Wireless and Mobile AllIP Networks YiBing Lin linycsie
Wireless and Mobile All-IP Networks Yi-Bing Lin liny@csie. nctu. edu. tw 1
From Traditional Telecom to All-IP n n n Circuit-Switched vs Packet-Switched: Intelligent Network (IN) vs. IP Multimedia Core Network Subsystem (IMS) Example: Video Phone All-IP Telecom Services : New Technologies vs. New Services Vo. IP: Numbering, Number Portability Service Creation: Dictatorship vs. Democracy Peer-to-Peer, Web 2. 0 2
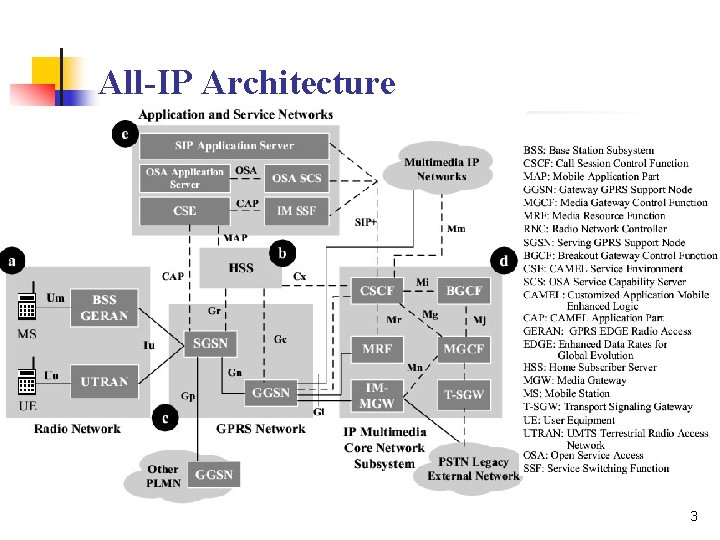
All-IP Architecture 3

4
5
6
Issues on Mobile All-IP Network n n Short Message Service (SMS) and IP Network Integration SMS is considered as the application level signaling mechanism. Session Management PDP context is introduced. 7
Issue: Mobility Management n n n GSM: Location Area (LA) tracking GPRS: Routing Area (RA), cell tracking UMTS: RA, UTRAN RA (URA), cell tracking Performance of Mobile Telecommunications Network with Overlapping Location Area Configuration. Accepted and to appear in IEEE Transactions on Vehicular Technology) 8
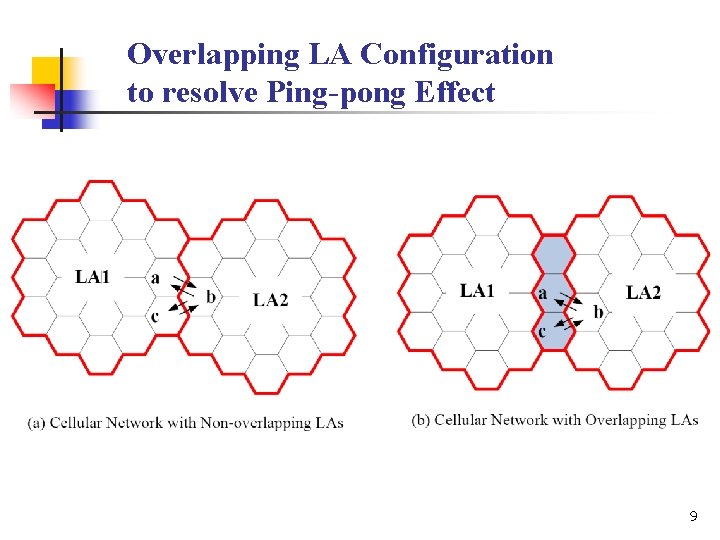
Overlapping LA Configuration to resolve Ping-pong Effect 9
![The expected number E[M] of cell movement in an LA N: LA size; K: The expected number E[M] of cell movement in an LA N: LA size; K:](http://slidetodoc.com/presentation_image_h/7e476897942a7bca5e50c2b8fb5ccbb6/image-10.jpg)
The expected number E[M] of cell movement in an LA N: LA size; K: overlay degree p: probability of moving direction 10
Issues on Mobile All-IP Network (Cont. ) n n Mobile Core Networks that Support All-IP: UMTS: GPRS cdma 2000: PDSN (Packet Data Support Node) Mobile All-IP Network Signaling Traditional: SS 7 is supported by MTP (Message Transfer Part) All-IP: SS 7 is supported by SCTP (Stream Control Transport Protocol) 11
