Year 2 Chapter 6Cisco 3 Module 6 ACLs
- Slides: 30
Year 2 - Chapter 6/Cisco 3 - Module 6 ACLs
Objectives p p p p Define and describe the purpose and operation of ACLs Explain the processes involved in testing packets with ACLs Describe ACL configuration commands, global statements, and interface commands Define and explain the function and operation of wildcard masks bits and the wildcards any and host Describe standard ACLs Describe extended ACLs Describe named ACLs Monitor and verify selected ACL operations on the router
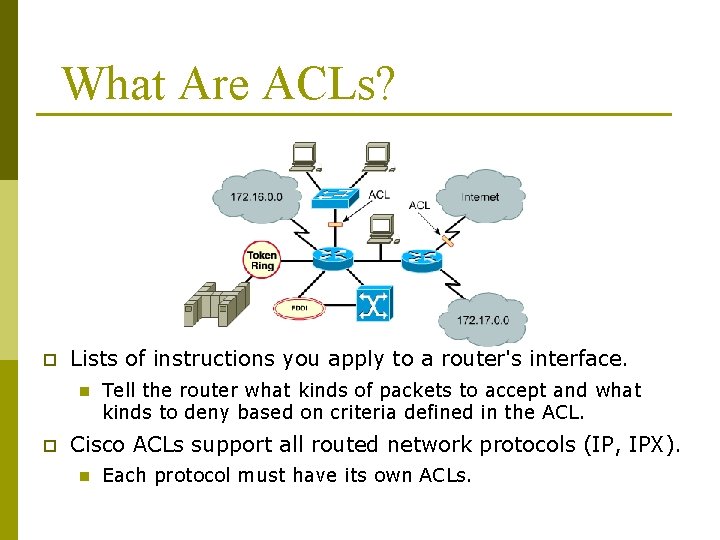
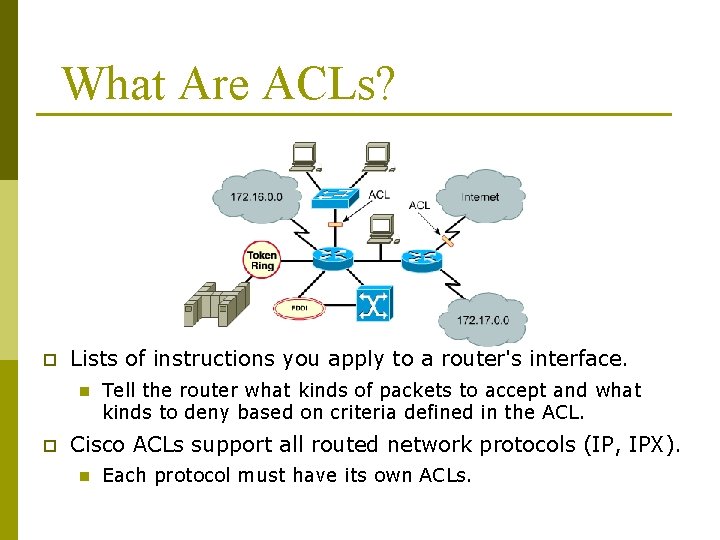
What Are ACLs? p Lists of instructions you apply to a router's interface. n p Tell the router what kinds of packets to accept and what kinds to deny based on criteria defined in the ACL. Cisco ACLs support all routed network protocols (IP, IPX). n Each protocol must have its own ACLs.
Definition Of ACL p p p ACLs are lists of instructions you apply to a router's interface. These lists tell the router what kinds of packets to accept and what kinds of packets to deny. Acceptance and denial can be based on certain specifications, such as source address, destination address, Traffic Direction, and port number. ACL in then applied to a router interface. Any traffic going through the interface is tested against certain conditions that are part of the ACLs must be defined on a per-protocol basis. If your router interface were configured for IP, Apple. Talk, and IPX, you would need to define at least three ACLs.
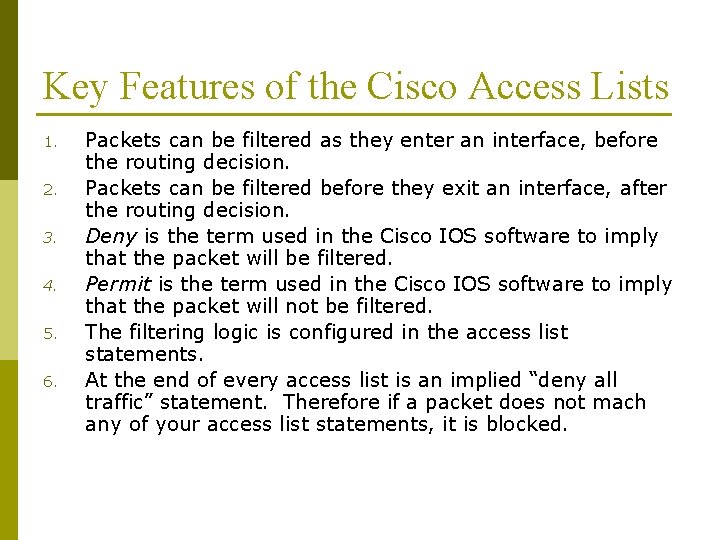
Key Features of the Cisco Access Lists 1. 2. 3. 4. 5. 6. Packets can be filtered as they enter an interface, before the routing decision. Packets can be filtered before they exit an interface, after the routing decision. Deny is the term used in the Cisco IOS software to imply that the packet will be filtered. Permit is the term used in the Cisco IOS software to imply that the packet will not be filtered. The filtering logic is configured in the access list statements. At the end of every access list is an implied “deny all traffic” statement. Therefore if a packet does not mach any of your access list statements, it is blocked.
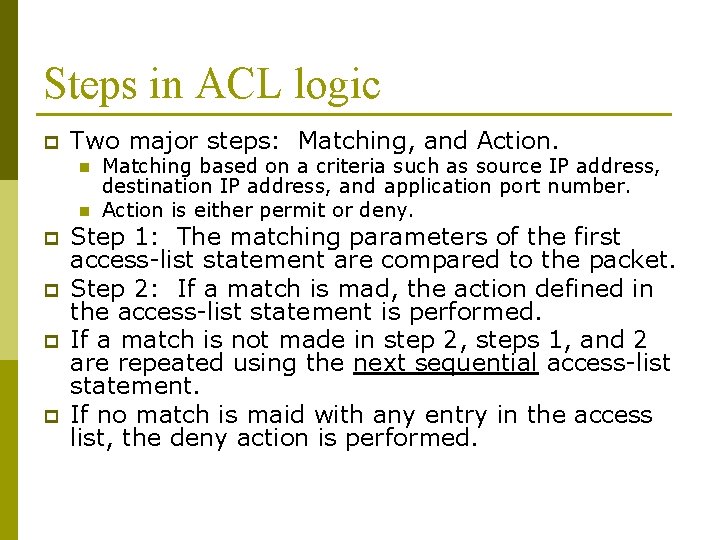
Steps in ACL logic p Two major steps: Matching, and Action. n n p p Matching based on a criteria such as source IP address, destination IP address, and application port number. Action is either permit or deny. Step 1: The matching parameters of the first access-list statement are compared to the packet. Step 2: If a match is mad, the action defined in the access-list statement is performed. If a match is not made in step 2, steps 1, and 2 are repeated using the next sequential access-list statement. If no match is maid with any entry in the access list, the deny action is performed.
