Wireless LAN Infrastructure Devices Dahlan Abdullah Email dahlanunimal
Wireless LAN Infrastructure Devices Dahlan Abdullah Email : dahlan@unimal. ac. id Web: http: //www. dahlan. web. id
Access Point
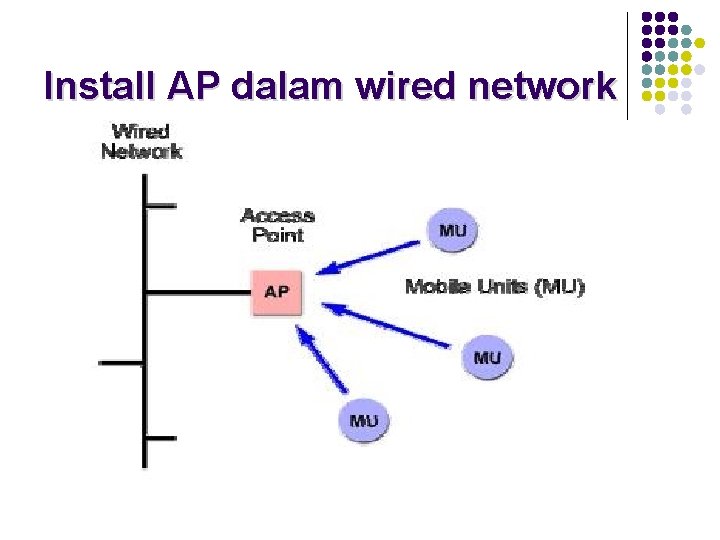
Install AP dalam wired network
3 Mode Konfigurasi AP l l l Root Mode Repeater Mode Bridge Mode
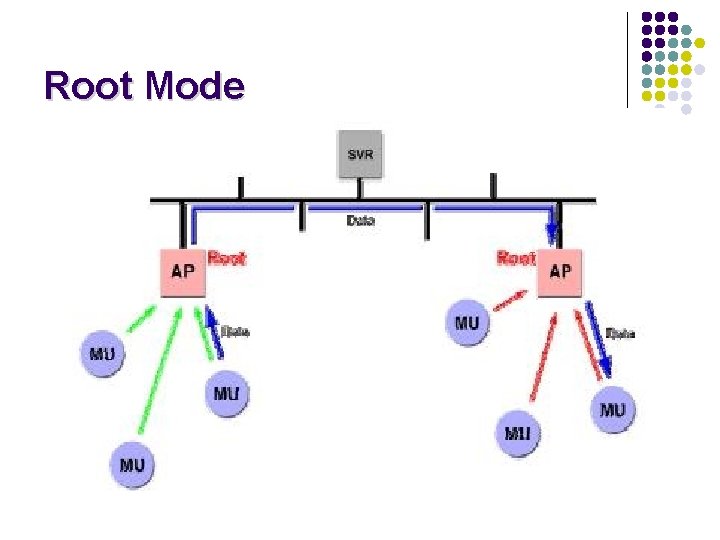
Root Mode
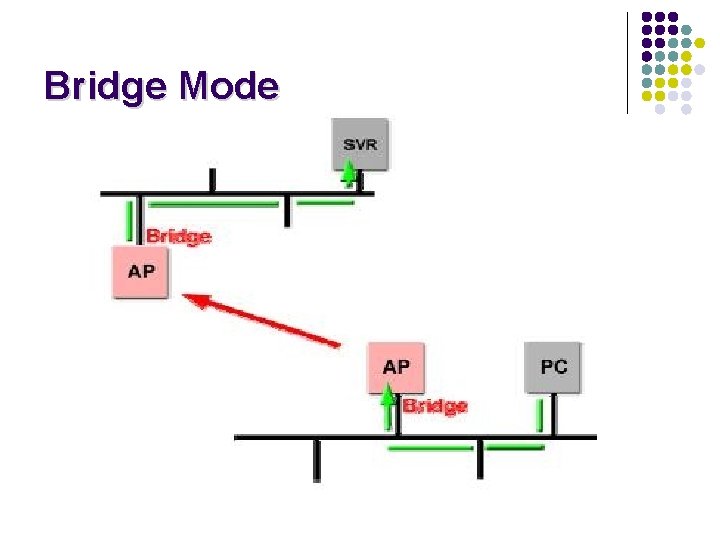
Bridge Mode
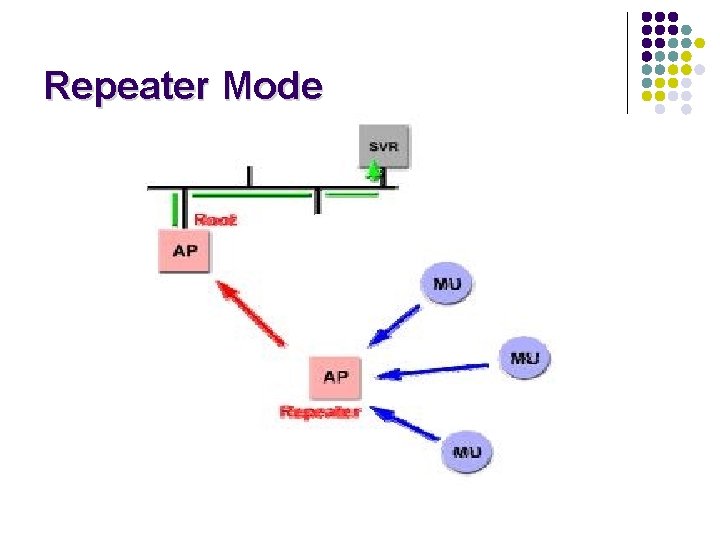
Repeater Mode
Wireless Bridge
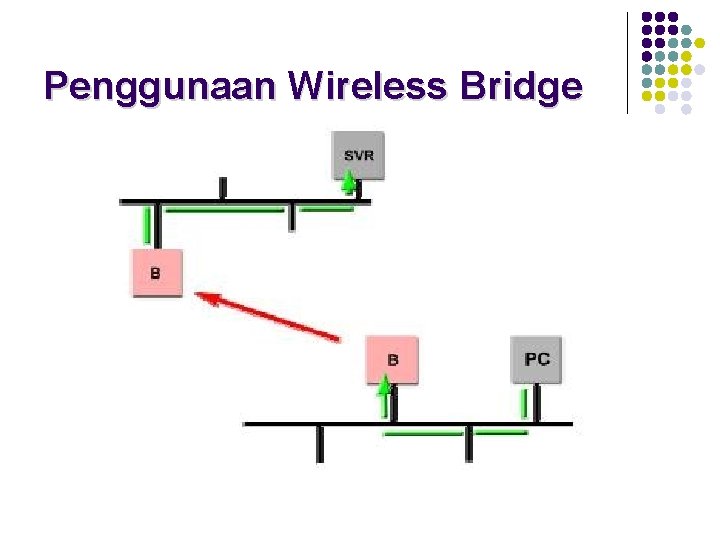
Penggunaan Wireless Bridge
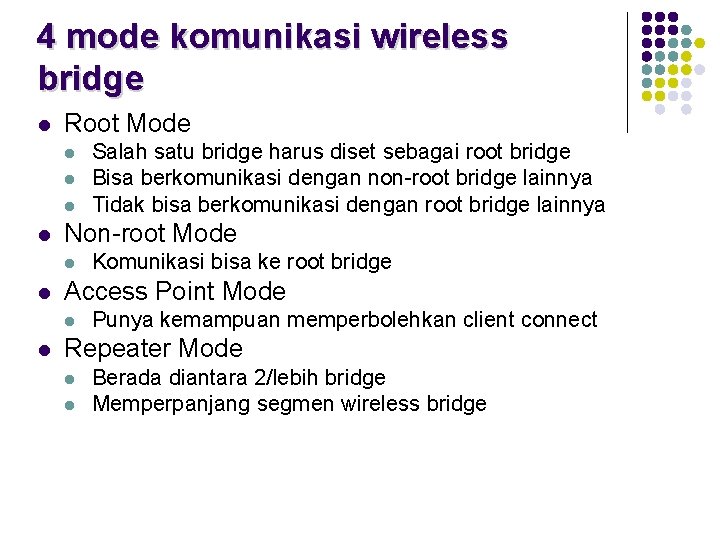
4 mode komunikasi wireless bridge l Root Mode l l Non-root Mode l l Komunikasi bisa ke root bridge Access Point Mode l l Salah satu bridge harus diset sebagai root bridge Bisa berkomunikasi dengan non-root bridge lainnya Tidak bisa berkomunikasi dengan root bridge lainnya Punya kemampuan memperbolehkan client connect Repeater Mode l l Berada diantara 2/lebih bridge Memperpanjang segmen wireless bridge