Issue: On-line Charging Sou, S. -I. , Hung, H. -N. , Lin, Y. -B. , Peng, N. -F. , and Jeng, J. -Y. Modeling Credit Reservation Procedure for UMTS Online Charging System. Accept and to appear in IEEE Transactions on Wireless Communications. n n n The Online Charging System (OCS) determines the rating and allocates the granted credit units to the IMS prepaid services. The prepaid credit units are deducted at the OCS in real time when the prepaid service is delivered. When the amount of the remaining prepaid credit is below a threshold, the OCS reminds the user to recharge the prepaid account. Issue: It is essential to choose an appropriate recharge threshold to reduce the probability that the in-progress service sessions are forced-terminated. 12
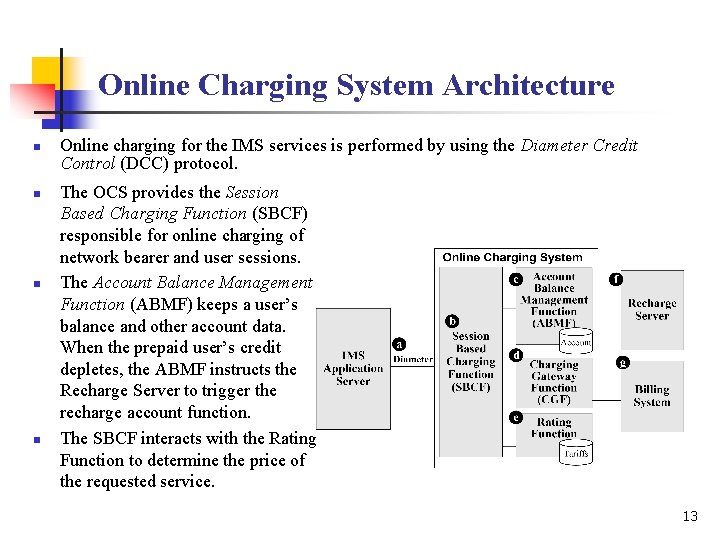
Online Charging System Architecture n n Online charging for the IMS services is performed by using the Diameter Credit Control (DCC) protocol. The OCS provides the Session Based Charging Function (SBCF) responsible for online charging of network bearer and user sessions. The Account Balance Management Function (ABMF) keeps a user’s balance and other account data. When the prepaid user’s credit depletes, the ABMF instructs the Recharge Server to trigger the recharge account function. The SBCF interacts with the Rating Function to determine the price of the requested service. 13
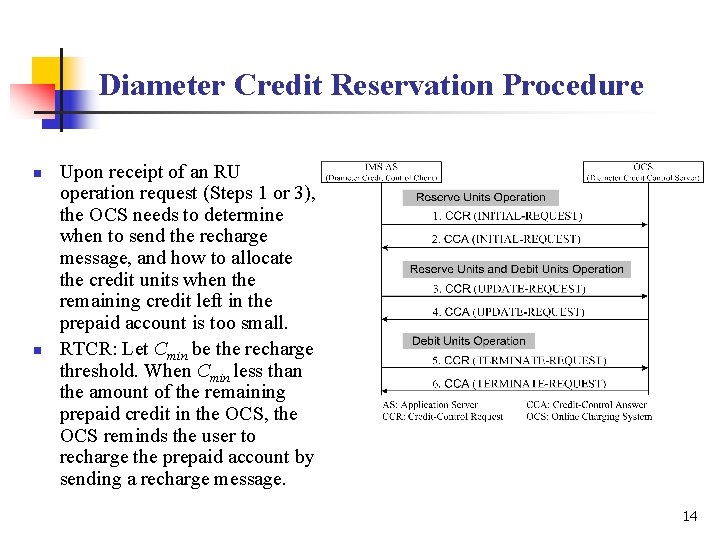
