTH CARE asset mgt process control environmental energy mgt CONSUMER ELECTRONICS TV VCR DVD/CD remote Zig. Bee Wireless Control that Simply Works INDUSTRIAL CONTROL RESIDENTIAL/ LIGHT COMMERCIAL CONTROL Copyright 2002 The Zig. Bee Alliance, Inc. PC & PERIPHERALS mouse keyboard joystick security HVAC lighting control access control lawn & garden irrigation

Promoter Companies Copyright 2002 The Zig. Bee Alliance, Inc.
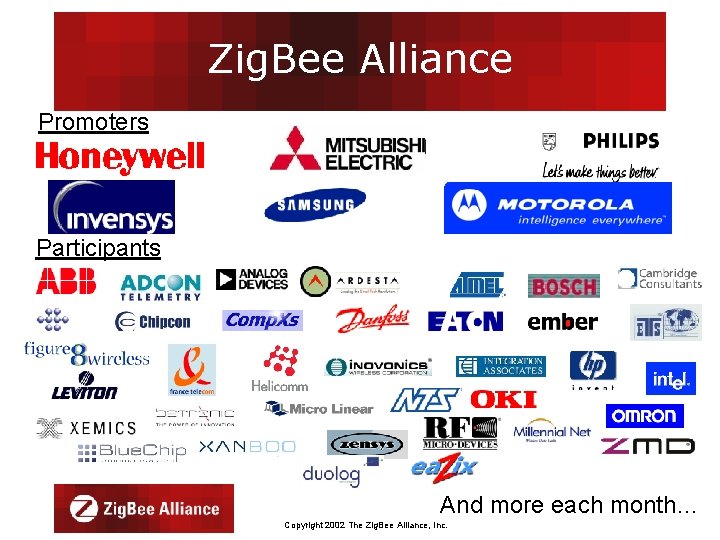
Zig. Bee Alliance Promoters Participants And more each month… Copyright 2002 The Zig. Bee Alliance, Inc.
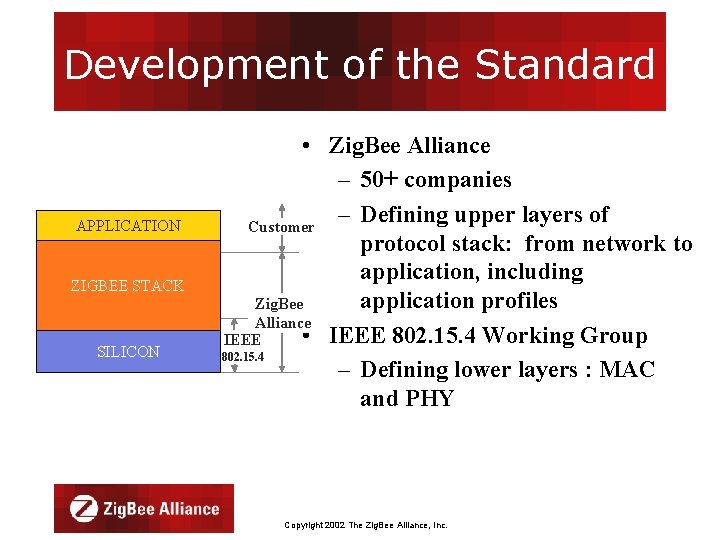
Development of the Standard APPLICATION ZIGBEE STACK SILICON • Zig. Bee Alliance – 50+ companies – Defining upper layers of Customer protocol stack: from network to application, including application profiles Zig. Bee Alliance • IEEE 802. 15. 4 Working Group IEEE 802. 15. 4 – Defining lower layers : MAC and PHY Copyright 2002 The Zig. Bee Alliance, Inc.
