Wireless Security Balancing Efficiency with Security CS4453 Daniel
Wireless Security Balancing Efficiency with Security CS-4453 Daniel Servos
The Problem Security Efficiency Access to signal not easily controlled Ensuring privacy for information being transfered Blocking access to network from unauthorized users Throughput of network Lost and retransmitted packets Ease of use and set up of network Trade Off
Current and Past Solutions MAC Filters Advantages Disadvantages Low cost MAC address are spoofable Needs to be set up before hand for each network device Encryption Wired Equivalent Privacy (WEP) Tried to make privacy equivalent to wired networks by using encryption Deprecated, found unsure and crackable in minutes.
Current and Past Solutions Cont. Wi-Fi Protected Access (WPA) Advantages of encryption Made to deal with security issues of WEP. Poor passkeys (less then 20 characters) are acceptable to dictionary and brute force attacks. Hides packets content from others in the area Blocks unwanted users of the network Disadvantges Processing time Avalanche property Cracking

New Solutions A new Authentication Scheme with Anonymity for Wireless Environments Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Wireless Security Through RF Fingerprinting
A new Authentication Scheme with Anonymity for Wireless Environments Proposed by Jianming Zhu and Jianfeng Ma of Xidian University. Offer a new authentication protocol that is optimized for wireless environments and ensures anonymity of the user. Protocol Goals Authentication of mobile user and visited network Agreement of shared secret key Key authentication Assurance of session key freshness Non-repudiation of origin for relevant user data
A new Authentication Scheme with Anonymity for Wireless Environments Cont. Confidentiality of relevent data User anonymity as a data origin and destination Protocol has two phases First Phase Foreign agent and moible user authenticate each other through home agent Foreign agent issues temporary certificate to user Second Phase Done when moible user sends a message Sends certificate and encrypted data containing the session key, same certificate and the message
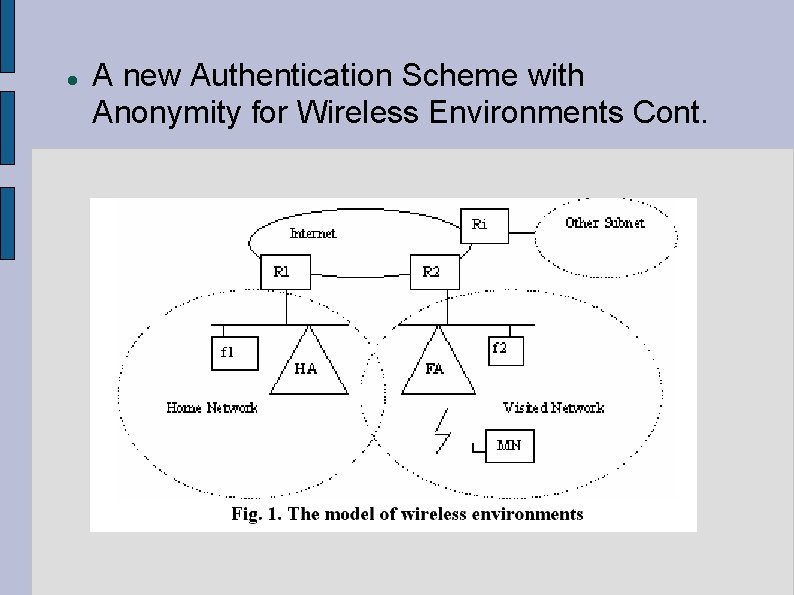
A new Authentication Scheme with Anonymity for Wireless Environments Cont.