Peralatan yang berhubungan dengan wireless bridge l l l Fixed or Detachable Antennas Advanced Filtering Capabilities Removable (modular) Radio cards Variable Output Power Varied Types of Wired Connectivity

Wireless Workgroup Bridges
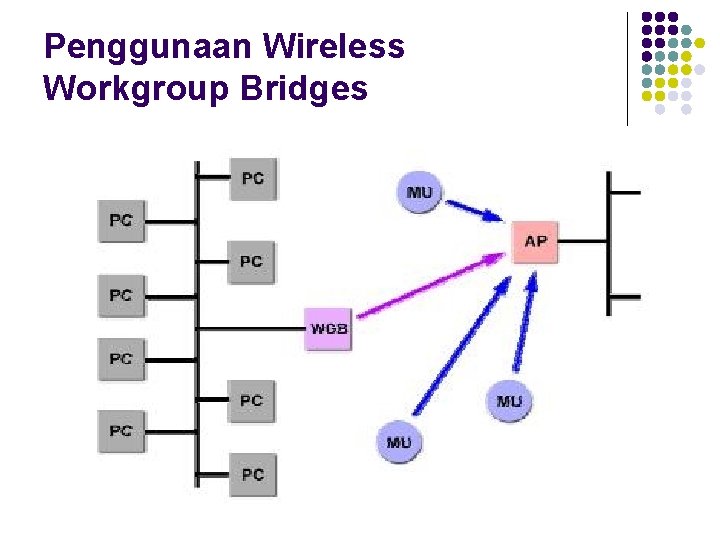
Penggunaan Wireless Workgroup Bridges
Wireless LAN client devices l l PCMCIA & compact flash cards Ethernet & serial converters USB Adapters PCI & ISA Adapters
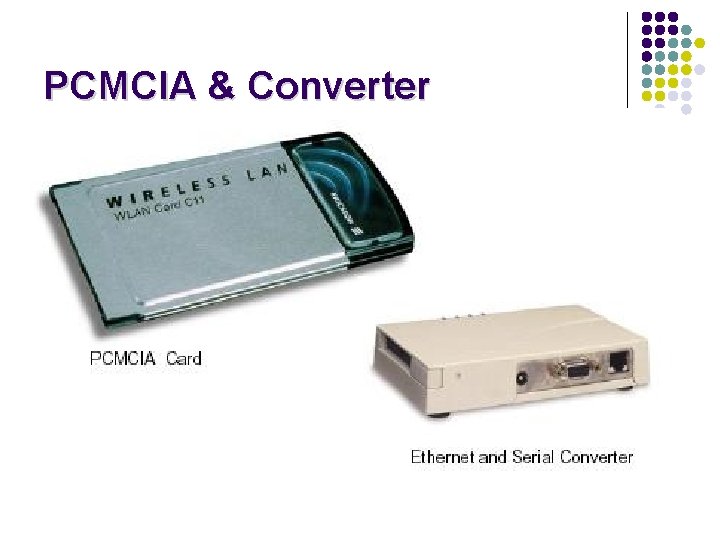
PCMCIA & Converter

Wireless Adapters
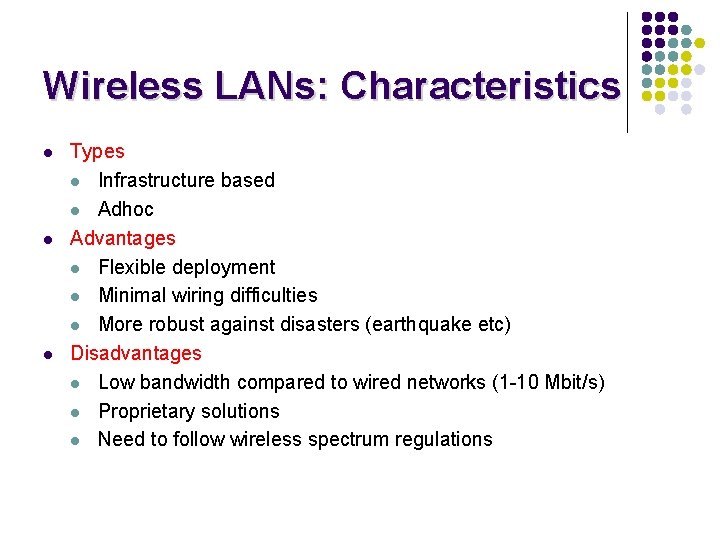
Wireless LANs: Characteristics l l l Types l Infrastructure based l Adhoc Advantages l Flexible deployment l Minimal wiring difficulties l More robust against disasters (earthquake etc) Disadvantages l Low bandwidth compared to wired networks (1 -10 Mbit/s) l Proprietary solutions l Need to follow wireless spectrum regulations
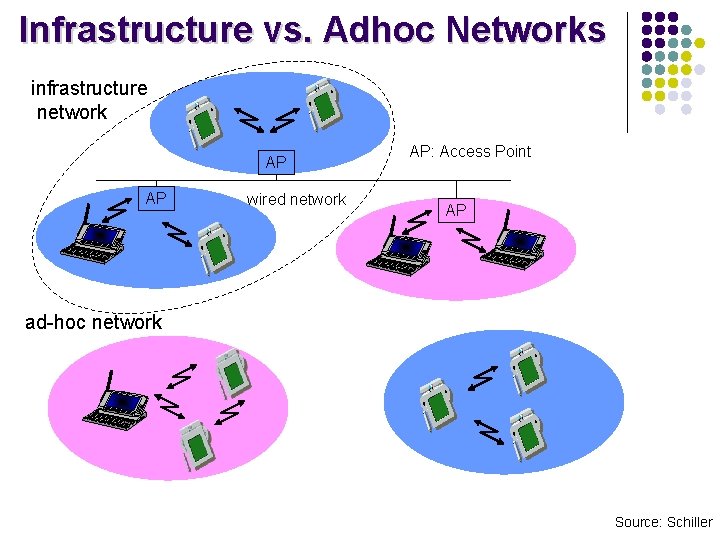
Infrastructure vs. Adhoc Networks infrastructure network AP AP wired network AP: Access Point AP ad-hoc network Source: Schiller
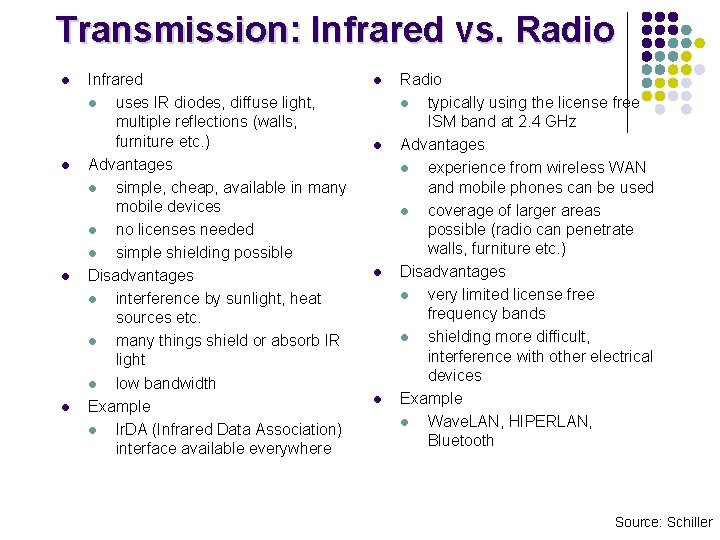
