WISE Workshop Data Protection WISE Information Security for


- Slides: 23

WISE Workshop Data Protection WISE Information Security for Collaborating E-Infrastructures NSF Summit 2018 Uros Stevanovic - KIT https: //aarc-project. eu
General Data Protection Regulation • General Data Protection Regulation (GDPR) • Adopted 14 th April 2016, went into force 25 th May 2018 • Legally binding for all Member States, without the need for parliament ratification • Replaces Data Protection Directive (1995/46/EC) • ~3 x longer
However. . • GDPR is not finished… • Certain areas left to individual states (e. g. genetic data, biometric data) • Guidances yet to be issued (e. g. cloud) • e. Privacy regulation is not yet finished • Uncertainty/change/contradiction well beyond May 2018
Application • One is processing personal data? If so, GDPR applies • MAC/IP address (dynamic, too), RFID tags, etc. • Per use record may contain personal data • e. Privacy Regulation covers all data related to communication • Headers, content, GPS location • Even non personal data
GDPR changes • Apply to the processing of personal data by controllers and processors in the EU, regardless where it takes place • Penalties – up to 4% of annual global turnover or 20 M€ (whichever is greater) • Consent – conditions are strengthened (clear and plain language, explicitly related to the processing, easy to withdraw) • Breach notification • Privacy by design • Right to access • Data Protection Officers • Right to be forgotten
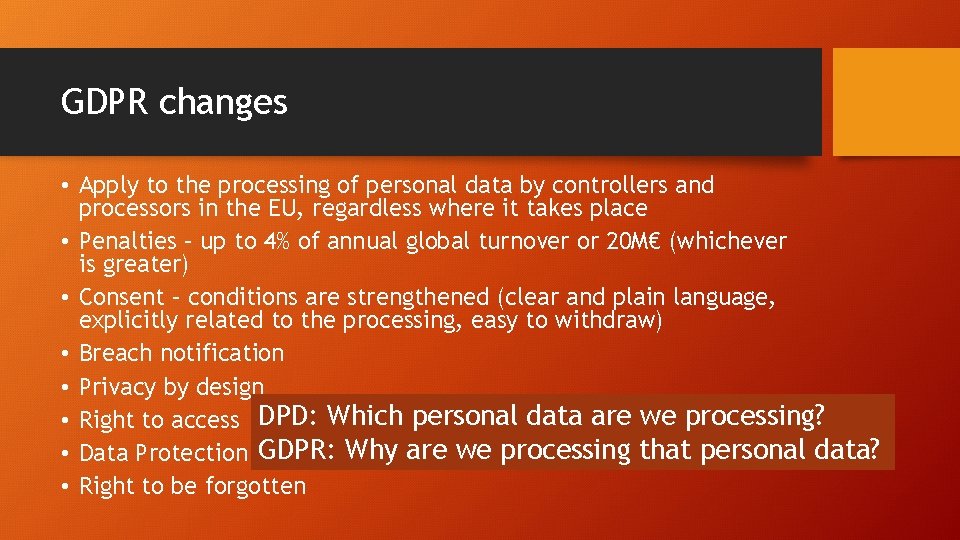
GDPR changes • Apply to the processing of personal data by controllers and processors in the EU, regardless where it takes place • Penalties – up to 4% of annual global turnover or 20 M€ (whichever is greater) • Consent – conditions are strengthened (clear and plain language, explicitly related to the processing, easy to withdraw) • Breach notification • Privacy by design • Right to access DPD: Which personal data are we processing? GDPR: Why are we processing that personal data? • Data Protection Officers • Right to be forgotten
