Windows Vista Security Tidbits Steve Lamb Technical Security

Windows Vista Security Tidbits Steve Lamb Technical Security Evangelist @ Microsoft Ltd Stephen. lamb@microsoft. com http: //blogs. technet. com/steve_lamb
Overview User And Group Changes Admin account New/Missing SIDs New/Missing Users and Groups Cached credentials Kernel Changes Buffer overflow protection ACL Changes Encryption changes Suite B TS SSO EFS with Smart Cards Audit changes User rights New and changed security options Firewall Auth IP SMBv 2
User and Group Changes
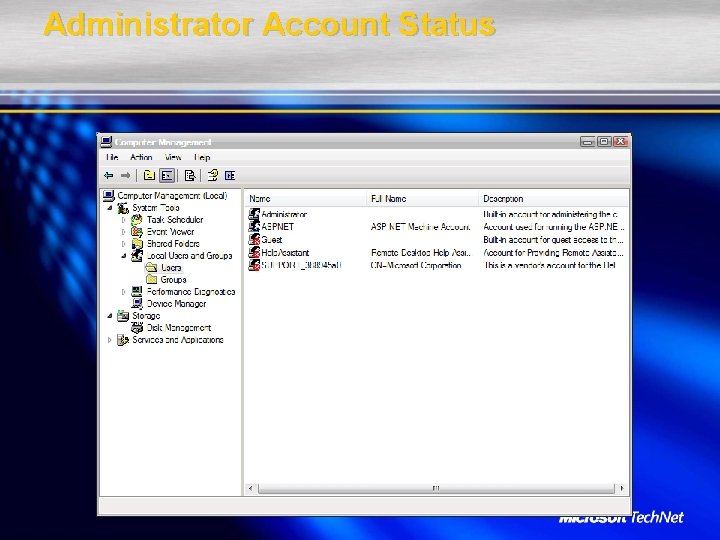
Administrator Account Status
Administrator Account Status

Power Users Are Not Anymore
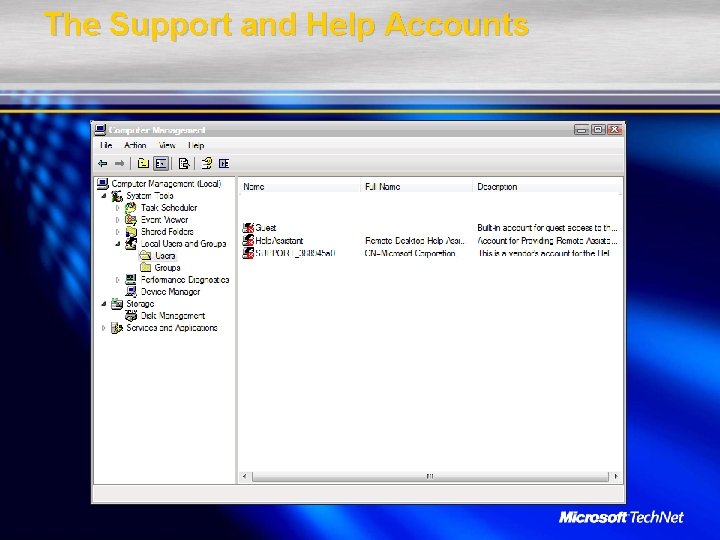
The Support and Help Accounts
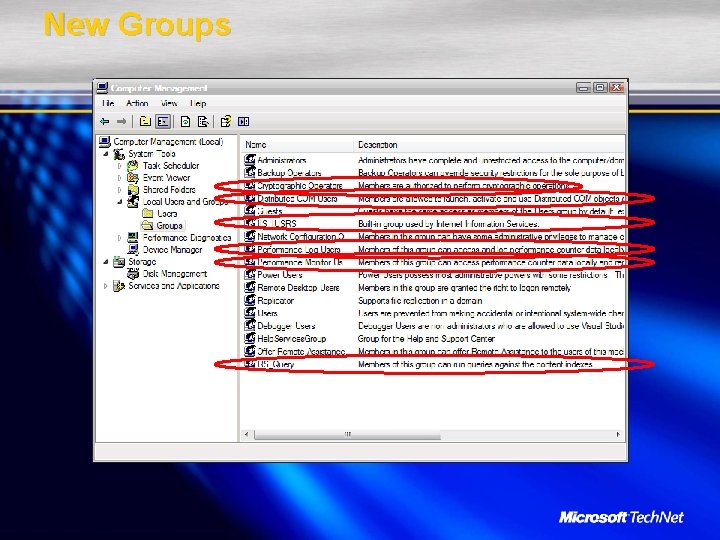
New Groups
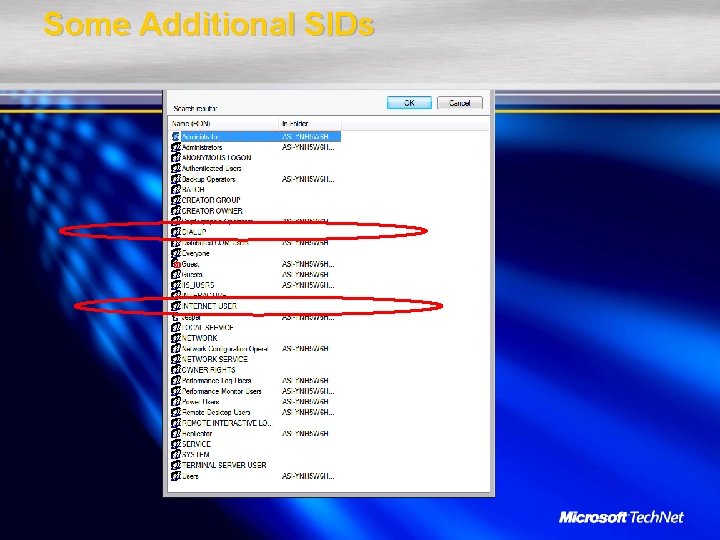
Some Additional SIDs
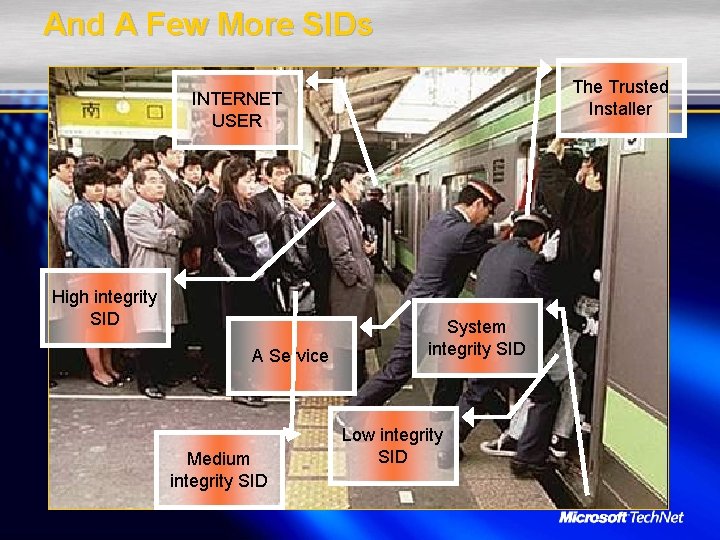