Diameter Credit Reservation Procedure n n Upon receipt of an RU operation request (Steps 1 or 3), the OCS needs to determine when to send the recharge message, and how to allocate the credit units when the remaining credit left in the prepaid account is too small. RTCR: Let Cmin be the recharge threshold. When Cmin less than the amount of the remaining prepaid credit in the OCS, the OCS reminds the user to recharge the prepaid account by sending a recharge message. 14
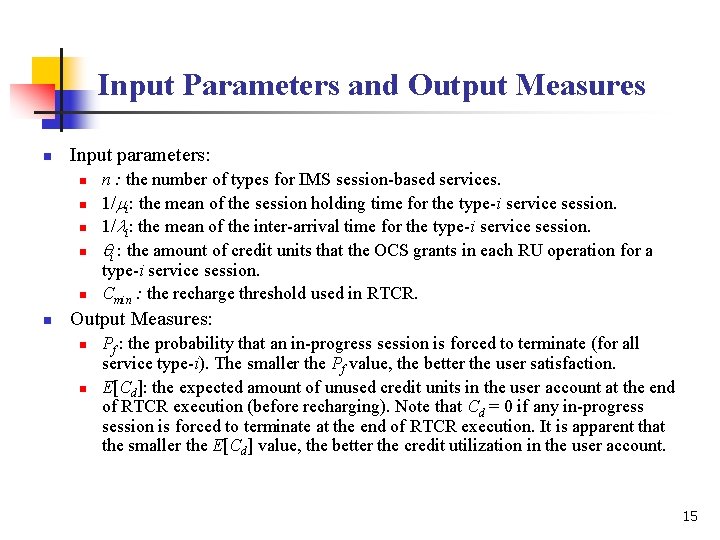
Input Parameters and Output Measures n Input parameters: n n n n : the number of types for IMS session-based services. 1/mi: the mean of the session holding time for the type-i service session. 1/li: the mean of the inter-arrival time for the type-i service session. qi : the amount of credit units that the OCS grants in each RU operation for a type-i service session. Cmin : the recharge threshold used in RTCR. Output Measures: n n Pf : the probability that an in-progress session is forced to terminate (for all service type-i). The smaller the Pf value, the better the user satisfaction. E[Cd]: the expected amount of unused credit units in the user account at the end of RTCR execution (before recharging). Note that Cd = 0 if any in-progress session is forced to terminate at the end of RTCR execution. It is apparent that the smaller the E[Cd] value, the better the credit utilization in the user account. 15
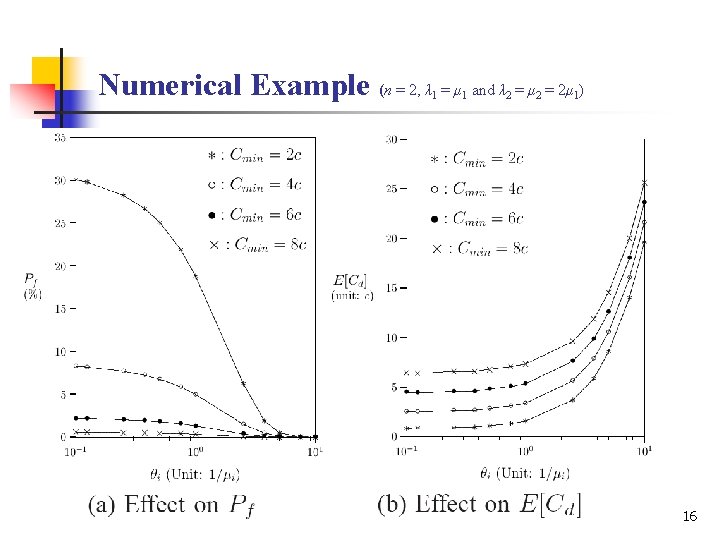
Numerical Example (n = 2, λ = μ and λ = μ = 2μ ) 1 1 2 2 1 16
Issue: UMTS Security Virus, fraudulent Usage, Redundant Authentication Eavesdropping through Mobile Phone Y. -B. Lin and M. -H. Tsai, Eavesdropping through Mobile Phone. Accepted and to appear in IEEE Transactions on Vehicular Technology. 17
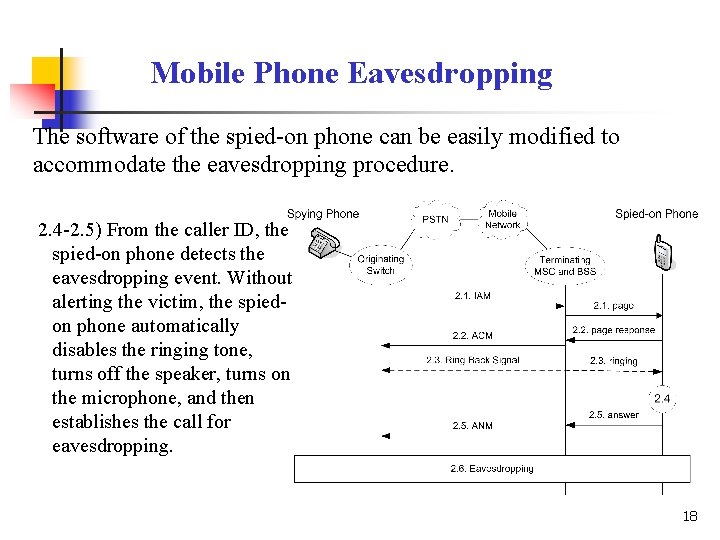