Accountability • Need to understand/document • • What you’re processing, why, where, how long for, who may obtain it Risks, and how they are managed Information lifecycles How users can monitor processing of their data • Different legal bases => different notices, duties and user rights • If required, appoint a Data Protection Officer • Public authorities (i. e. bodies with special legal powers), or • Core activities involve large-scale monitoring/SPD of individuals
Data Protection by Design/Default • Data protection considered early in system/process design • Data minimisation, anonymisation, pseudonyms, etc. • Formal Data Protection Impact Assessments (DPIA) • Required for large-scale/risky processing • Identify risks to individuals (not the organisation), mitigate, assess • DPA approval needed if high risks remain
Consent • New, tighter, conditions for consent to be valid • Free, informed, positive action, revocable (as easily) at any time • In particular: not a condition of service, not under compulsion • Must keep records of consent • Who, when, how, to what • Designed to be hard to obtain/manage (“reduce overuse”) • Likely to have to consider other legal bases
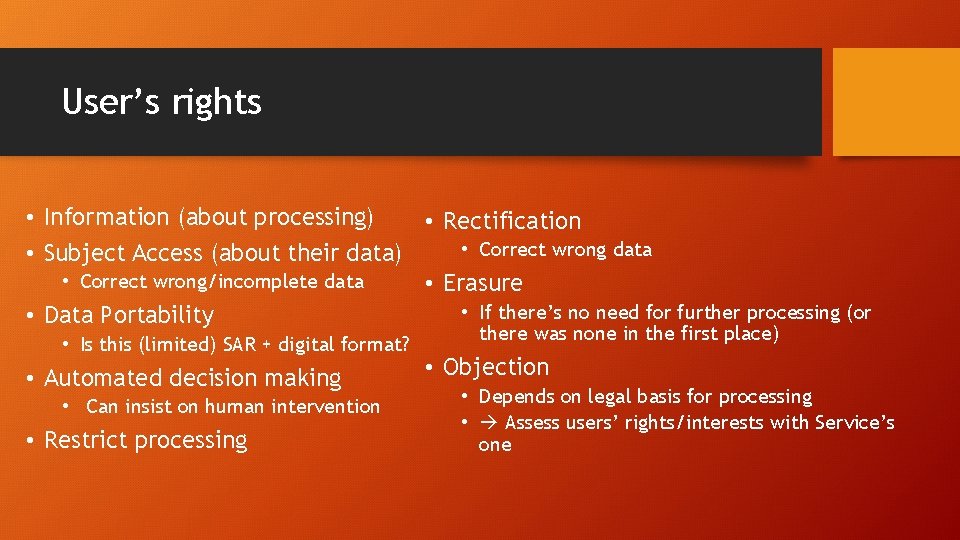
User’s rights • Information (about processing) • Rectification • Correct wrong data • Subject Access (about their data) • Correct wrong/incomplete data • Erasure • If there’s no need for further processing (or • Data Portability • Is this (limited) SAR + digital format? • Automated decision making • Can insist on human intervention • Restrict processing there was none in the first place) • Objection • Depends on legal basis for processing • Assess users’ rights/interests with Service’s one
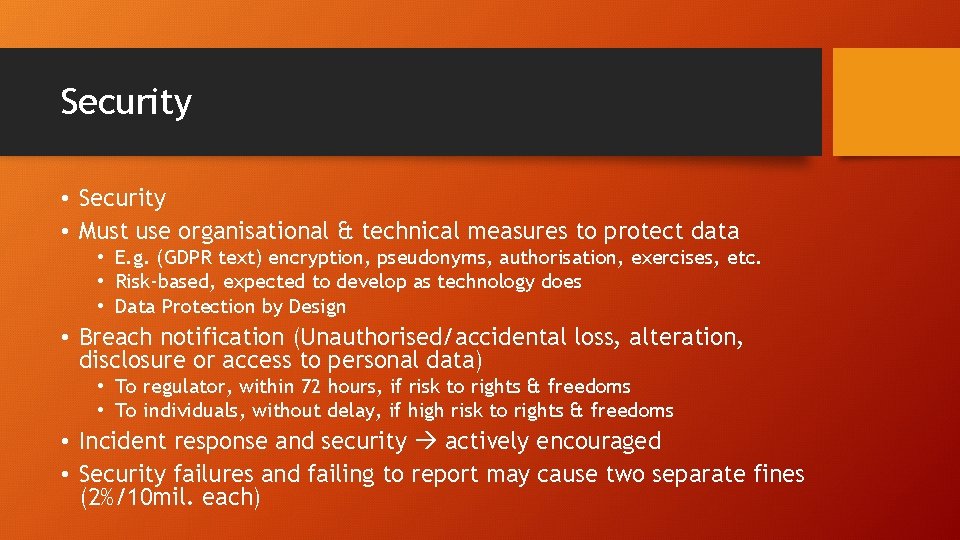
Security • Must use organisational & technical measures to protect data • E. g. (GDPR text) encryption, pseudonyms, authorisation, exercises, etc. • Risk-based, expected to develop as technology does • Data Protection by Design • Breach notification (Unauthorised/accidental loss, alteration, disclosure or access to personal data) • To regulator, within 72 hours, if risk to rights & freedoms • To individuals, without delay, if high risk to rights & freedoms • Incident response and security actively encouraged • Security failures and failing to report may cause two separate fines (2%/10 mil. each)
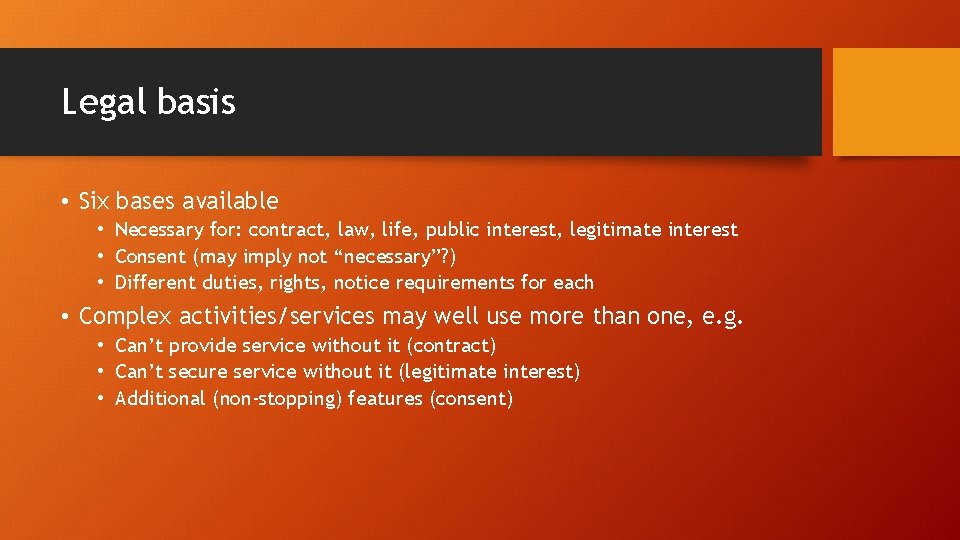
