YOUR BOTNET IS MY BOTNET ANALYSIS OF A
YOUR BOTNET IS MY BOTNET: ANALYSIS OF A BOTNET TAKEOVER BRETT STONE-GROSS, MARCO COVA, LORENZO CAVALLARO, BOB GILBERT, MARTIN SZYDLOWSKI, RICHARD KEMMERER, CHRIS KRUEGEL, GIOVANNI VIGNA SECURITY GROUP, DEPT. OF COMPUTER SCIENCE, UNIVERSITY OF CALIFORNIA Presented by Lior Neudorfer
In this presentation… Overview of botnets and the Torpig botnet Botnet coordination: “Domain Flux” The Torpig takeover Torpig data analysis: Botnet Size Financial implications Spam & DDo. S potential Privacy concerns
Botnets: Introduction Bots: malicious code, designed to take control over hosts on the Internet Once infected, hosts join a botnet Botnets are used for: Launching Do. S attacks Mass spam sending Personal data collection Each botnet has a Command & Control server
Botnets: meet Torpig Distributed through a rootkit (“Mebroot”) Preliminary infection through hacked websites Used primarily for data theft “…may be one of the most pervasive and advanced pieces of crimeware ever created…” - RSA Fraud. Action Research Lab
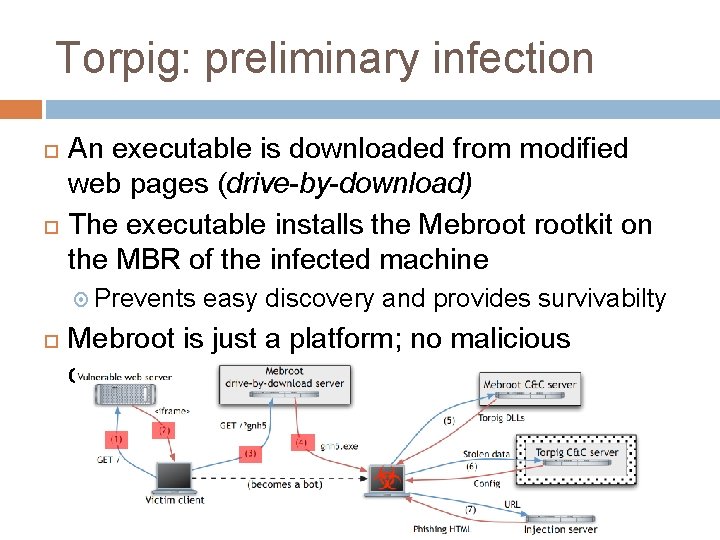
