Wireshark Lab ICMP Computer Networking A Topdown Approach
Wireshark Lab: ICMP Computer Networking: A Topdown Approach, 4 th edition.
Wireshark Lab: ICMP In this lab, we’ll explore several aspects of the ICMP protocol ICMP messages generating by the Ping program; ICMP messages generated by the Traceroute(tracert) program The format and contents of an ICMP message.
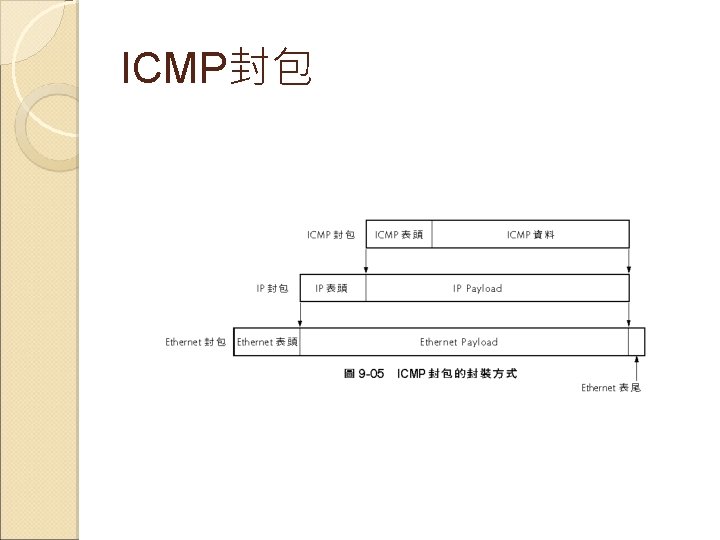
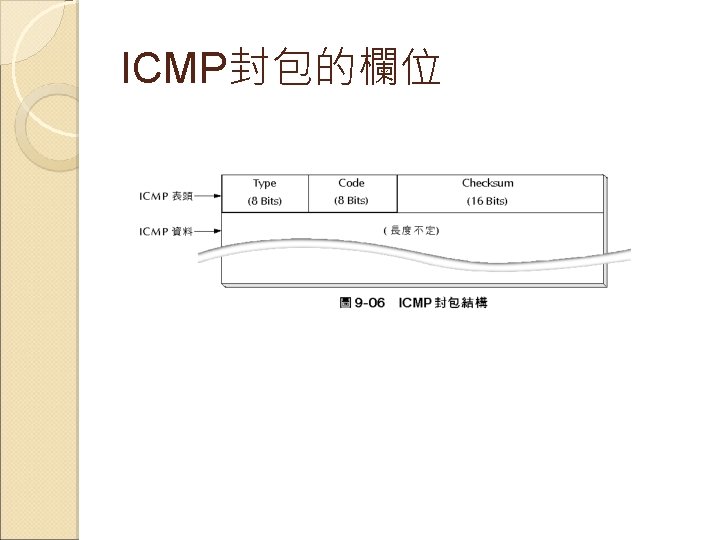
ICMP封包
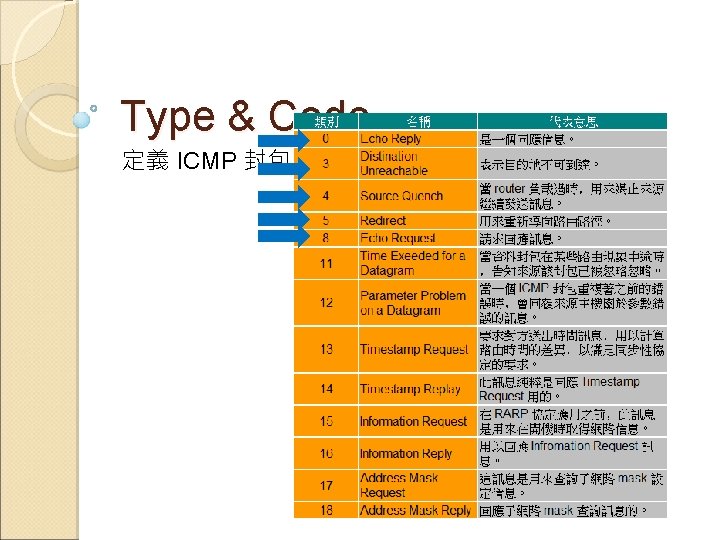