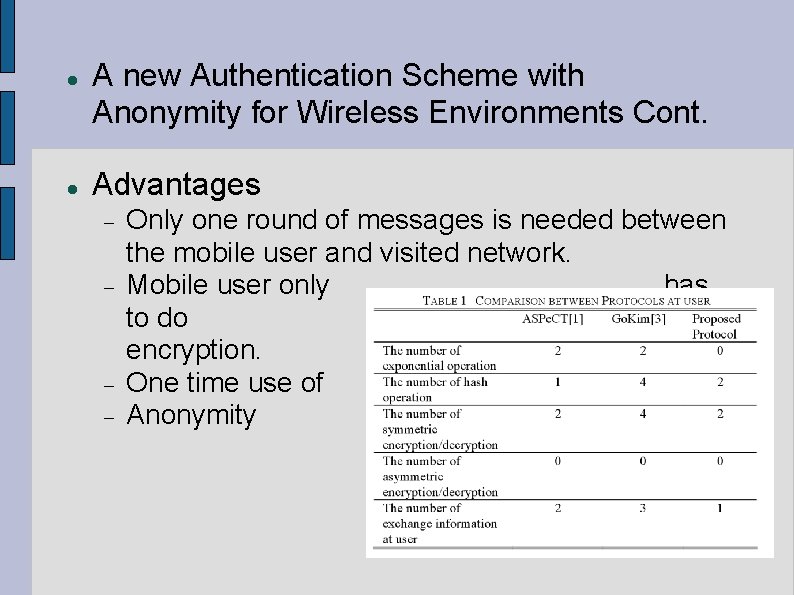
A new Authentication Scheme with Anonymity for Wireless Environments Cont. Advantages Only one round of messages is needed between the mobile user and visited network. Mobile user only has to do symmetric encryption. One time use of key. Anonymity
Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Proposed by Mohamed A. Haleem, Chetan N. Mathur, R. Chandramouli and K. P. Subbalakshmi of Stevens Institute of Technology Note that current encryption systems are greatly effected by even signal bit errors Note that in wirless systems bit errors are common and increases in like hood as noise level goes up
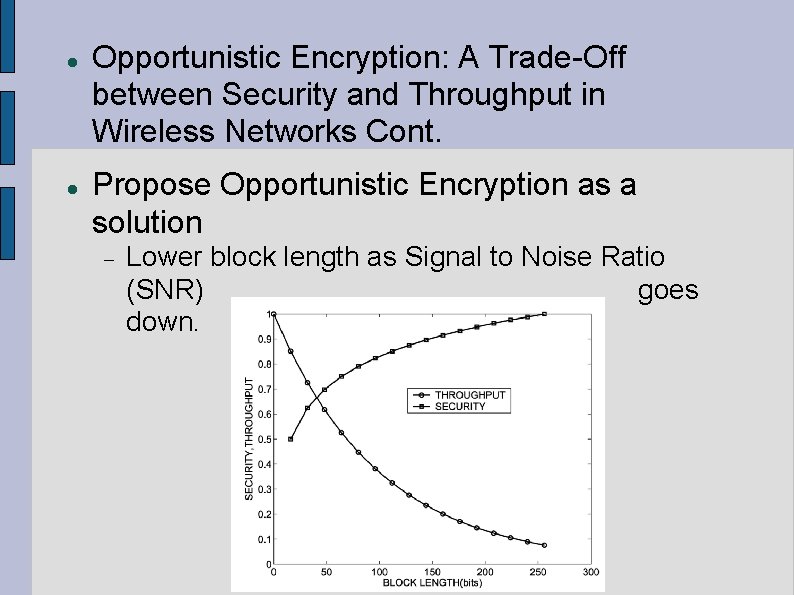
Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Cont. Propose Opportunistic Encryption as a solution Lower block length as Signal to Noise Ratio (SNR) goes down.
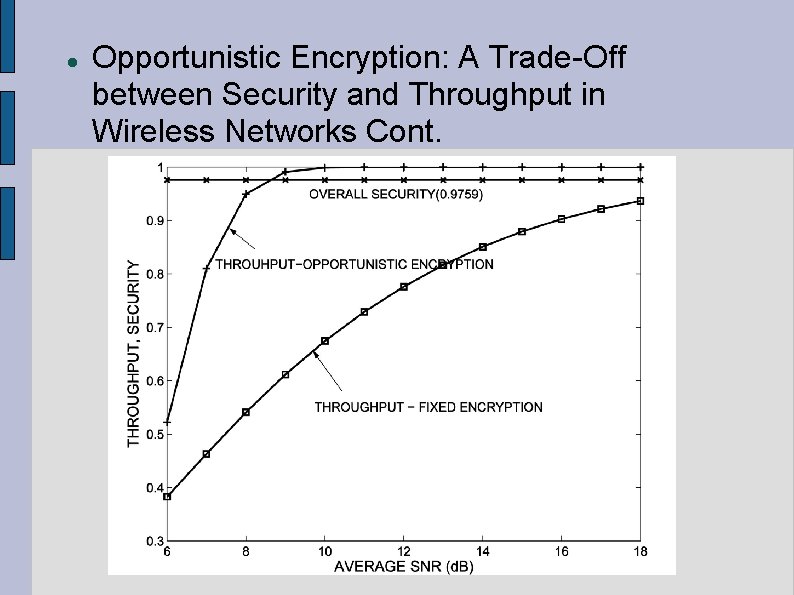
Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Cont.
