X 86 Assembly Buffer Overflow III 1 Admin
X 86 Assembly – Buffer Overflow III: 1
Admin ¢ Link to “buffer overflow demo” § http: //nsfsecurity. pr. erau. edu/bom/ ¢ ASM quick-reference from Larry Zhang (thanks!) § http: //www. cs. uaf. edu/2010/fall/cs 301/support/x 86/gcc. html § Need a operand argument summary too? ¢ Best tool (so far) for C and ASM exploration ddd (Linux) § We will use this later in labs too III: 2
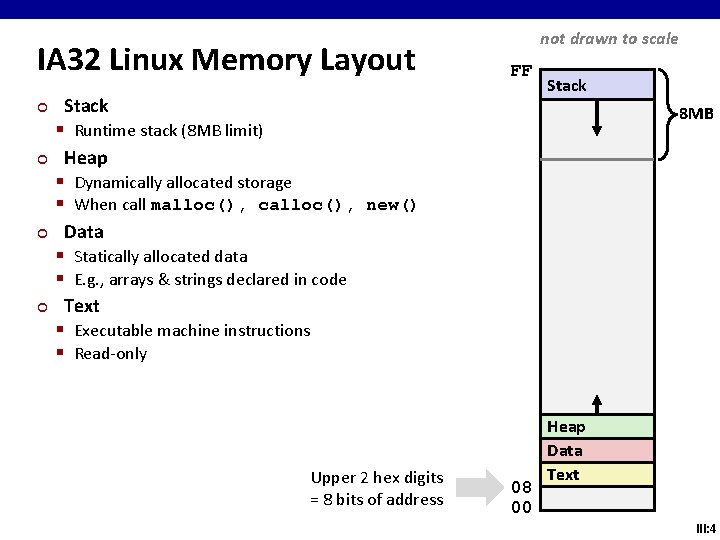
IA 32 Linux Memory Layout ¢ ¢ not drawn to scale FF Stack § Runtime stack (8 MB limit) Heap § Dynamically allocated storage § When call malloc(), calloc(), new() Data § Statically allocated data § E. g. , arrays & strings declared in code Text § Executable machine instructions § Read-only Upper 2 hex digits = 8 bits of address Stack 8 MB 08 00 Heap Data Text III: 4
![Memory Allocation Example not drawn to scale FF Stack char big_array[1<<24]; /* 16 MB Memory Allocation Example not drawn to scale FF Stack char big_array[1<<24]; /* 16 MB](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-4.jpg)
Memory Allocation Example not drawn to scale FF Stack char big_array[1<<24]; /* 16 MB */ char huge_array[1<<28]; /* 256 MB */ int beyond; char *p 1, *p 2, *p 3, *p 4; int useless() { int { p 1 p 2 p 3 p 4 /* } return 0; } main() = malloc(1 Some print <<28); /* << 8); /* statements Where does everything go? 256 256. . . MB B */ */ */ 08 00 Heap Data Text III: 5
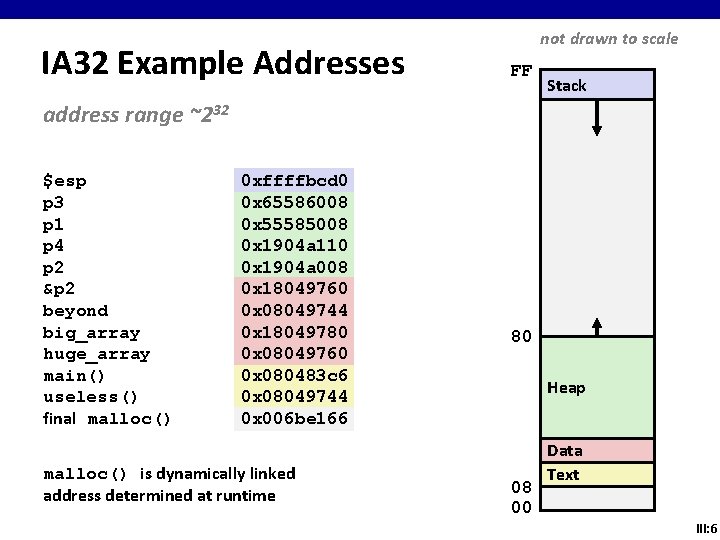
IA 32 Example Addresses not drawn to scale FF Stack address range ~232 $esp p 3 p 1 p 4 p 2 &p 2 beyond big_array huge_array main() useless() final malloc() 0 xffffbcd 0 0 x 65586008 0 x 55585008 0 x 1904 a 110 0 x 1904 a 008 0 x 18049760 0 x 08049744 0 x 18049780 0 x 08049760 0 x 080483 c 6 0 x 08049744 0 x 006 be 166 malloc() is dynamically linked address determined at runtime 80 Heap 08 00 Data Text III: 6
Pointers How about some pointers to deal with the new boss? Sure. Try 0 x 0000 A 4 F 5, 0 x 00008 EEF and 0 x 0000 B 32 A. III: 7
![C operators Operators () [] ->. ! ~ ++ -- + - * & C operators Operators () [] ->. ! ~ ++ -- + - * &](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-7.jpg)
C operators Operators () [] ->. ! ~ ++ -- + - * & (type) sizeof * / % + << >> < <= > >= == != & ^ | && || ? : = += -= *= /= %= &= ^= != <<= >>= , ¢ ¢ ¢ Associativity left to right to left to right left to right left to right to left right to left to right -> has very high precedence () has very high precedence monadic * just below III: 8
![C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13]](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-8.jpg)
C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] p is an array[13] of pointer to int *(p[13]) p is an array[13] of pointer to int **p p is a pointer to an int (*p)[13] p is a pointer to an array[13] of int *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f is a function returning ptr to an array[13] of pointers to functions returning int (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 9