Legal basis • Six bases available • Necessary for: contract, law, life, public interest, legitimate interest • Consent (may imply not “necessary”? ) • Different duties, rights, notice requirements for each • Complex activities/services may well use more than one, e. g. • Can’t provide service without it (contract) • Can’t secure service without it (legitimate interest) • Additional (non-stopping) features (consent)
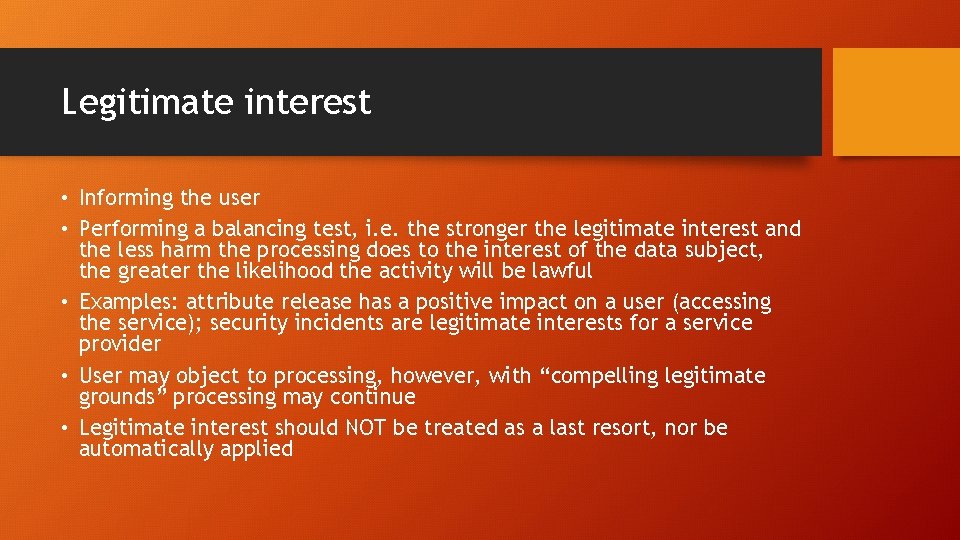
Legitimate interest • Informing the user • Performing a balancing test, i. e. the stronger the legitimate interest and the less harm the processing does to the interest of the data subject, the greater the likelihood the activity will be lawful • Examples: attribute release has a positive impact on a user (accessing the service); security incidents are legitimate interests for a service provider • User may object to processing, however, with “compelling legitimate grounds” processing may continue • Legitimate interest should NOT be treated as a last resort, nor be automatically applied
Release of personal data outside the EU • Recognized countries (Andorra, Isle of Man, Argentina, etc. ) – not many, US is not recognized • Several possible conditions for transfer: • User needs to be informed of the safeguards • Custom exchange model needs an explicit approval from a data protection authority • “Binding Corporate Rules” (BCR) • “Standard Data Protection Clauses” • “Approved Codes of Conduct” • Compelling legitimate interest* • Explicit user consent – an option, user needs to be informed of the risks, potential issues • “Safe Harbor” – invalidated by ECJ in 2015, no adequate protection • “EU-US Privacy Shield” – not applicable to research environment, potential similar issues as with the “Safe Harbor”
Federated AAI • Data minimisation is built-in • Necessary attributes, pseudonyms, anonymization, etc. • Legitimate interest basis applies • Info is necessary to provide a service • Transfer outside EU* • Consent • For additional data (not necessary to provide a service)
Incident response and security • Recital 49 • Necessary, proportionate • Resisting accidents or malicious activity, ensuring availability, integrity, confidentiality • Public authorities, CERTs, CSIRTs • Necessary for breach notification • Balancing interests (users vs services) • Compatible with current practices
