Workshop Administrasi Jaringan TELNET SSH Ferry Isbat Iwan

Workshop Administrasi Jaringan TELNET &SSH Ferry, Isbat, Iwan Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2000
OBJECTIVES: q To introduce the TELNET protocol and show it implements local and remote login. q To discuss options and sub-options used in TELNET and how they are negotiated. q To define out-of-band signaling in TELNET. q To define different modes of operations in TELNET. q To introduce SSH as an alternative to TELNET. q To show different components of SSH are combined to provide a secure connection over an insecure TCP connection. q To discuss port-forwarding in SSH and how it can be used to provide security for other applications. TCP/IP Protocol Suite 2
20 -1 TELNET is an abbreviation for TErmina. L NETwork. It is the standard TCP/IP protocol for virtual terminal service as proposed by ISO. TELNET enables the establishment of a connection to a remote system in such a way that the local terminal appears to be a terminal at the remote system. 3
Topics Discussed in the Section ü Concepts ü Time-Sharing Environment ü Network Virtual Terminal (NVT) ü Embedding ü Options and Suboption Negotiation ü Controlling the Server ü Out-of-Band Signaling ü Escape Character ü Modes of Operation ü User Interface ü Security Issue TCP/IP Protocol Suite 4
Note TELNET is a general-purpose client-server application program. TCP/IP Protocol Suite 5
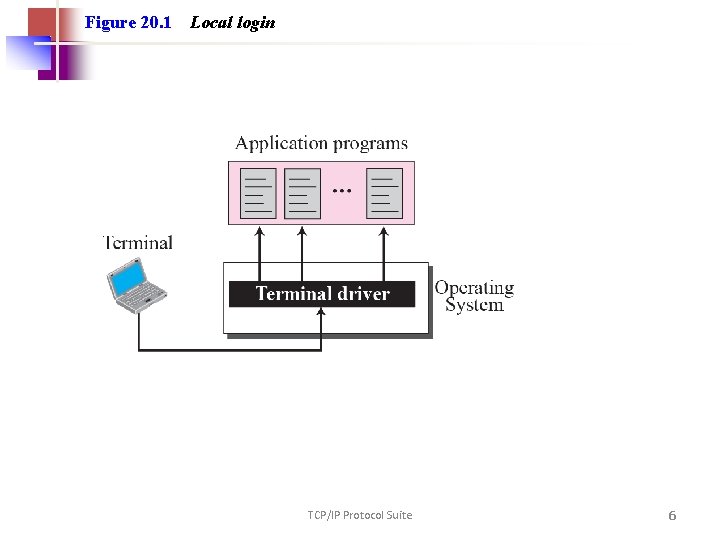
Figure 20. 1 Local login TCP/IP Protocol Suite 6
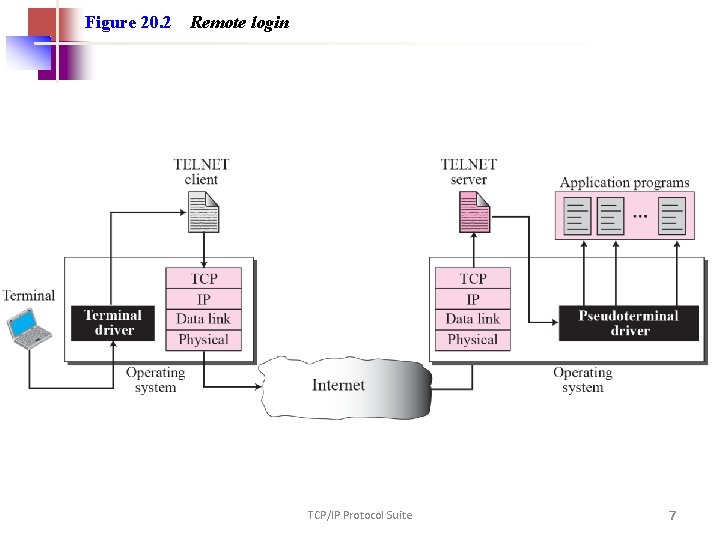
Figure 20. 2 Remote login TCP/IP Protocol Suite 7
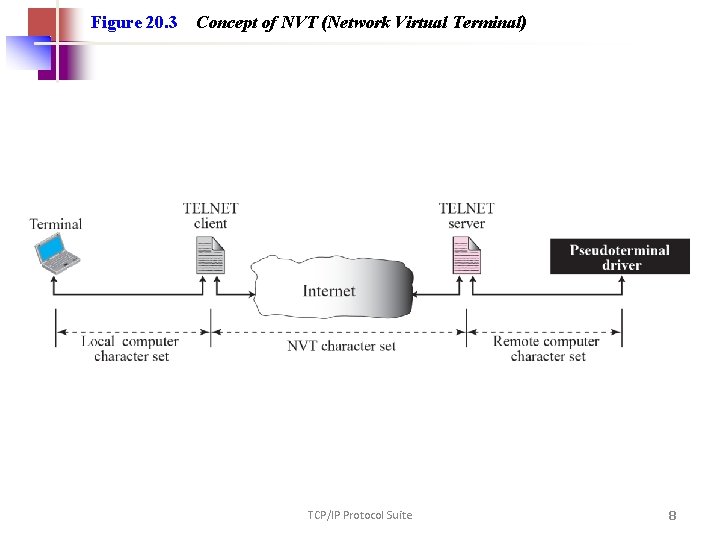
Figure 20. 3 Concept of NVT (Network Virtual Terminal) TCP/IP Protocol Suite 8
20 -2 SECURE SHELL (SSH) Another popular remote login application program is Secure Shell (SSH). SSH, like TELNET, uses TCP as the underlying transport protocol, but SSH is more secure and provides more services than TELNET. TCP/IP Protocol Suite 9
