Wrapup Overview First half Last half First half

- Slides: 18

Wrapup
Overview First half Last half
First half
First Half • Shells ▫ ▫ ▫ What is a shell and what does it do Most popular shells Redirection shell variables environment export and environment
First Half • Utilities and Filters ▫ ▫ ▫ What are filters and why to use them Filter examples (tail, diff, etc) Basics of regular expressions grep sed
First Half • Scripting ▫ Centered on BASH ▫ Basic operators �(conditionals, if, test, case, for, while, here docs, trap, signals, etc)
First half • NTP ▫ Centralized clock ▫ Many networked programs need a synchronized clock • Syslog ▫ Need a common clock when monitoring errors on a network
First half • SSH • DNS ▫ DNSSec • Distributed File Systems ▫ ▫ NFS SMB SAN NAS • RAID
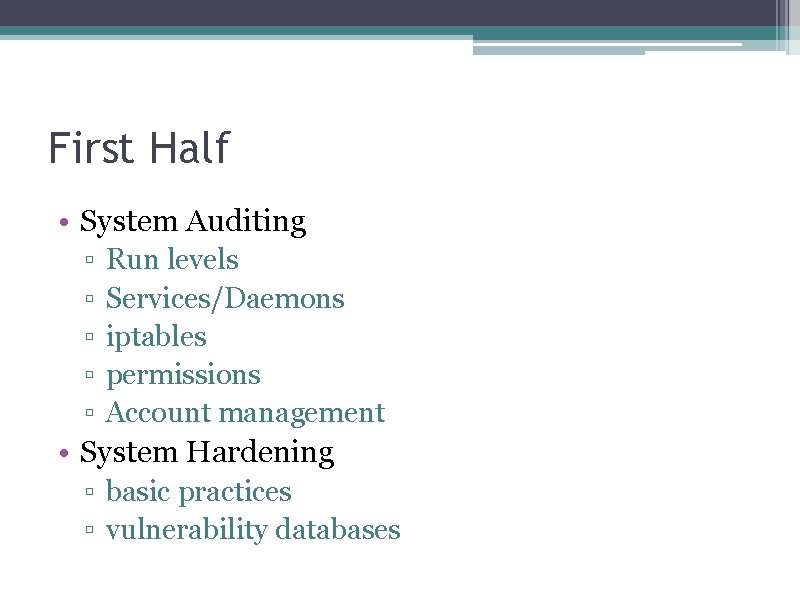
First Half • System Auditing ▫ ▫ ▫ Run levels Services/Daemons iptables permissions Account management • System Hardening ▫ basic practices ▫ vulnerability databases
Last Half
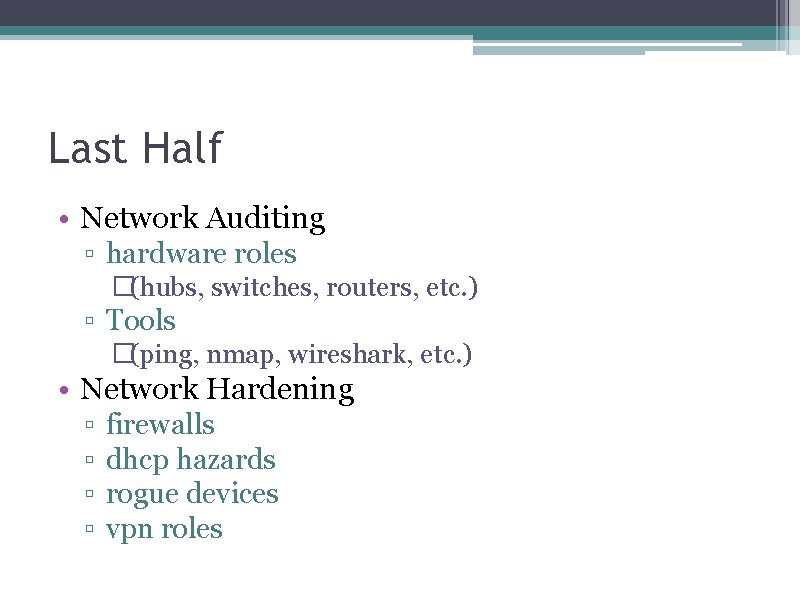
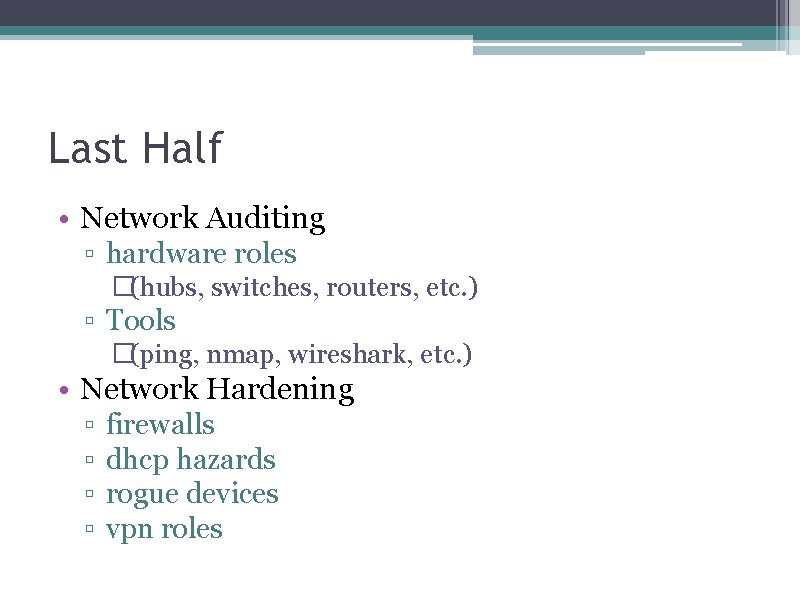
