Wireless Network Attacks Tools Attack Vectors and Solutions
- Slides: 10
Wireless Network Attacks: Tools, Attack Vectors, and Solutions. By: Thomas Vaccaro
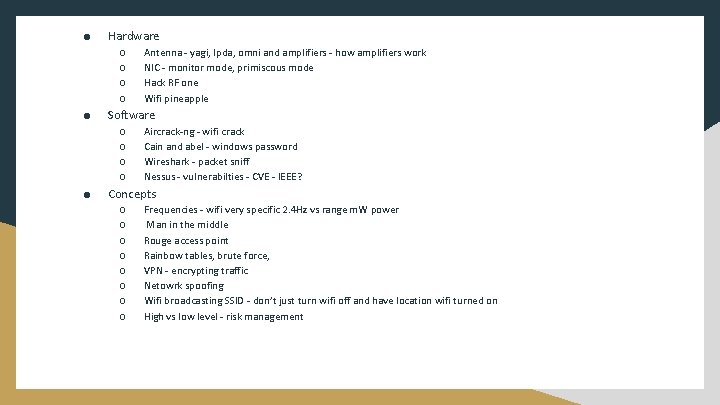
● Hardware ○ ○ ● Software ○ ○ ● Antenna - yagi, lpda, omni and amplifiers - how amplifiers work NIC - monitor mode, primiscous mode Hack RF one Wifi pineapple Aircrack-ng - wifi crack Cain and abel - windows password Wireshark - packet sniff Nessus - vulnerabilties - CVE - IEEE? Concepts ○ ○ ○ ○ Frequencies - wifi very specific 2. 4 Hz vs range m. W power Man in the middle Rouge access point Rainbow tables, brute force, VPN - encrypting traffic Netowrk spoofing Wifi broadcasting SSID - don’t just turn wifi off and have location wifi turned on High vs low level - risk management
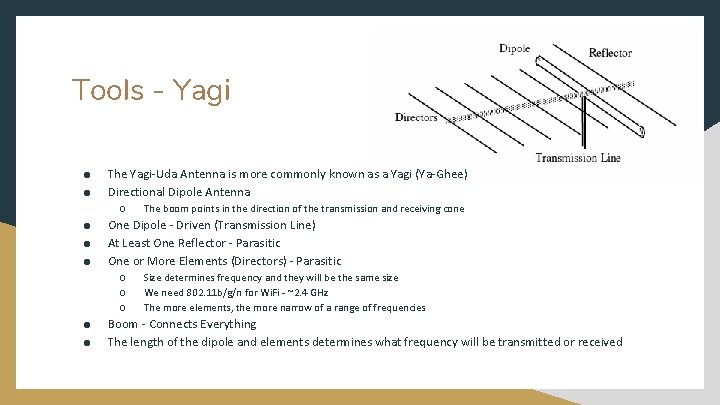
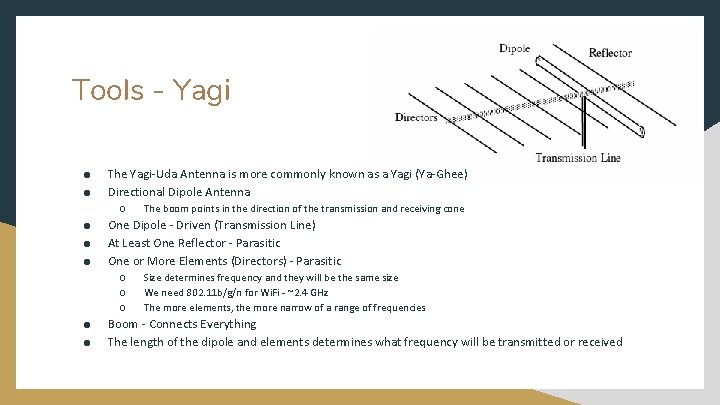
Tools - Yagi ● ● The Yagi-Uda Antenna is more commonly known as a Yagi (Ya-Ghee) Directional Dipole Antenna ○ ● ● ● One Dipole - Driven (Transmission Line) At Least One Reflector - Parasitic One or More Elements (Directors) - Parasitic ○ ○ ○ ● ● The boom points in the direction of the transmission and receiving cone Size determines frequency and they will be the same size We need 802. 11 b/g/n for Wi. Fi - ~2. 4 GHz The more elements, the more narrow of a range of frequencies Boom - Connects Everything The length of the dipole and elements determines what frequency will be transmitted or received
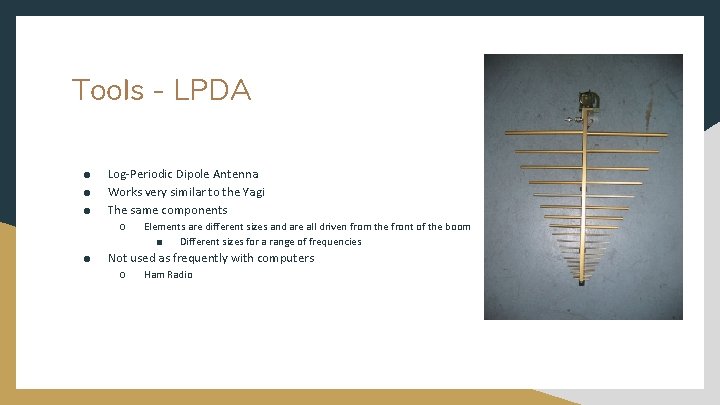
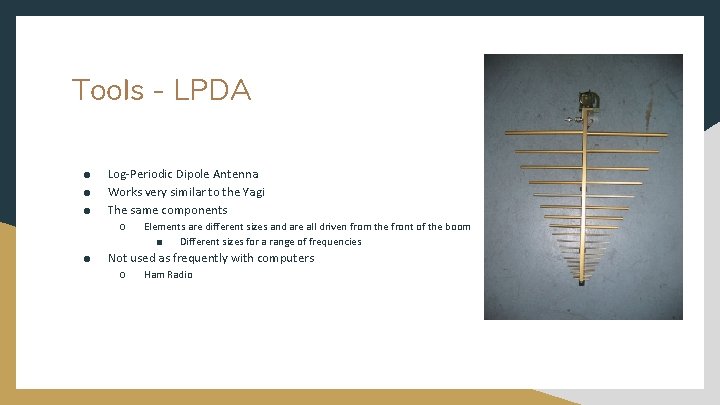
Tools - LPDA ● ● ● Log-Periodic Dipole Antenna Works very similar to the Yagi The same components ○ ● Elements are different sizes and are all driven from the front of the boom ■ Different sizes for a range of frequencies Not used as frequently with computers ○ Ham Radio
Tools - Omnidirectional ● Signal is transmitted or received 360 º around the antenna ● ● The antenna is driven The part that connects to the antenna is ground Can be tuned for different frequencies Less far-reaching than directional
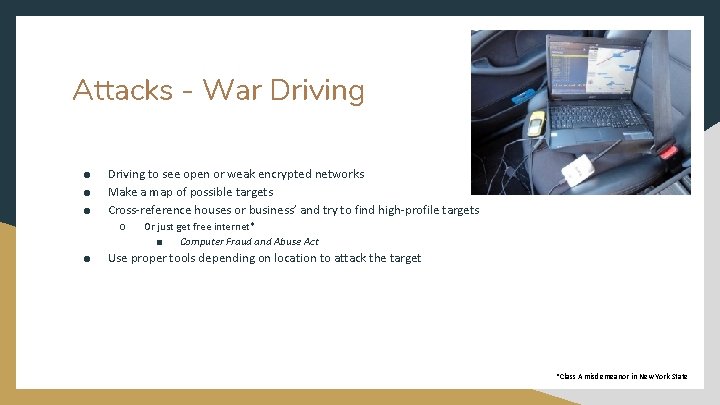
Attacks - War Driving ● ● ● Driving to see open or weak encrypted networks Make a map of possible targets Cross-reference houses or business’ and try to find high-profile targets ○ ● Or just get free internet* ■ Computer Fraud and Abuse Act Use proper tools depending on location to attack the target *Class A misdemeanor in New York State