Topics Discussed in the Section ü Versions ü Components ü Port Forwarding ü Format of the SSH Packet TCP/IP Protocol Suite 10
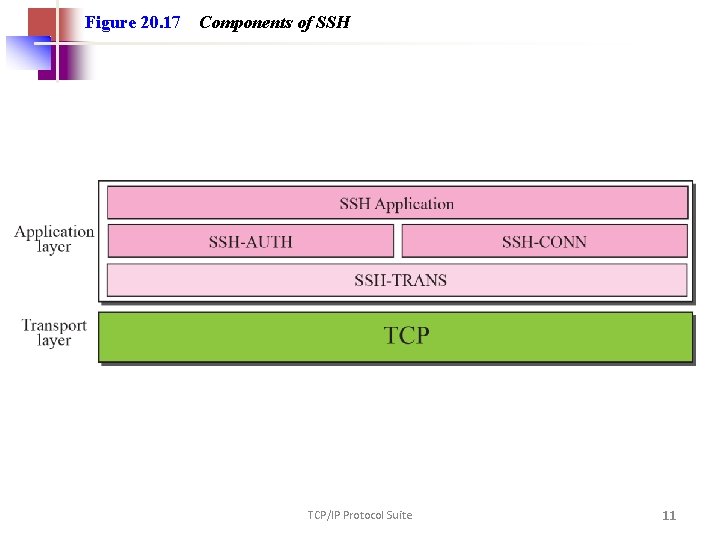
Figure 20. 17 Components of SSH TCP/IP Protocol Suite 11
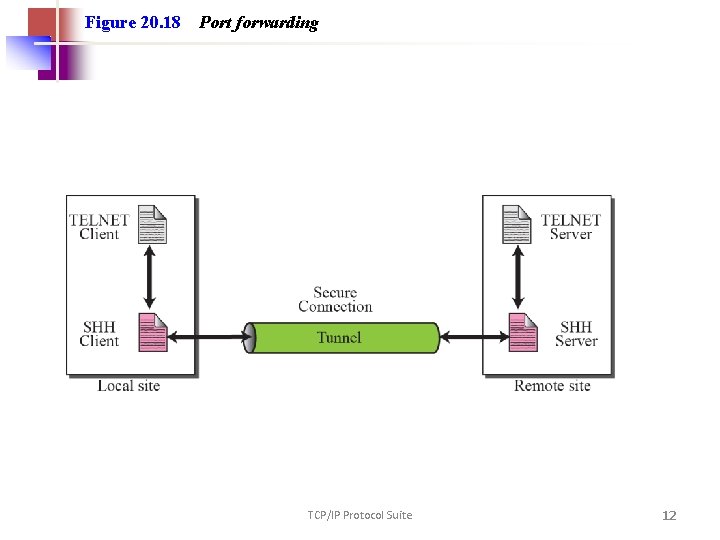
Figure 20. 18 Port forwarding TCP/IP Protocol Suite 12
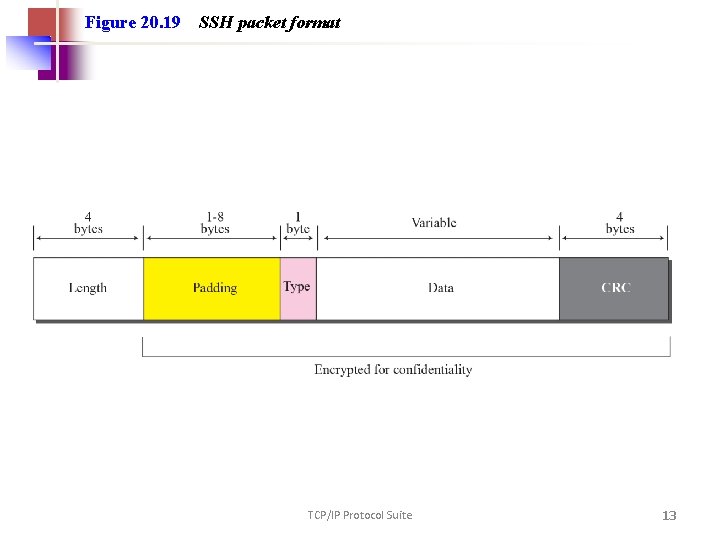
Figure 20. 19 SSH packet format TCP/IP Protocol Suite 13
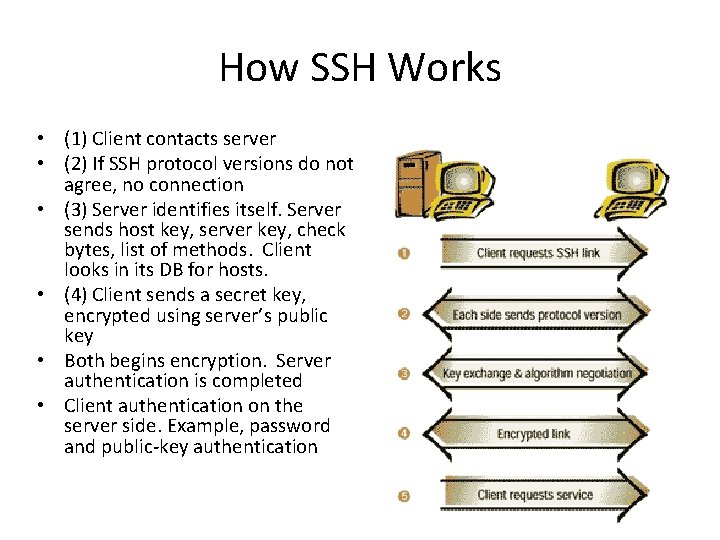
How SSH Works • (1) Client contacts server • (2) If SSH protocol versions do not agree, no connection • (3) Server identifies itself. Server sends host key, server key, check bytes, list of methods. Client looks in its DB for hosts. • (4) Client sends a secret key, encrypted using server’s public key • Both begins encryption. Server authentication is completed • Client authentication on the server side. Example, password and public-key authentication
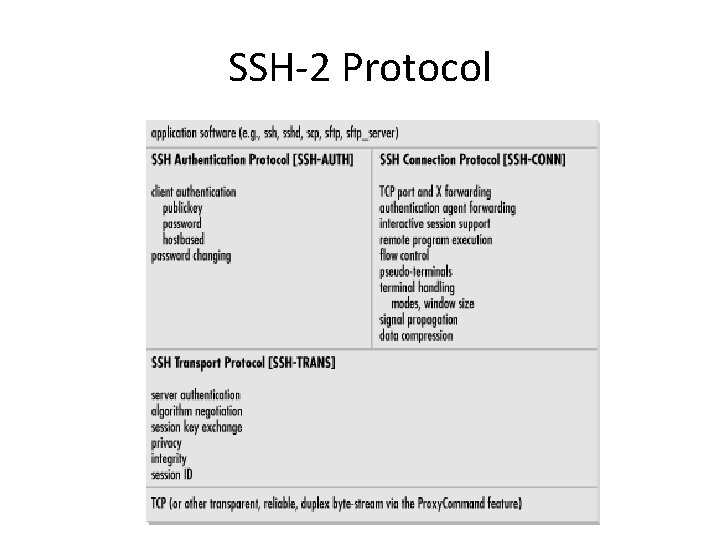
SSH-2 Protocol
- Slides: 15