Torpig: preliminary infection An executable is downloaded from modified web pages (drive-by-download) The executable installs the Mebrootkit on the MBR of the infected machine Prevents easy discovery and provides survivabilty Mebroot is just a platform; no malicious capabilities
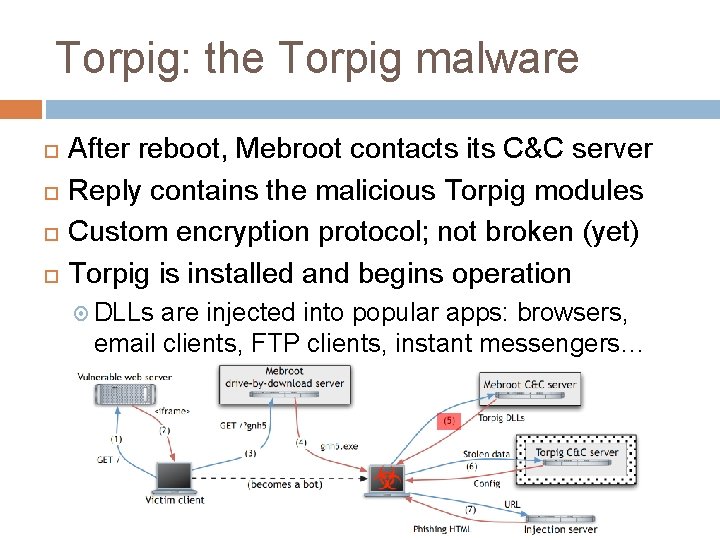
Torpig: the Torpig malware After reboot, Mebroot contacts its C&C server Reply contains the malicious Torpig modules Custom encryption protocol; not broken (yet) Torpig is installed and begins operation DLLs are injected into popular apps: browsers, email clients, FTP clients, instant messengers…
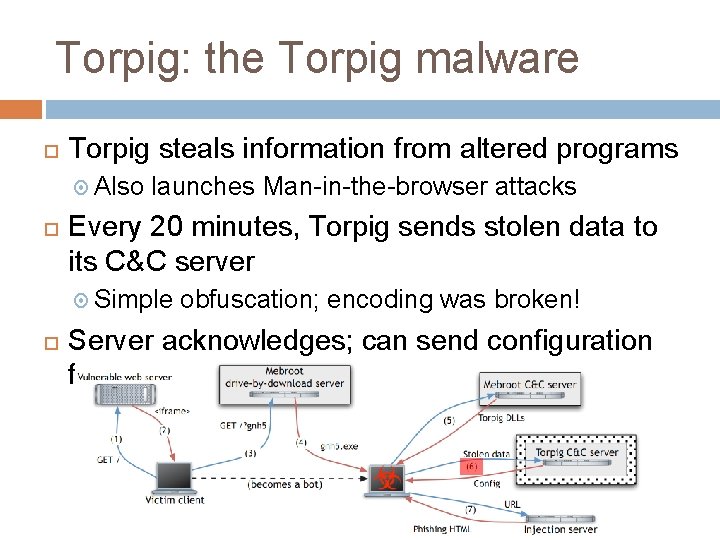
Torpig: the Torpig malware Torpig steals information from altered programs Also launches Man-in-the-browser attacks Every 20 minutes, Torpig sends stolen data to its C&C server Simple obfuscation; encoding was broken! Server acknowledges; can send configuration files
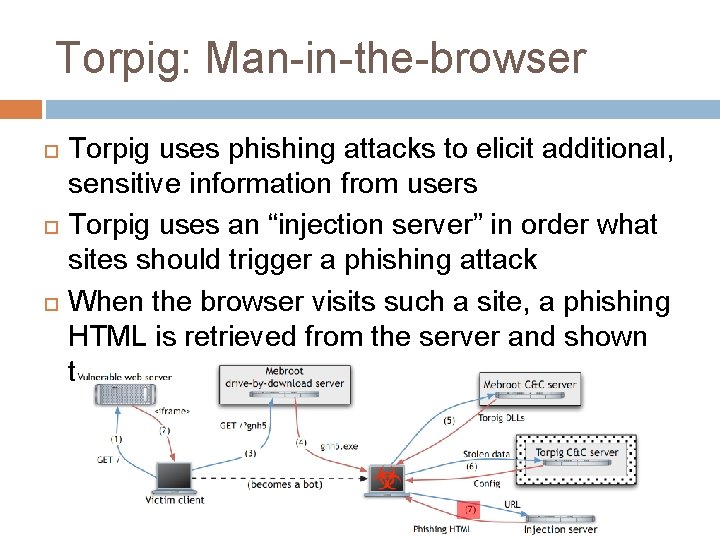
Torpig: Man-in-the-browser Torpig uses phishing attacks to elicit additional, sensitive information from users Torpig uses an “injection server” in order what sites should trigger a phishing attack When the browser visits such a site, a phishing HTML is retrieved from the server and shown to user
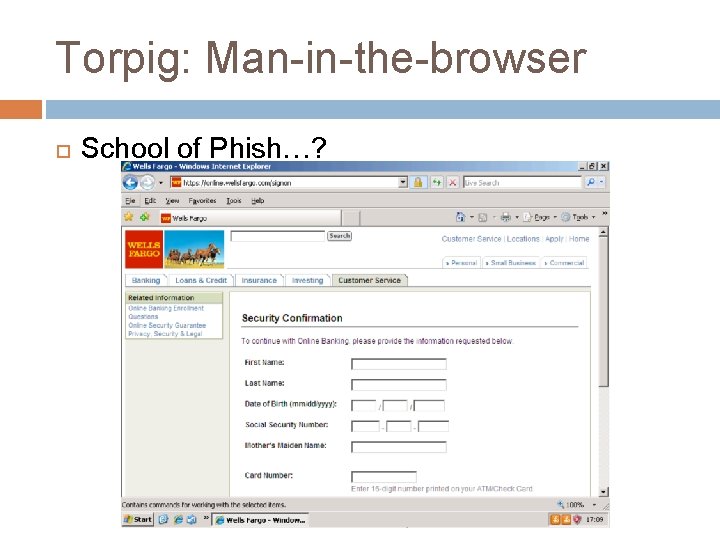
Torpig: Man-in-the-browser School of Phish…?
