WIRELESS SECURITY DEFENSE TBONE TONIC ALY BOGHANI JOAN
WIRELESS SECURITY DEFENSE T-BONE & TONIC: ALY BOGHANI JOAN OLIVER MIKE PATRICK AMOL POTDAR 05/30/2009 May 30, 2009
Problem Overview 2 T-Bone & Tonic Corporate governance for wireless, wired access, and intranet security used to be governed separately, however, it can no longer be so for the following two reasons: 1. Security threats need to be addressed on an enterprise wide-level 2. Mobility is a critical component of IT infrastructure access today 05/30/2009
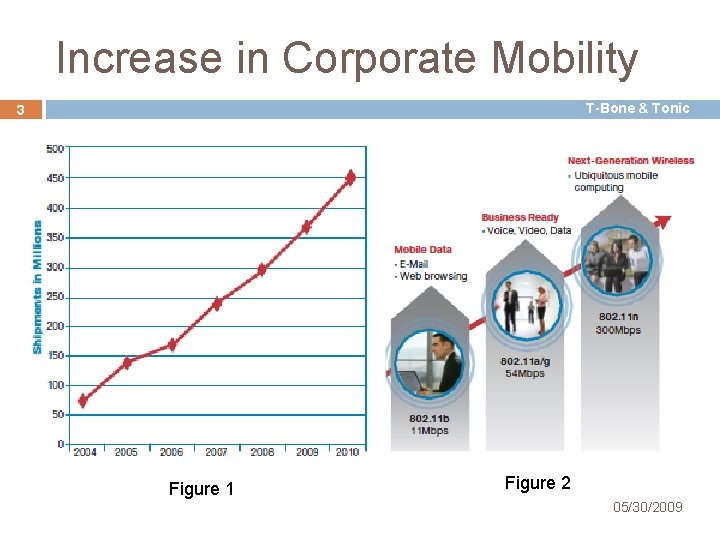
Increase in Corporate Mobility T-Bone & Tonic 3 Figure 1 F Figure 2 05/30/2009
Proposed Solution T-Bone & Tonic 4 • Cisco Wireless and Network Security Integration – Provides the architectural, design, and implementation framework in deploying the Cisco Unified Network – Enables an enterprise to deploy and enforce a common network security policy – Consistent end-to-end policy enforcement as well as a highly effective threat detection and mitigation capability – WLAN/LAN integrated and layered security 05/30/2009 protocol solution
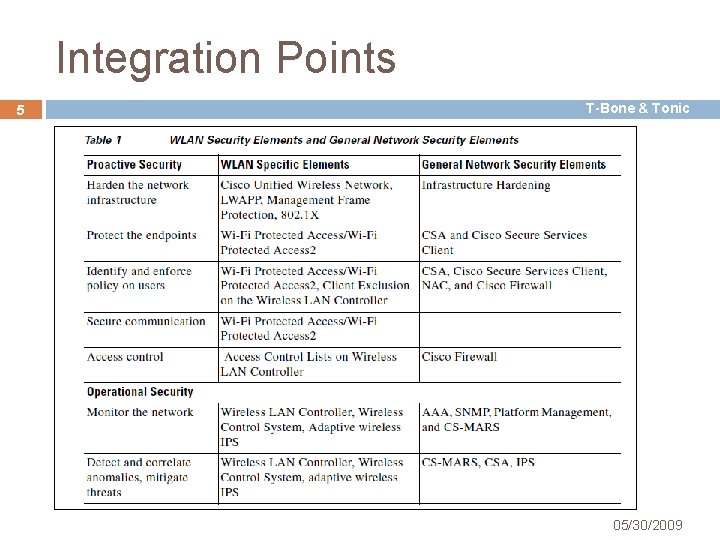
Integration Points 5 T-Bone & Tonic 05/30/2009