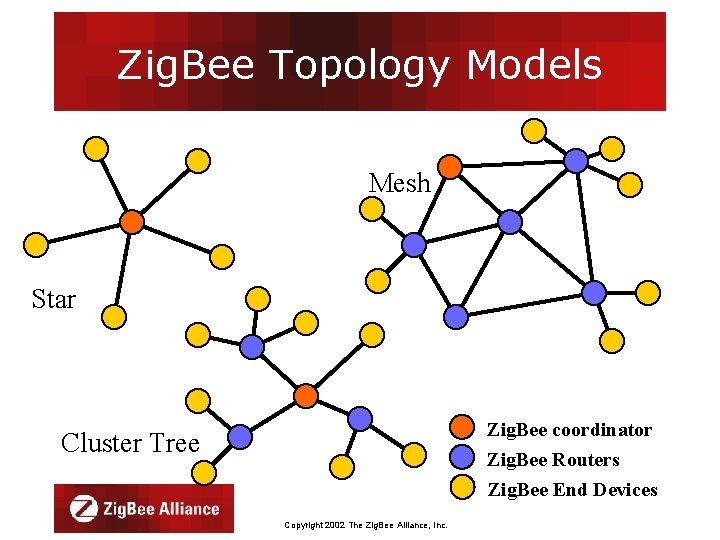
Zig. Bee Topology Models Mesh Star Zig. Bee coordinator Zig. Bee Routers Zig. Bee End Devices Cluster Tree Copyright 2002 The Zig. Bee Alliance, Inc.
Zig. Bee and Bluetooth Competitive or Complementary? Copyright 2002 The Zig. Bee Alliance, Inc.

Zig. Bee and Bluetooth Optimized for different applications • Bluetooth • Zig. Bee – Larger packets over small – Smaller packets over network large network – Ad-hoc networks – Mostly Static networks with many, – File transfer; streaming infrequently used – Screen graphics, pictures, devices hands-free audio, Mobile – Home automation, phones, headsets, PDAs, toys remote controls etc. – Energy saver!!! Copyright 2002 The Zig. Bee Alliance, Inc.
Zig. Bee and Bluetooth Address Different Needs • Bluetooth is a cable replacement for items like Phones, Laptop Computers, Headsets • Bluetooth expects regular charging – Target is to use <10% of host power Copyright 2002 The Zig. Bee Alliance, Inc.
Zig. Bee and Bluetooth Address Different Needs • Zig. Bee is better for devices where the battery is ‘rarely’ replaced – Targets are : • Tiny fraction of host power • New opportunities where wireless not yet used Copyright 2002 The Zig. Bee Alliance, Inc.
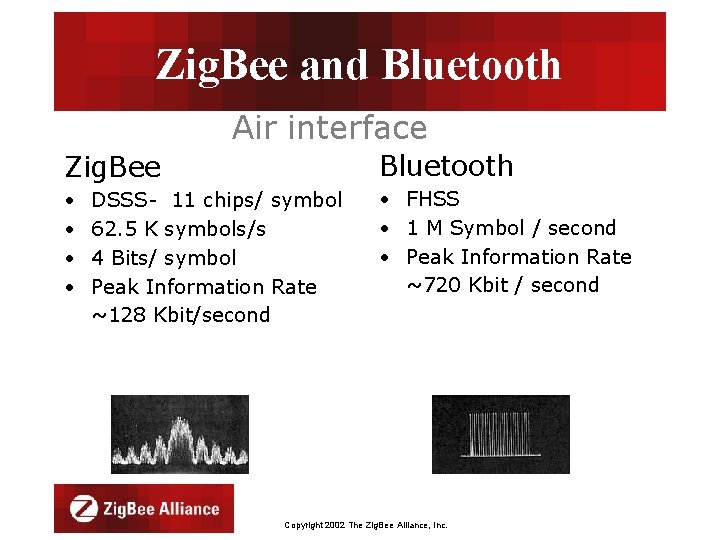
Zig. Bee and Bluetooth Air interface Zig. Bee Bluetooth • • • FHSS • 1 M Symbol / second • Peak Information Rate ~720 Kbit / second DSSS- 11 chips/ symbol 62. 5 K symbols/s 4 Bits/ symbol Peak Information Rate ~128 Kbit/second Copyright 2002 The Zig. Bee Alliance, Inc.

Zig. Bee and Bluetooth Voice Application Interface Network Layer Service Discovery Protocol (Serial Port) L 2 CAP Host Control Interface Link Manager MAC Layer Link Controller Baseband RF PHY Layer Zig. Bee Stack Fax Telephony OBEX Control RFCOMM Protocol Data Link Layer Silicon Dial-up Networking Application v. Message Intercom Headset Cordless Group Call v. Card v. Cal v. Note User Interface Application Silicon Zigbee Bluetooth Stack Applications Bluetooth Protocol Stack Comparison Copyright 2002 The Zig. Bee Alliance, Inc.