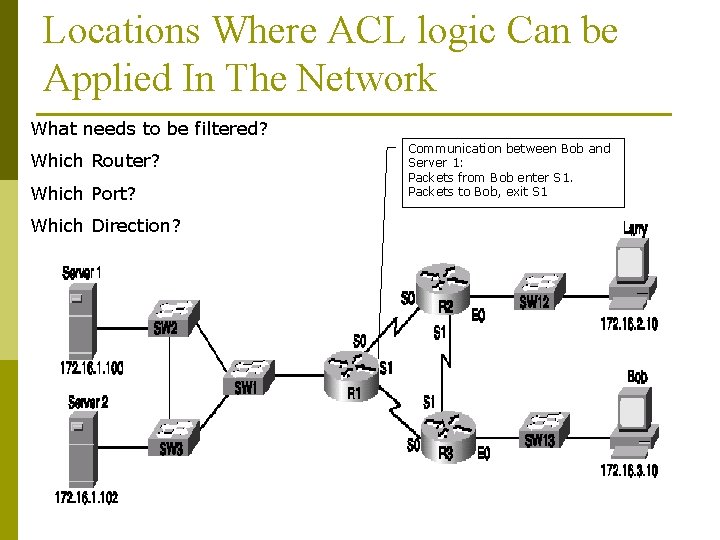
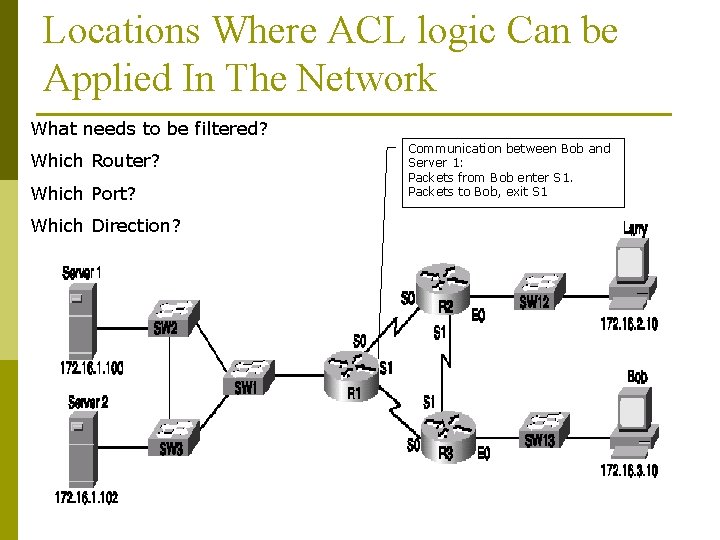
Locations Where ACL logic Can be Applied In The Network What needs to be filtered? Which Router? Which Port? Which Direction? Communication between Bob and Server 1: Packets from Bob enter S 1. Packets to Bob, exit S 1
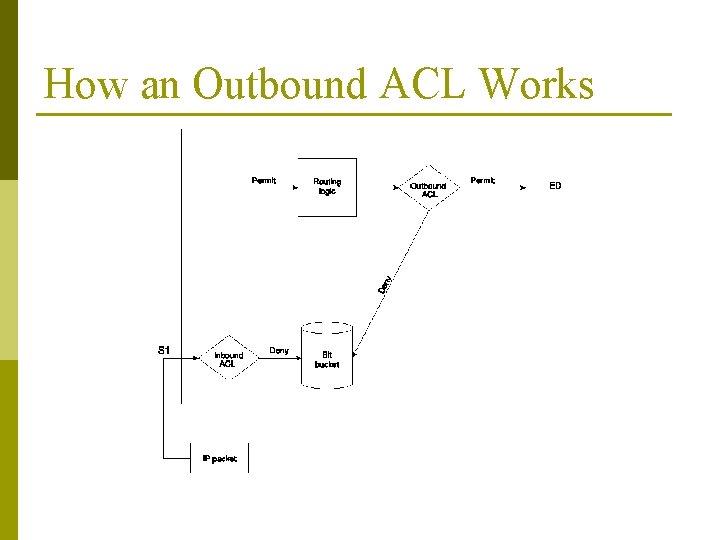
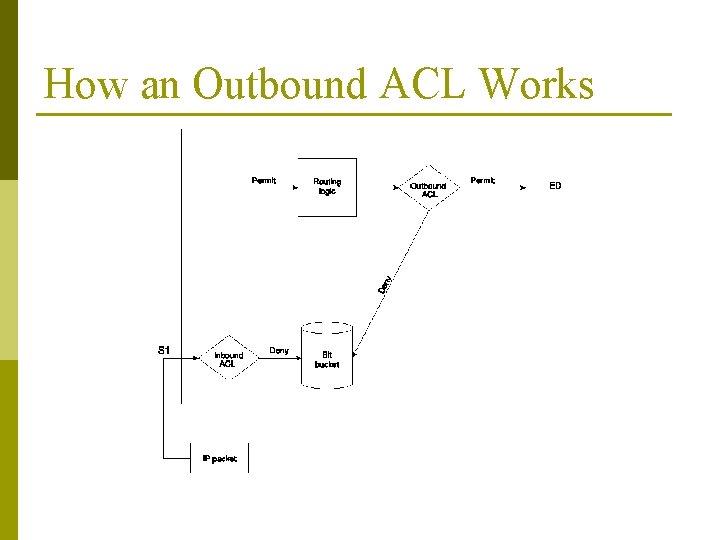
How an Outbound ACL Works
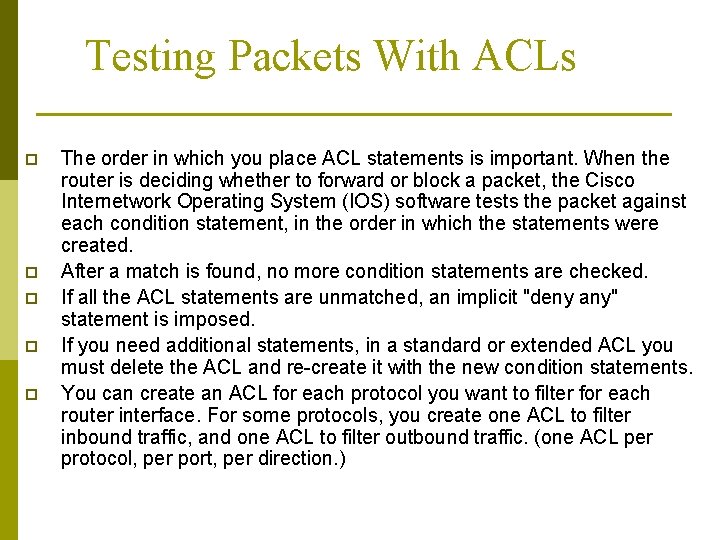
Testing Packets With ACLs p p p The order in which you place ACL statements is important. When the router is deciding whether to forward or block a packet, the Cisco Internetwork Operating System (IOS) software tests the packet against each condition statement, in the order in which the statements were created. After a match is found, no more condition statements are checked. If all the ACL statements are unmatched, an implicit "deny any" statement is imposed. If you need additional statements, in a standard or extended ACL you must delete the ACL and re-create it with the new condition statements. You can create an ACL for each protocol you want to filter for each router interface. For some protocols, you create one ACL to filter inbound traffic, and one ACL to filter outbound traffic. (one ACL per protocol, per port, per direction. )
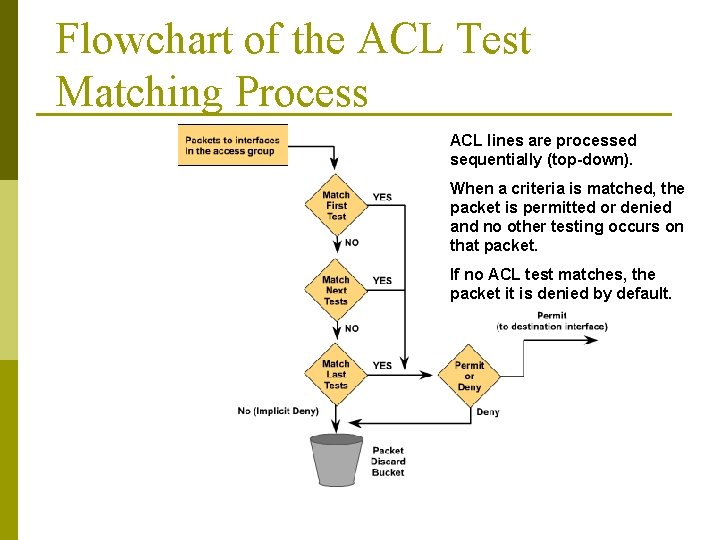
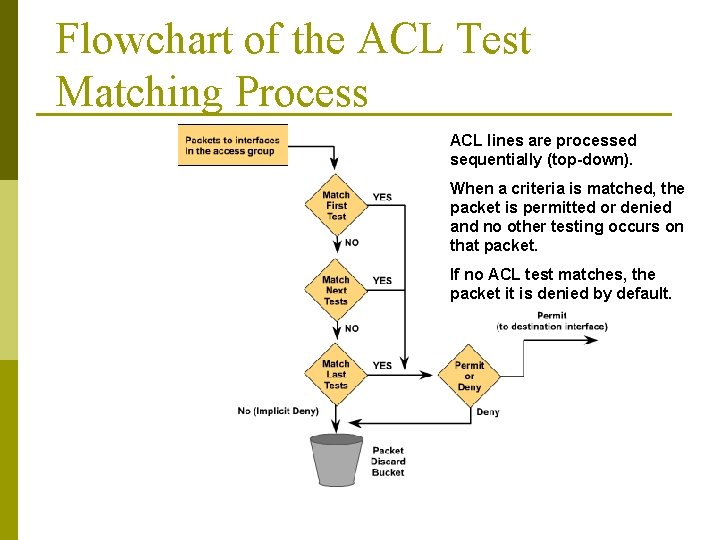
Flowchart of the ACL Test Matching Process ACL lines are processed sequentially (top-down). When a criteria is matched, the packet is permitted or denied and no other testing occurs on that packet. If no ACL test matches, the packet it is denied by default.