Transmission: Infrared vs. Radio l l Infrared l uses IR diodes, diffuse light, multiple reflections (walls, furniture etc. ) Advantages l simple, cheap, available in many mobile devices l no licenses needed l simple shielding possible Disadvantages l interference by sunlight, heat sources etc. l many things shield or absorb IR light l low bandwidth Example l Ir. DA (Infrared Data Association) interface available everywhere l l Radio l typically using the license free ISM band at 2. 4 GHz Advantages l experience from wireless WAN and mobile phones can be used l coverage of larger areas possible (radio can penetrate walls, furniture etc. ) Disadvantages l very limited license frequency bands l shielding more difficult, interference with other electrical devices Example l Wave. LAN, HIPERLAN, Bluetooth Source: Schiller
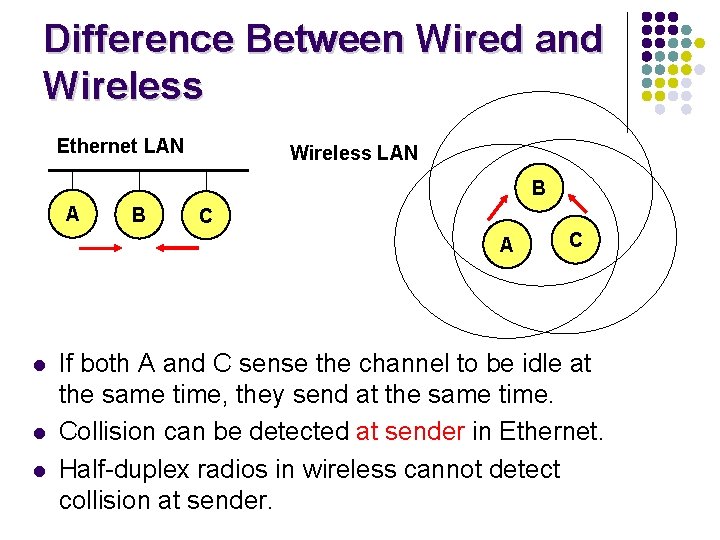
Difference Between Wired and Wireless Ethernet LAN Wireless LAN B A B C A l l l C If both A and C sense the channel to be idle at the same time, they send at the same time. Collision can be detected at sender in Ethernet. Half-duplex radios in wireless cannot detect collision at sender.