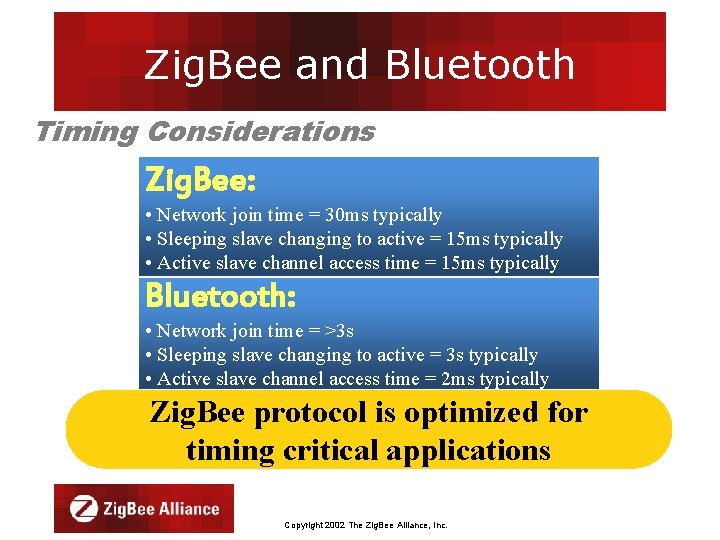
Zig. Bee and Bluetooth Timing Considerations Zig. Bee: • Network join time = 30 ms typically • Sleeping slave changing to active = 15 ms typically • Active slave channel access time = 15 ms typically Bluetooth: • Network join time = >3 s • Sleeping slave changing to active = 3 s typically • Active slave channel access time = 2 ms typically Zig. Bee protocol is optimized for timing critical applications Copyright 2002 The Zig. Bee Alliance, Inc.
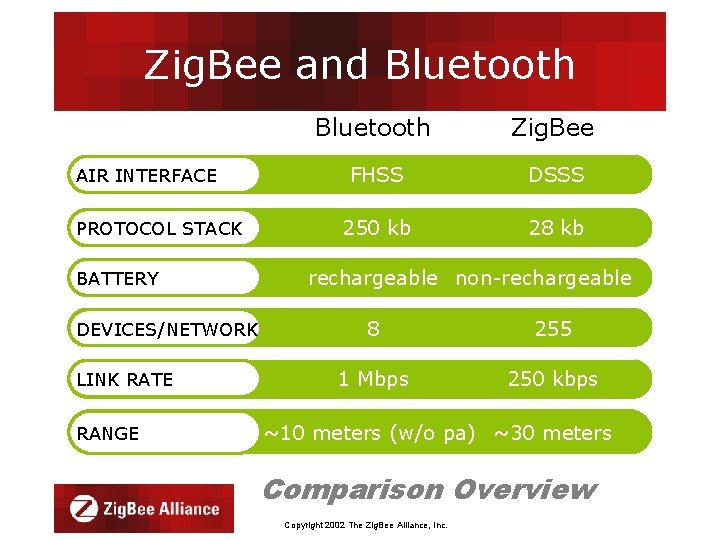
Zig. Bee and Bluetooth AIR INTERFACE PROTOCOL STACK BATTERY DEVICES/NETWORK LINK RATE RANGE Bluetooth Zig. Bee FHSS DSSS 250 kb 28 kb rechargeable non-rechargeable 8 255 1 Mbps 250 kbps ~10 meters (w/o pa) ~30 meters Comparison Overview Copyright 2002 The Zig. Bee Alliance, Inc.