![C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13]](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-9.jpg)
C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] p pisisananarray[13]ofofpointertotointint *(p[13]) p is an array[13] of pointer to int **p p is a pointer to an int (*p)[13] p is a pointer to an array[13] of int *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f is a function returning ptr to an array[13] of pointers to functions returning int (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 10
![C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13]](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-10.jpg)
C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] p pisisananarray[13]ofofpointertotointint *(p[13]) p pisisananarray[13]ofofpointertotointint **p p is a pointer to an int (*p)[13] p is a pointer to an array[13] of int *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f is a function returning ptr to an array[13] of pointers to functions returning int (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 11
![C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13]](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-11.jpg)
C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] p pisisananarray[13]ofofpointertotointint *(p[13]) p pisisananarray[13]ofofpointertotointint **p p is a pointer to an int (*p)[13] p pisisa apointertotoananarray[13]ofofintint *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f is a function returning ptr to an array[13] of pointers to functions returning int (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 12
![C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13]](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-12.jpg)
C Pointer Declarations: Test Yourself! int *p p is a pointer to int *p[13] p pisisananarray[13]ofofpointertotointint *(p[13]) p pisisananarray[13]ofofpointertotointint **p p is a pointer to an int (*p)[13] p pisisa apointertotoananarray[13]ofofintint *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f fisisaafunctionreturningptr ptrtotoan anarray[13] of ofpointerstotofunctionsreturningintint (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 13
![C Pointer Declarations int *p p is a pointer to int *p[13] p is C Pointer Declarations int *p p is a pointer to int *p[13] p is](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-13.jpg)
C Pointer Declarations int *p p is a pointer to int *p[13] p is an array[13] of pointer to int *(p[13]) p is an array[13] of pointer to int **p p is a pointer to an int (*p)[13] p is a pointer to an array[13] of int *f() f is a function returning a pointer to int (*f)() f is a pointer to a function returning int (*(*f())[13])() f is a function returning ptr to an array[13] of pointers to functions returning int (*(*x[3])())[5] x is an array[3] of pointers to functions returning pointers to array[5] of ints III: 14
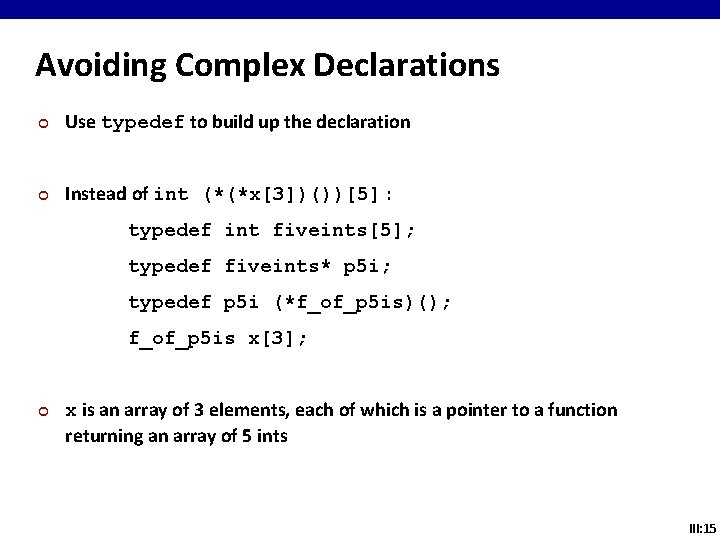