Mobile Phone Eavesdropping The software of the spied-on phone can be easily modified to accommodate the eavesdropping procedure. 2. 4 -2. 5) From the caller ID, the spied-on phone detects the eavesdropping event. Without alerting the victim, the spiedon phone automatically disables the ringing tone, turns off the speaker, turns on the microphone, and then establishes the call for eavesdropping. 18
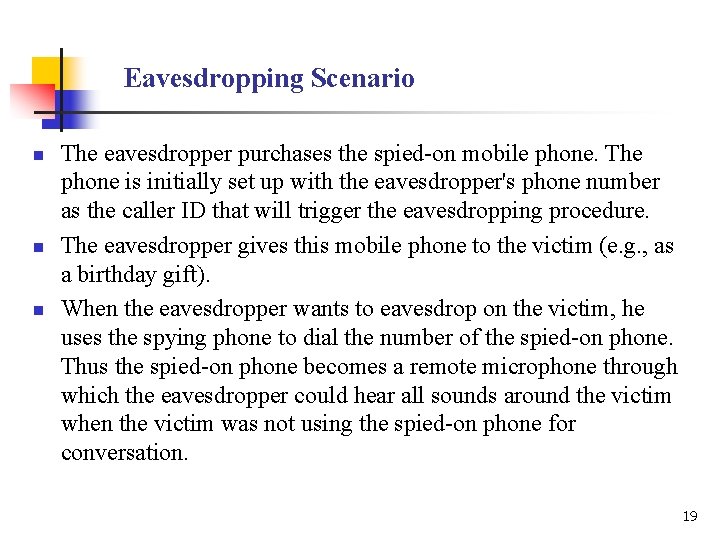
Eavesdropping Scenario n n n The eavesdropper purchases the spied-on mobile phone. The phone is initially set up with the eavesdropper's phone number as the caller ID that will trigger the eavesdropping procedure. The eavesdropper gives this mobile phone to the victim (e. g. , as a birthday gift). When the eavesdropper wants to eavesdrop on the victim, he uses the spying phone to dial the number of the spied-on phone. Thus the spied-on phone becomes a remote microphone through which the eavesdropper could hear all sounds around the victim when the victim was not using the spied-on phone for conversation. 19
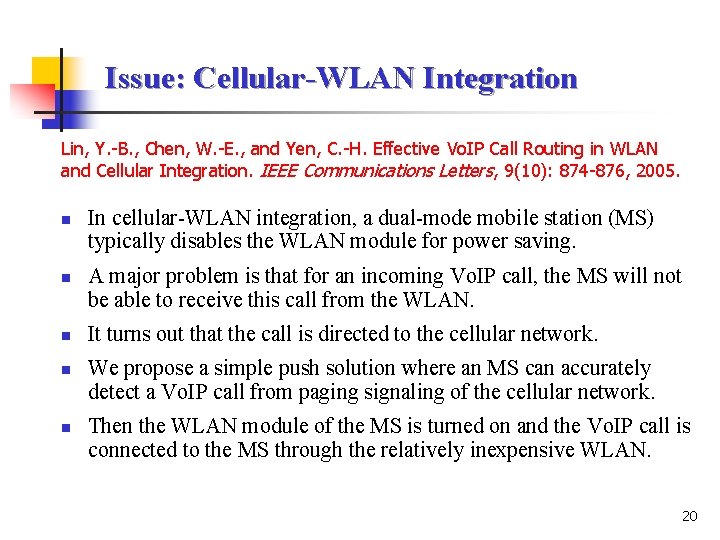
Issue: Cellular-WLAN Integration Lin, Y. -B. , Chen, W. -E. , and Yen, C. -H. Effective Vo. IP Call Routing in WLAN and Cellular Integration. IEEE Communications Letters, 9(10): 874 -876, 2005. n n n In cellular-WLAN integration, a dual-mode mobile station (MS) typically disables the WLAN module for power saving. A major problem is that for an incoming Vo. IP call, the MS will not be able to receive this call from the WLAN. It turns out that the call is directed to the cellular network. We propose a simple push solution where an MS can accurately detect a Vo. IP call from paging signaling of the cellular network. Then the WLAN module of the MS is turned on and the Vo. IP call is connected to the MS through the relatively inexpensive WLAN. 20