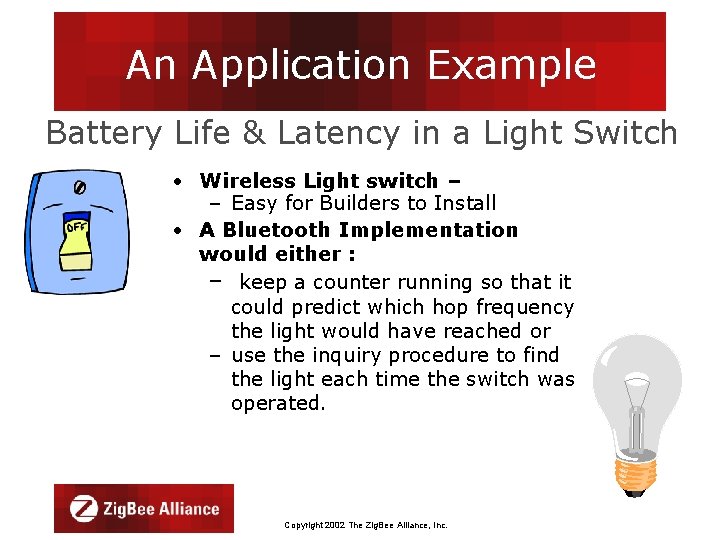
An Application Example Battery Life & Latency in a Light Switch • Wireless Light switch – – Easy for Builders to Install • A Bluetooth Implementation would either : – keep a counter running so that it could predict which hop frequency the light would have reached or – use the inquiry procedure to find the light each time the switch was operated. Copyright 2002 The Zig. Bee Alliance, Inc.
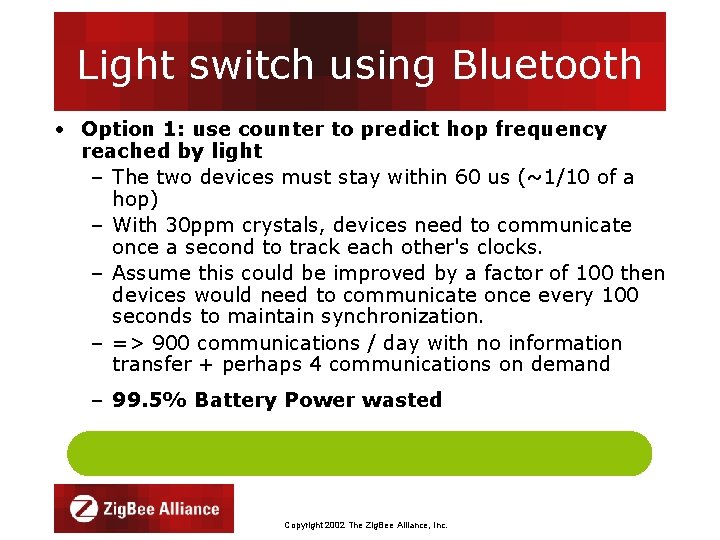
Light switch using Bluetooth • Option 1: use counter to predict hop frequency reached by light – The two devices must stay within 60 us (~1/10 of a hop) – With 30 ppm crystals, devices need to communicate once a second to track each other's clocks. – Assume this could be improved by a factor of 100 then devices would need to communicate once every 100 seconds to maintain synchronization. – => 900 communications / day with no information transfer + perhaps 4 communications on demand – 99. 5% Battery Power wasted Copyright 2002 The Zig. Bee Alliance, Inc.
Light switch using Bluetooth • Option 2: Inquiry procedure to locate light each time switch is operated – Bluetooth 1. 1 = up to 10 seconds typical – Bluetooth 1. 2 = several seconds even if optimized – Unacceptable latency Copyright 2002 The Zig. Bee Alliance, Inc.
Light switch using Zig. Bee • With DSSS interface, only need to perform CSMA before transmitting – Only 200 µs of latency – Highly efficient use of battery power Zig. Bee offers longer battery life and lower latency than a Bluetooth equivalent. Copyright 2002 The Zig. Bee Alliance, Inc.
Conclusion • Bluetooth and 802. 15. 4 transceiver physical characteristics are very similar • Protocols are substantially different and designed for different purposes • 802. 15. 4 designed for low to very low duty cycle static and dynamic environments with many active nodes • Bluetooth designed for high Qo. S, variety of duty cycles, moderate data rates in fairly static simple networks with limited active nodes Copyright 2002 The Zig. Bee Alliance, Inc.
Zig. Bee and Bluetooth Conclusion • Zig. Bee targets applications not addressable by Bluetooth or any other wireless standard • Zig. Bee and Bluetooth complement for a broader solution Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability and Robustness throughout the stacks of IEEE 802. 15. 4 and Zig. Bee Copyright 2002 The Zig. Bee Alliance, Inc.