Next • Data Protection Code of Conduct • Data Protection Impact Assessment
Thank you Questions? wise@lists. wise-community. org
Legal terms • Personal data • Article 4(1) - Any information relating to an identified or identifiable natural person (‘data subject’), i. e name, IP address, email, geolocation, identifier to physical, gender, mental, economic etc. identity • Processing • Article 4(2) – any operation or set of operations which is performed on personal data or on sets of personal data, whether or not by automated means, i. e. collection, recording, organisation, structuring, storage, etc. • Data Controllers and Data Processing • Article 4(7) – Data controller is any person (natural or legal) or entity that decides for which purpose personal data is processed • Article 4(8) – Data processor is any person (natural or legal) who process the data on behalf of the controller • Data controller is the responsible party that must ensure that all processing of personal data complies with the GDPR • In the case of research communities, data controllers are most common • Joint controllers – Article 26(1): “two or more controllers jointly determine the purposes and means of processing”
Rules for data processing, ensured by data controller Personal data must be processed legally and fairly It must be collected for explicit and legitimate purposes and used accordingly It must be adequate, relevant and not excessive, updated when necessary Data controllers must ensure that data subjects can rectify, remove or block incorrect data about themselves • Data that identifies individuals (personal data) must not be kept any longer than strictly necessary • Data controllers must protect personal data against accidental or unlawful destruction, loss, alteration and disclosure, particularly when processing involves data transmission over networks. They shall implement the appropriate security measures • These protection measures must ensure a level of protection appropriate to the data • •
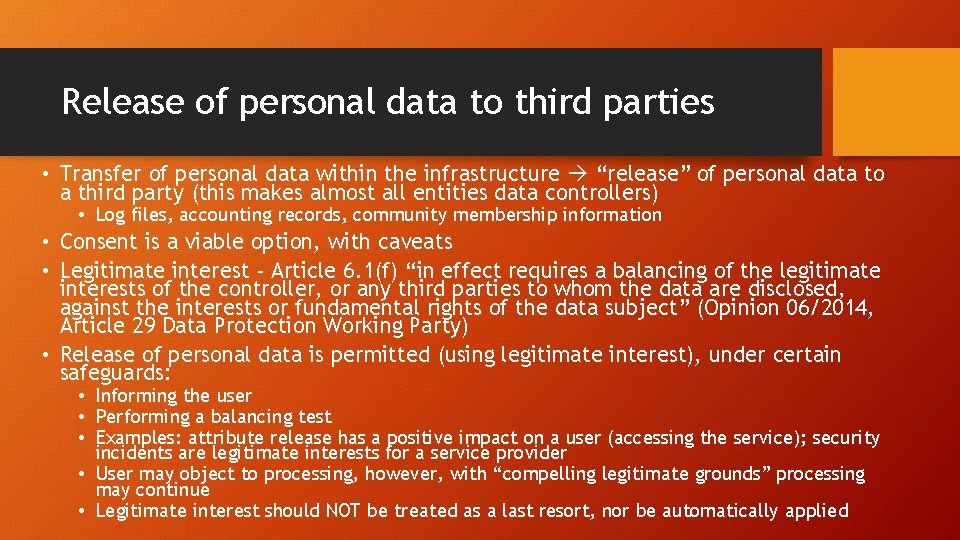