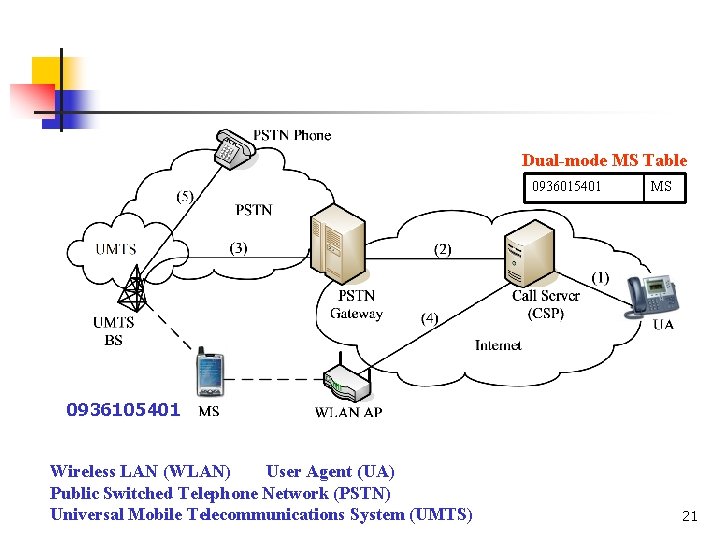
Dual-mode MS Table 0936015401 MS 0936105401 Wireless LAN (WLAN) User Agent (UA) Public Switched Telephone Network (PSTN) Universal Mobile Telecommunications System (UMTS) 21
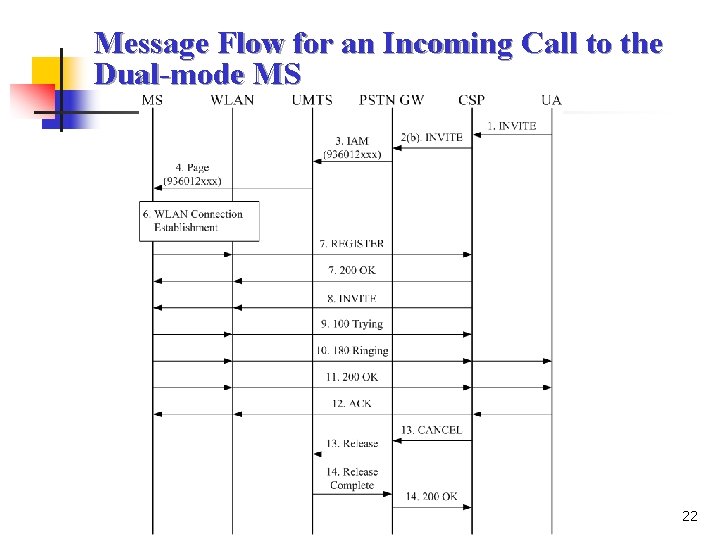
Message Flow for an Incoming Call to the Dual-mode MS 22
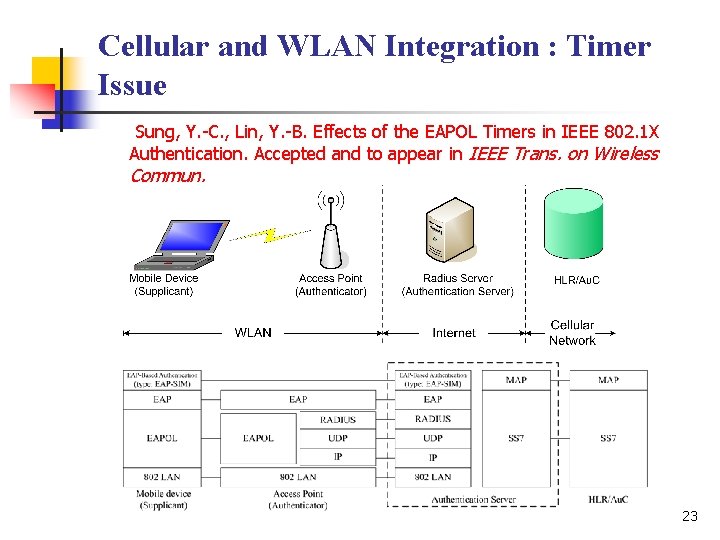
Cellular and WLAN Integration : Timer Issue Sung, Y. -C. , Lin, Y. -B. Effects of the EAPOL Timers in IEEE 802. 1 X Authentication. Accepted and to appear in IEEE Trans. on Wireless Commun. 23
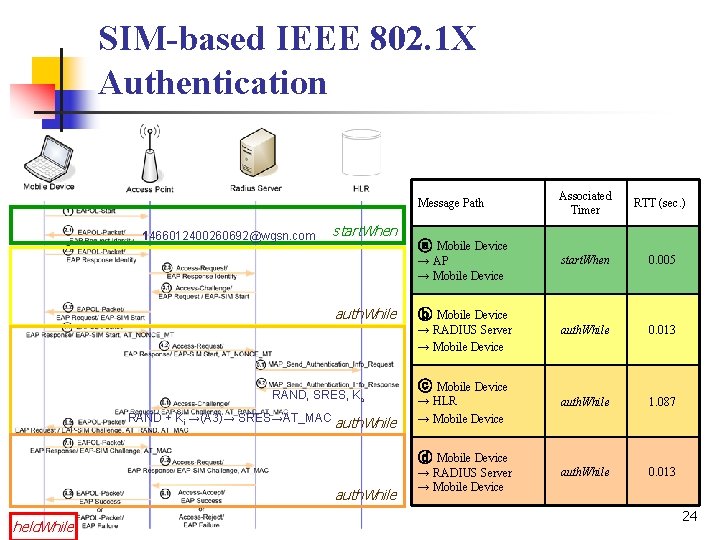
SIM-based IEEE 802. 1 X Authentication Message Path 1466012400260692@wgsn. com start. When RAND + Ki →(A 3)→ SRES→AT_MAC auth. While start. When 0. 005 auth. While 0. 013 auth. While 1. 087 auth. While 0. 013 ⓑ Mobile Device → RADIUS Server → Mobile Device RAND, SRES, Kc RTT (sec. ) ⓐ Mobile Device → AP → Mobile Device auth. While Associated Timer ⓒ Mobile Device → HLR → Mobile Device ⓓ Mobile Device auth. While held. While → RADIUS Server → Mobile Device 24
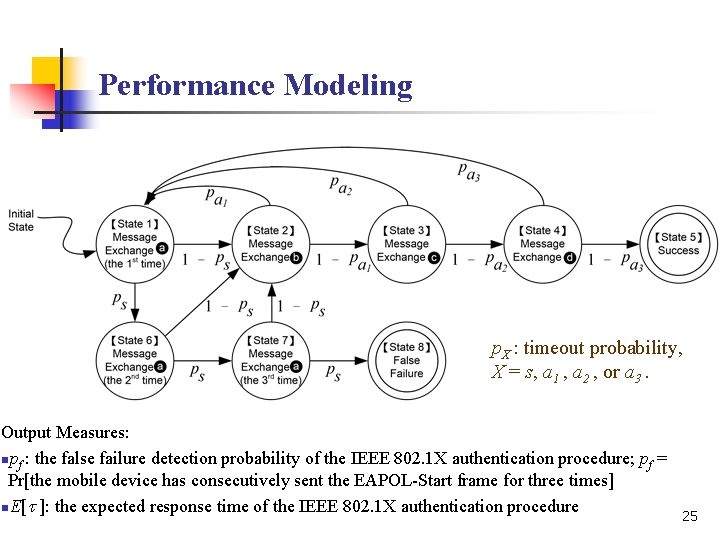
Performance Modeling p. X : timeout probability, X = s, a 1 , a 2 , or a 3. Output Measures: npf : the false failure detection probability of the IEEE 802. 1 X authentication procedure; pf = Pr[the mobile device has consecutively sent the EAPOL-Start frame for three times] n. E[t ]: the expected response time of the IEEE 802. 1 X authentication procedure 25
![Numerical Examples var[t ] = 100 × E[t ] X X 2 (t. X: Numerical Examples var[t ] = 100 × E[t ] X X 2 (t. X:](http://slidetodoc.com/presentation_image_h/7e476897942a7bca5e50c2b8fb5ccbb6/image-26.jpg)