Reliability • Consistently perform a given task to the desired result despite all changes of environmental behavior • Without fail • A necessary ingredient of trust • “When the sensor measures its environment; the controller always knows that same value” Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability • The wireless medium is not a protected environment like the wired medium, but rather, it is fraught with degradations, disruptions, and pitfalls such as dispersion, multipath, interference, frequency dependent fading, sleeping nodes, hidden nodes, and security issues. Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability • Each of these degradations and disruptions can be mitigated by various mechanisms within the ISO layers; but not all mechanisms are compatible with all other mechanisms or may negatively impact critical performance attributes • The system must be optimized for the best performance in a realistic environment Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability • In addition to the previous disruptions there is the case of sending messages to devices that are not receiving, e. g. they’re in the “sleep” mode. When this happens the message needs to be buffered by another device that is able to send the message when the sleeping device wakes up. Copyright 2002 The Zig. Bee Alliance, Inc.

Reliability Interferer Router Multipath XX Sleeping Node Network Coordinator Hidden Node Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability • IEEE 802. 15. 4 has built upon the successes of previous IEEE 802 standards by selecting those mechanisms proven to ensure good reliability without seriously degrading system and device performance. Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability ISO Layers: • PHY: Direct Sequence with Frequency Agility (DS/FA) • MAC: ARQ, Coordinator buffering • Network: Mesh Network (redundant routing) • Application Support Layer: Security Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability PHY Layers: • Direct sequence: allows the radio to reject multipath and interference by use of a special “chip” sequence. The more chips per symbol, the higher its ability to reject multipath and interference. • Frequency Agility: ability to change frequencies to avoid interference from a known interferer or other signal source. Copyright 2002 The Zig. Bee Alliance, Inc.
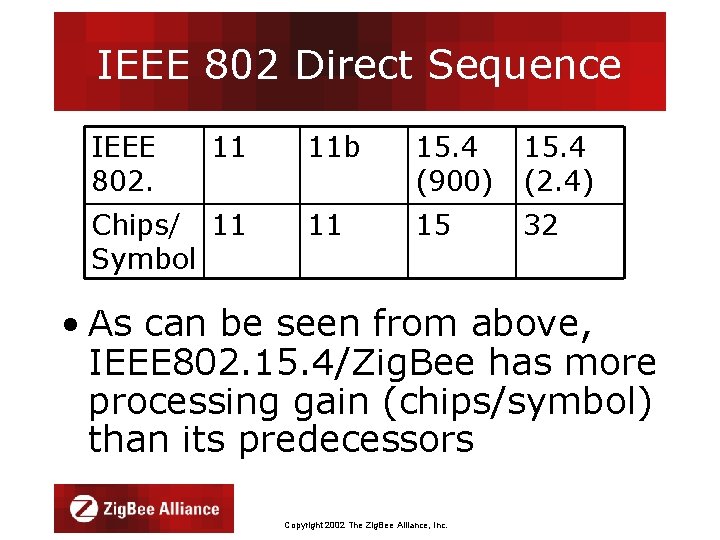
IEEE 802 Direct Sequence IEEE 802. 11 Chips/ 11 Symbol 11 b 15. 4 (900) 15. 4 (2. 4) 11 15 32 • As can be seen from above, IEEE 802. 15. 4/Zig. Bee has more processing gain (chips/symbol) than its predecessors Copyright 2002 The Zig. Bee Alliance, Inc.
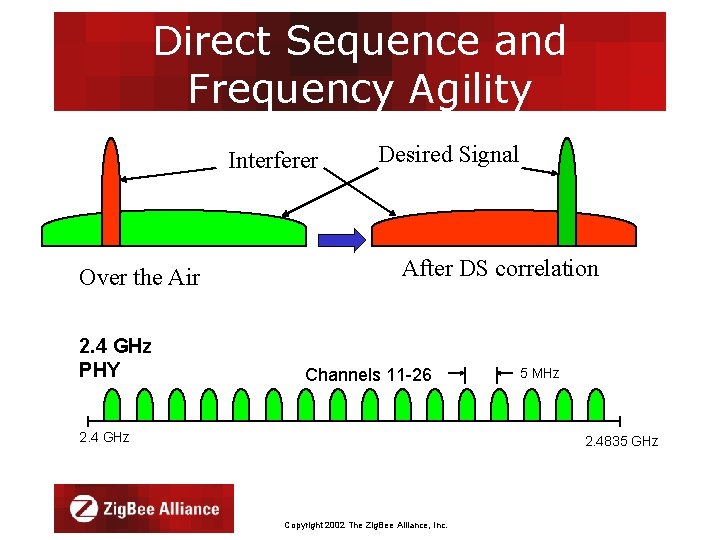
Direct Sequence and Frequency Agility Interferer Over the Air 2. 4 GHz PHY Desired Signal After DS correlation Channels 11 -26 2. 4 GHz 5 MHz 2. 4835 GHz Copyright 2002 The Zig. Bee Alliance, Inc.