Release of personal data to third parties • Transfer of personal data within the infrastructure “release” of personal data to a third party (this makes almost all entities data controllers) • Log files, accounting records, community membership information • Consent is a viable option, with caveats • Legitimate interest - Article 6. 1(f) “in effect requires a balancing of the legitimate interests of the controller, or any third parties to whom the data are disclosed, against the interests or fundamental rights of the data subject” (Opinion 06/2014, Article 29 Data Protection Working Party) • Release of personal data is permitted (using legitimate interest), under certain safeguards: • Informing the user • Performing a balancing test • Examples: attribute release has a positive impact on a user (accessing the service); security incidents are legitimate interests for a service provider • User may object to processing, however, with “compelling legitimate grounds” processing may continue • Legitimate interest should NOT be treated as a last resort, nor be automatically applied
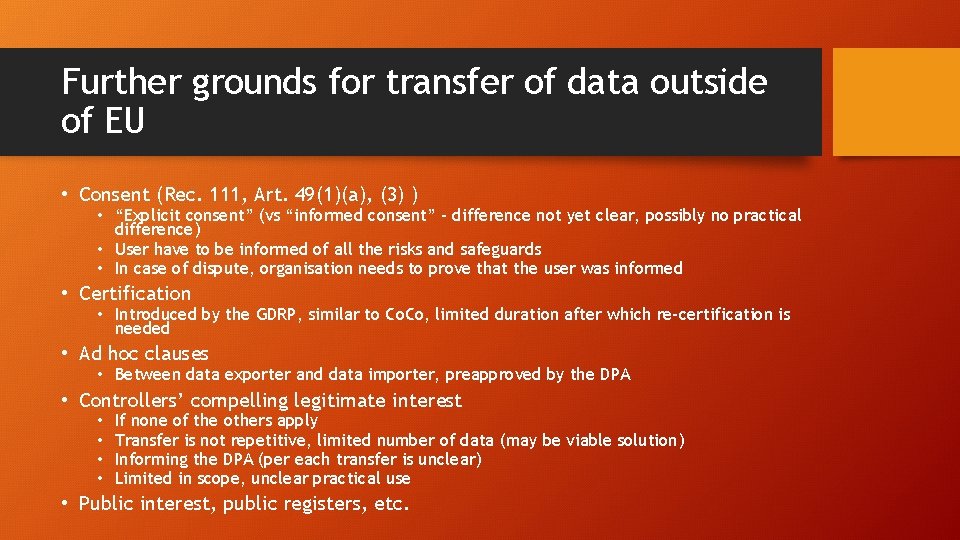
Further grounds for transfer of data outside of EU • Consent (Rec. 111, Art. 49(1)(a), (3) ) • “Explicit consent” (vs “informed consent” – difference not yet clear, possibly no practical difference) • User have to be informed of all the risks and safeguards • In case of dispute, organisation needs to prove that the user was informed • Certification • Introduced by the GDRP, similar to Co. Co, limited duration after which re-certification is needed • Ad hoc clauses • Between data exporter and data importer, preapproved by the DPA • Controllers’ compelling legitimate interest • • If none of the others apply Transfer is not repetitive, limited number of data (may be viable solution) Informing the DPA (per each transfer is unclear) Limited in scope, unclear practical use • Public interest, public registers, etc.

References • Andrew Cormack: • https: //eventr. geant. org/events/2731 • https: //community. jisc. ac. uk/blogs/regulatory-developments • https: //script-ed. org/article/incident-response-protecting-individual-rightsunder-the-general-data-protection-regulation/ • https: //edpb. europa. eu/ • https: //ico. org. uk/for-organisations/data-protection-reform/ • https: //eur-lex. europa. eu/legalcontent/EN/TXT/PDF/? uri=CELEX: 32016 R 0679