Inbound ACLs VS. Outbound ACLs p p p Outbound ACLs are generally more efficient than inbound, and are therefore preferred. A router with an inbound ACL must check every packet to see whether it matches the ACL condition before switching the packet to an outbound interface. Inbound access lists are dangerous because all the packets coming are examined and could be filtered including IGRP updates. Outbound ACLs are less dangerous because the router will not filter packets originating on that router.
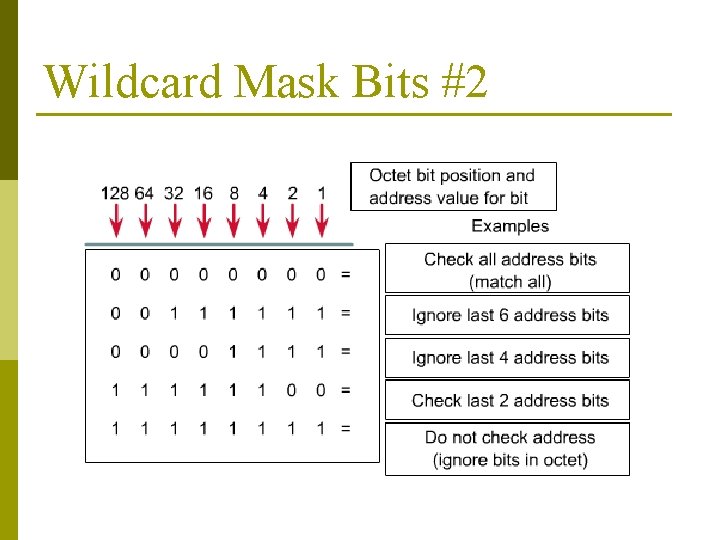
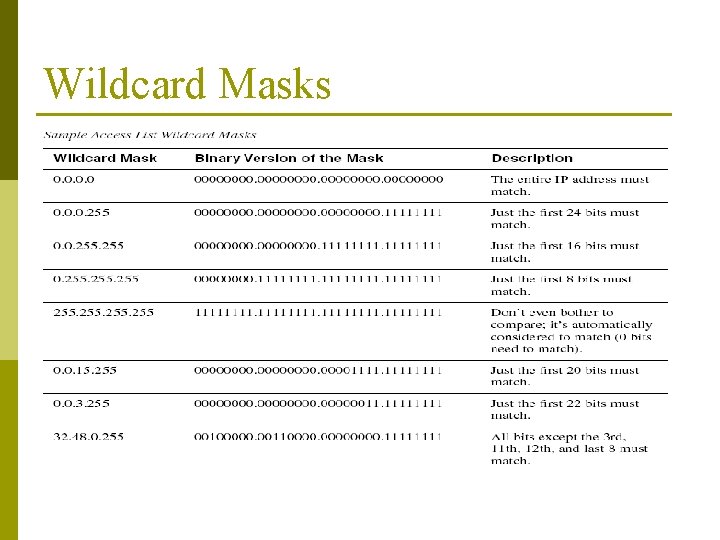
The Purpose and Function of Wilde Card Mask p ACLs use wildcard masking to identify a single or multiple addresses for permit or deny tests. p A wildcard mask is a 32 -bit quantity that is divided into four octets, with each octet containing 8 bits. A wildcard mask bit 0 means "check the corresponding bit value" and a wildcard mask bit 1 means "do not check (ignore) that corresponding bit value“ A wildcard mask is paired with an IP address. The numbers one and zero are used to identify how to treat the corresponding IP address bits. p p ACLs define the portion of the IP address that should be examined.
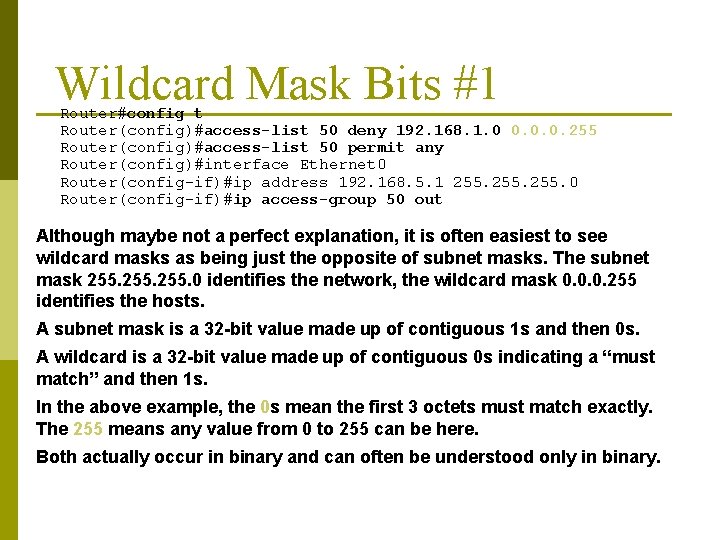
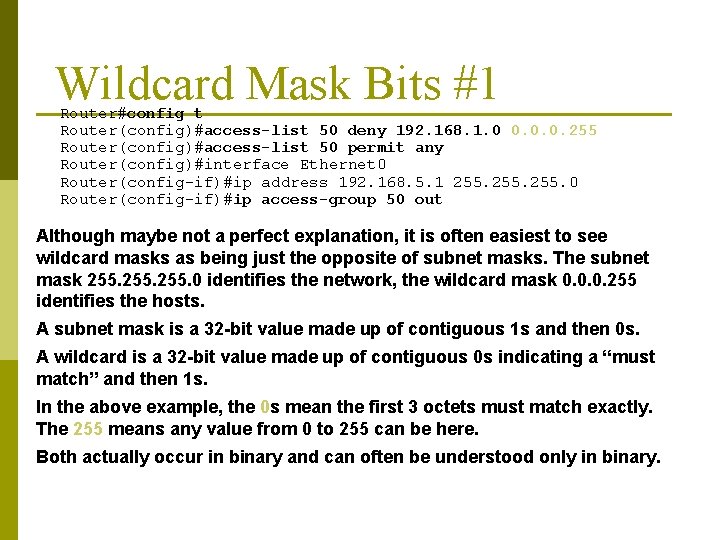
Wildcard Mask Bits #1 Router#config t Router(config)#access-list 50 deny 192. 168. 1. 0 0. 0. 0. 255 Router(config)#access-list 50 permit any Router(config)#interface Ethernet 0 Router(config-if)#ip address 192. 168. 5. 1 255. 0 Router(config-if)#ip access-group 50 out Although maybe not a perfect explanation, it is often easiest to see wildcard masks as being just the opposite of subnet masks. The subnet mask 255. 0 identifies the network, the wildcard mask 0. 0. 0. 255 identifies the hosts. A subnet mask is a 32 -bit value made up of contiguous 1 s and then 0 s. A wildcard is a 32 -bit value made up of contiguous 0 s indicating a “must match” and then 1 s. In the above example, the 0 s mean the first 3 octets must match exactly. The 255 means any value from 0 to 255 can be here. Both actually occur in binary and can often be understood only in binary.