Reliability MAC: • ARQ (acknowledgement request) is where a successful transmission is verified by replying with an acknowledge (ACK). If the ACK is not received the transmission is sent again • Coordinator buffering is where the network coordinator buffers messages for sleeping nodes until they wake again Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability Network: • Mesh Networking: allows various paths of routing data to the destination device. In this way if a device in the primary route is not able to pass the data, a different valid route is formed, transparent to the user. Copyright 2002 The Zig. Bee Alliance, Inc.
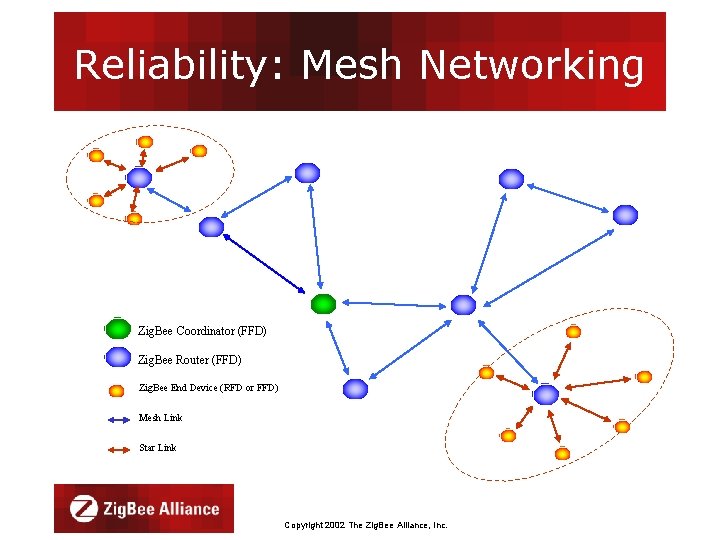
Reliability: Mesh Networking Zig. Bee Coordinator (FFD) Zig. Bee Router (FFD) Zig. Bee End Device (RFD or FFD) Mesh Link Star Link Copyright 2002 The Zig. Bee Alliance, Inc.
Reliability Application Support Sub-layer(APS): • Security: supports reliability by keeping other devices from corrupting communications. • The APS configures the security emplaced in the MAC layer and also adds some of its own. Copyright 2002 The Zig. Bee Alliance, Inc.
Robustness • Let’s define robustness as the ability to tolerate significant degrading phenomena in the physical medium • Multipath and interference are probably the most significant degradations to the channel model. Copyright 2002 The Zig. Bee Alliance, Inc.
Robustness • Frequency hopping is a method that allows the radio to periodically change channels to over time minimize the effect of a “bad” channel. While this technique is very effective in some circumstances it creates other problems such as latency, network uncertainty for sleeping nodes, loss of the product bandwidth x time, etc. Copyright 2002 The Zig. Bee Alliance, Inc.
Robustness • Direct Sequence with Frequency Agility (DS/FA) combines the best features of DS and FH without most of the problems caused by frequency hopping because frequency changes aren’t necessary most of the time, rather they’re appropriate only on an exception basis. Copyright 2002 The Zig. Bee Alliance, Inc.
Robustness The 802. 11 Working Group couldn’t agree upon which of the following PHYs was the best: FH, IR, or DS. So all three were standardized and left to the market to decide. Of the three PHYs; DS was the clear market winner. DS provided sufficient robustness with higher overall performance. Copyright 2002 The Zig. Bee Alliance, Inc.
Robustness • Excess robustness does not achieve higher performance, rather it typically costs performance Copyright 2002 The Zig. Bee Alliance, Inc.
Conclusion • IEEE 802. 15. 4/Zig. Bee have addressed reliability throughout the ISO stack with proven mechanisms to minimize the uncertainty of the wireless medium Copyright 2002 The Zig. Bee Alliance, Inc.
- Slides: 72