Numerical Examples var[t ] = 100 × E[t ] X X 2 (t. X: service time of message exchange, X = s, a 1, a 2, or a 3). n EAPOL message arrival rate l ≦ 0. 925 × E[ta 2]– 1 n Ts ≧ 10 sec pf =0 n n n Case 1: Ts = Ta 1 = Ta 2 = Ta 3 = 30 sec (default values of timeout timers) Case 2: Ts = Ta 1 = Ta 2 = Ta 3 = 15 sec Case 3: Ts = Ta 1 = Ta 2 = Ta 3 = 10 sec Case 4: Ts = Ta 1 = 10 sec, Ta 2 = 5 sec, Ta 3 = 30 sec (TX: associated timeout period of message exchange) Case 4 has the same pf performance as Cases 1 – 3, but has much better E[t] performance than these three Cases. In Case 3, the total timeout value Ts + Ta 1 + Ta 2 + Ta 3 = 40 seconds. For Case 4, the total timeout value is 55 seconds. But, Case 4 outperforms Case 3 for both pf and E[t] performances. l ≧ 0. 925 × E[ta 2]– 1 n n Case 4 improves E[t] at the cost of degrading pf as compared with Cases 1 and 2 The system is saturated, and will not occur be allowed in most commercial operations 26
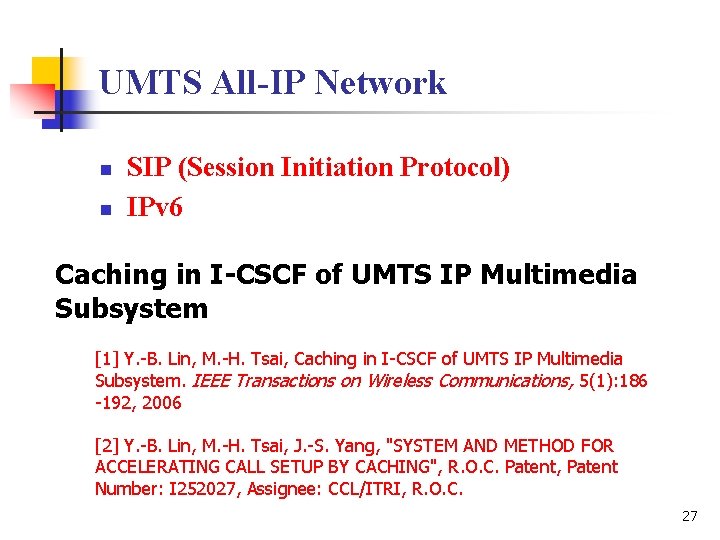
UMTS All-IP Network n n SIP (Session Initiation Protocol) IPv 6 Caching in I-CSCF of UMTS IP Multimedia Subsystem [1] Y. -B. Lin, M. -H. Tsai, Caching in I-CSCF of UMTS IP Multimedia Subsystem. IEEE Transactions on Wireless Communications, 5(1): 186 -192, 2006 [2] Y. -B. Lin, M. -H. Tsai, J. -S. Yang, "SYSTEM AND METHOD FOR ACCELERATING CALL SETUP BY CACHING", R. O. C. Patent, Patent Number: I 252027, Assignee: CCL/ITRI, R. O. C. 27
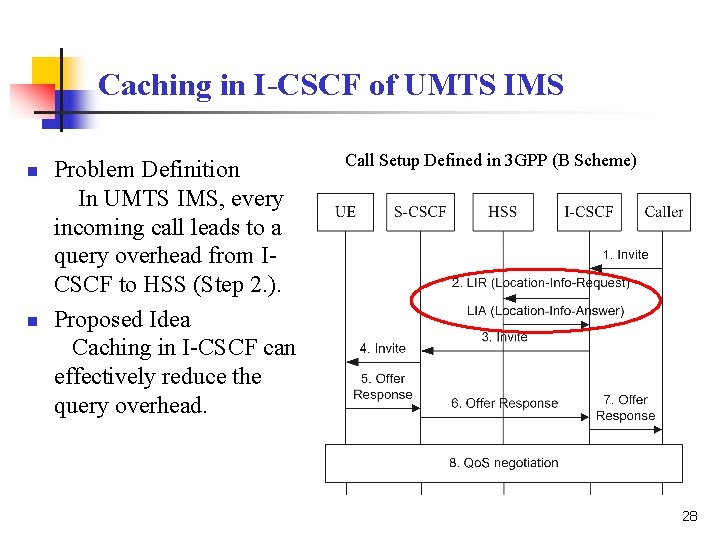
Caching in I-CSCF of UMTS IMS n n Problem Definition In UMTS IMS, every incoming call leads to a query overhead from ICSCF to HSS (Step 2. ). Proposed Idea Caching in I-CSCF can effectively reduce the query overhead. Call Setup Defined in 3 GPP (B Scheme) 28