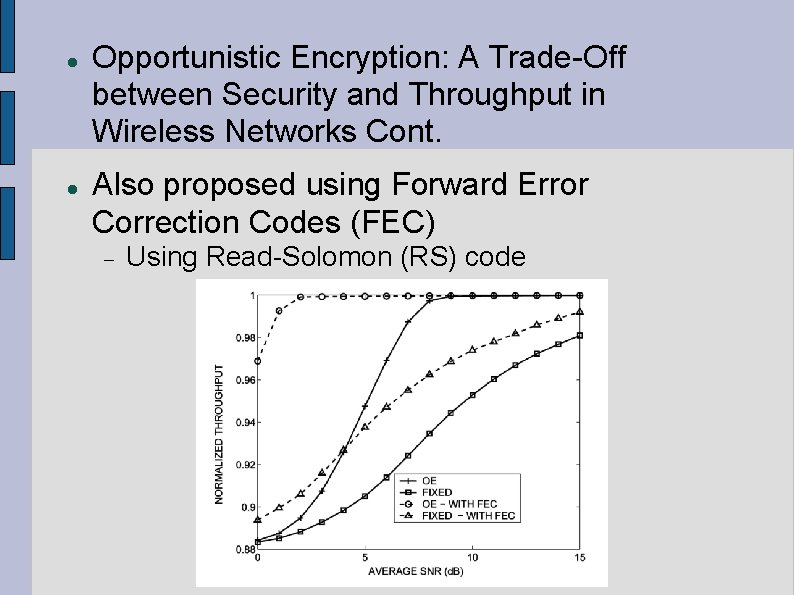
Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Cont. Also proposed using Forward Error Correction Codes (FEC) Using Read-Solomon (RS) code
Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Cont. Advantages Increases throughput in low SNR cases Decreases retransmition and bit errors Disadvantages Less secure in low SNR cases Overall slightly less secure then fixed encryption
Wireless Security Through RF Fingerprinting Proposed by Oktay Ureten and Nur Serinken of the Communications Research Centre Propose that Wi. Fi devices can be identifyed by a RF Fingerprint RF fingerprint is made up characteristics of the Wi. Fi device during the power up stage. Each Wi. Fi device has small differences in the amplitude and other characteristics of the signal due to manufacturing, model, age and installation differences. Same technique has been used for some time for identifying sources of radio singals
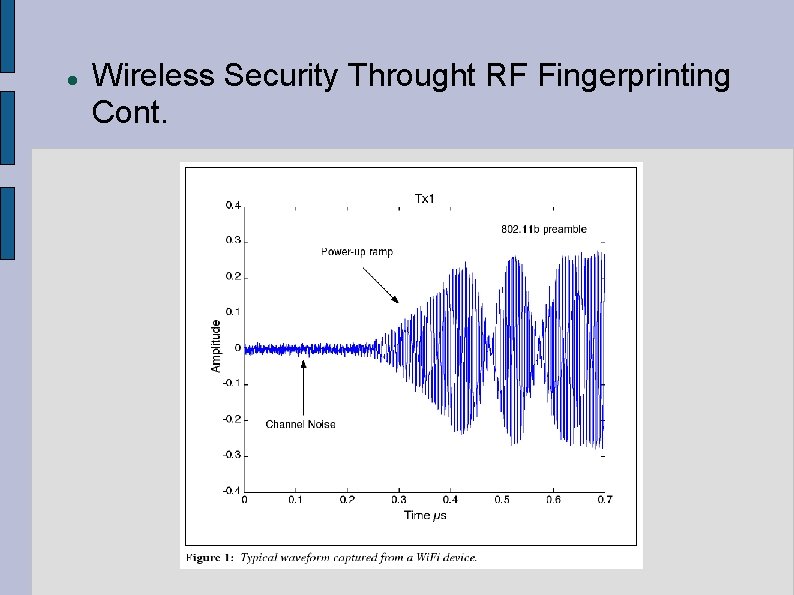
Wireless Security Throught RF Fingerprinting Cont.
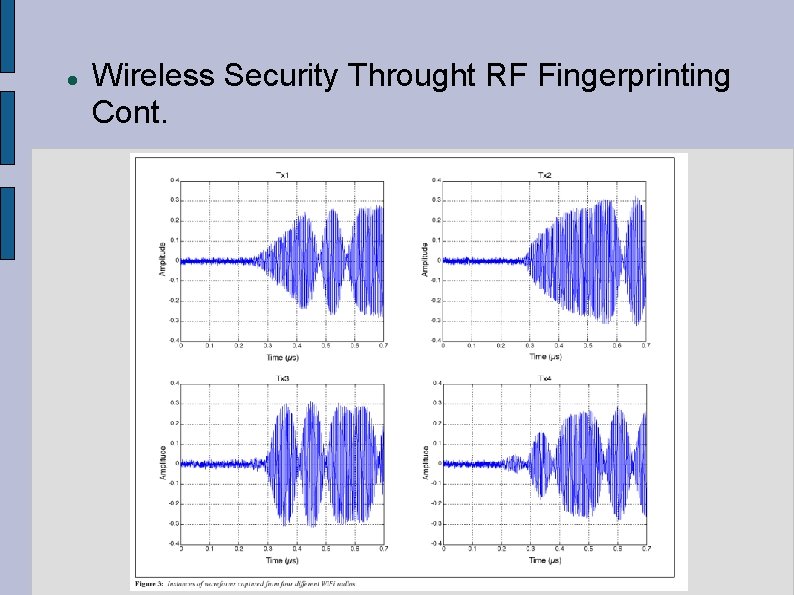
Wireless Security Throught RF Fingerprinting Cont.