Avoiding Complex Declarations ¢ Use typedef to build up the declaration ¢ Instead of int (*(*x[3])())[5] : typedef int fiveints[5]; typedef fiveints* p 5 i; typedef p 5 i (*f_of_p 5 is)(); f_of_p 5 is x[3]; ¢ x is an array of 3 elements, each of which is a pointer to a function returning an array of 5 ints III: 15
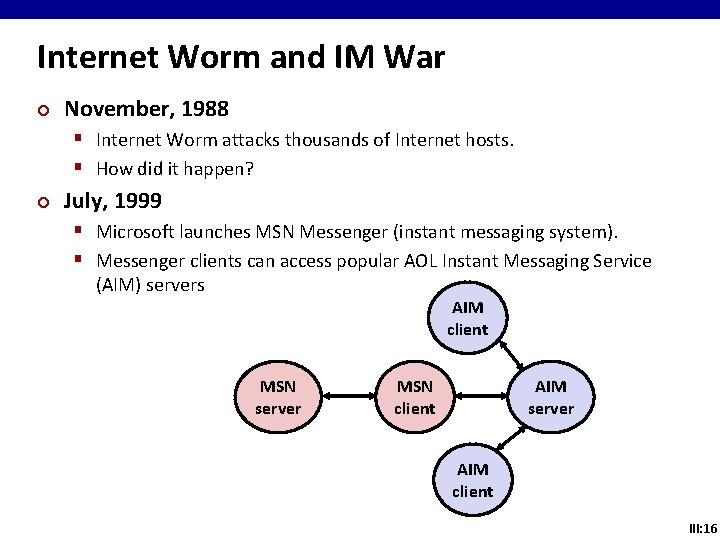
Internet Worm and IM War ¢ November, 1988 § Internet Worm attacks thousands of Internet hosts. § How did it happen? ¢ July, 1999 § Microsoft launches MSN Messenger (instant messaging system). § Messenger clients can access popular AOL Instant Messaging Service (AIM) servers AIM client MSN server MSN client AIM server AIM client III: 16
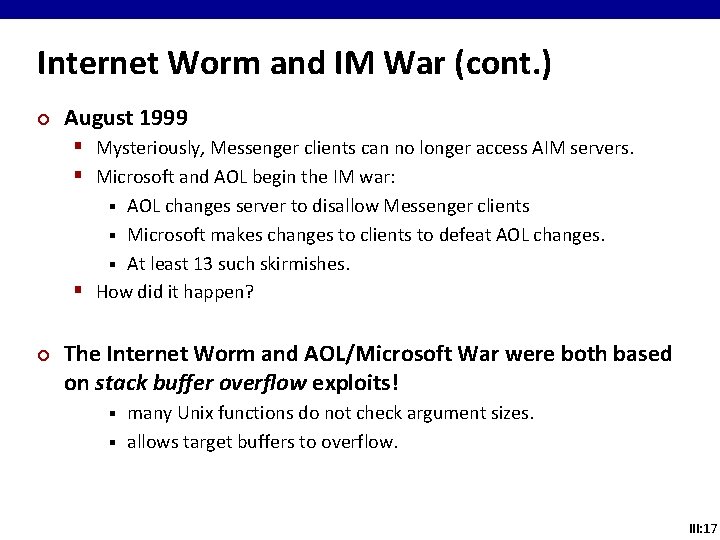
Internet Worm and IM War (cont. ) ¢ August 1999 § Mysteriously, Messenger clients can no longer access AIM servers. § Microsoft and AOL begin the IM war: AOL changes server to disallow Messenger clients § Microsoft makes changes to clients to defeat AOL changes. § At least 13 such skirmishes. § How did it happen? § ¢ The Internet Worm and AOL/Microsoft War were both based on stack buffer overflow exploits! many Unix functions do not check argument sizes. § allows target buffers to overflow. § III: 17
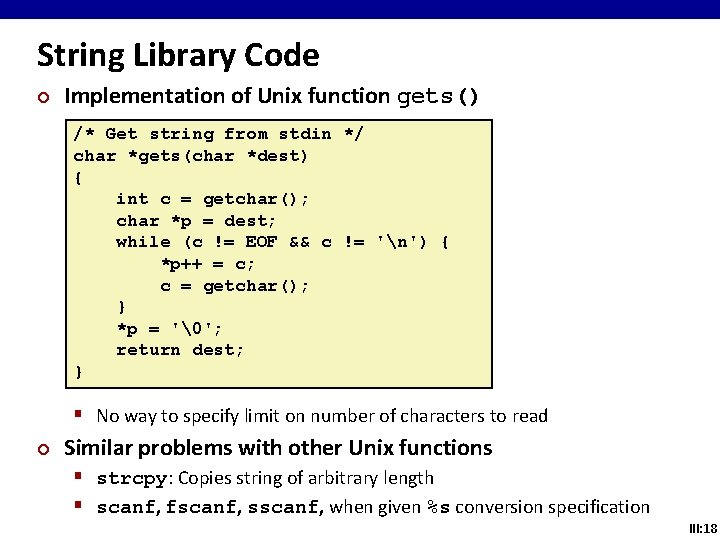
String Library Code ¢ Implementation of Unix function gets() /* Get string from stdin */ char *gets(char *dest) { int c = getchar(); char *p = dest; while (c != EOF && c != 'n') { *p++ = c; c = getchar(); } *p = '�'; return dest; } § No way to specify limit on number of characters to read ¢ Similar problems with other Unix functions § strcpy: Copies string of arbitrary length § scanf, fscanf, sscanf, when given %s conversion specification III: 18
![Vulnerable Buffer Code /* Echo Line */ void echo() { char buf[4]; gets(buf); puts(buf); Vulnerable Buffer Code /* Echo Line */ void echo() { char buf[4]; gets(buf); puts(buf);](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-18.jpg)
Vulnerable Buffer Code /* Echo Line */ void echo() { char buf[4]; gets(buf); puts(buf); } /* Way too small! */ int main() { printf("Type a string: "); echo(); return 0; } unix>. /bufdemo Type a string: 12345678 Segmentation Fault unix>. /bufdemo Type a string: 123456789 ABC Segmentation Fault III: 19
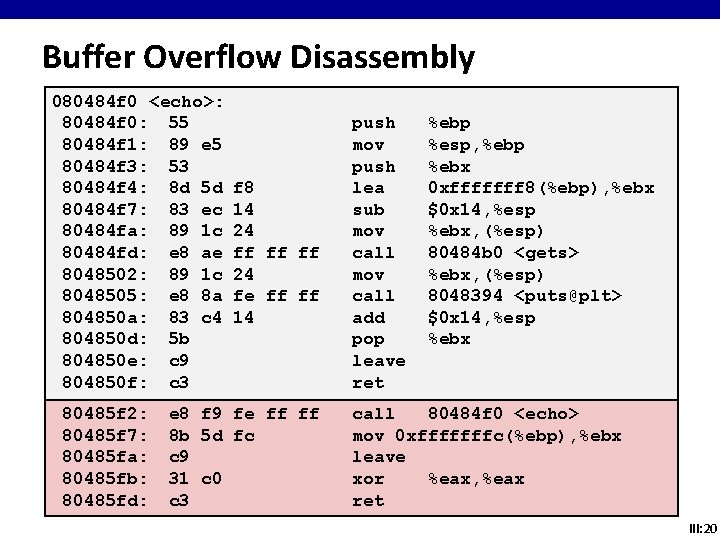
Buffer Overflow Disassembly 080484 f 0 <echo>: 80484 f 0: 55 80484 f 1: 89 e 5 80484 f 3: 53 80484 f 4: 8 d 5 d 80484 f 7: 83 ec 80484 fa: 89 1 c 80484 fd: e 8 ae 8048502: 89 1 c 8048505: e 8 8 a 804850 a: 83 c 4 804850 d: 5 b 804850 e: c 9 804850 f: c 3 80485 f 2: 80485 f 7: 80485 fa: 80485 fb: 80485 fd: f 8 14 24 ff ff ff 24 fe ff ff 14 e 8 f 9 fe ff ff 8 b 5 d fc c 9 31 c 0 c 3 push mov push lea sub mov call add pop leave ret %ebp %esp, %ebp %ebx 0 xfffffff 8(%ebp), %ebx $0 x 14, %esp %ebx, (%esp) 80484 b 0 <gets> %ebx, (%esp) 8048394 <puts@plt> $0 x 14, %esp %ebx call 80484 f 0 <echo> mov 0 xfffffffc(%ebp), %ebx leave xor %eax, %eax ret III: 20
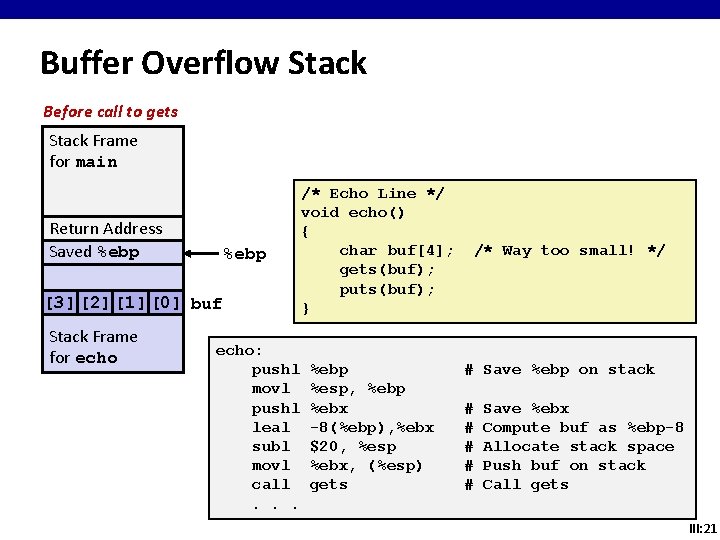