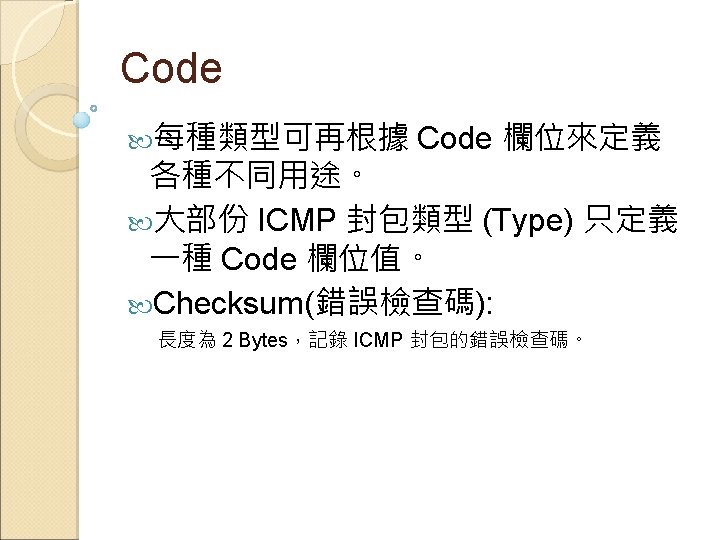
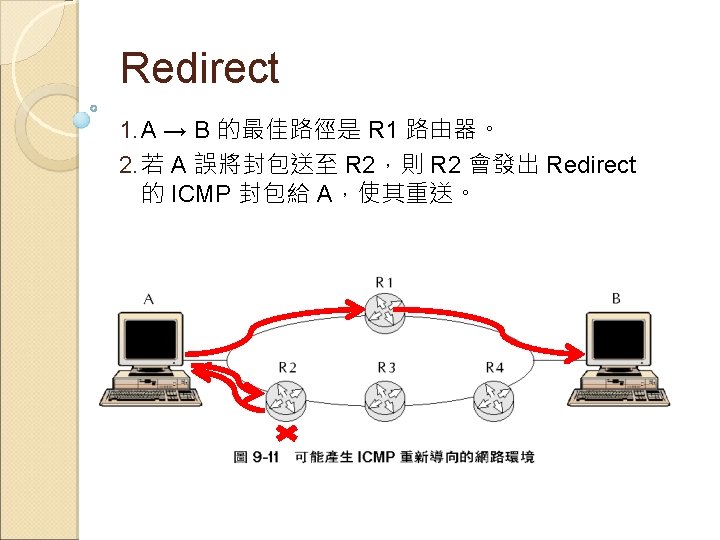
常見的 ICMP 類型 Echo Request / Echo Reply Destination Unreachable Source Quench Redirect Time Exceeded


ICMP 具程式 PING TRACERT

關於 PING Figure 1 Command Prompt window after entering Ping command
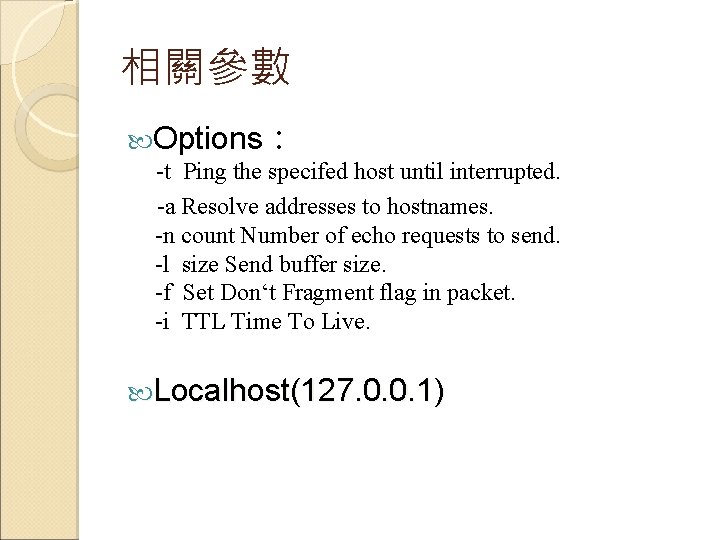
相關參數 Options: -t Ping the specifed host until interrupted. -a Resolve addresses to hostnames. -n count Number of echo requests to send. -l size Send buffer size. -f Set Don‘t Fragment flag in packet. -i TTL Time To Live. Localhost(127. 0. 0. 1)