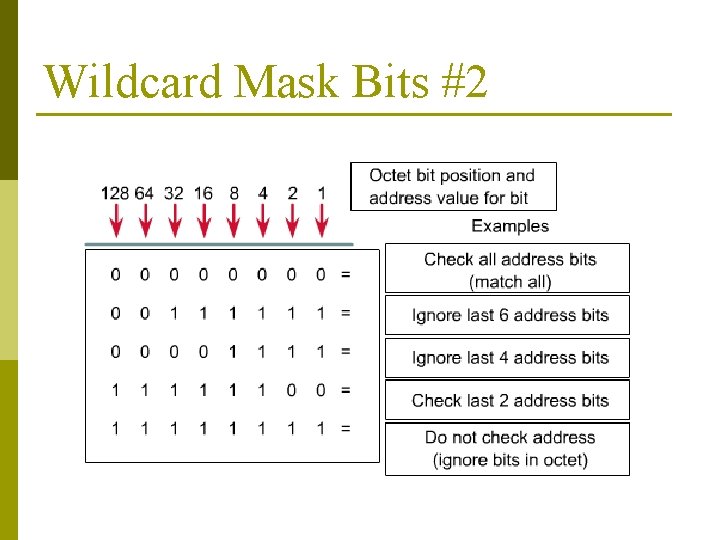
Wildcard Mask Bits #2
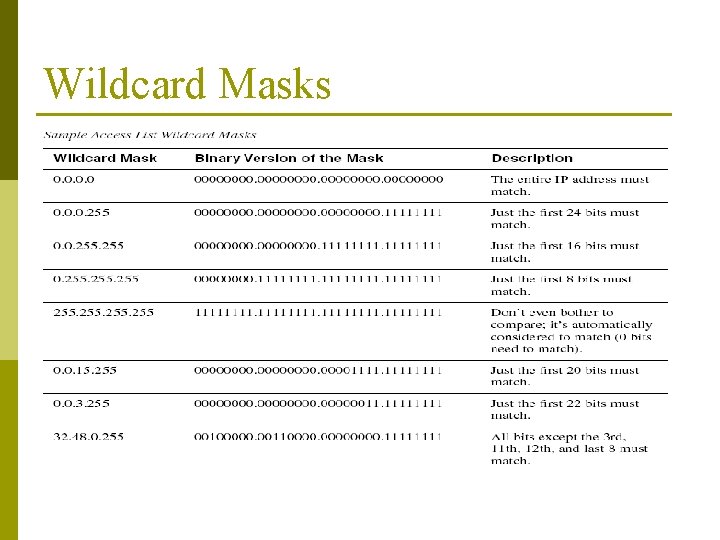
Wildcard Masks
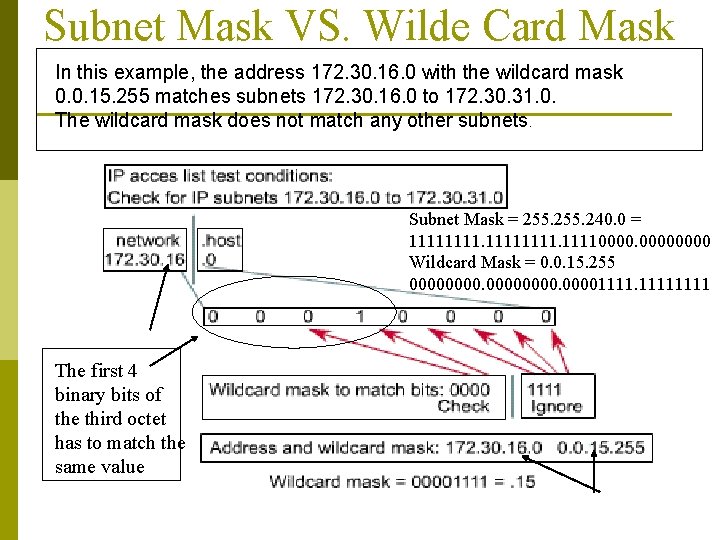
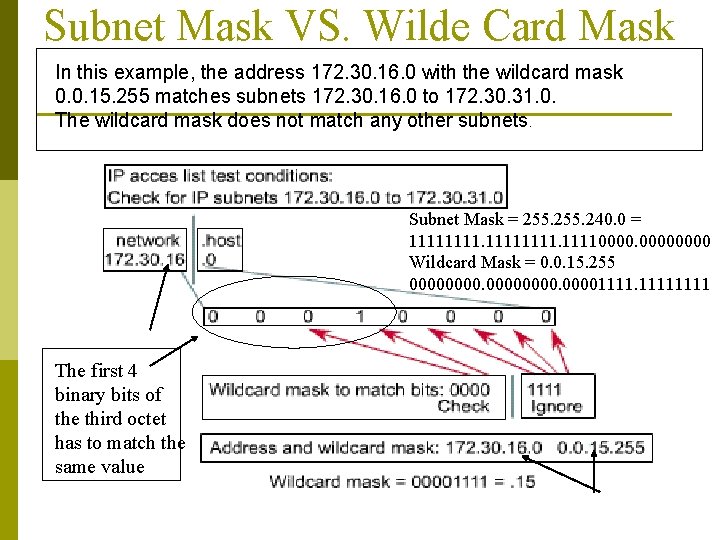
Subnet Mask VS. Wilde Card Mask In this example, the address 172. 30. 16. 0 with the wildcard mask 0. 0. 15. 255 matches subnets 172. 30. 16. 0 to 172. 30. 31. 0. The wildcard mask does not match any other subnets. Subnet Mask = 255. 240. 0 = 111111110000 Wildcard Mask = 0. 0. 15. 255 000000001111 The first 4 binary bits of the third octet has to match the same value
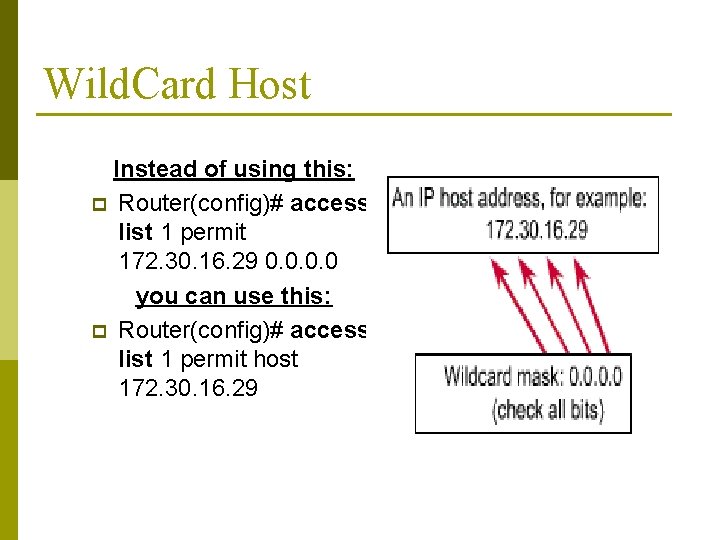
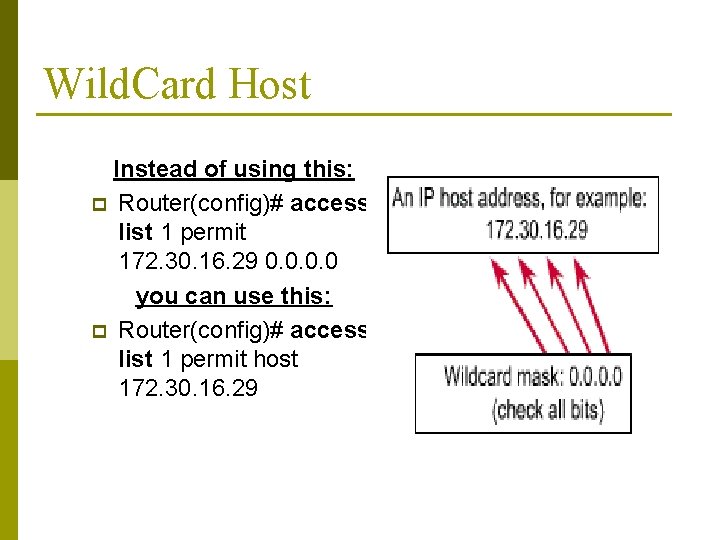
Wild. Card Host Instead of using this: p Router(config)# accesslist 1 permit 172. 30. 16. 29 0. 0 you can use this: p Router(config)# accesslist 1 permit host 172. 30. 16. 29
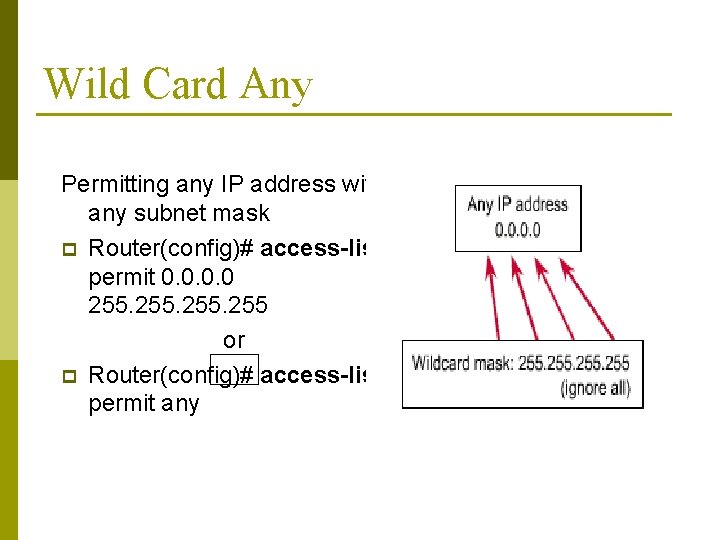
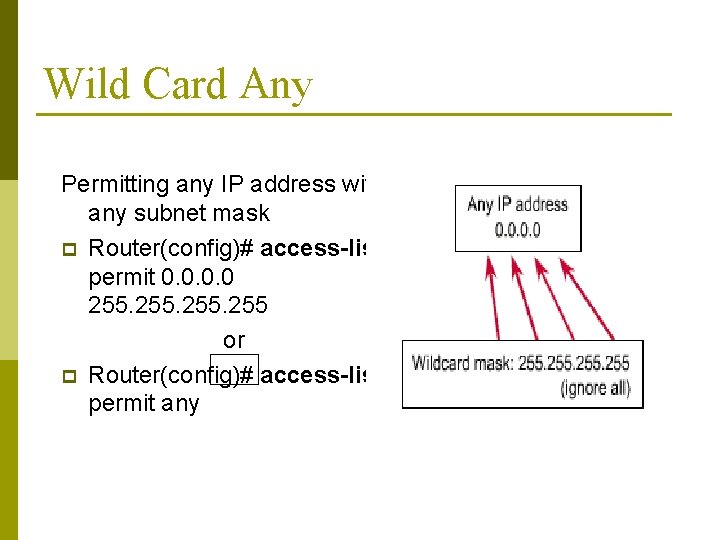