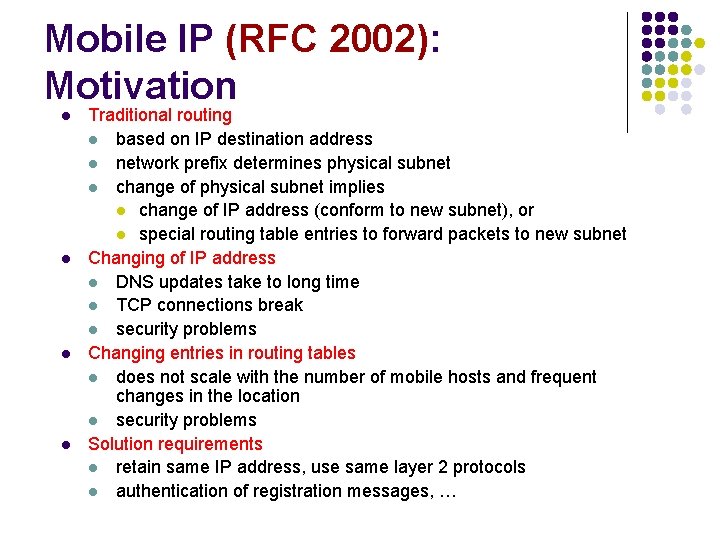
Mobile IP (RFC 2002): Motivation l l Traditional routing l based on IP destination address l network prefix determines physical subnet l change of physical subnet implies l change of IP address (conform to new subnet), or l special routing table entries to forward packets to new subnet Changing of IP address l DNS updates take to long time l TCP connections break l security problems Changing entries in routing tables l does not scale with the number of mobile hosts and frequent changes in the location l security problems Solution requirements l retain same IP address, use same layer 2 protocols l authentication of registration messages, …
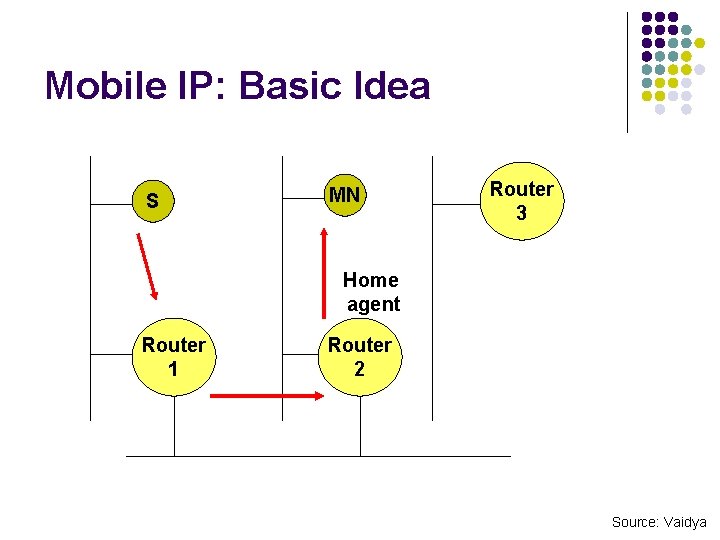
Mobile IP: Basic Idea S MN Router 3 Home agent Router 1 Router 2 Source: Vaidya
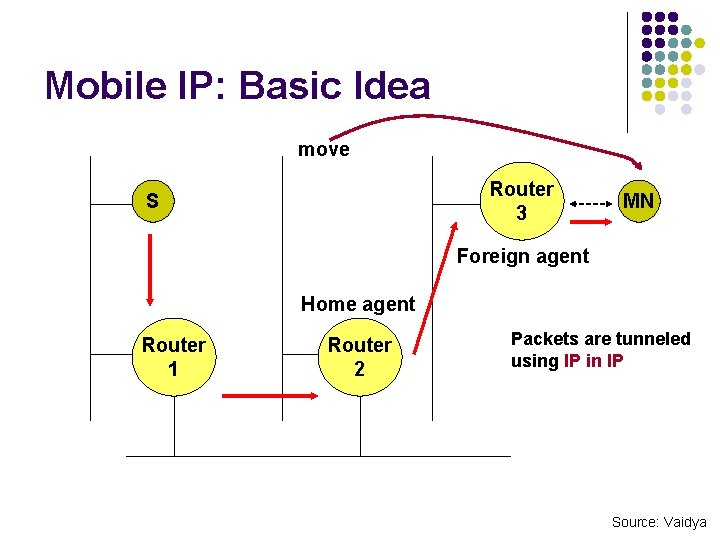
Mobile IP: Basic Idea move Router 3 S MN Foreign agent Home agent Router 1 Router 2 Packets are tunneled using IP in IP Source: Vaidya
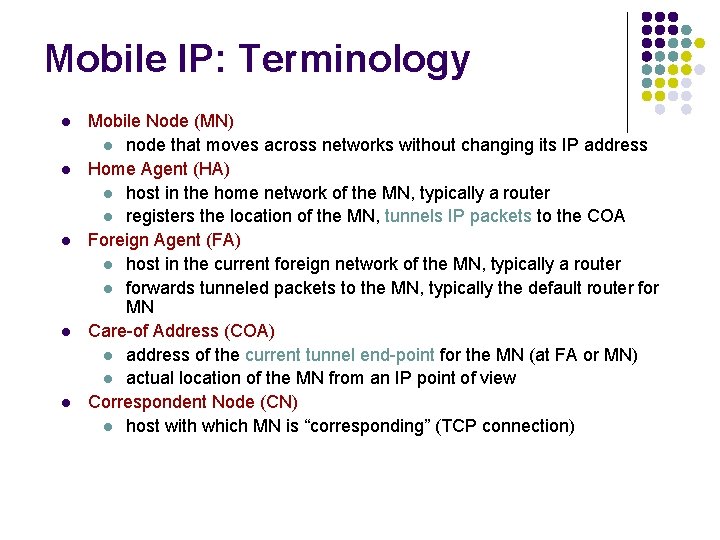
Mobile IP: Terminology l l l Mobile Node (MN) l node that moves across networks without changing its IP address Home Agent (HA) l host in the home network of the MN, typically a router l registers the location of the MN, tunnels IP packets to the COA Foreign Agent (FA) l host in the current foreign network of the MN, typically a router l forwards tunneled packets to the MN, typically the default router for MN Care-of Address (COA) l address of the current tunnel end-point for the MN (at FA or MN) l actual location of the MN from an IP point of view Correspondent Node (CN) l host with which MN is “corresponding” (TCP connection)
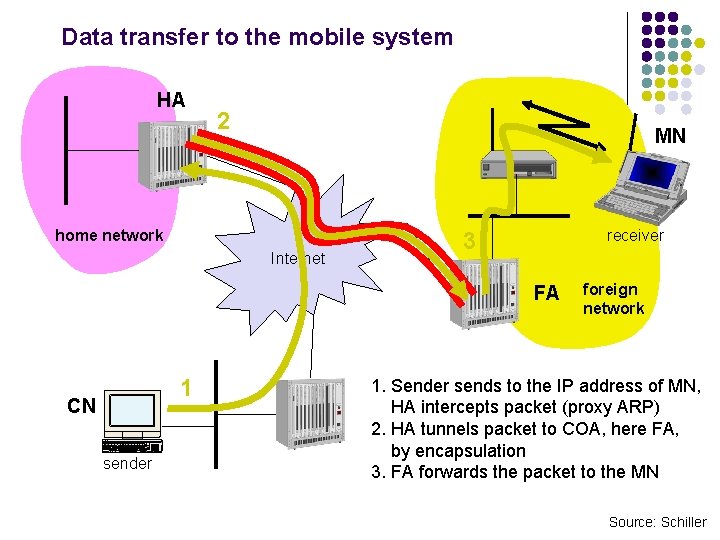
Data transfer to the mobile system HA 2 MN home network Internet receiver 3 FA 1 CN sender foreign network 1. Sender sends to the IP address of MN, HA intercepts packet (proxy ARP) 2. HA tunnels packet to COA, here FA, by encapsulation 3. FA forwards the packet to the MN Source: Schiller
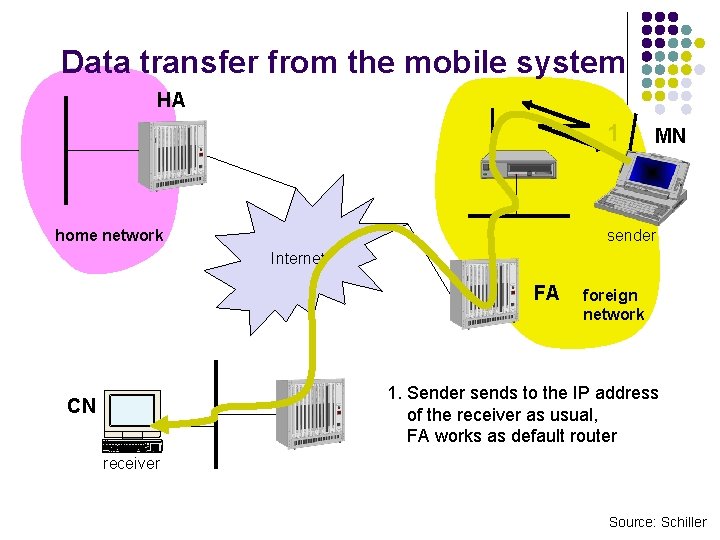
Data transfer from the mobile system HA 1 home network MN sender Internet FA foreign network 1. Sender sends to the IP address of the receiver as usual, FA works as default router CN receiver Source: Schiller
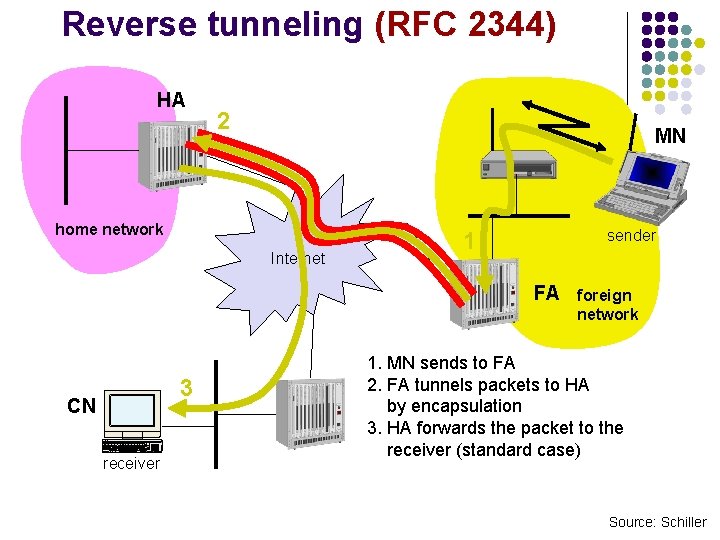
Reverse tunneling (RFC 2344) HA 2 MN home network Internet sender 1 FA 3 CN receiver foreign network 1. MN sends to FA 2. FA tunnels packets to HA by encapsulation 3. HA forwards the packet to the receiver (standard case) Source: Schiller