Domain Flux C&C servers are vulnerable to take-down actions A single IP address/domain name consists a single point-of-failure Torpig uses “Domain Flux” to generate domains Generates a pseudo-random list of domain names Seeded by current date (causes predictability) Bot tries to contact domains in order until it succeeds Domains may be blocked
Domain Flux: threats & countermeasures Botmasters register the domains ahead of their “due date” If defenders block a domain, the botmasters just need to register the next one according to algorithm Botmasters will always win registration war Each domain costs ~5$ to legally register, Some botnets generate 50, 000 domains per day Rogue registrars help botmasters Let’s try and control a domain, not block it…
Taking control Two domain names, predicted by the known domain generation algorithm, were purchased in advance An apache web server was setup on the domain Reminder: A week before time – data begins to flow! Machines Torpig C&C protocol is known with incorrect time settings? Control was achieved for 10 days 69 GB of pcap data
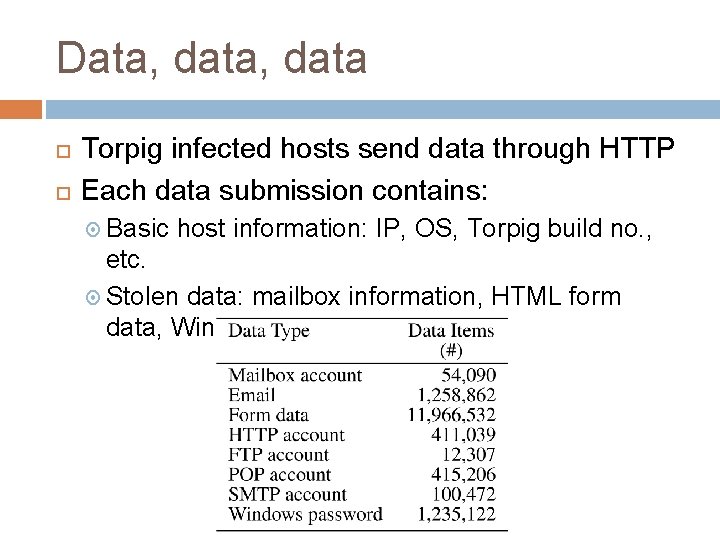
Data, data Torpig infected hosts send data through HTTP Each data submission contains: Basic host information: IP, OS, Torpig build no. , etc. Stolen data: mailbox information, HTML form data, Windows passwords, etc.
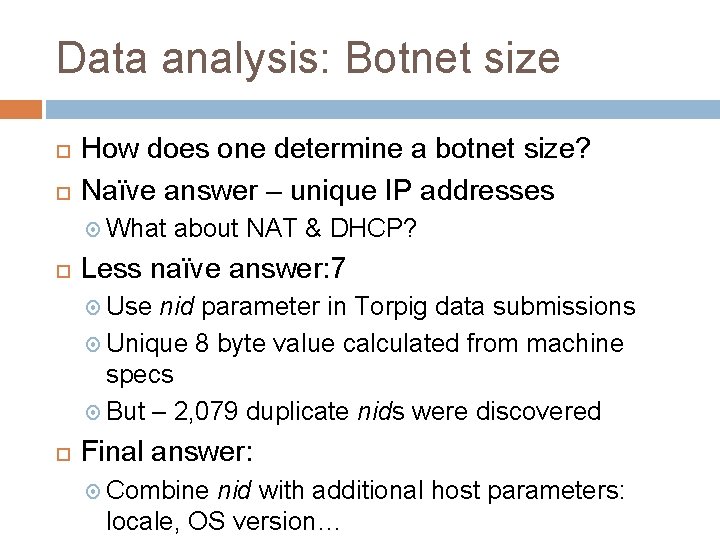