Wild Card Any Permitting any IP address with any subnet mask p Router(config)# access-list 1 permit 0. 0 255 or p Router(config)# access-list 1 permit any
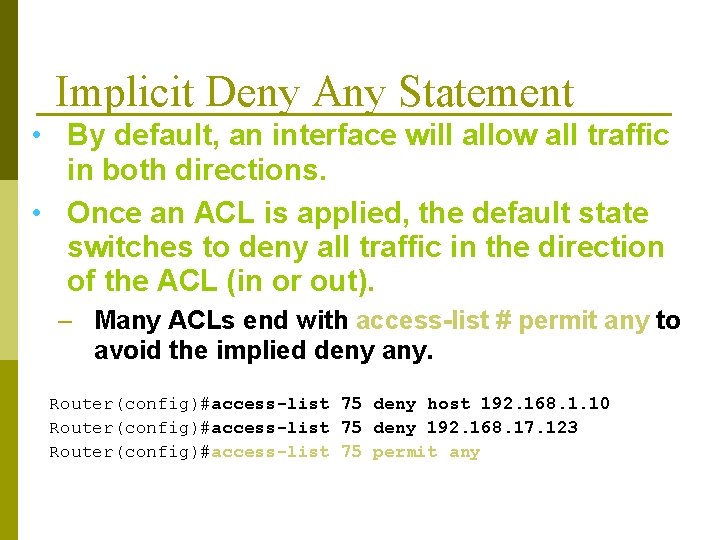
Implicit Deny Any Statement • By default, an interface will allow all traffic in both directions. • Once an ACL is applied, the default state switches to deny all traffic in the direction of the ACL (in or out). – Many ACLs end with access-list # permit any to avoid the implied deny any. Router(config)#access-list 75 deny host 192. 168. 1. 10 Router(config)#access-list 75 deny 192. 168. 17. 123 Router(config)#access-list 75 permit any
Permit and Deny Statements p Except in special circumstances, every ACL must have at least one permit statement. n An ACL made up of only deny statements combined with the implicit deny any statement will block all traffic in the direction of the ACL.