Buffer Overflow Stack Before call to gets Stack Frame for main Return Address Saved %ebp [3] [2] [1] [0] buf Stack Frame for echo: pushl movl pushl leal subl movl call. . . /* Echo Line */ void echo() { char buf[4]; gets(buf); puts(buf); } %ebp %esp, %ebp %ebx -8(%ebp), %ebx $20, %esp %ebx, (%esp) gets /* Way too small! */ # Save %ebp on stack # # # Save %ebx Compute buf as %ebp-8 Allocate stack space Push buf on stack Call gets III: 21
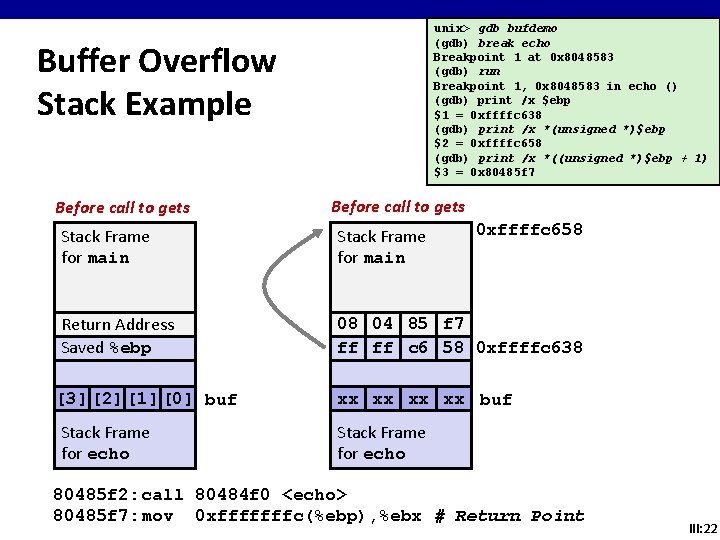
unix> gdb bufdemo (gdb) break echo Breakpoint 1 at 0 x 8048583 (gdb) run Breakpoint 1, 0 x 8048583 in echo () (gdb) print /x $ebp $1 = 0 xffffc 638 (gdb) print /x *(unsigned *)$ebp $2 = 0 xffffc 658 (gdb) print /x *((unsigned *)$ebp + 1) $3 = 0 x 80485 f 7 Buffer Overflow Stack Example Before call to gets 0 xffffc 658 Stack Frame for main Return Address Saved %ebp 08 04 85 f 7 ff ff c 6 58 0 xffffc 638 [3] [2] [1] [0] buf Stack Frame for echo xx xx buf Stack Frame for echo 80485 f 2: call 80484 f 0 <echo> 80485 f 7: mov 0 xfffffffc(%ebp), %ebx # Return Point III: 22
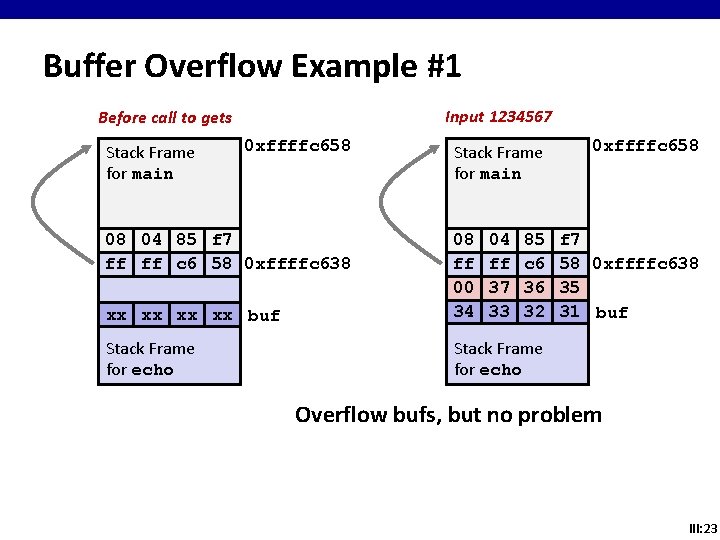
Buffer Overflow Example #1 Input 1234567 Before call to gets Stack Frame for main 0 xffffc 658 08 04 85 f 7 ff ff c 6 58 0 xffffc 638 Stack Frame for main xx xx buf 08 ff 00 34 04 ff 37 33 85 c 6 36 32 Stack Frame for echo 0 xffffc 658 f 7 58 0 xffffc 638 35 31 buf Overflow bufs, but no problem III: 23
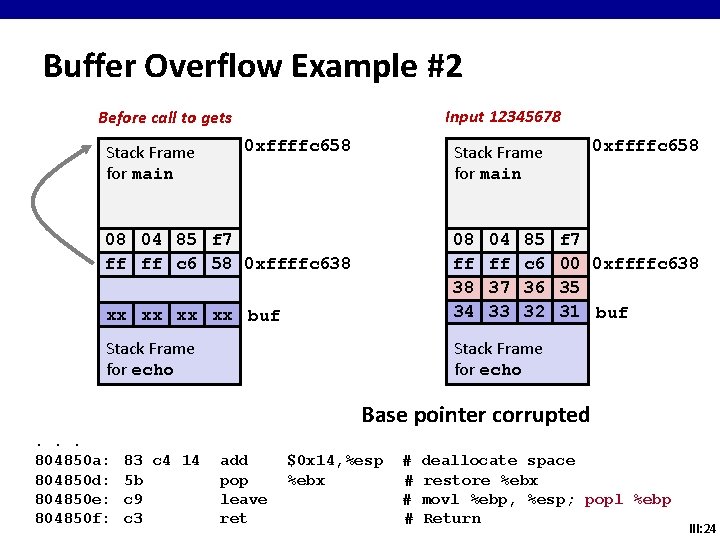
Buffer Overflow Example #2 Input 12345678 Before call to gets Stack Frame for main 0 xffffc 658 Stack Frame for main 08 04 85 f 7 ff ff c 6 58 0 xffffc 638 xx xx buf 08 ff 38 34 04 ff 37 33 85 c 6 36 32 Stack Frame for echo f 7 00 0 xffffc 638 35 31 buf Base pointer corrupted. . . 804850 a: 804850 d: 804850 e: 804850 f: 83 c 4 14 5 b c 9 c 3 add pop leave ret $0 x 14, %esp %ebx # # deallocate space restore %ebx movl %ebp, %esp; popl %ebp Return III: 24
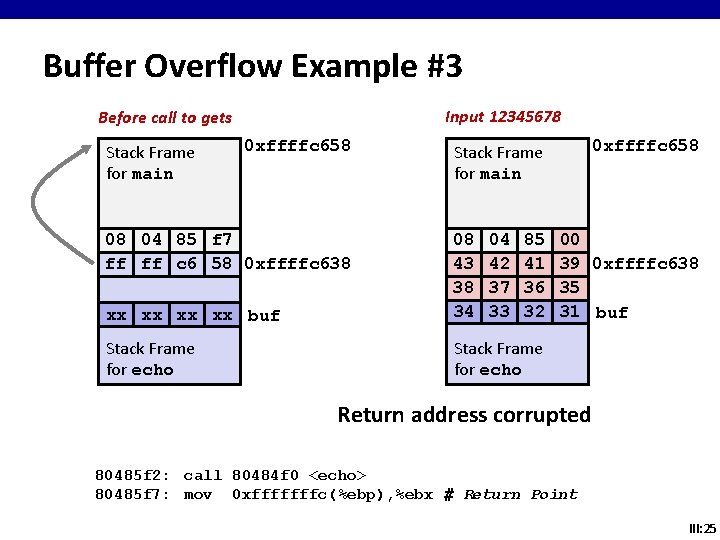
Buffer Overflow Example #3 Input 12345678 Before call to gets Stack Frame for main 0 xffffc 658 08 04 85 f 7 ff ff c 6 58 0 xffffc 638 0 xffffc 658 Stack Frame for main xx xx buf 08 43 38 34 04 42 37 33 85 41 36 32 Stack Frame for echo 00 39 0 xffffc 638 35 31 buf Return address corrupted 80485 f 2: call 80484 f 0 <echo> 80485 f 7: mov 0 xfffffffc(%ebp), %ebx # Return Point III: 25
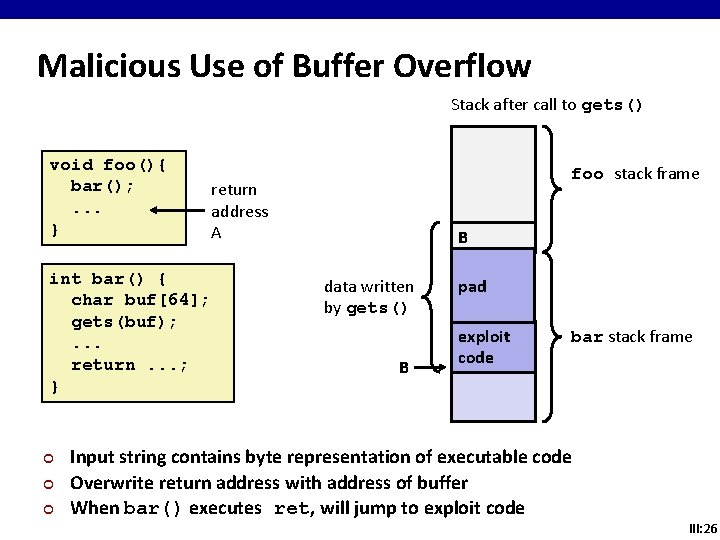
Malicious Use of Buffer Overflow Stack after call to gets() void foo(){ bar(); . . . } int bar() { char buf[64]; gets(buf); . . . return. . . ; } ¢ ¢ ¢ foo stack frame return address A B data written by gets() B pad exploit code bar stack frame Input string contains byte representation of executable code Overwrite return address with address of buffer When bar() executes ret, will jump to exploit code III: 26
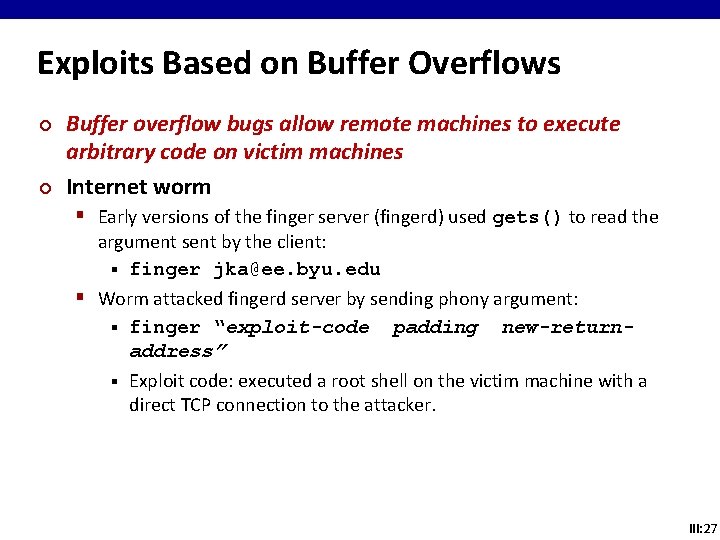
Exploits Based on Buffer Overflows ¢ ¢ Buffer overflow bugs allow remote machines to execute arbitrary code on victim machines Internet worm § Early versions of the finger server (fingerd) used gets() to read the argument sent by the client: § finger jka@ee. byu. edu § Worm attacked fingerd server by sending phony argument: § finger “exploit-code padding new-returnaddress” § Exploit code: executed a root shell on the victim machine with a direct TCP connection to the attacker. III: 27