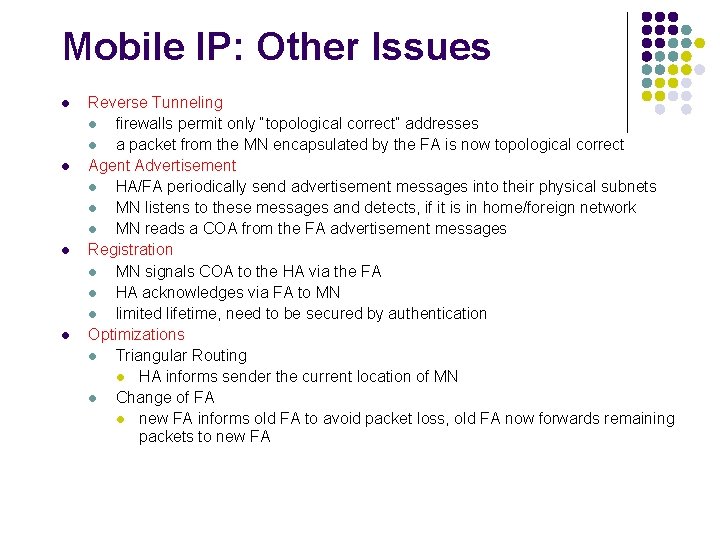
Mobile IP: Other Issues l l Reverse Tunneling l firewalls permit only “topological correct“ addresses l a packet from the MN encapsulated by the FA is now topological correct Agent Advertisement l HA/FA periodically send advertisement messages into their physical subnets l MN listens to these messages and detects, if it is in home/foreign network l MN reads a COA from the FA advertisement messages Registration l MN signals COA to the HA via the FA l HA acknowledges via FA to MN l limited lifetime, need to be secured by authentication Optimizations l Triangular Routing l HA informs sender the current location of MN l Change of FA l new FA informs old FA to avoid packet loss, old FA now forwards remaining packets to new FA
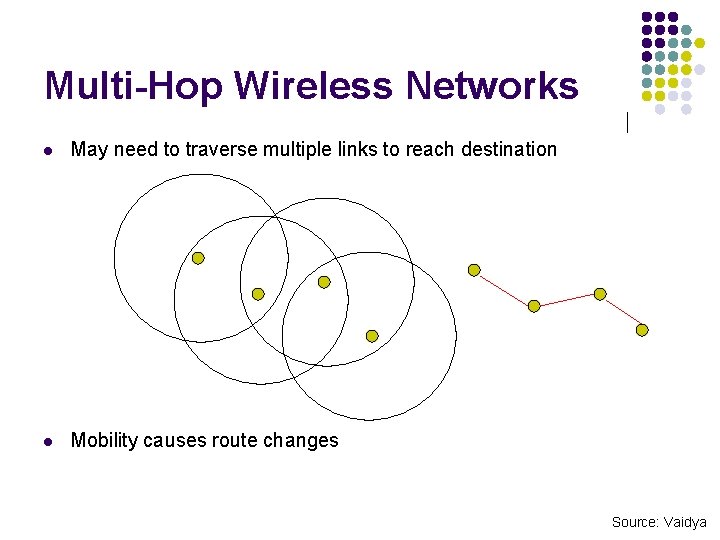
Multi-Hop Wireless Networks l May need to traverse multiple links to reach destination l Mobility causes route changes Source: Vaidya
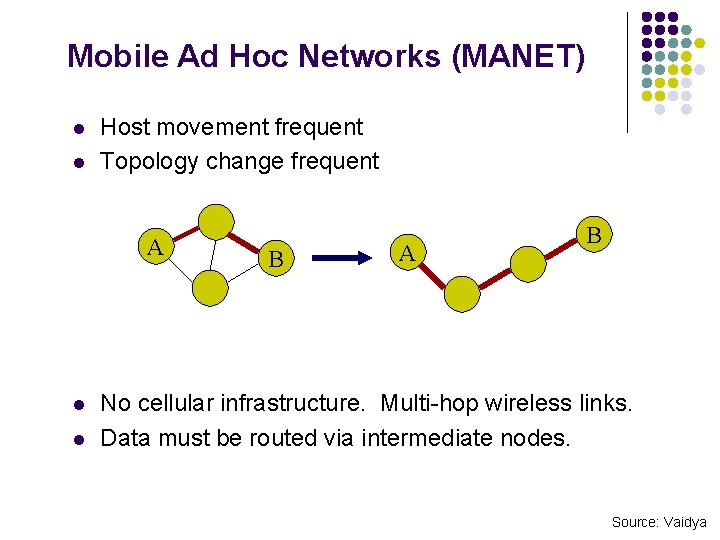
Mobile Ad Hoc Networks (MANET) l l Host movement frequent Topology change frequent A l l B A B No cellular infrastructure. Multi-hop wireless links. Data must be routed via intermediate nodes. Source: Vaidya
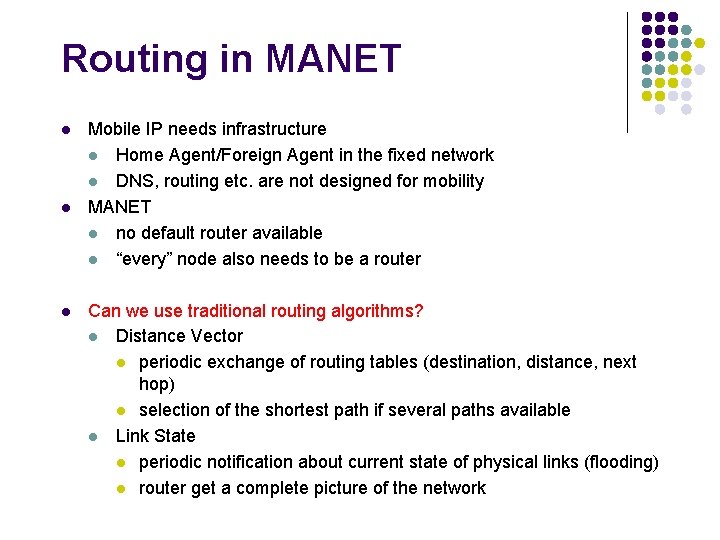
Routing in MANET l l l Mobile IP needs infrastructure l Home Agent/Foreign Agent in the fixed network l DNS, routing etc. are not designed for mobility MANET l no default router available l “every” node also needs to be a router Can we use traditional routing algorithms? l Distance Vector l periodic exchange of routing tables (destination, distance, next hop) l selection of the shortest path if several paths available l Link State l periodic notification about current state of physical links (flooding) l router get a complete picture of the network
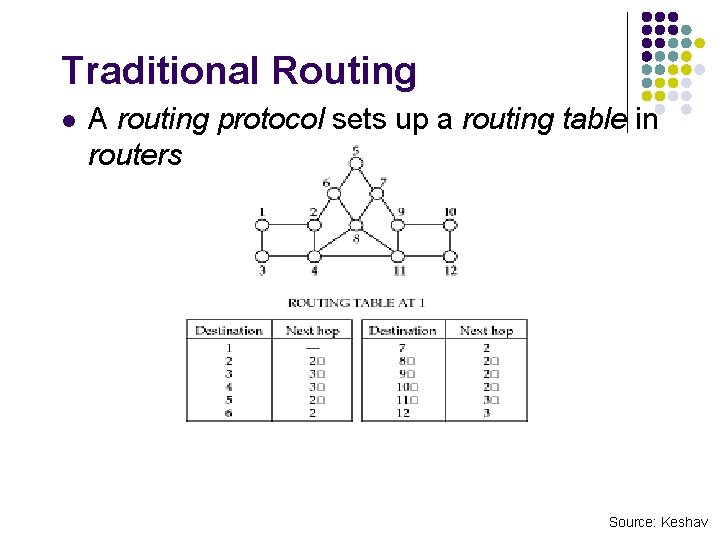
Traditional Routing l A routing protocol sets up a routing table in routers Source: Keshav
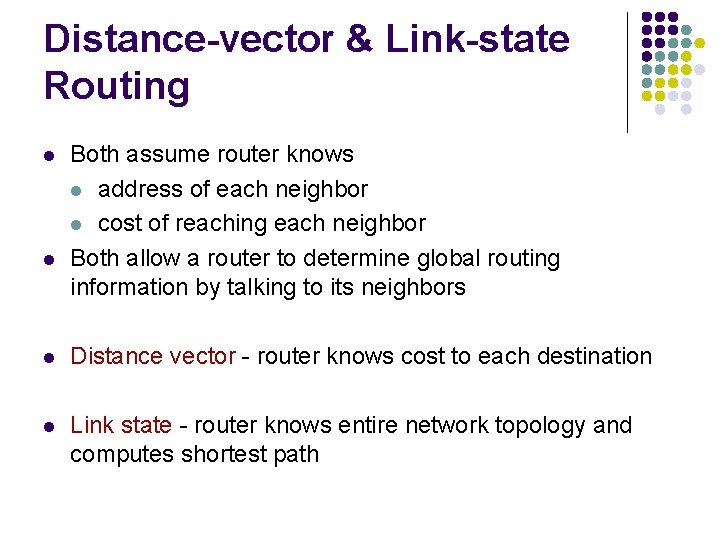
Distance-vector & Link-state Routing l l Both assume router knows l address of each neighbor l cost of reaching each neighbor Both allow a router to determine global routing information by talking to its neighbors l Distance vector - router knows cost to each destination l Link state - router knows entire network topology and computes shortest path