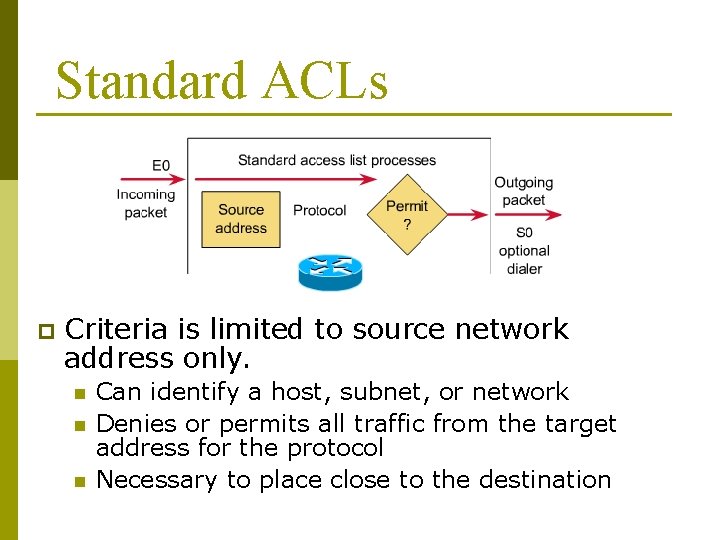
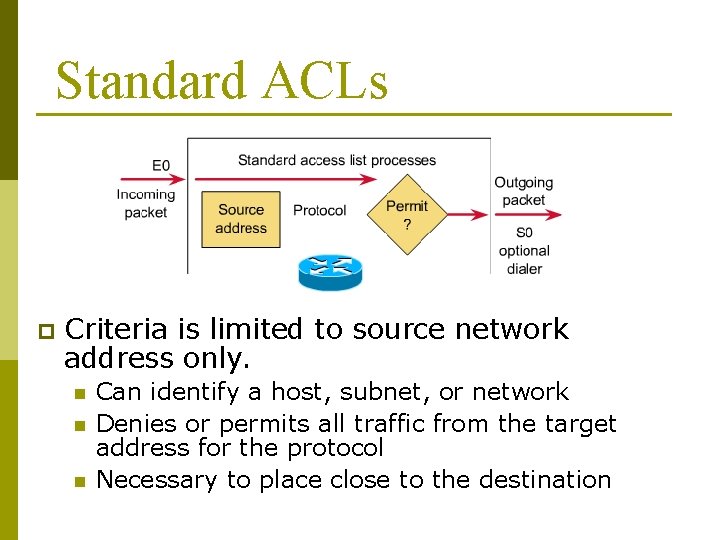
Standard ACLs p Criteria is limited to source network address only. n n n Can identify a host, subnet, or network Denies or permits all traffic from the target address for the protocol Necessary to place close to the destination
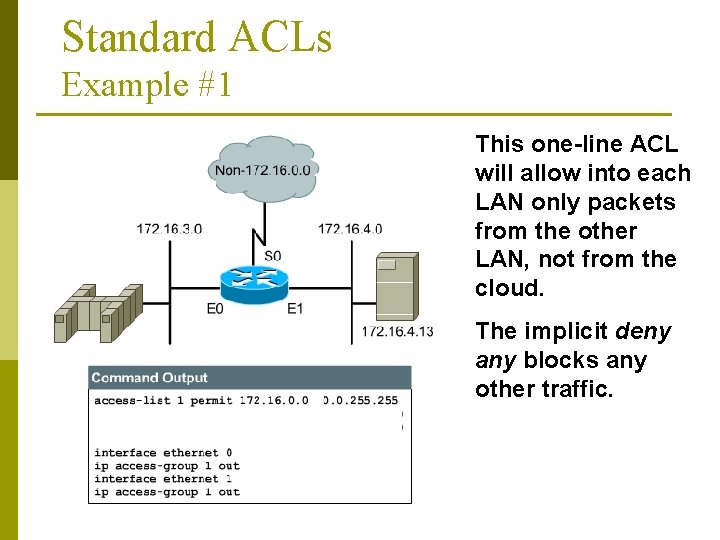
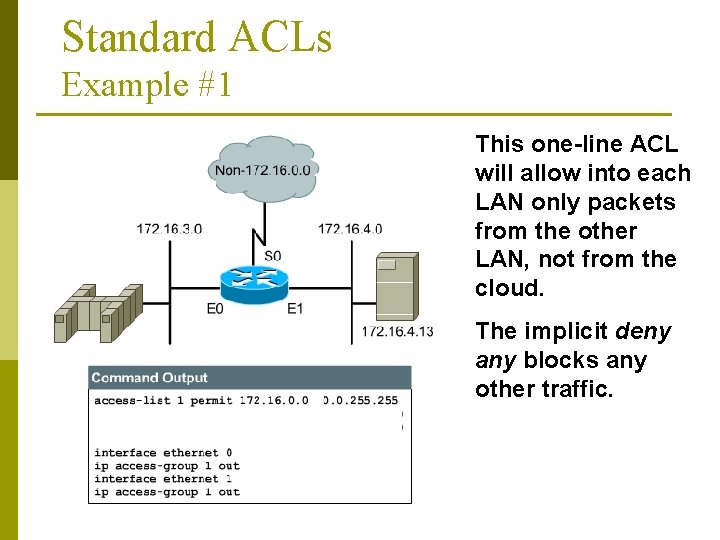
Standard ACLs Example #1 This one-line ACL will allow into each LAN only packets from the other LAN, not from the cloud. The implicit deny any blocks any other traffic.
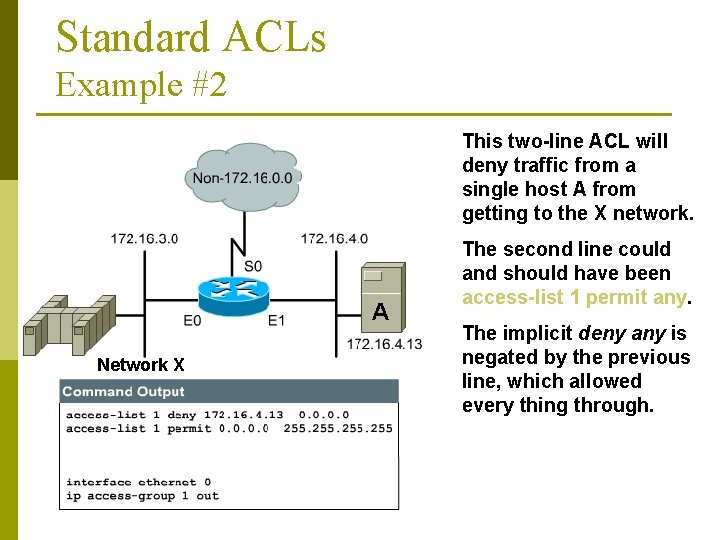
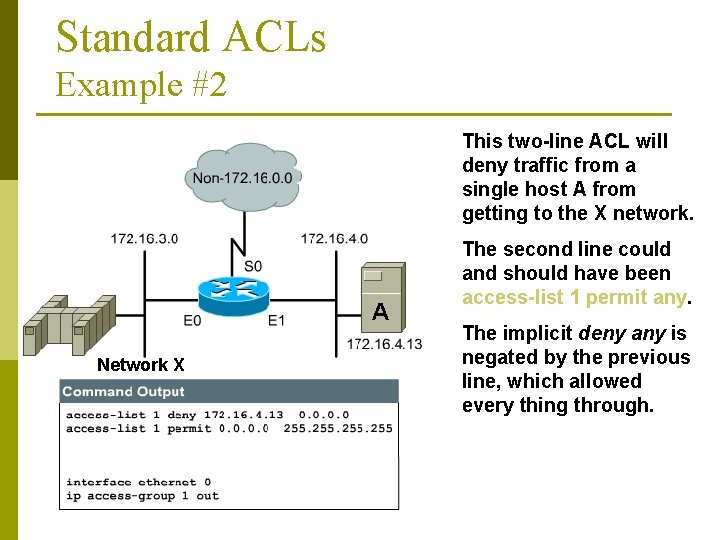
Standard ACLs Example #2 This two-line ACL will deny traffic from a single host A from getting to the X network. A Network X The second line could and should have been access-list 1 permit any. The implicit deny any is negated by the previous line, which allowed every thing through.