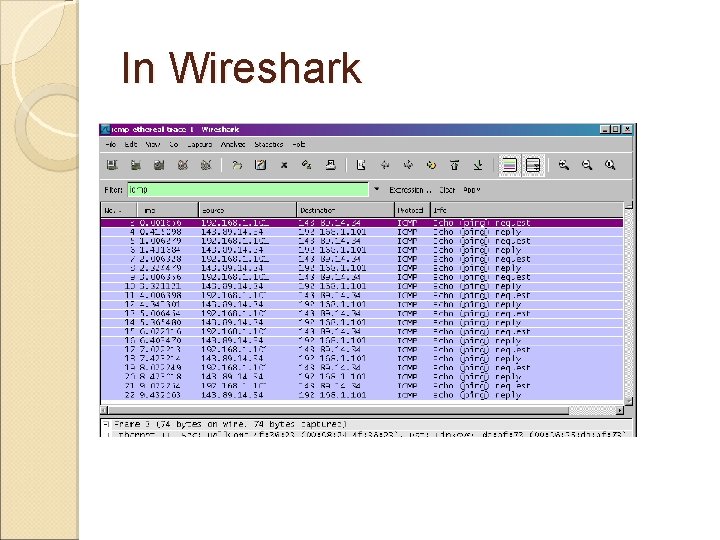
In Wireshark
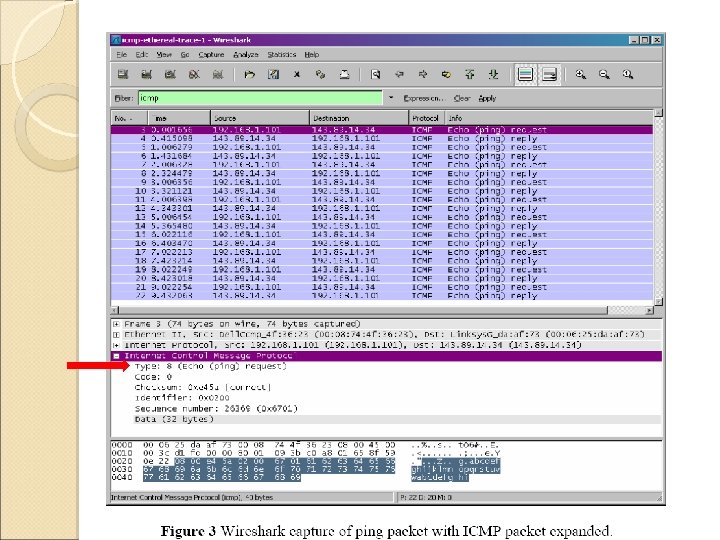
In wireshark Sender : echo-request( type 8 ) Receiver : echo-reply( type 0 )
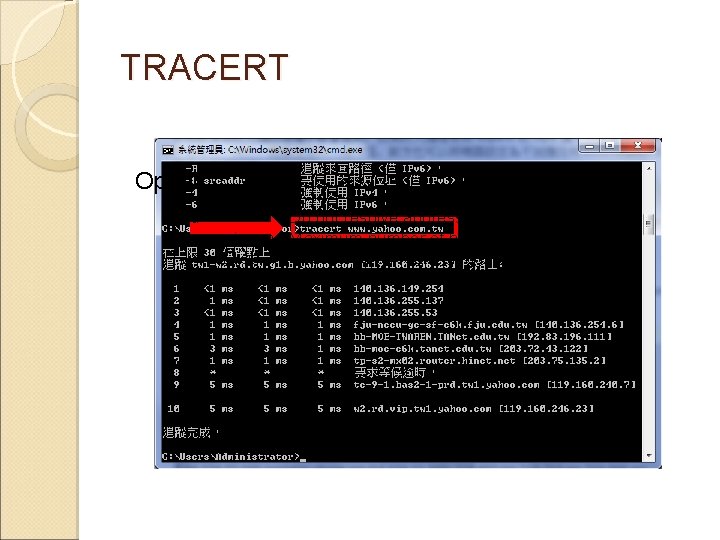
TRACERT Option: -d Do not resolve addresses to hostnames. -h maximum Maximum number of hops to search for target. -j host-list Loose source route along host-list. -w timeout Wait timeout milliseconds for each reply.