Attacks - Packet Sniffing ● Wireshark or Aircrack-ng ○ ● Enable Promiscuous Mode ○ ● See traffic that isn’t intended for user’s MAC address Monitor Mode ○ ● Aircrack-ng comes with WEP and WPA cracking tools Check NIC for Monitor Mode Availability Observe plaintext for any useful data ○ ○ ○ Credentials PCI or PII Vulnerabilities
Attacks - Password Cracking ● ● Brute Force Rainbow Tables ○ ○ ● Pass the Hash ○ ○ ● Giving up hard disk space over computing power Common encrypted passwords Sending the hash of a password and being authenticated WPA/WPA 2 WEP Cracking ○ Nearly plaintext
Solutions ● ● Use WPA 2 or more secure and never use WEP Passwords need to be 13+ characters with an upper and lowercase, a number, and a symbol Two factor authentication with active directory Keep access points physically secure ○ ● Keep a watch and CCTV 24/7 for wardriving ○ ● ● ● ● Keep access point’s range at a minimum If suspected - file a police report No Wireless Make the whole building a faraday cage Patch vulnerabilities using tools Local VPN Firewall Segment network Tools - IPS, IDS, Log manager, vulnerability manager
References Anim K, Jung Y-B. Shortened Log-Periodic Dipole Antenna Using Printed Dual-Band Dipole Elements. IEEE Transactions on Antennas & Propagation. 2018; 66(12): 6762 -6771. doi: 10. 1109/TAP. 2018. 2874710. Hal Berghel and Jacob Uecker. 2005. Wi. Fi attack vectors. Commun. ACM 48, 8 (August 2005), 21 -28. DOI: https: //doi-org. rdas-proxy. mercy. edu/10. 1145/1076211. 1076229 Horáleka, Josef, et al. “Analysis of the Use of Rainbow Tables to Break Hash. ” Journal of Intelligent & Fuzzy Systems, vol. 32, no. 2, Feb. 2017, pp. 1523– 1534. EBSCOhost, doi: 10. 3233/JIFS-169147. Mac. Michael, Cmdr. John. “Navy Wireless Networks — FIPS 140 -2 or Bust!” Department of Navy Chief Information Officer - Policy: Acceptable Use of DON Information Technology, Sept. 2005, www. doncio. navy. mil/CHIPS/Article. Details. aspx? ID=3202. NIST. “National Institute of Standards and Technology. ” NIST Special Publication 800 -63 B, 2019, pages. nist. gov/800 -63 -3/sp 800 -63 b. html. Saurav K, Sarkar D, Srivastava K. A dual-band reconfigurable Yagi-Uda antenna with diverse radiation patterns. Applied Physics A: Materials Science & Processing. 2017; 123(7): 1 -8. doi: 10. 1007/s 00339 -017 -1087 -y. Scalisi, Michael. “Analyze Network Problems With Wireshark. ” PCWorld, vol. 28, no. 4, Apr. 2010, p. 30. EBSCOhost, search. ebscohost. com/login. aspx? direct=true&db=aph&AN=48752878&site=ehost-live Simmonds M. Beware the drive-by attack. Computer Fraud & Security. 2016; 2016(10): 19 -20. doi: 10. 1016/S 1361 -3723(16)30083 -5.