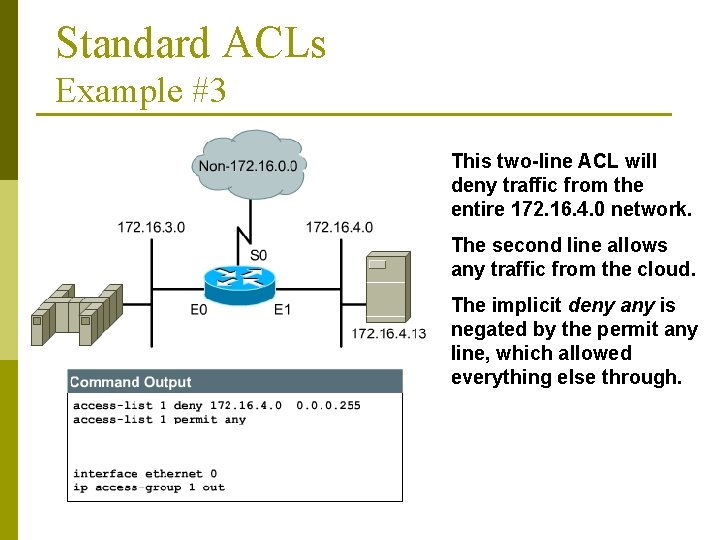
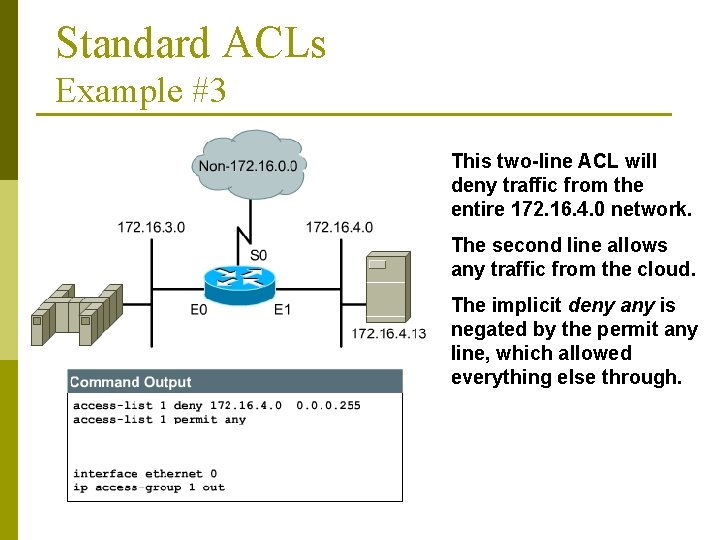
Standard ACLs Example #3 This two-line ACL will deny traffic from the entire 172. 16. 4. 0 network. The second line allows any traffic from the cloud. The implicit deny any is negated by the permit any line, which allowed everything else through.
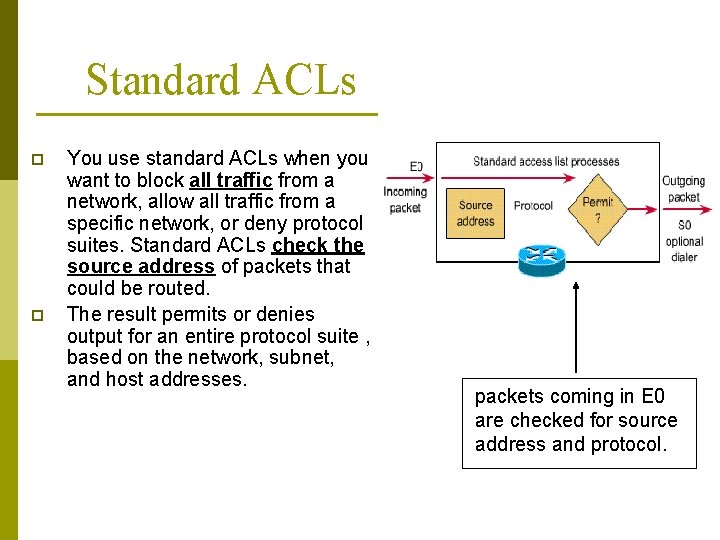
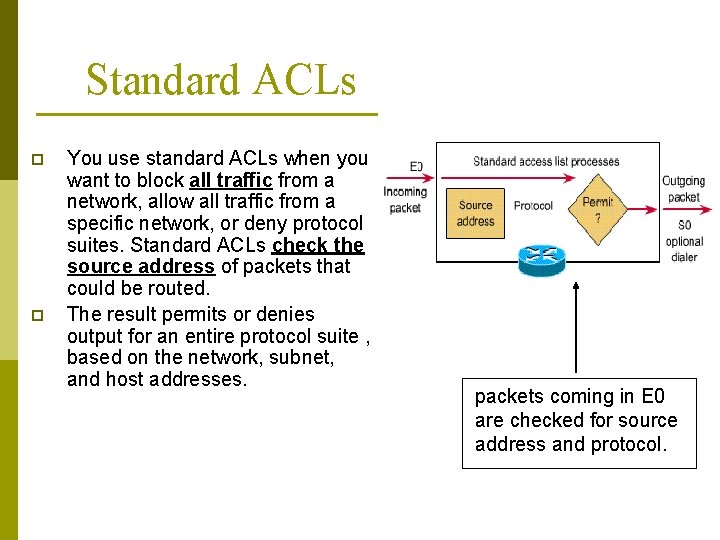
Standard ACLs p p You use standard ACLs when you want to block all traffic from a network, allow all traffic from a specific network, or deny protocol suites. Standard ACLs check the source address of packets that could be routed. The result permits or denies output for an entire protocol suite , based on the network, subnet, and host addresses. packets coming in E 0 are checked for source address and protocol.
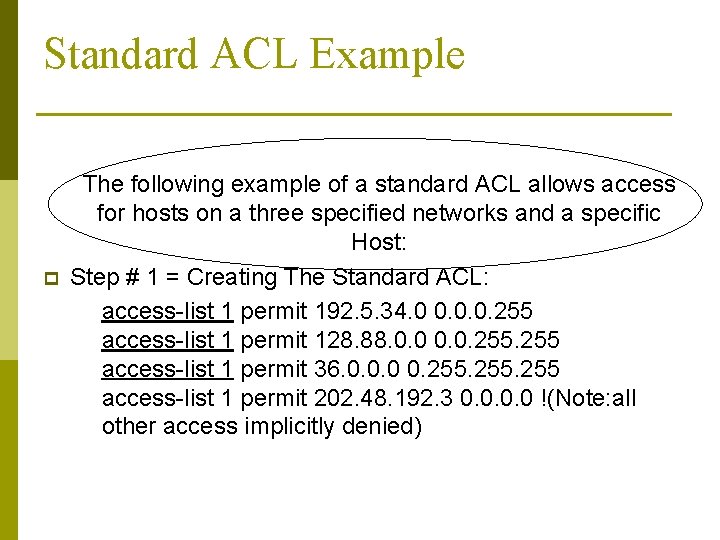
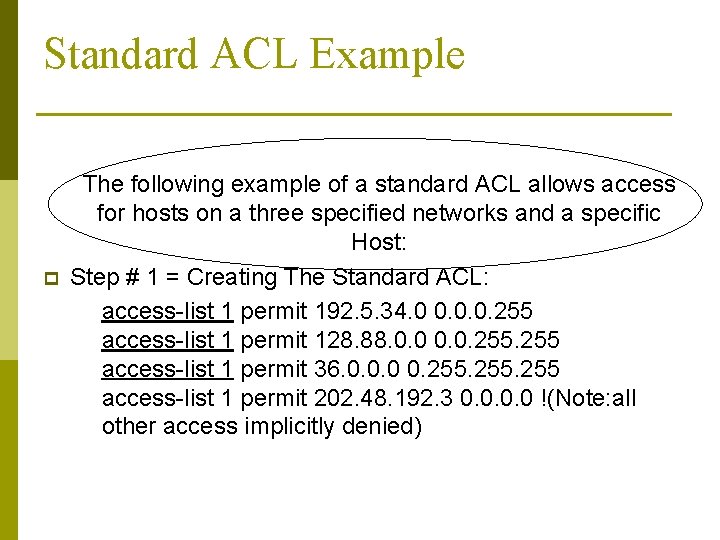