Last Half • Network Auditing ▫ hardware roles �(hubs, switches, routers, etc. ) ▫ Tools �(ping, nmap, wireshark, etc. ) • Network Hardening ▫ ▫ firewalls dhcp hazards rogue devices vpn roles
Last half • Wireless I and II
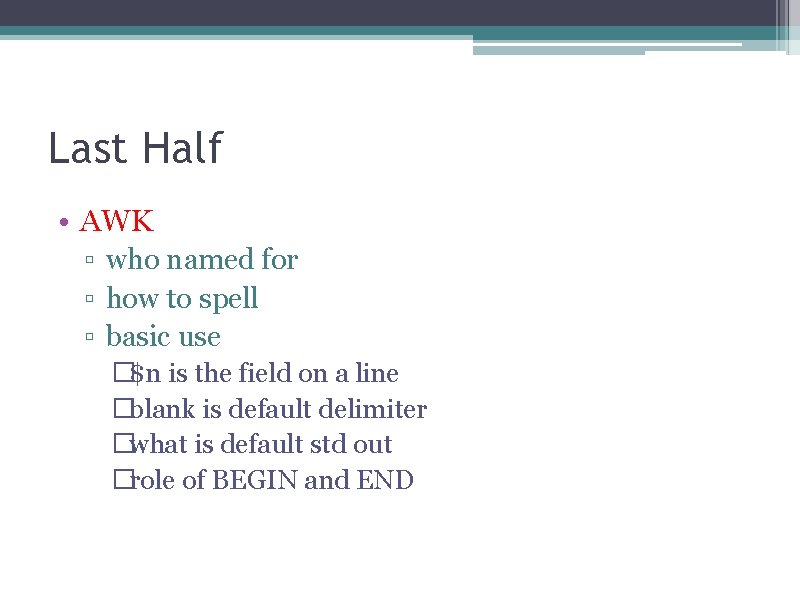
Last Half • AWK ▫ who named for ▫ how to spell ▫ basic use �$n is the field on a line �blank is default delimiter �what is default std out �role of BEGIN and END
Last half • User Management ▫ Keberos • LDAP ▫ Good as standalone ▫ Better when teamed with another product • e. Mail ▫ TLS ▫ SPF �Verifies a domains valid mail servers �Does not validate content
Last Half • Replication ▫ Types: �Primary/backup �Master/Slave �Multi-master • Load Balancing ▫ What is it �Round Robin �Reverse Proxies ▫ Differences ▫ How to do
Last Half • System Administration ▫ sudo ▫ special attributes �(suid, guid, sticky bit) ▫ booting basics ▫ ▫ �init device files file systems tar, compress, gzip and zip package management �Why?
Last Half • SNMP ▫ basics of protocol ▫ security concerns �Most common version �Most secure version
Last Half • Configuration Management ▫ What is supposed to be on the systems ▫ What IS on the systems • Security Policies ▫ Procedures ▫ Objectives �Confidentiality �Integrity �Availability