XMSS A Practical Forward Secure Signature Scheme based
XMSS - A Practical Forward Secure Signature Scheme based on Minimal Security Assumptions J. Buchmann, E. Dahmen, A. Hülsing 02. 12. 2011 | TU Darmstadt | A. Huelsing | 1

Digital Signature Schemes 02. 12. 2011 | TU Darmstadt | A. Huelsing | 2

RSA – DSA – EC-DSA - … Trapdoor oneway function RSA, DH, SVP, MQ, … Digital signature scheme 02. 12. 2011 | TU Darmstadt | A. Huelsing | 3 Collision resistant hash function
Digital Signature Schemes - Strong complexity theoretic assumption (Trapdoor one-way function) hard to fulfill - Specific hardness assumptions Quantum computers, new algorithms + efficient but mostly in ROM 02. 12. 2011 | TU Darmstadt | A. Huelsing | 4
The e. Xtended Merkle Signature Scheme XMSS 02. 12. 2011 | TU Darmstadt | A. Huelsing | 5

The e. Xtended Merkle Signature Scheme (XMSS) § Minimal complexity theoretic assumptions § Generic construction (No specific hardness assumption) § Efficient (comparable to RSA) § Forward secure 02. 12. 2011 | TU Darmstadt | A. Huelsing | 6
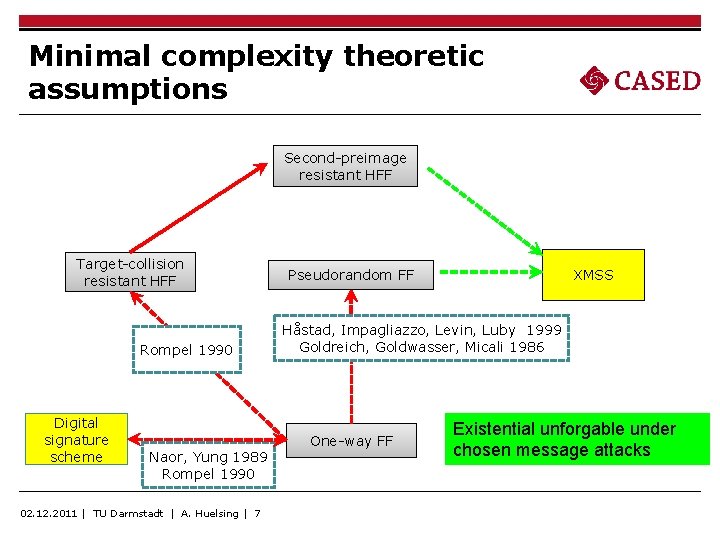
Minimal complexity theoretic assumptions Second-preimage resistant HFF Target-collision resistant HFF Rompel 1990 Digital signature scheme Naor, Yung 1989 Rompel 1990 02. 12. 2011 | TU Darmstadt | A. Huelsing | 7 Pseudorandom FF XMSS Håstad, Impagliazzo, Levin, Luby 1999 Goldreich, Goldwasser, Micali 1986 One-way FF Existential unforgable under chosen message attacks

Output length of hash functions Hash function h: {0, 1}* → {0, 1}m Assume: - only generic attacks, - security level n Collision resistance required: → generic attack = birthday attack → m = 2 n Second-preimage resistance required: → generic attack = exhaustive search → 02. 12. 2011 | TU Darmstadt | A. Huelsing | 8 m=n
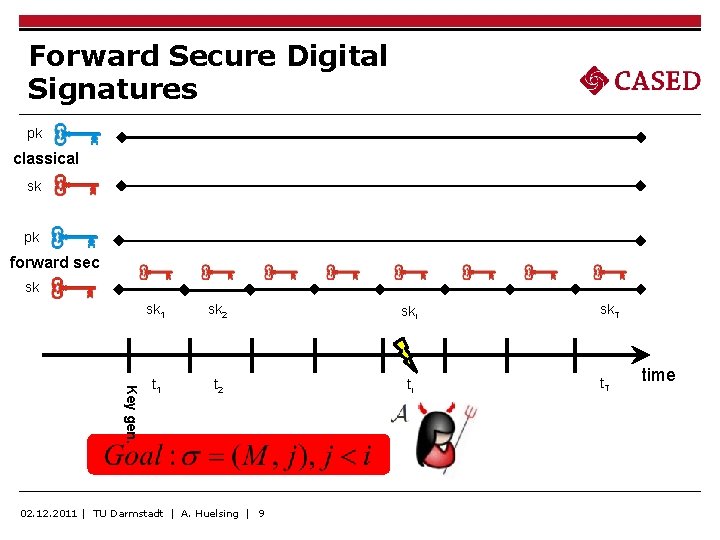
Forward Secure Digital Signatures pk classical sk pk forward sec sk Key gen. sk 1 sk 2 ski t 1 t 2 ti 02. 12. 2011 | TU Darmstadt | A. Huelsing | 9 sk. T time