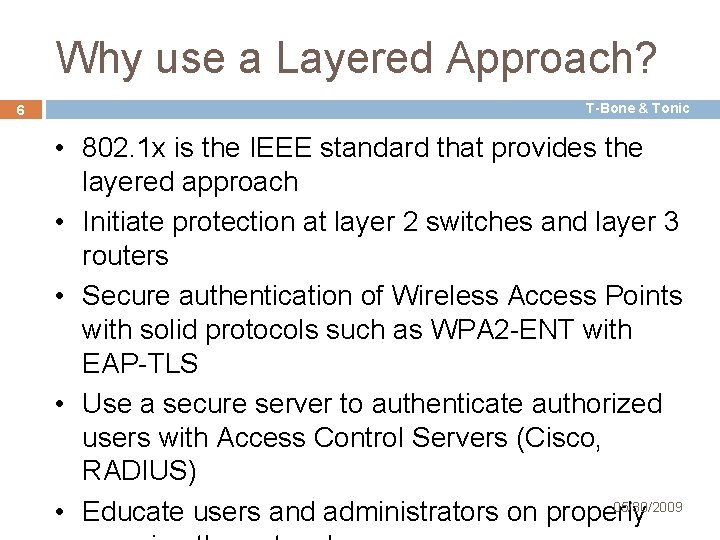
Why use a Layered Approach? 6 T-Bone & Tonic • 802. 1 x is the IEEE standard that provides the layered approach • Initiate protection at layer 2 switches and layer 3 routers • Secure authentication of Wireless Access Points with solid protocols such as WPA 2 -ENT with EAP-TLS • Use a secure server to authenticate authorized users with Access Control Servers (Cisco, RADIUS) 05/30/2009 • Educate users and administrators on properly
Why Cisco? T-Bone & Tonic 7 • Cisco is unique in occupying 3 industry spaces: – Core Wired Networking products – Wireless Communications – Network Security 05/30/2009
The Cisco Unified Network 8 T-Bone & Tonic Cisco Unified Network is the marriage of the following 3 Cisco components: • Cisco Secure Wireless Architecture • Cisco Campus Architecture • Cisco Branch Architecture 05/30/2009
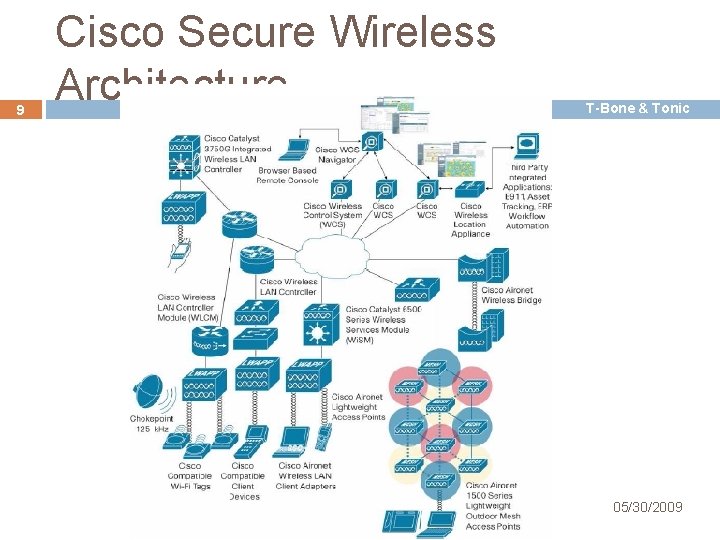
9 Cisco Secure Wireless Architecture T-Bone & Tonic 05/30/2009
10 Cisco Secure Wireless Architecture T-Bone & Tonic • Cisco Unified Wireless Network • Cisco Security Agent (CSA) • Cisco Network Admission Control (NAC) Appliance • Cisco Firewall • Cisco IPS • CS-MARS 05/30/2009