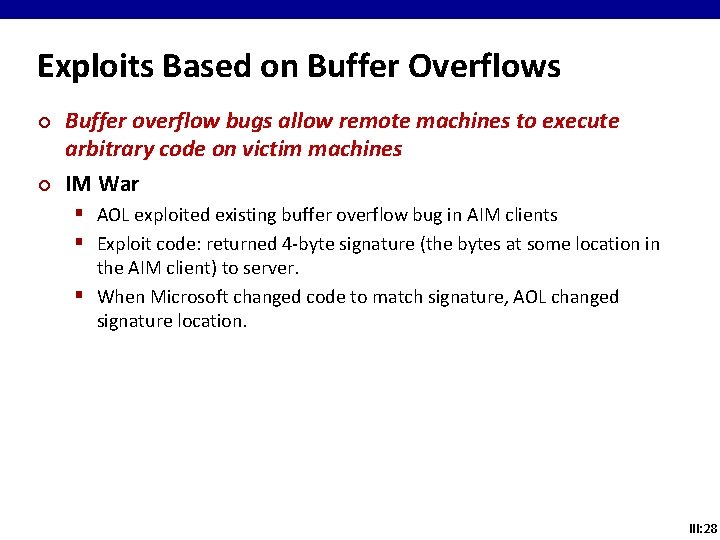
Exploits Based on Buffer Overflows ¢ ¢ Buffer overflow bugs allow remote machines to execute arbitrary code on victim machines IM War § AOL exploited existing buffer overflow bug in AIM clients § Exploit code: returned 4 -byte signature (the bytes at some location in the AIM client) to server. § When Microsoft changed code to match signature, AOL changed signature location. III: 28
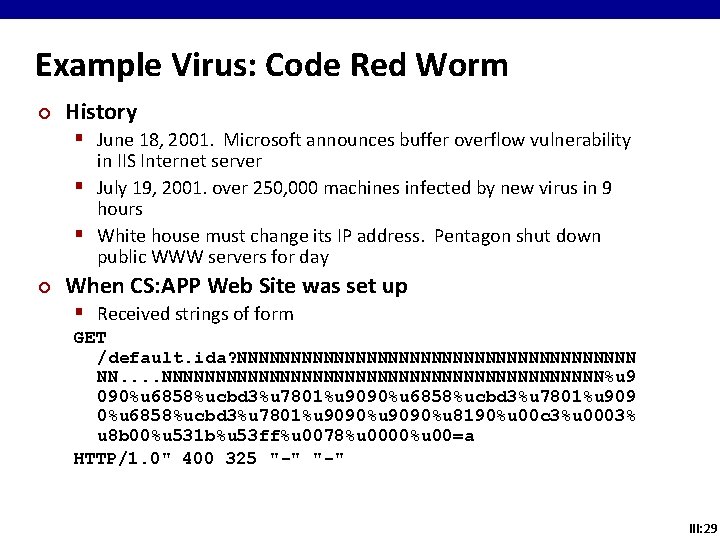
Example Virus: Code Red Worm ¢ History § June 18, 2001. Microsoft announces buffer overflow vulnerability in IIS Internet server § July 19, 2001. over 250, 000 machines infected by new virus in 9 hours § White house must change its IP address. Pentagon shut down public WWW servers for day ¢ When CS: APP Web Site was set up § Received strings of form GET /default. ida? NNNNNNNNNNNNNNNNNNN NN. . NNNNNNNNNNNNNNNNNNNNN%u 9 090%u 6858%ucbd 3%u 7801%u 9090%u 8190%u 00 c 3%u 0003% u 8 b 00%u 531 b%u 53 ff%u 0078%u 0000%u 00=a HTTP/1. 0" 400 325 "-" III: 29
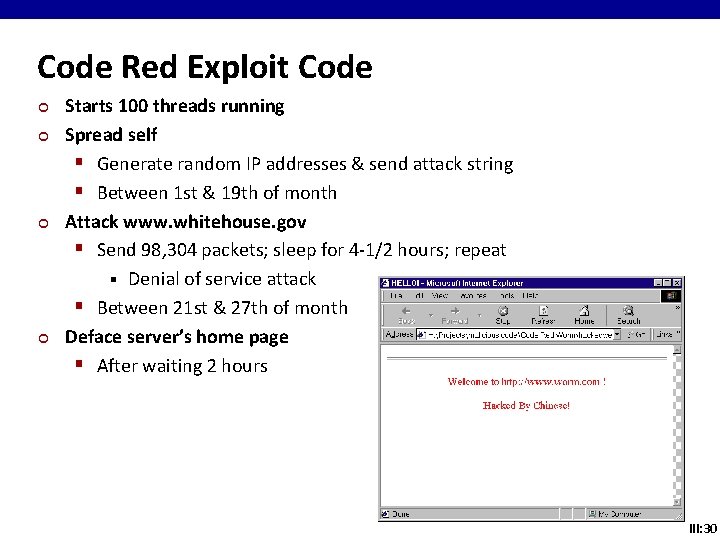
Code Red Exploit Code ¢ ¢ Starts 100 threads running Spread self § Generate random IP addresses & send attack string § Between 1 st & 19 th of month Attack www. whitehouse. gov § Send 98, 304 packets; sleep for 4 -1/2 hours; repeat § Denial of service attack § Between 21 st & 27 th of month Deface server’s home page § After waiting 2 hours III: 30
![Avoiding Overflow Vulnerability /* Echo Line */ void echo() { char buf[4]; /* Way Avoiding Overflow Vulnerability /* Echo Line */ void echo() { char buf[4]; /* Way](http://slidetodoc.com/presentation_image/310d049256aeb2d166a4c69eab2c09d8/image-30.jpg)
Avoiding Overflow Vulnerability /* Echo Line */ void echo() { char buf[4]; /* Way too small! */ fgets(buf, 4, stdin); puts(buf); } ¢ Use library routines that limit string lengths § fgets instead of gets § strncpy instead of strcpy § Don’t use scanf with %s conversion specification Use fgets to read the string § Or use %ns where n is a suitable integer § III: 31
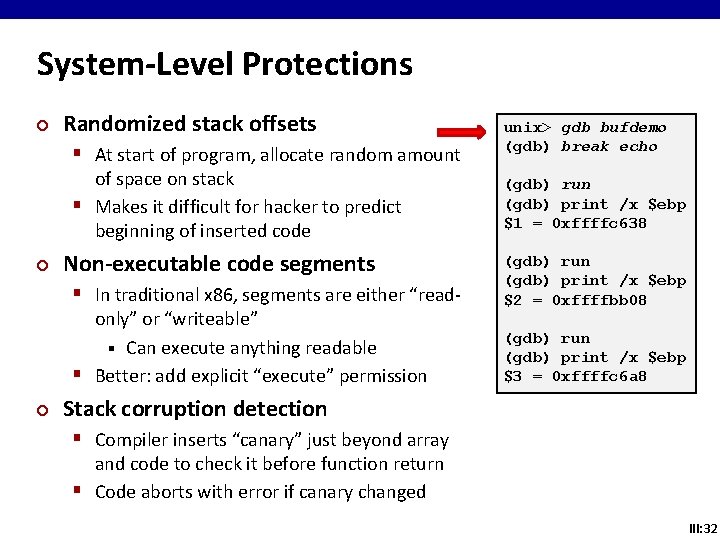
System-Level Protections ¢ Randomized stack offsets § At start of program, allocate random amount of space on stack § Makes it difficult for hacker to predict beginning of inserted code ¢ Non-executable code segments § In traditional x 86, segments are either “readonly” or “writeable” § Can execute anything readable § Better: add explicit “execute” permission ¢ unix> gdb bufdemo (gdb) break echo (gdb) run (gdb) print /x $ebp $1 = 0 xffffc 638 (gdb) run (gdb) print /x $ebp $2 = 0 xffffbb 08 (gdb) run (gdb) print /x $ebp $3 = 0 xffffc 6 a 8 Stack corruption detection § Compiler inserts “canary” just beyond array and code to check it before function return § Code aborts with error if canary changed III: 32