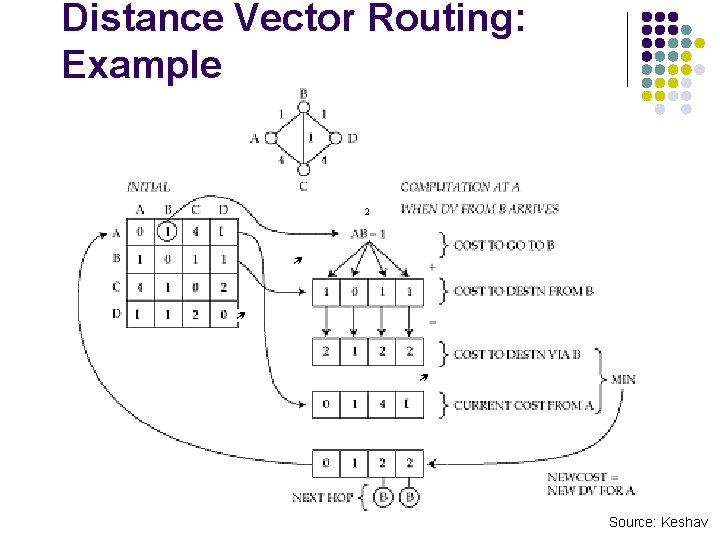
Distance Vector Routing: Example 2 Source: Keshav
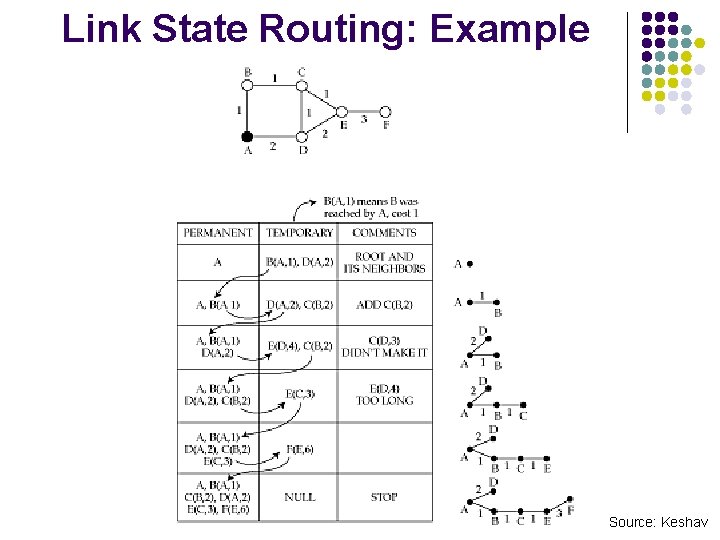
Link State Routing: Example Source: Keshav
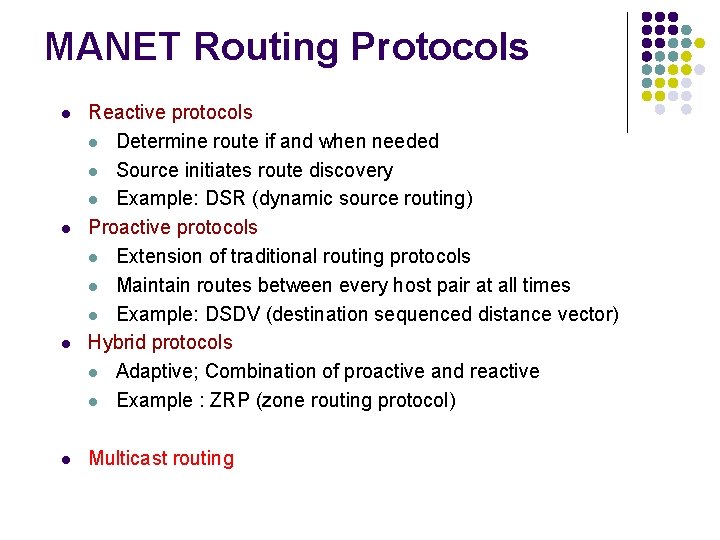
MANET Routing Protocols l l Reactive protocols l Determine route if and when needed l Source initiates route discovery l Example: DSR (dynamic source routing) Proactive protocols l Extension of traditional routing protocols l Maintain routes between every host pair at all times l Example: DSDV (destination sequenced distance vector) Hybrid protocols l Adaptive; Combination of proactive and reactive l Example : ZRP (zone routing protocol) Multicast routing
![Dynamic Source Routing (DSR) [Johnson 96] l l l l l When source S Dynamic Source Routing (DSR) [Johnson 96] l l l l l When source S](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-37.jpg)
Dynamic Source Routing (DSR) [Johnson 96] l l l l l When source S wants to send a packet to destination D, but does not know a route to D, S initiates a route discovery S floods Route Request (RREQ) Each node appends its own identifier when forwarding RREQ D on receiving the first RREQ, sends a Route Reply (RREP) RREP sent on route obtained by reversing the route appended in RREQ RREP includes the route from S to D, on which RREQ was received by D S on receiving RREP, caches the route included in the RREP When S sends a data packet to D, entire route is included in the header Intermediate nodes use the source route in the packet header to determine to whom a packet should be forwarded
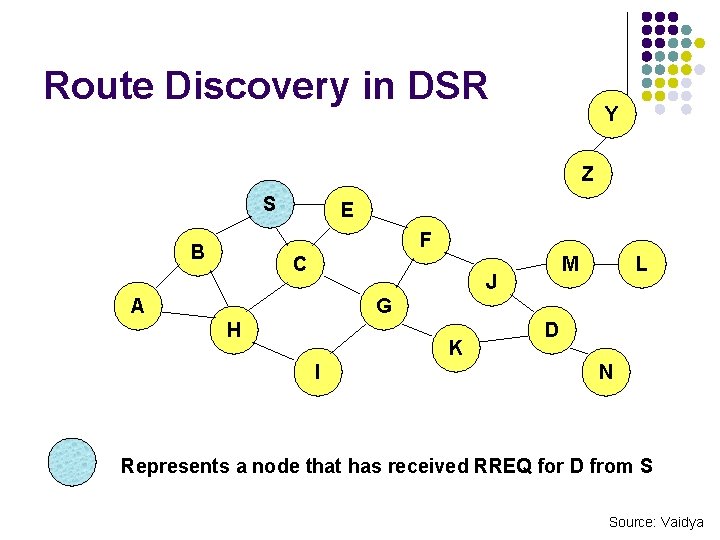
Route Discovery in DSR Y Z S E F B C M J A L G H K I D N Represents a node that has received RREQ for D from S Source: Vaidya
![Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-39.jpg)
Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C M J A L G H K I D N Represents transmission of RREQ [X, Y] Represents list of identifiers appended to RREQ
![Route Discovery in DSR S E Y Z [S, E] F B C A Route Discovery in DSR S E Y Z [S, E] F B C A](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-40.jpg)
Route Discovery in DSR S E Y Z [S, E] F B C A M J [S, C] H G K I L D N • Node H receives packet RREQ from two neighbors: potential for collision
![Route Discovery in DSR Y Z S E F B [S, E, F] C Route Discovery in DSR Y Z S E F B [S, E, F] C](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-41.jpg)