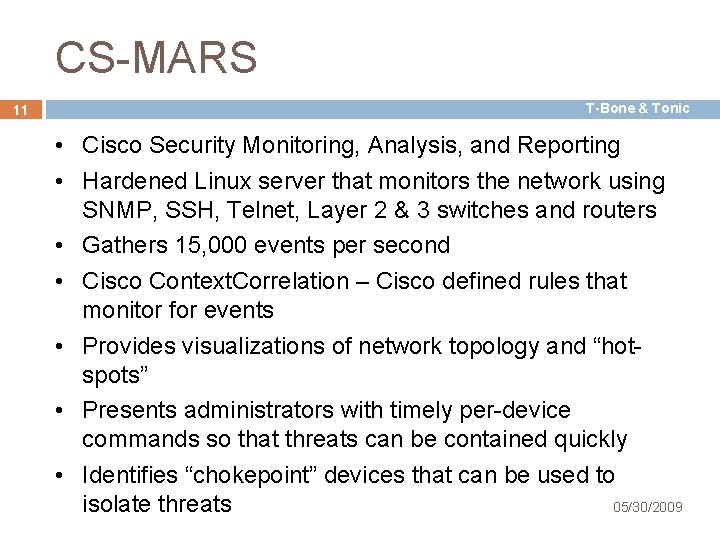
CS-MARS 11 T-Bone & Tonic • Cisco Security Monitoring, Analysis, and Reporting • Hardened Linux server that monitors the network using SNMP, SSH, Telnet, Layer 2 & 3 switches and routers • Gathers 15, 000 events per second • Cisco Context. Correlation – Cisco defined rules that monitor for events • Provides visualizations of network topology and “hotspots” • Presents administrators with timely per-device commands so that threats can be contained quickly • Identifies “chokepoint” devices that can be used to 05/30/2009 isolate threats
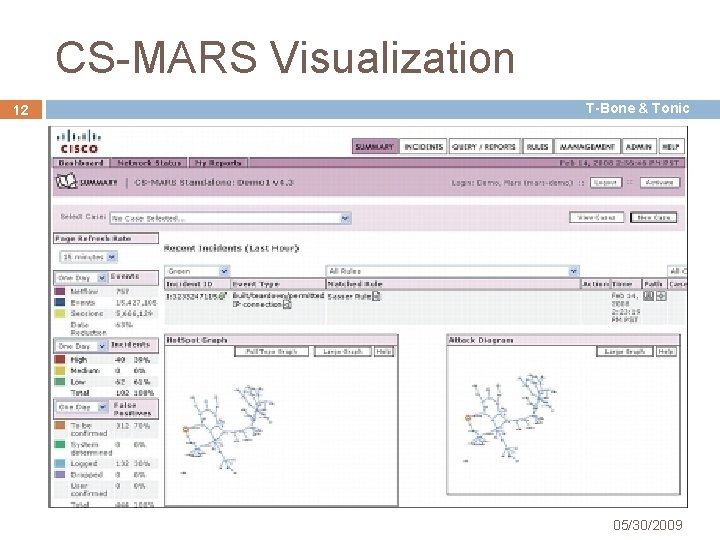
CS-MARS Visualization 12 T-Bone & Tonic 05/30/2009
NAC – Network Access Control T-Bone & Tonic 13 • 4 Main Capabilities – – Securely Identify Devices and Users Enforce Consistent Policy Quarantine and Remediate Configure and Manage • Access is controlled from all entry points to the network – LAN, WLAN, VPN, Internet, Guest • Can be used to tier access levels • Be careful with quarantine policies, isolate as much as possible • Uses Cisco Trust Agent and Cisco Security Agent to verify “security posture” 05/30/2009