Web-aside: Assembly & C ¢ Requirements to have asm + C integrated together? § In assembly, follow register usage, parameter passing, and return value conventions ¢ Problems with inline assembly § Not portable § Knowing what registers are safe to use ¢ Advantages of GCC’s extended asm § You inform compiler of source values required, results your code generates, and registers that will be overwritten § GCC generates code to correctly set up source values, execute desired instructions, and correctly use computed results III: 33
BONUS SLIDES III: 34
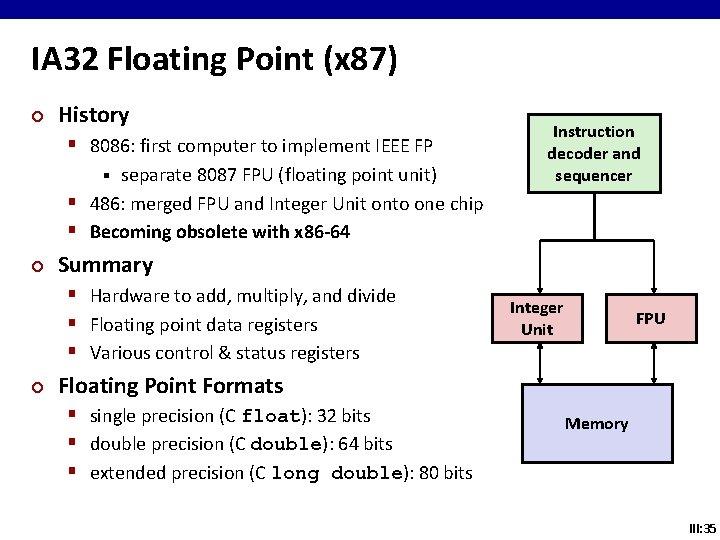
IA 32 Floating Point (x 87) ¢ History § 8086: first computer to implement IEEE FP separate 8087 FPU (floating point unit) § 486: merged FPU and Integer Unit onto one chip § Becoming obsolete with x 86 -64 § ¢ Summary § Hardware to add, multiply, and divide § Floating point data registers § Various control & status registers ¢ Instruction decoder and sequencer Integer Unit FPU Floating Point Formats § single precision (C float): 32 bits § double precision (C double): 64 bits § extended precision (C long double): 80 bits Memory III: 35
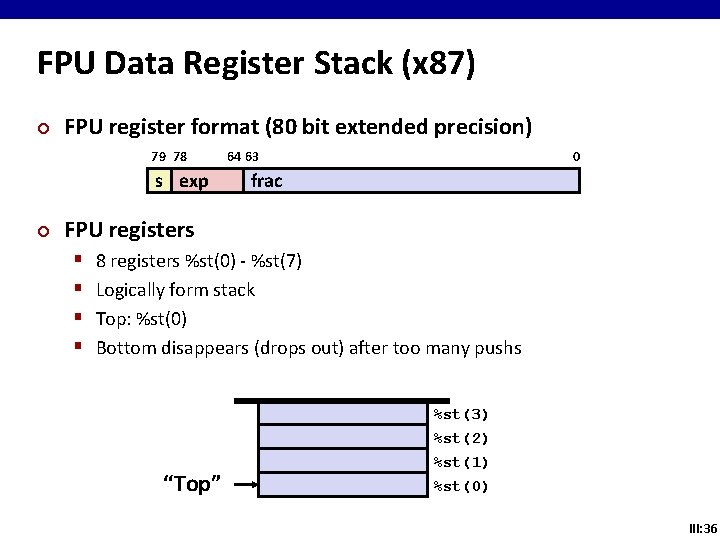
FPU Data Register Stack (x 87) ¢ FPU register format (80 bit extended precision) 79 78 s exp ¢ 0 64 63 frac FPU registers § § 8 registers %st(0) - %st(7) Logically form stack Top: %st(0) Bottom disappears (drops out) after too many pushs “Top” %st(3) %st(2) %st(1) %st(0) III: 36
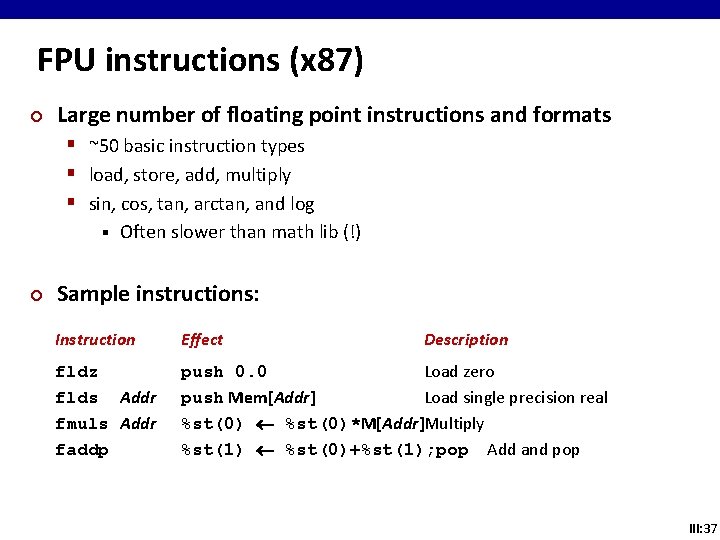
FPU instructions (x 87) ¢ Large number of floating point instructions and formats § ~50 basic instruction types § load, store, add, multiply § sin, cos, tan, arctan, and log § ¢ Often slower than math lib (!) Sample instructions: Instruction Effect Description fldz flds Addr fmuls Addr faddp push 0. 0 Load zero push Mem[Addr] Load single precision real %st(0)*M[Addr]Multiply %st(1) %st(0)+%st(1); pop Add and pop III: 37
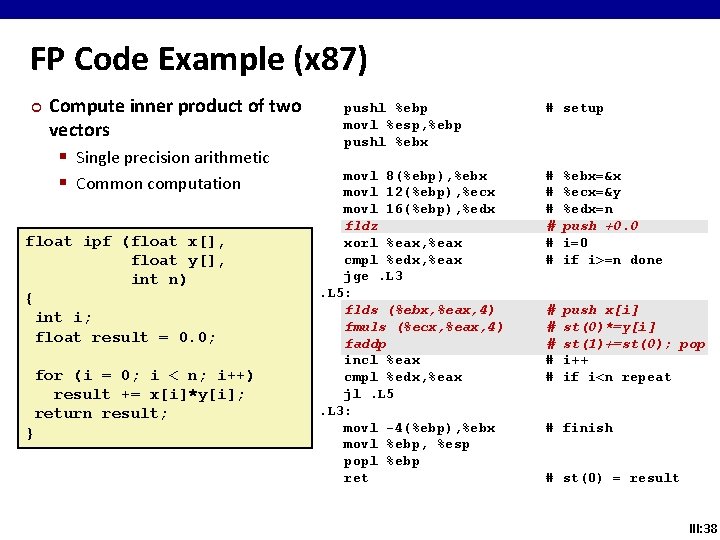
FP Code Example (x 87) ¢ Compute inner product of two vectors § Single precision arithmetic § Common computation float ipf (float x[], float y[], int n) { int i; float result = 0. 0; for (i = 0; i < n; i++) result += x[i]*y[i]; return result; } pushl %ebp movl %esp, %ebp pushl %ebx movl 8(%ebp), %ebx movl 12(%ebp), %ecx movl 16(%ebp), %edx fldz xorl %eax, %eax cmpl %edx, %eax jge. L 3. L 5: flds (%ebx, %eax, 4) fmuls (%ecx, %eax, 4) faddp incl %eax cmpl %edx, %eax jl. L 5. L 3: movl -4(%ebp), %ebx movl %ebp, %esp popl %ebp ret # setup # # # %ebx=&x %ecx=&y %edx=n push +0. 0 i=0 if i>=n done # # # push x[i] st(0)*=y[i] st(1)+=st(0); pop i++ if i<n repeat # finish # st(0) = result III: 38
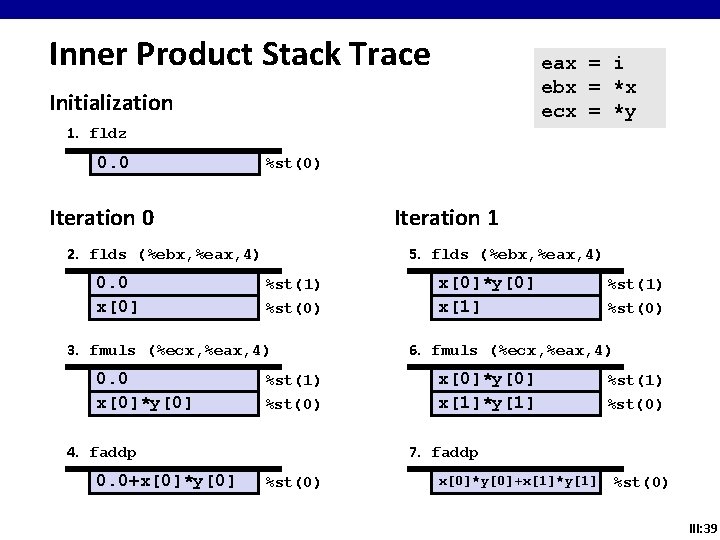
Inner Product Stack Trace eax = i ebx = *x ecx = *y Initialization 1. fldz 0. 0 %st(0) Iteration 0 Iteration 1 2. flds (%ebx, %eax, 4) 0. 0 x[0] 5. flds (%ebx, %eax, 4) %st(1) %st(0) 3. fmuls (%ecx, %eax, 4) 0. 0 x[0]*y[0] %st(1) %st(0) 4. faddp 0. 0+x[0]*y[0] x[1] %st(1) %st(0) 6. fmuls (%ecx, %eax, 4) x[0]*y[0] x[1]*y[1] %st(1) %st(0) 7. faddp %st(0) x[0]*y[0]+x[1]*y[1] %st(0) III: 39