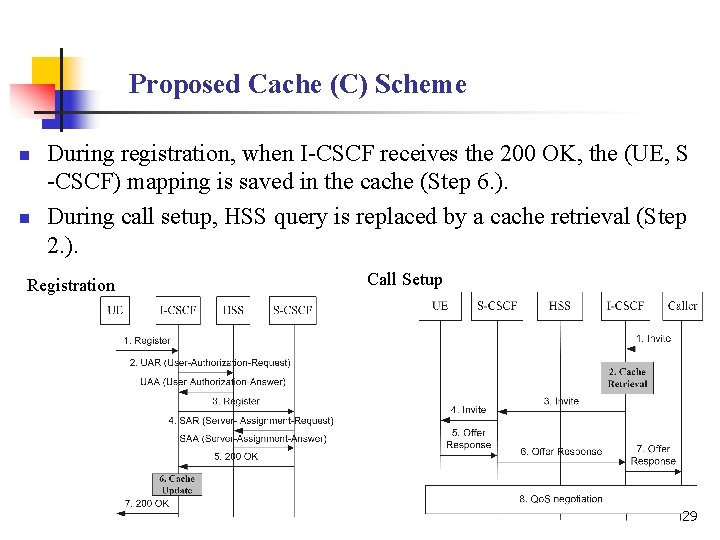
Proposed Cache (C) Scheme n n During registration, when I-CSCF receives the 200 OK, the (UE, S -CSCF) mapping is saved in the cache (Step 6. ). During call setup, HSS query is replaced by a cache retrieval (Step 2. ). Registration Call Setup 29
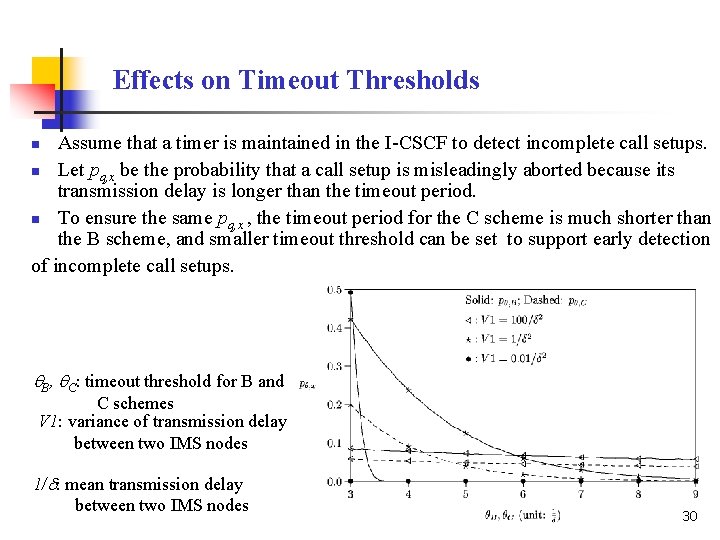
Effects on Timeout Thresholds Assume that a timer is maintained in the I-CSCF to detect incomplete call setups. n Let pq, x be the probability that a call setup is misleadingly aborted because its transmission delay is longer than the timeout period. n To ensure the same pq, x , the timeout period for the C scheme is much shorter than the B scheme, and smaller timeout threshold can be set to support early detection of incomplete call setups. n q. B, q. C: timeout threshold for B and C schemes V 1: variance of transmission delay between two IMS nodes 1/d: mean transmission delay between two IMS nodes 30
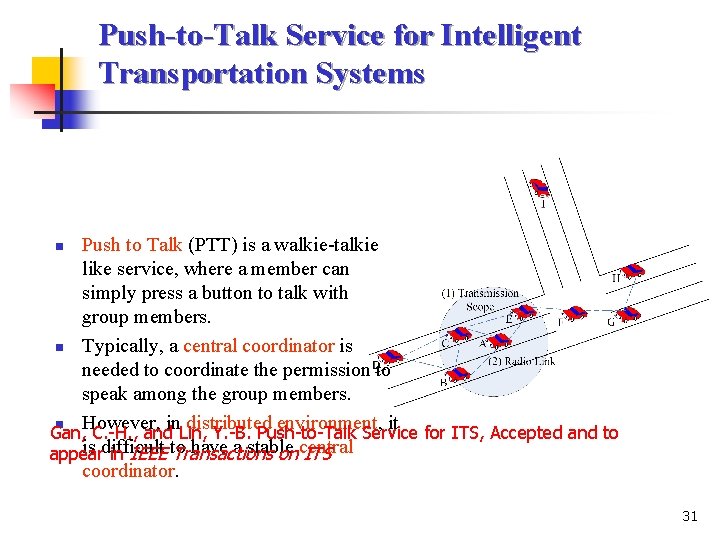
Push-to-Talk Service for Intelligent Transportation Systems Push to Talk (PTT) is a walkie-talkie like service, where a member can simply press a button to talk with group members. n Typically, a central coordinator is needed to coordinate the permission to speak among the group members. n However, in distributed environment, it Gan, C. -H. , and Lin, Y. -B. Push-to-Talk Service for ITS, Accepted and to is difficult have a stable appear in IEEE to Transactions on central ITS coordinator. n 31
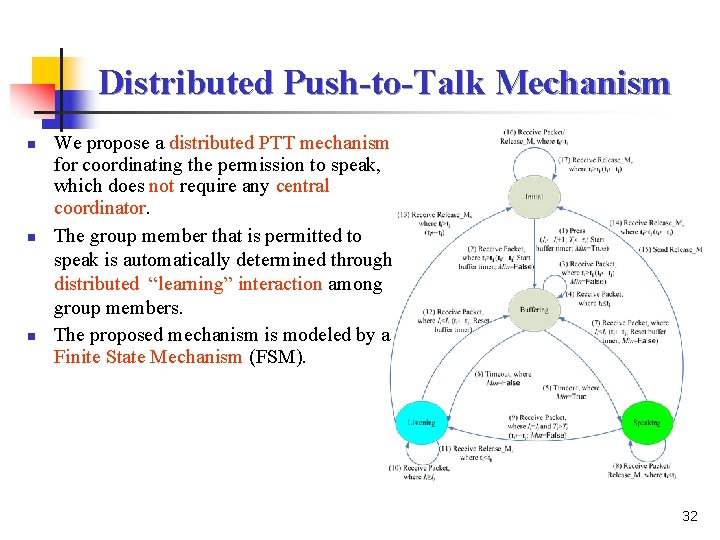