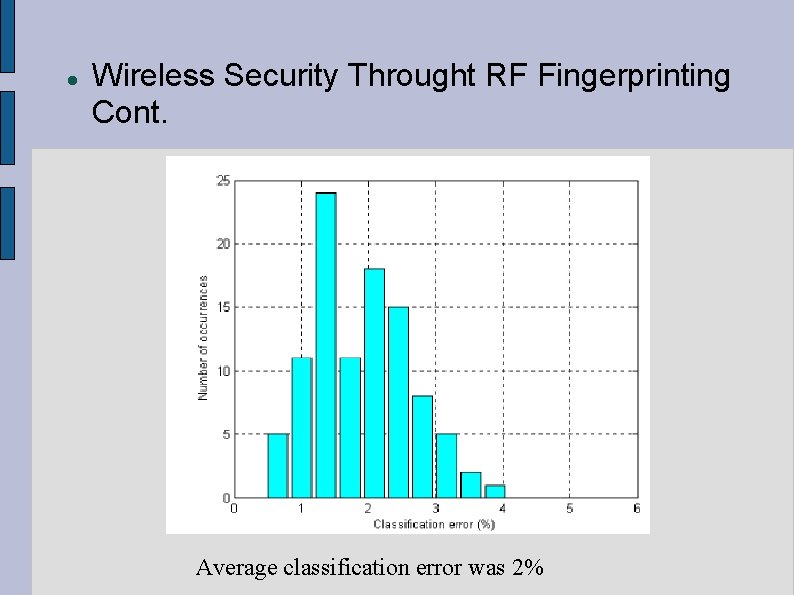
Wireless Security Throught RF Fingerprinting Cont. Average classification error was 2%
Wireless Security Throught RF Fingerprinting Cont. Advantages Low Cost During Use Does not need to be implemented client side Hard to fake RF Fingerprint Disadvantages Requires a lot of process power on the side of the acess point Profiles need to be made before hand using a neural network Fingerprints can change in time and in different environments Has a relatively high error rate compared to other methods
Other Solutions WLAN Security Processor Hardware implementation of wireless encryption The Advantages of Elliptic Curve Cryptography for Wireless Security Faster and more efficient public key encryption using principles of elliptical curves
Proposed Solution Based on Opportunistic Encryption. Add more characteristics to determine block size and calculations to be done. Power level of device Processing power of device User defined setting Benchmark Opportunistic Encryption implementation against current wireless encryption standards such as WEP and WAP. Implement in a wirless network simulator
Network Simulator Several good simulators for wireless networks Lecs. Sim - http: //sourceforge. net/projects/lecssim Open. WNS - http: //www. openwns. org SIMULX - http: //simulx. u-strasbg. fr NCTUns - http: //nsl 10. csie. nctu. edu. tw Secan Lab simulator - http: //wiki. uni. lu/secanlab/802. 11+Network+Simulator. html PROWLER http: //www. isis. vanderbilt. edu/Projects/nest/prowl er/
Sources A new Authentication Scheme with Anonymity for Wireless Environments Jianming Zhu and Jianfeng Ma J. Zhu and J. Ma: A New Authentication Scheme with Anonymity for Wireless Environments Opportunistic Encryption: A Trade-Off between Security and Throughput in Wireless Networks Mohamed A. Haleem, Chetan N. Mathur, R. Chandramouli, and K. P. Subbalakshmi IEEE Transactions on Dependable and Secure Computing, Vol. 4, No. 4, October. December 2007 Wireless Security Throught RF Fingerprinting Oktay Ureten and Nur Serinken Can. J. Elect. Comput. Eng. , Vol. 32, No. 1, Winter 2007 WLAN Security Processor Neil Smyth, Máire Mc. Loone, and John V. Mc. Canny IEEE Transactions on Circuits and Systems—I: Regular Papers, Vol. 53, No. 7, July 2006 The Advantages of Elliptic Curve Cryptography for Wireless Security Kristin Lauter, Microsoft Corporation IEEE Wireless Communications • February 2004
- Slides: 23