Data analysis: Botnet size How does one determine a botnet size? Naïve answer – unique IP addresses What about NAT & DHCP? Less naïve answer: 7 Use nid parameter in Torpig data submissions Unique 8 byte value calculated from machine specs But – 2, 079 duplicate nids were discovered Final answer: Combine nid with additional host parameters: locale, OS version…
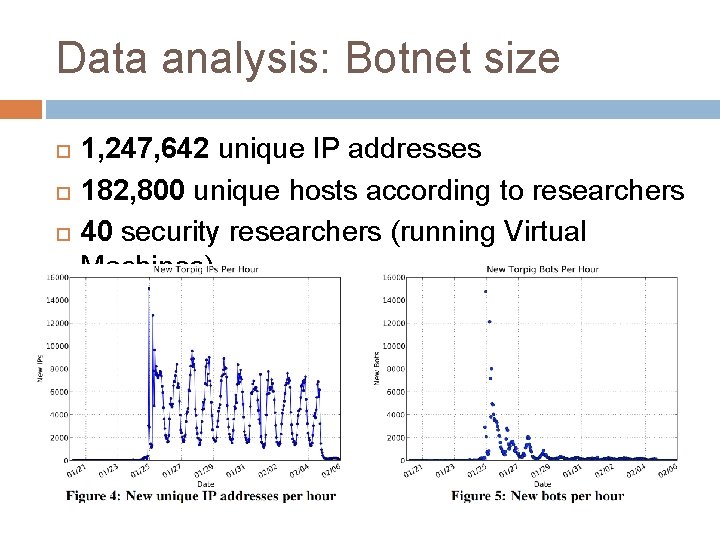
Data analysis: Botnet size 1, 247, 642 unique IP addresses 182, 800 unique hosts according to researchers 40 security researchers (running Virtual Machines)
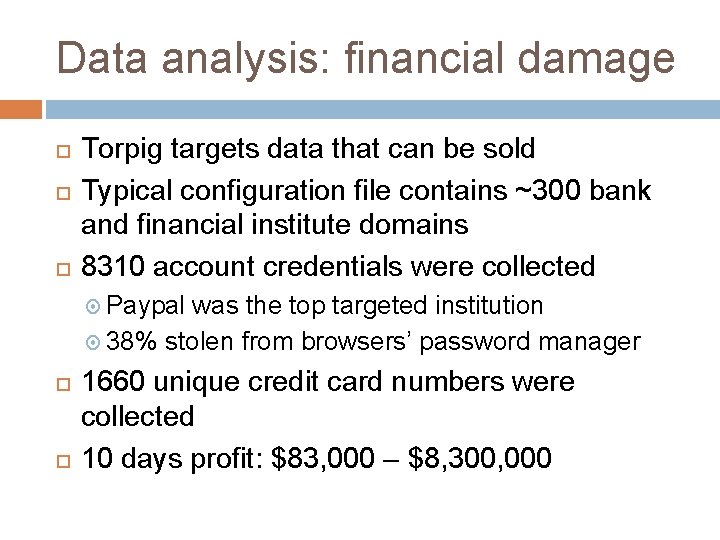
Data analysis: financial damage Torpig targets data that can be sold Typical configuration file contains ~300 bank and financial institute domains 8310 account credentials were collected Paypal was the top targeted institution 38% stolen from browsers’ password manager 1660 unique credit card numbers were collected 10 days profit: $83, 000 – $8, 300, 000
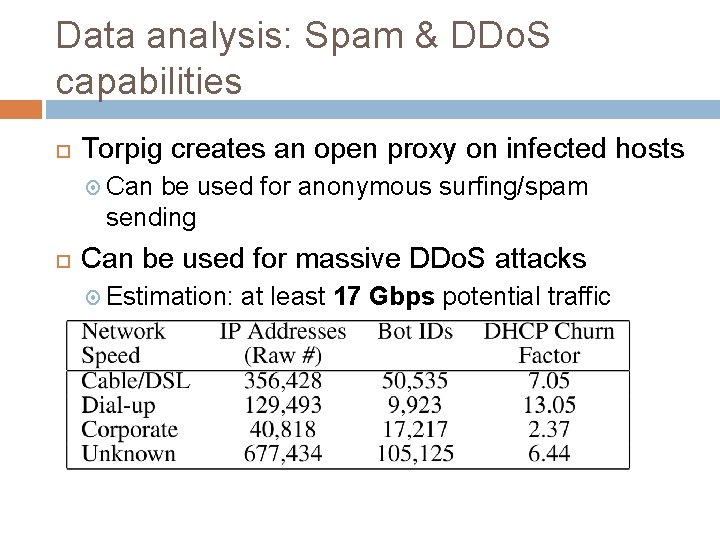
Data analysis: Spam & DDo. S capabilities Torpig creates an open proxy on infected hosts Can be used for anonymous surfing/spam sending Can be used for massive DDo. S attacks Estimation: at least 17 Gbps potential traffic
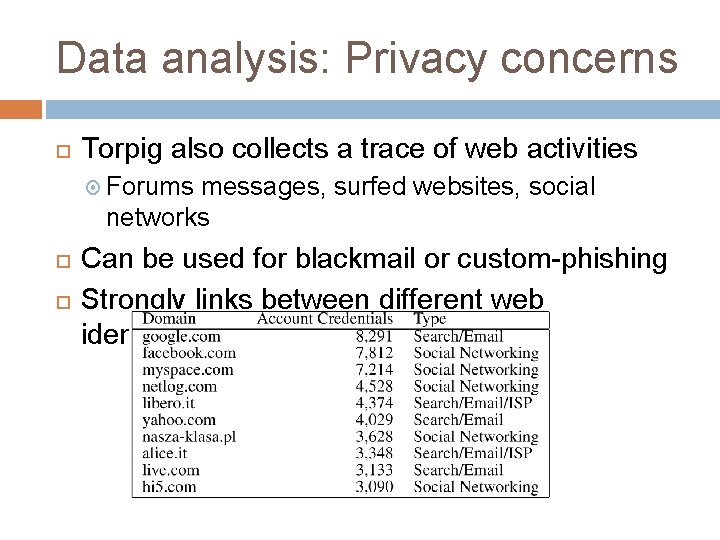
Data analysis: Privacy concerns Torpig also collects a trace of web activities Forums messages, surfed websites, social networks Can be used for blackmail or custom-phishing Strongly links between different web identities…
Questions?
- Slides: 19