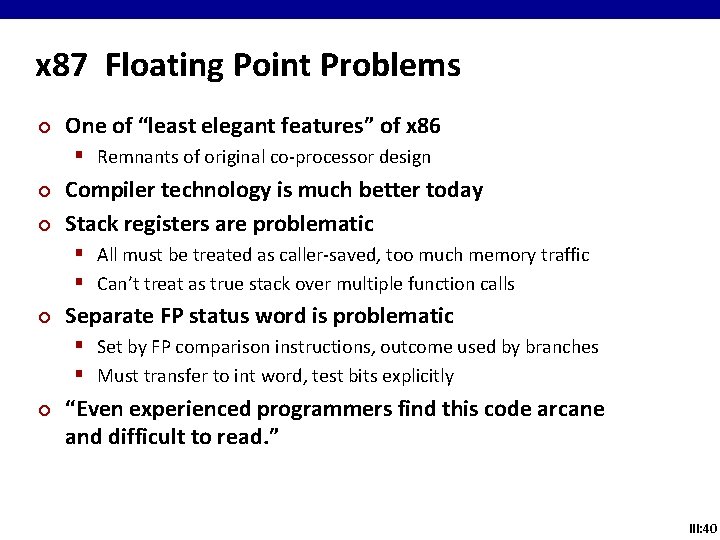
x 87 Floating Point Problems ¢ One of “least elegant features” of x 86 § Remnants of original co-processor design ¢ ¢ Compiler technology is much better today Stack registers are problematic § All must be treated as caller-saved, too much memory traffic § Can’t treat as true stack over multiple function calls ¢ Separate FP status word is problematic § Set by FP comparison instructions, outcome used by branches § Must transfer to int word, test bits explicitly ¢ “Even experienced programmers find this code arcane and difficult to read. ” III: 40
SSE Floating Point Architecture ¢ ¢ Better compiler target than x 87 Includes new registers and instructions In Intel CPUs since Pentium III Default for x 86 -64, but not IA 32 III: 41
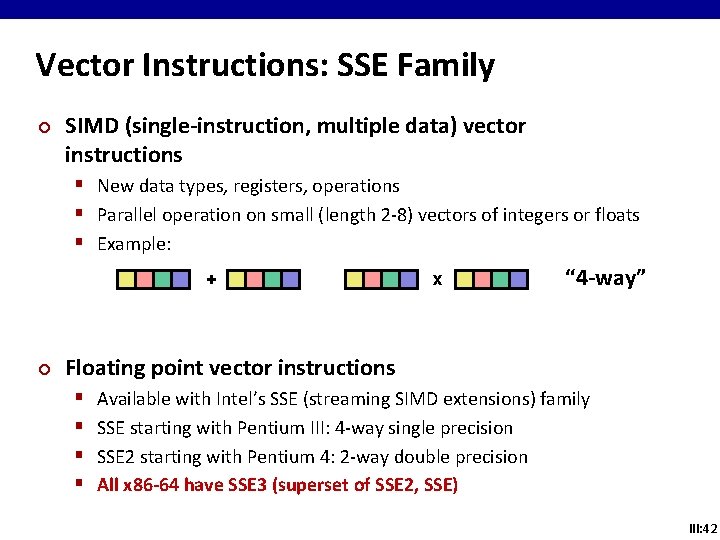
Vector Instructions: SSE Family ¢ SIMD (single-instruction, multiple data) vector instructions § New data types, registers, operations § Parallel operation on small (length 2 -8) vectors of integers or floats § Example: + ¢ x “ 4 -way” Floating point vector instructions § § Available with Intel’s SSE (streaming SIMD extensions) family SSE starting with Pentium III: 4 -way single precision SSE 2 starting with Pentium 4: 2 -way double precision All x 86 -64 have SSE 3 (superset of SSE 2, SSE) III: 42
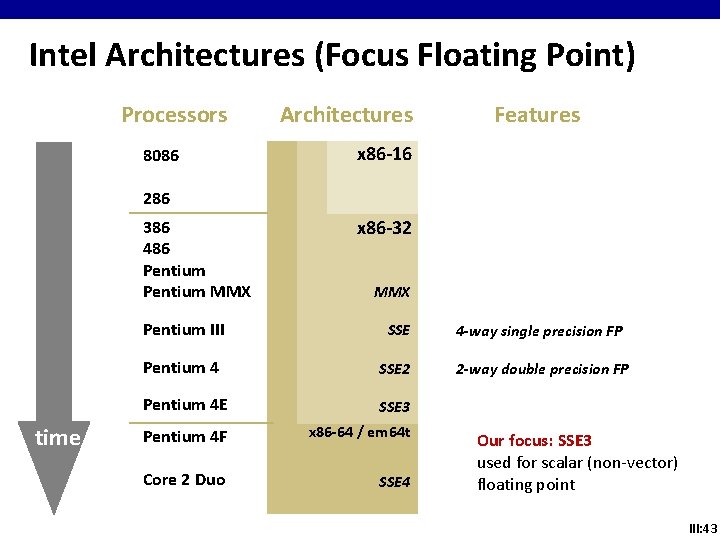
Intel Architectures (Focus Floating Point) Processors 8086 Architectures Features x 86 -16 286 386 486 Pentium MMX time x 86 -32 MMX Pentium III SSE 4 -way single precision FP Pentium 4 SSE 2 2 -way double precision FP Pentium 4 E SSE 3 Pentium 4 F x 86 -64 / em 64 t Core 2 Duo SSE 4 Our focus: SSE 3 used for scalar (non-vector) floating point III: 43
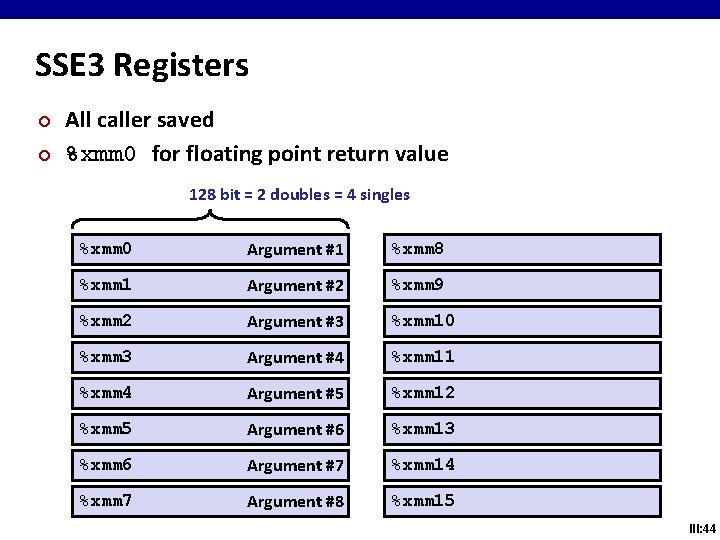
SSE 3 Registers ¢ ¢ All caller saved %xmm 0 for floating point return value 128 bit = 2 doubles = 4 singles %xmm 0 Argument #1 %xmm 8 %xmm 1 Argument #2 %xmm 9 %xmm 2 Argument #3 %xmm 10 %xmm 3 Argument #4 %xmm 11 %xmm 4 Argument #5 %xmm 12 %xmm 5 Argument #6 %xmm 13 %xmm 6 Argument #7 %xmm 14 %xmm 7 Argument #8 %xmm 15 III: 44
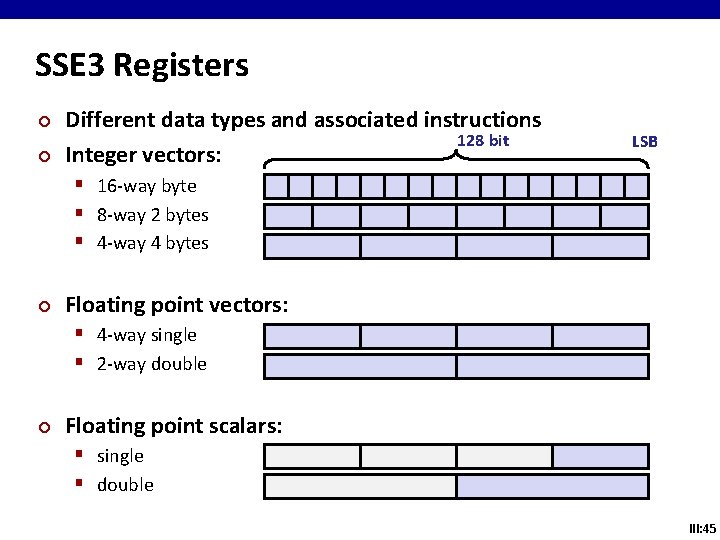
SSE 3 Registers ¢ ¢ Different data types and associated instructions 128 bit Integer vectors: LSB § 16 -way byte § 8 -way 2 bytes § 4 -way 4 bytes ¢ Floating point vectors: § 4 -way single § 2 -way double ¢ Floating point scalars: § single § double III: 45
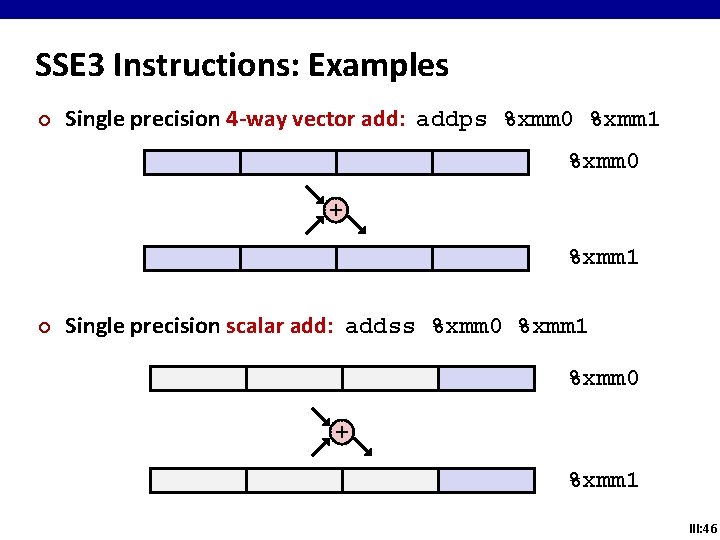
SSE 3 Instructions: Examples ¢ Single precision 4 -way vector add: addps %xmm 0 %xmm 1 %xmm 0 + %xmm 1 ¢ Single precision scalar add: addss %xmm 0 %xmm 1 %xmm 0 + %xmm 1 III: 46
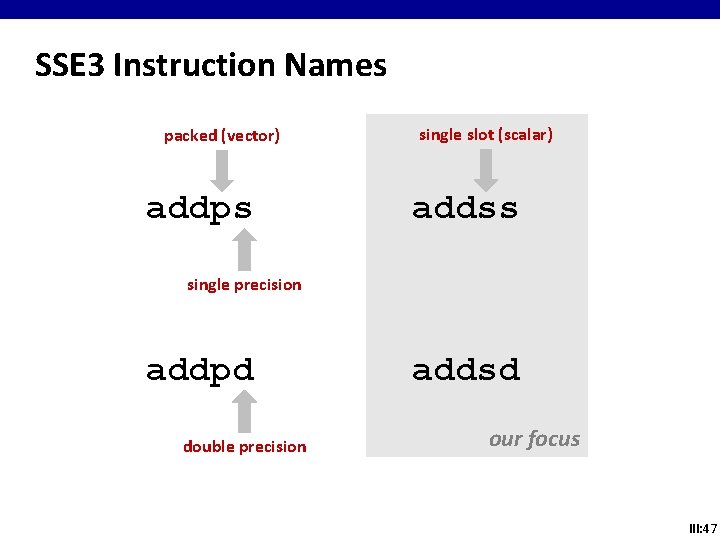
SSE 3 Instruction Names packed (vector) addps single slot (scalar) addss single precision addpd double precision addsd our focus III: 47
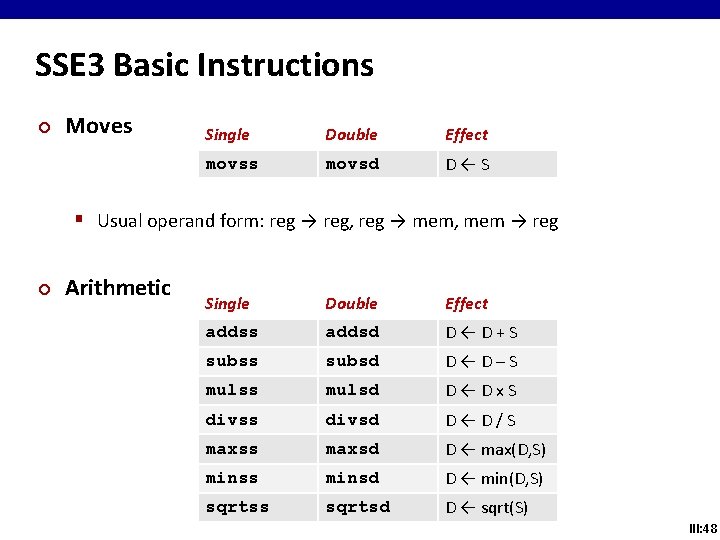
SSE 3 Basic Instructions ¢ Moves Single Double Effect movss movsd D←S § Usual operand form: reg → reg, reg → mem, mem → reg ¢ Arithmetic Single Double Effect addss addsd D←D+S subss subsd D←D–S mulss mulsd D←Dx. S divss divsd D←D/S maxss maxsd D ← max(D, S) minss minsd D ← min(D, S) sqrtss sqrtsd D ← sqrt(S) III: 48