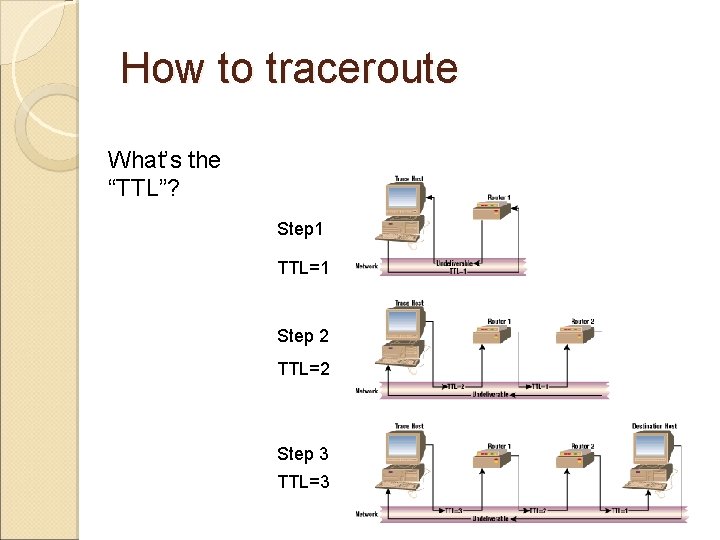
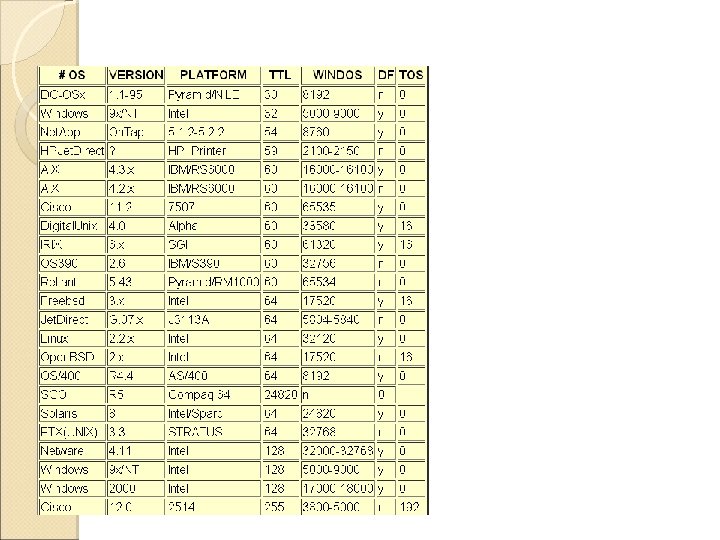
How to traceroute What’s the “TTL”? Step 1 TTL=1 Step 2 TTL=2 Step 3 TTL=3
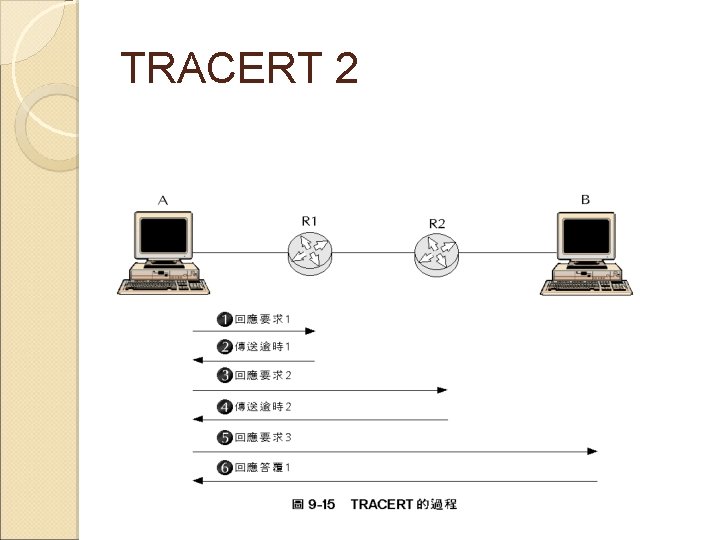
TRACERT 2
following questions: 1. What is the IP address of your host? What is the IP address of the destination host? 2. Why is it that an ICMP packet does not have source and destination port numbers? 3. Examine of the ping request packets sent by your host. What are the ICMP type and code numbers? What other fields does this ICMP packet have? How many bytes are the checksum, sequence number and identifier fields? 4. Examine the corresponding ping reply packet. What are the ICMP type and code numbers? What other fields does this ICMP packet have? How many bytes are the checksum, sequence number and identifier fields?

- Slides: 25