Distributed Push-to-Talk Mechanism n n n We propose a distributed PTT mechanism for coordinating the permission to speak, which does not require any central coordinator. The group member that is permitted to speak is automatically determined through distributed “learning” interaction among group members. The proposed mechanism is modeled by a Finite State Mechanism (FSM). 32
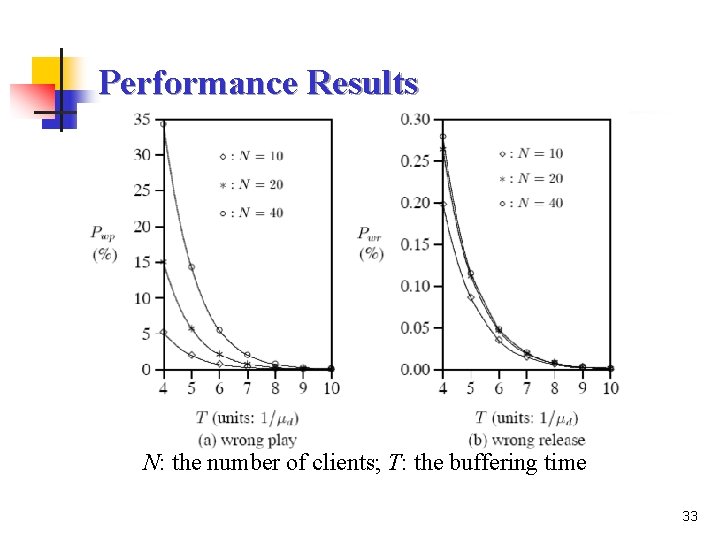
Performance Results N: the number of clients; T: the buffering time 33
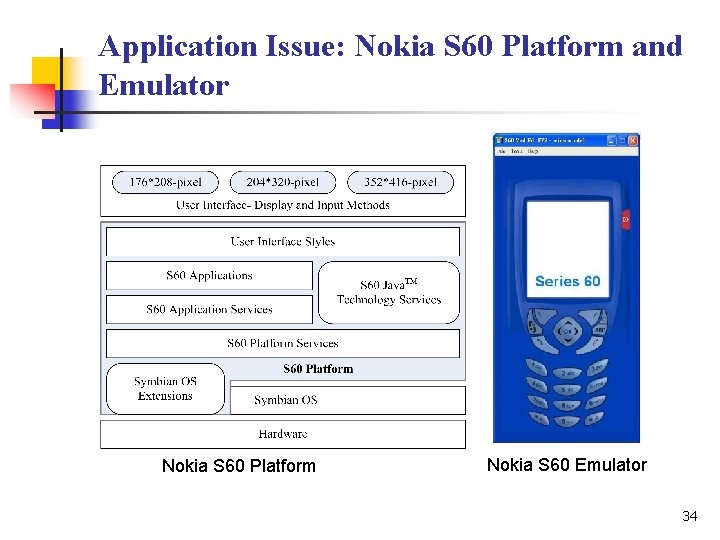
Application Issue: Nokia S 60 Platform and Emulator Nokia S 60 Platform Nokia S 60 Emulator 34
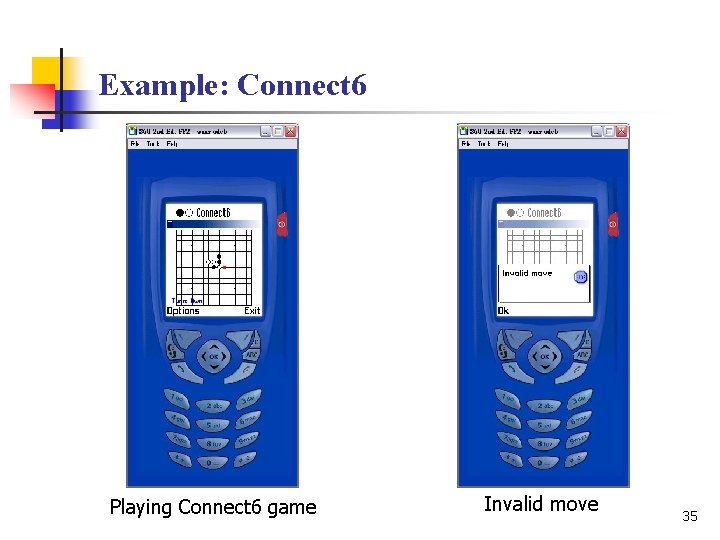
Example: Connect 6 Playing Connect 6 game Invalid move 35
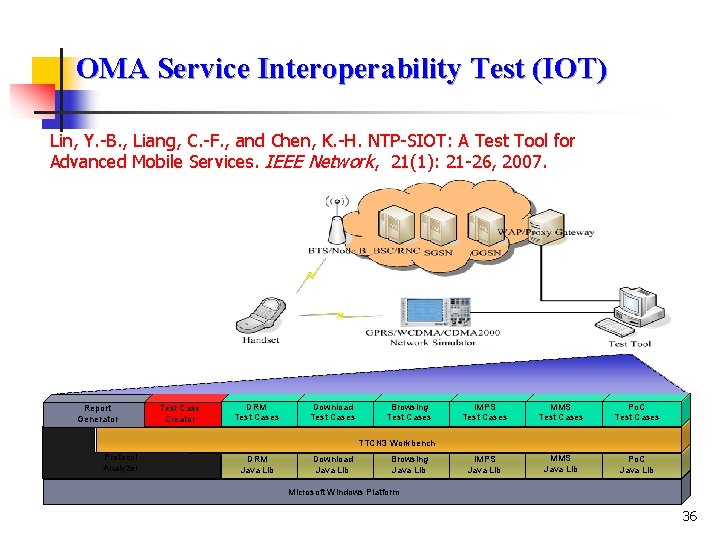
OMA Service Interoperability Test (IOT) Lin, Y. -B. , Liang, C. -F. , and Chen, K. -H. NTP-SIOT: A Test Tool for Advanced Mobile Services. IEEE Network, 21(1): 21 -26, 2007. Report Generator Test Case Creator DRM Test Cases Download Test Cases Browsing Test Cases IMPS Test Cases MMS Test Cases Po. C Test Cases IMPS Java Lib MMS Java Lib Po. C Java Lib TTCN 3 Workbench Protocol Analyzer DRM Java Lib Download Java Lib Browsing Java Lib Microsoft Windows Platform 36
Our Work on OMA Service IOT n OMA Test Tool Development n n Contributions to OMA n n Push-to-talk over Cellular (Po. C) Instant Messaging and Presence Service (IMPS) Multimedia Messaging Service (MMS) 6 test cases submitted to OMA IOP working group Ongoing Tasks n n Download and Browsing test cases Digital Right Management (DRM) test tool 37
Contributions to OMA 38
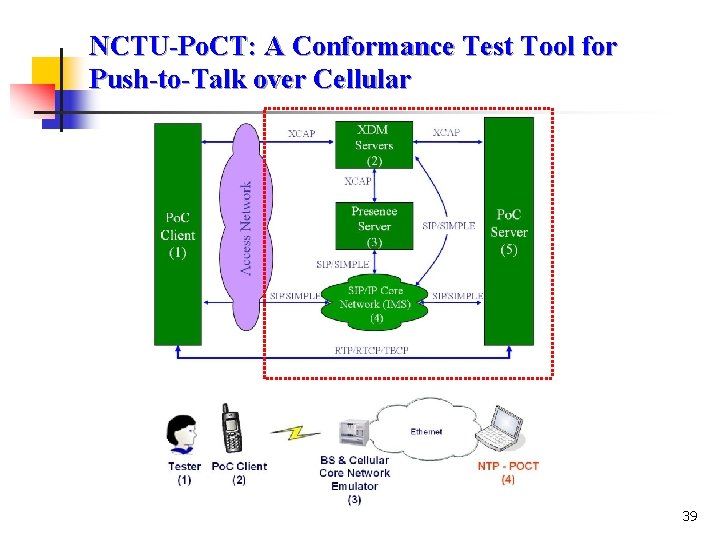
NCTU-Po. CT: A Conformance Test Tool for Push-to-Talk over Cellular 39
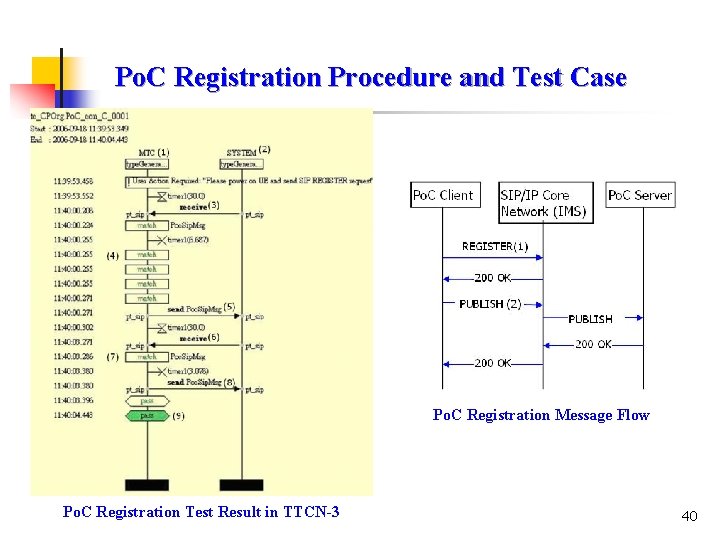
Po. C Registration Procedure and Test Case Po. C Registration Message Flow Po. C Registration Test Result in TTCN-3 40
- Slides: 40