Standard ACL Example p The following example of a standard ACL allows access for hosts on a three specified networks and a specific Host: Step # 1 = Creating The Standard ACL: access-list 1 permit 192. 5. 34. 0 0. 0. 0. 255 access-list 1 permit 128. 88. 0. 0. 255 access-list 1 permit 36. 0. 0. 0 0. 255 access-list 1 permit 202. 48. 192. 3 0. 0 !(Note: all other access implicitly denied)
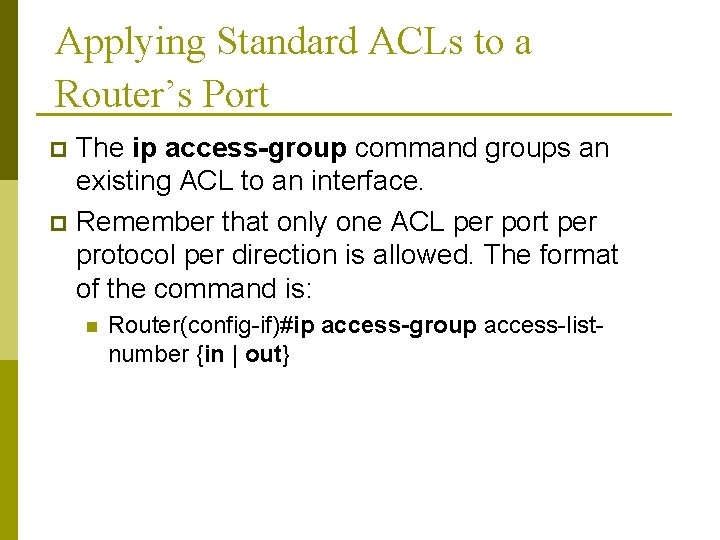
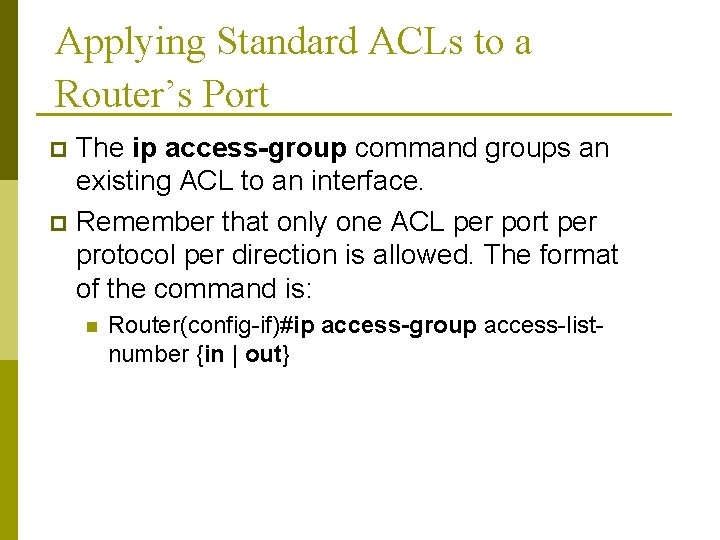
Applying Standard ACLs to a Router’s Port The ip access-group command groups an existing ACL to an interface. p Remember that only one ACL per port per protocol per direction is allowed. The format of the command is: p n Router(config-if)#ip access-group access-listnumber {in | out}
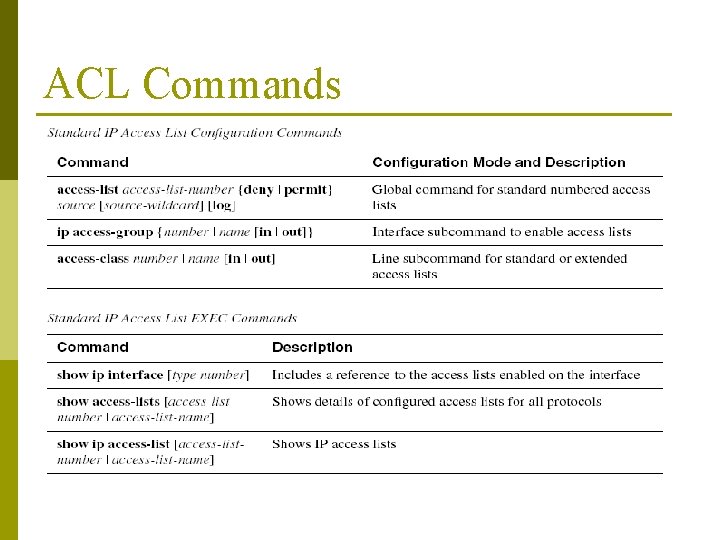
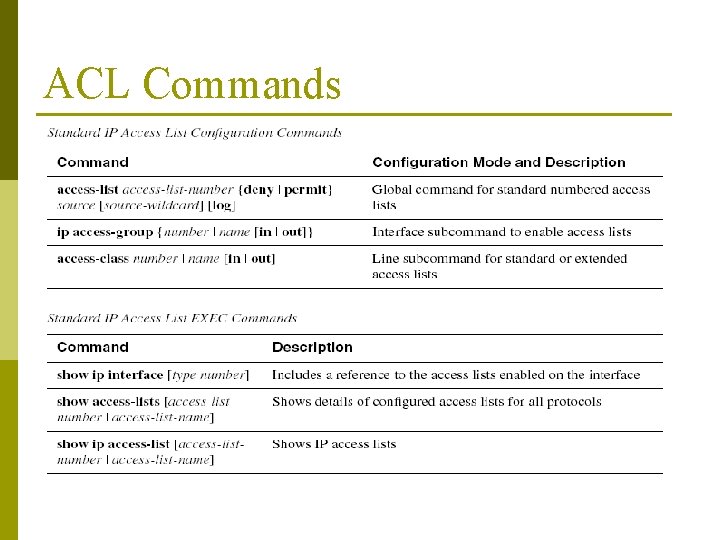
ACL Commands
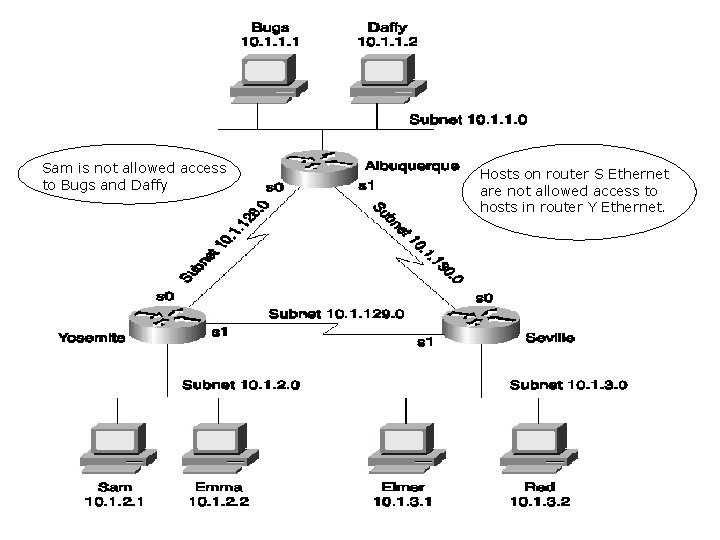
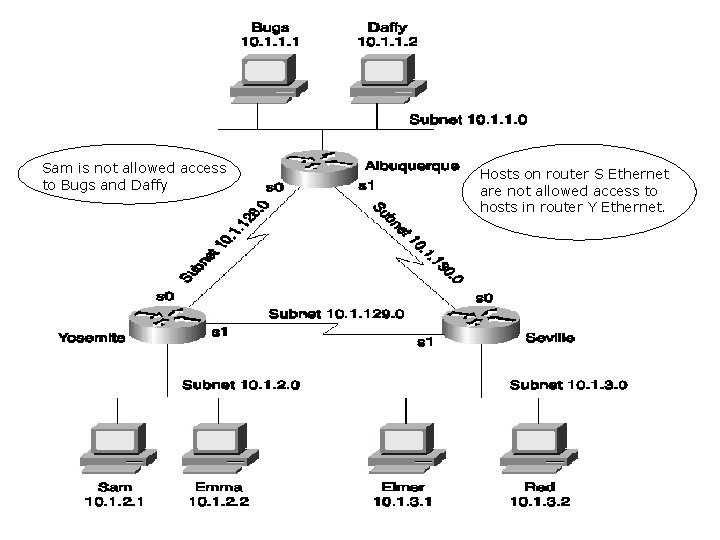
Sam is not allowed access to Bugs and Daffy Hosts on router S Ethernet are not allowed access to hosts in router Y Ethernet.
Standard ACLs Practice Problems p Labs p