Route Discovery in DSR Y Z S E F B [S, E, F] C M J A L G H I [S, C, G] K D N • Node C receives RREQ from G and H, but does not forward it again, because node C has already forwarded RREQ once
![Route Discovery in DSR Y Z S E [S, E, F, J] F B Route Discovery in DSR Y Z S E [S, E, F, J] F B](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-42.jpg)
Route Discovery in DSR Y Z S E [S, E, F, J] F B C M J A L G H K I D [S, C, G, K] • Nodes J and K both broadcast RREQ to node D • Since nodes J and K are hidden from each other, their transmissions may collide N
![Route Discovery in DSR Y Z S E [S, E, F, J, M] F Route Discovery in DSR Y Z S E [S, E, F, J, M] F](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-43.jpg)
Route Discovery in DSR Y Z S E [S, E, F, J, M] F B C M J A L G H K D I • Node D does not forward RREQ, because node D is the intended target of the route discovery N
![Route Reply in DSR S E Y Z RREP [S, E, F, J, D] Route Reply in DSR S E Y Z RREP [S, E, F, J, D]](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-44.jpg)
Route Reply in DSR S E Y Z RREP [S, E, F, J, D] F B C M J A L G H K I Represents RREP control message D N
![Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-45.jpg)
Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E F B C M J A L G H K I Packet header size grows with route length D N
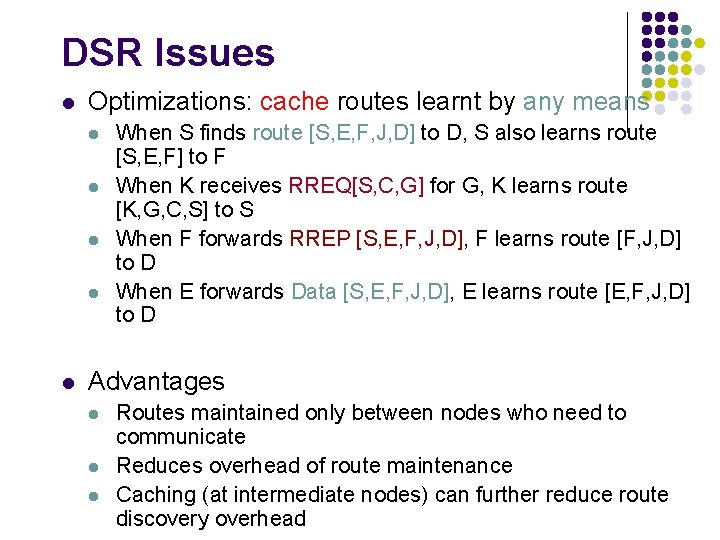
DSR Issues l Optimizations: cache routes learnt by any means l l l When S finds route [S, E, F, J, D] to D, S also learns route [S, E, F] to F When K receives RREQ[S, C, G] for G, K learns route [K, G, C, S] to S When F forwards RREP [S, E, F, J, D], F learns route [F, J, D] to D When E forwards Data [S, E, F, J, D], E learns route [E, F, J, D] to D Advantages l l l Routes maintained only between nodes who need to communicate Reduces overhead of route maintenance Caching (at intermediate nodes) can further reduce route discovery overhead
![Destination-Sequenced Distance-Vector (DSDV) [Perkins 94 Sigcomm] l l l Each node maintains a routing Destination-Sequenced Distance-Vector (DSDV) [Perkins 94 Sigcomm] l l l Each node maintains a routing](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-47.jpg)