Construction 02. 12. 2011 | TU Darmstadt | A. Huelsing | 10
![XMSS – Winternitz OTS [Buchmann et al. 2011] - Uses pseudorandom function family - XMSS – Winternitz OTS [Buchmann et al. 2011] - Uses pseudorandom function family -](http://slidetodoc.com/presentation_image_h/97eee2d772e40063441bb34141329666/image-11.jpg)
XMSS – Winternitz OTS [Buchmann et al. 2011] - Uses pseudorandom function family - Winternitz parameter w, message length m, random value x sk 1 pk 1 x l skl pkl x w 02. 12. 2011 | TU Darmstadt | A. Huelsing | 11

XMSS – secret key PRG PRG PRG For multiple signatures use many key pairs. Generated using pseudorandom generator (PRG), build using PRFF Fn: Secret key: Random SEED for pseudorandom generation of current signature key. 02. 12. 2011 | TU Darmstadt | A. Huelsing | 12
![XMSS – public key Modified Merkle Tree [Dahmen et al 2008] h second preimage XMSS – public key Modified Merkle Tree [Dahmen et al 2008] h second preimage](http://slidetodoc.com/presentation_image_h/97eee2d772e40063441bb34141329666/image-13.jpg)
XMSS – public key Modified Merkle Tree [Dahmen et al 2008] h second preimage resistant hash function Public key =( , b 0, b 1, b 2, h) bh b 1 b 0 02. 12. 2011 | TU Darmstadt | A. Huelsing | 13 b 0

XMSS signature b 2 b 1 b 0 b 0 i i 02. 12. 2011 | TU Darmstadt | A. Huelsing | 14 Signature = (i, , )

XMSS forward secure PRG FSPRG FSPRG: Forward secure PRG using PRFF Fn 02. 12. 2011 | TU Darmstadt | A. Huelsing | 15

Security Proof - Idea Tree construction and W-OTS are provably secure. Given Adversary A against pseudorandom Scheme can be used against the random scheme. → Inputs are the same Input distribution differs → We can bound success probability against random scheme We can use A to distinguish PRG See full version on iacr eprint (report 2011/484) 02. 12. 2011 | TU Darmstadt | A. Huelsing | 16

XMSS in practice 02. 12. 2011 | TU Darmstadt | A. Huelsing | 17

XMSS - Instantiations Trapdoor oneway function DL RSA MP-Sign Cryptographic HFF Second-preimage resistant HFF Pseudorandom FF XMSS 02. 12. 2011 | TU Darmstadt | A. Huelsing | 18 Block Cipher

Hash functions & Blockciphers AES Blowfish 3 DES Twofish Threefish Serpent IDEA RC 5 RC 6 … 02. 12. 2011 | TU Darmstadt | A. Huelsing | 19 SHA-2 BLAKE Grøstl JH Keccak Skein VSH SWIFFTX RFSB …

XMSS Implementations C Implementation, using Open. SSL Sign (ms) Verify (ms) Signature (bit) Public Key (bit) Secret Key (byte) Bit Security Comment XMSS-SHA-2 15. 17 1. 02 16, 664 13, 568 280 146 H = 20, w = 64 XMSS-SHA-2 33. 47 2. 34 15, 384 13, 568 280 100 H = 20, w = 108 XMSS-AES-NI 1. 72 0. 11 19, 608 7, 296 152 82 H = 20, w=4 XMSS-AES 2. 87 0. 22 19, 608 7, 296 152 82 H = 20, w=4 MSS-SPR (n=128) - - 68, 096 7, 680 - 98 H = 20 RSA 2048 3. 08 0. 09 ≤ 2, 048 ≤ 4, 096 87 Intel(R) Core(TM) i 5 CPU M 540 @ 2. 53 GHz with Intel AES-NI 02. 12. 2011 | TU Darmstadt | A. Huelsing | 20

Conclusion 02. 12. 2011 | TU Darmstadt | A. Huelsing | 21

XMSS … needs minimal security assumptions … is forward secure … can be used with any hash function or block cipher … performance is comparable to RSA, DSA, ECDSA … 02. 12. 2011 | TU Darmstadt | A. Huelsing | 22
- Slides: 22