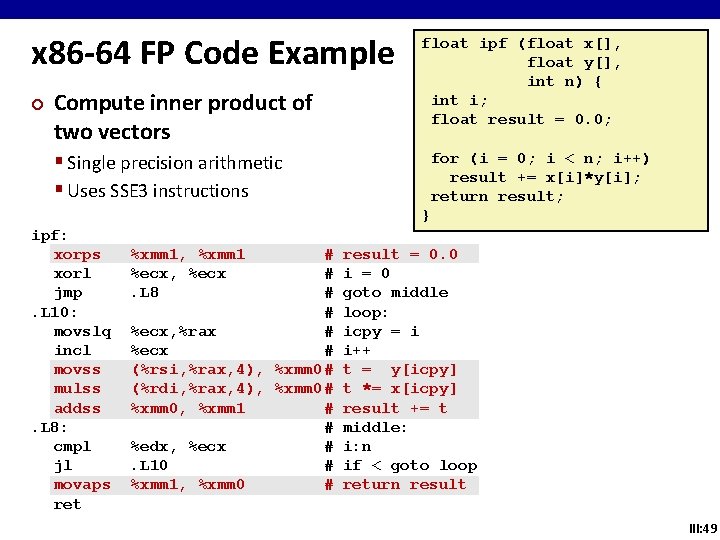
x 86 -64 FP Code Example ¢ Compute inner product of two vectors float ipf (float x[], float y[], int n) { int i; float result = 0. 0; § Single precision arithmetic § Uses SSE 3 instructions for (i = 0; i < n; i++) result += x[i]*y[i]; return result; } ipf: xorps xorl jmp. L 10: movslq incl movss mulss addss. L 8: cmpl jl movaps ret %xmm 1, %xmm 1 %ecx, %ecx. L 8 # # %ecx, %rax # %ecx # (%rsi, %rax, 4), %xmm 0# (%rdi, %rax, 4), %xmm 0# %xmm 0, %xmm 1 # # %edx, %ecx #. L 10 # %xmm 1, %xmm 0 # result = 0. 0 i = 0 goto middle loop: icpy = i i++ t = y[icpy] t *= x[icpy] result += t middle: i: n if < goto loop return result III: 49
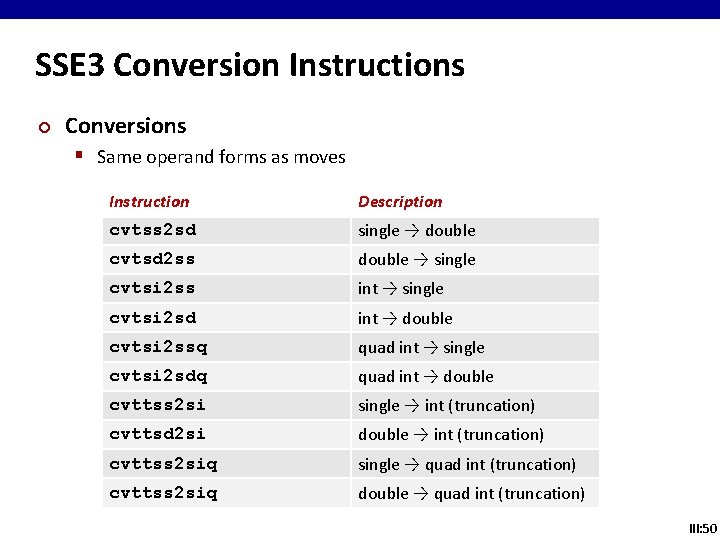
SSE 3 Conversion Instructions ¢ Conversions § Same operand forms as moves Instruction Description cvtss 2 sd single → double cvtsd 2 ss double → single cvtsi 2 ss int → single cvtsi 2 sd int → double cvtsi 2 ssq quad int → single cvtsi 2 sdq quad int → double cvttss 2 si single → int (truncation) cvttsd 2 si double → int (truncation) cvttss 2 siq single → quad int (truncation) cvttss 2 siq double → quad int (truncation) III: 50
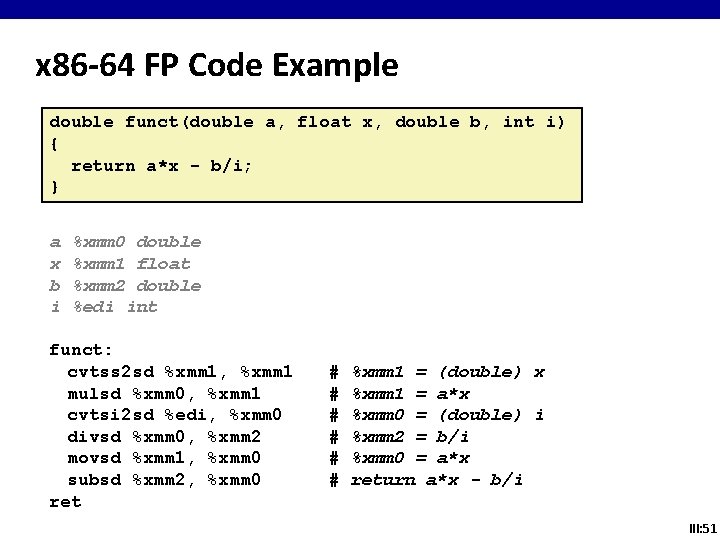
x 86 -64 FP Code Example double funct(double a, float x, double b, int i) { return a*x - b/i; } a x b i %xmm 0 double %xmm 1 float %xmm 2 double %edi int funct: cvtss 2 sd %xmm 1, %xmm 1 mulsd %xmm 0, %xmm 1 cvtsi 2 sd %edi, %xmm 0 divsd %xmm 0, %xmm 2 movsd %xmm 1, %xmm 0 subsd %xmm 2, %xmm 0 ret # # # %xmm 1 = (double) x %xmm 1 = a*x %xmm 0 = (double) i %xmm 2 = b/i %xmm 0 = a*x return a*x - b/i III: 51
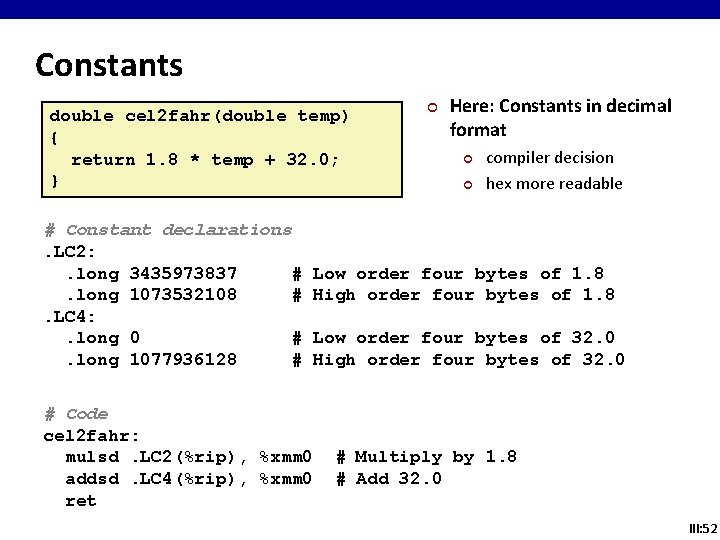
Constants double cel 2 fahr(double temp) { return 1. 8 * temp + 32. 0; } # Constant declarations. LC 2: . long 3435973837 #. long 1073532108 #. LC 4: . long 0 #. long 1077936128 # ¢ Here: Constants in decimal format ¢ ¢ compiler decision hex more readable Low order four bytes of 1. 8 High order four bytes of 1. 8 Low order four bytes of 32. 0 High order four bytes of 32. 0 # Code cel 2 fahr: mulsd. LC 2(%rip), %xmm 0 addsd. LC 4(%rip), %xmm 0 ret # Multiply by 1. 8 # Add 32. 0 III: 52
Comments ¢ SSE 3 floating point § Uses lower ½ (double) or ¼ (single) of vector § Finally departure from awkward x 87 § Assembly very similar to integer code ¢ x 87 still supported § Even mixing with SSE 3 possible § Not recommended ¢ For highest floating point performance § Vectorization a must (but not in this course ) § See next slide III: 53
Vector Instructions ¢ Starting with version 4. 1. 1, GCC can auto-vectorize to some extent § § ¢ -O 3 or –ftree-vectorize No speed-up guaranteed – limited capability Intel’s C++ compiler (icc) currently much better Spice machines have 4. 1. 2 installed (May 2010) For highest performance vectorize yourself using intrinsics § Intrinsics = C interface to vector instructions ¢ Future § Intel AVX announced: 4 -way double, 8 -way single III: 54
- Slides: 53