Destination-Sequenced Distance-Vector (DSDV) [Perkins 94 Sigcomm] l l l Each node maintains a routing table which stores l next hop, cost metric towards each destination l a sequence number that is created by the destination itself Each node periodically forwards routing table to neighbors l Each node increments and appends its sequence number when sending its local routing table Each route is tagged with a sequence number; routes with greater sequence numbers are preferred Each node advertises a monotonically increasing even sequence number for itself When a node decides that a route is broken, it increments the sequence number of the route and advertises it with infinite metric Destination advertises new sequence number
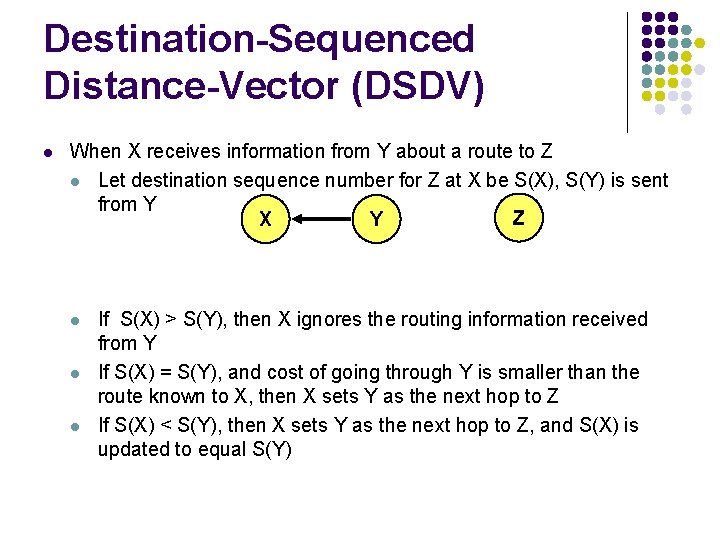
Destination-Sequenced Distance-Vector (DSDV) l When X receives information from Y about a route to Z l Let destination sequence number for Z at X be S(X), S(Y) is sent from Y Z X Y l l l If S(X) > S(Y), then X ignores the routing information received from Y If S(X) = S(Y), and cost of going through Y is smaller than the route known to X, then X sets Y as the next hop to Z If S(X) < S(Y), then X sets Y as the next hop to Z, and S(X) is updated to equal S(Y)
Reactive v/s Proactive Tradeoffs l Reactive protocols l Lower overhead since routes are determined on demand l Significant delay in route determination l Employ flooding (global search) l Control traffic may be bursty l Proactive protocols l Always maintain routes l Little or no delay for route determination l Consume bandwidth to keep routes up-to-date l Maintain routes which may never be used l Which approach achieves a better trade-off depends on the traffic and mobility patterns
![Zone Routing Protocol (ZRP) [Haas 98] l ZRP combines proactive and reactive approaches l Zone Routing Protocol (ZRP) [Haas 98] l ZRP combines proactive and reactive approaches l](http://slidetodoc.com/presentation_image_h2/8cc73ca4df358e7d3bf584562267503f/image-50.jpg)
Zone Routing Protocol (ZRP) [Haas 98] l ZRP combines proactive and reactive approaches l All nodes within hop distance at most d from a node X are said to be in the routing zone of node X All nodes at hop distance exactly d are said to be peripheral nodes of node X’s routing zone l l l Intra-zone routing: Proactively maintain routes to all nodes within the source node’s own zone. Inter-zone routing: Use an on-demand protocol (similar to DSR or AODV) to determine routes to outside zone.
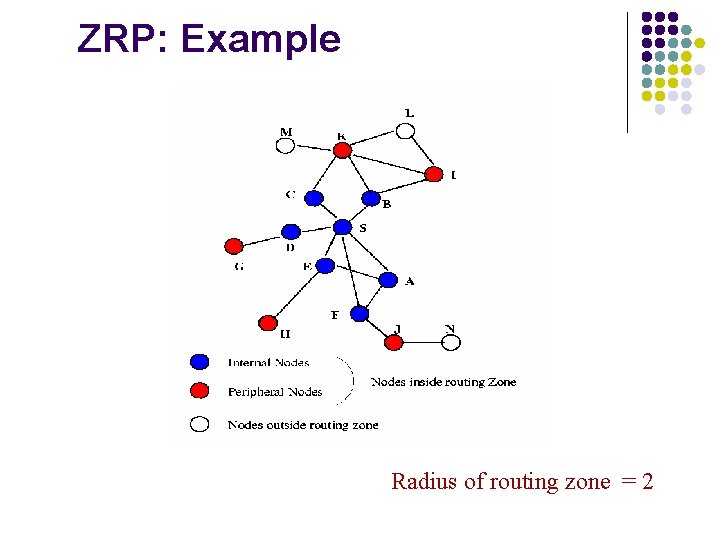
ZRP: Example Radius of routing zone = 2
SELESAI … TERIMA KASIH
- Slides: 52