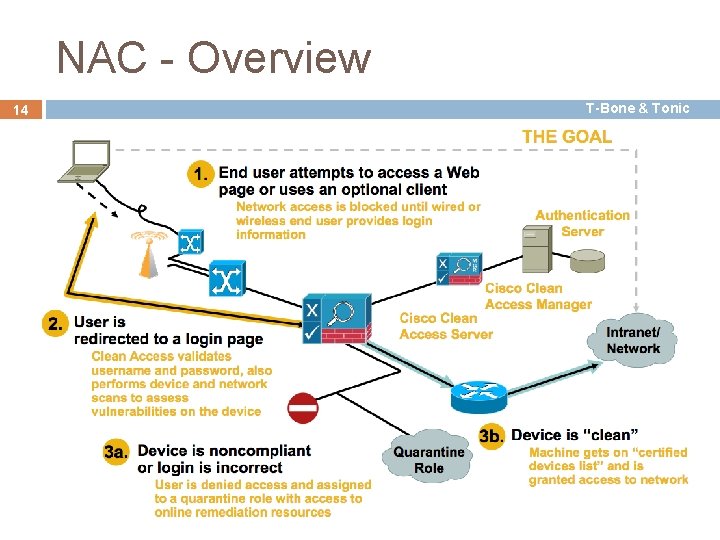
NAC - Overview 14 T-Bone & Tonic 05/30/2009
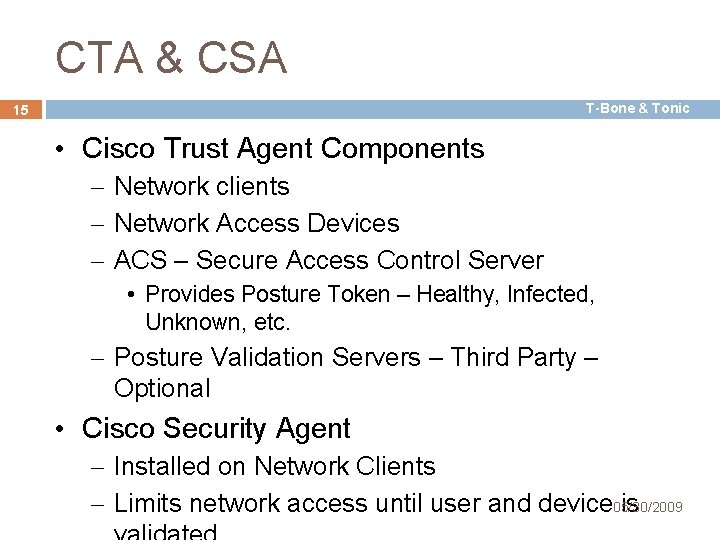
CTA & CSA T-Bone & Tonic 15 • Cisco Trust Agent Components – Network clients – Network Access Devices – ACS – Secure Access Control Server • Provides Posture Token – Healthy, Infected, Unknown, etc. – Posture Validation Servers – Third Party – Optional • Cisco Security Agent – Installed on Network Clients – Limits network access until user and device 05/30/2009 is
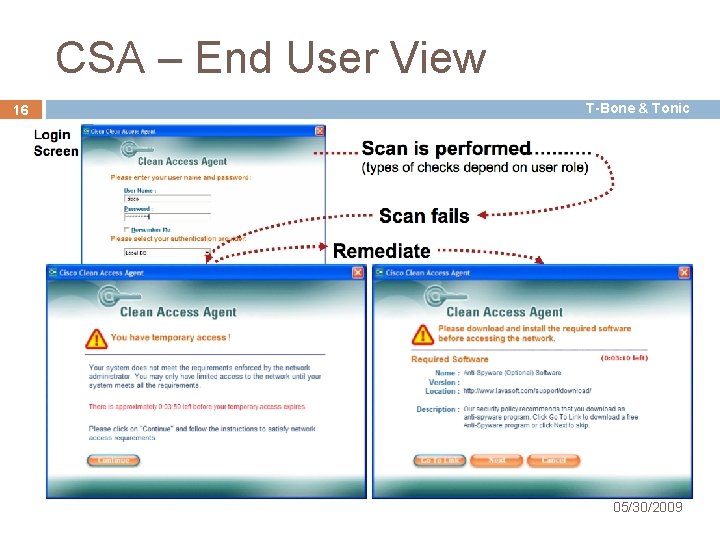
CSA – End User View 16 T-Bone & Tonic 05/30/2009
Cisco Campus Architecture T-Bone & Tonic 17 • Provision proper network access to: – Data Centers – Servers – User Devices • Provide the necessary internal routing and switching capabilities 05/30/2009
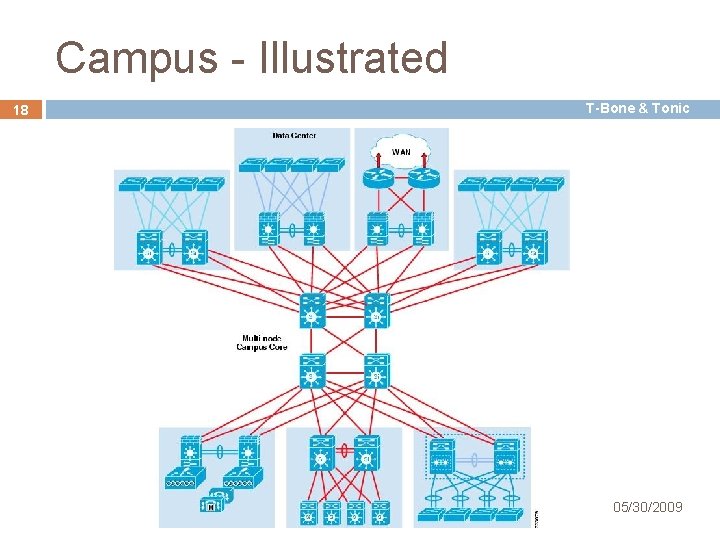
Campus - Illustrated 18 T-Bone & Tonic 05/30/2009
Cisco Branch Architecture 19 T-Bone & Tonic • Branch Architecture ties together the different infrastructure, application and computing resources across various organizational divisions and hierarchies. 05/30/2009
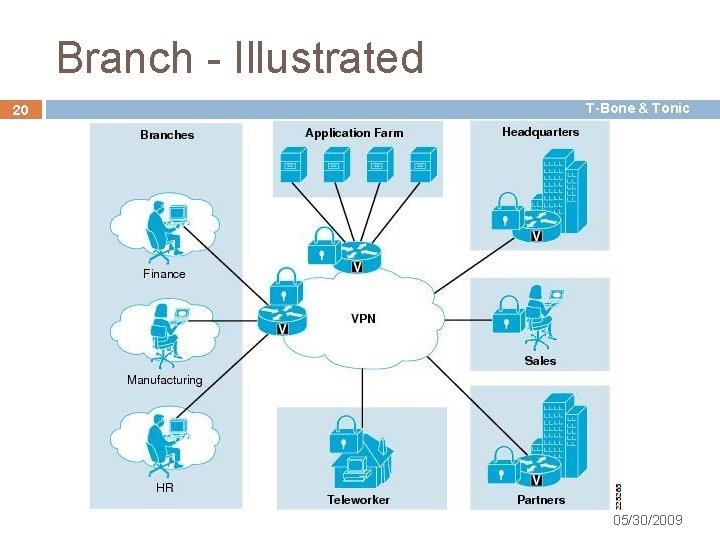
Branch - Illustrated 20 T-Bone & Tonic 05/30/2009
- Slides: 20