And A Few More SIDs The Trusted Installer INTERNET USER High integrity SID A Service Medium integrity SID System integrity SID Low integrity SID
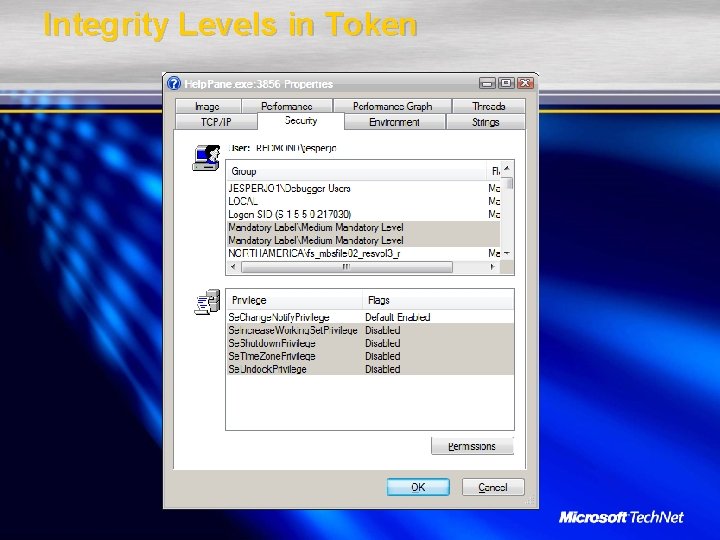
Integrity Levels in Token
ACL Changes
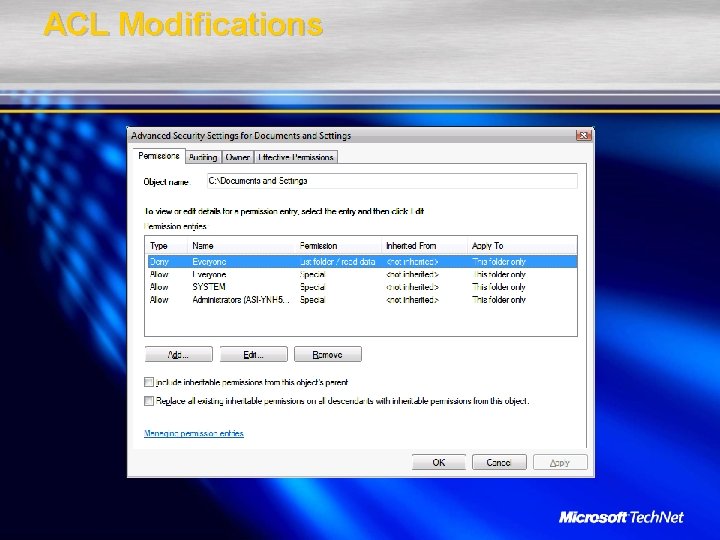
ACL Modifications
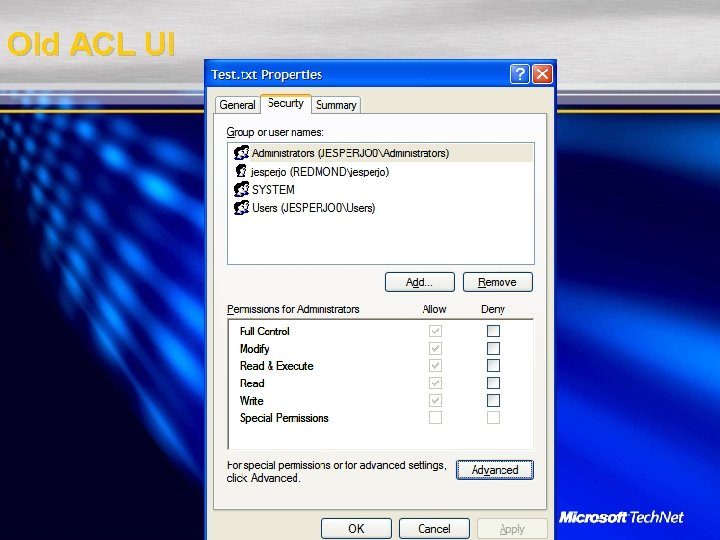
Old ACL UI
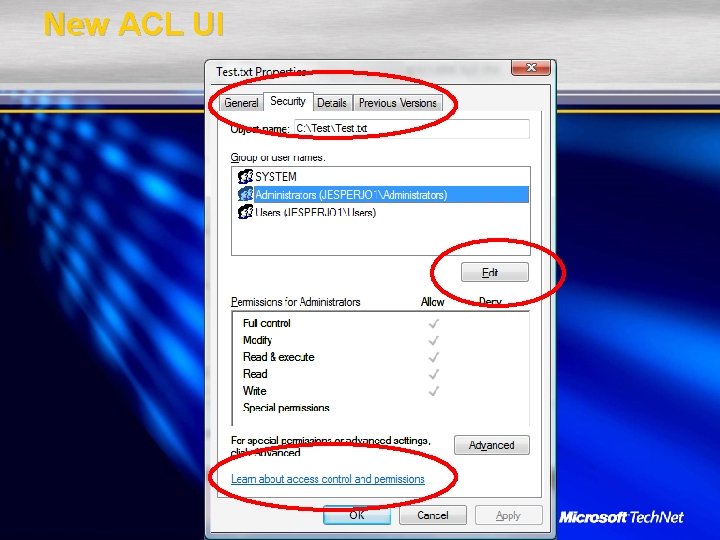
New ACL UI
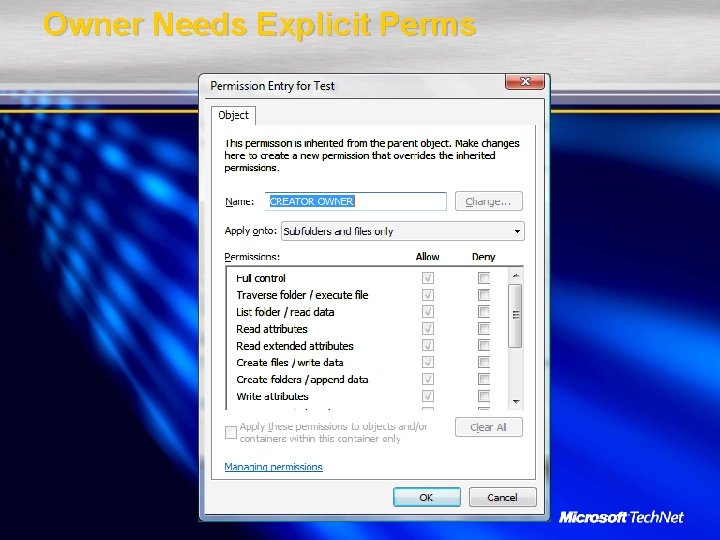
Owner Needs Explicit Perms
Kernel Changes
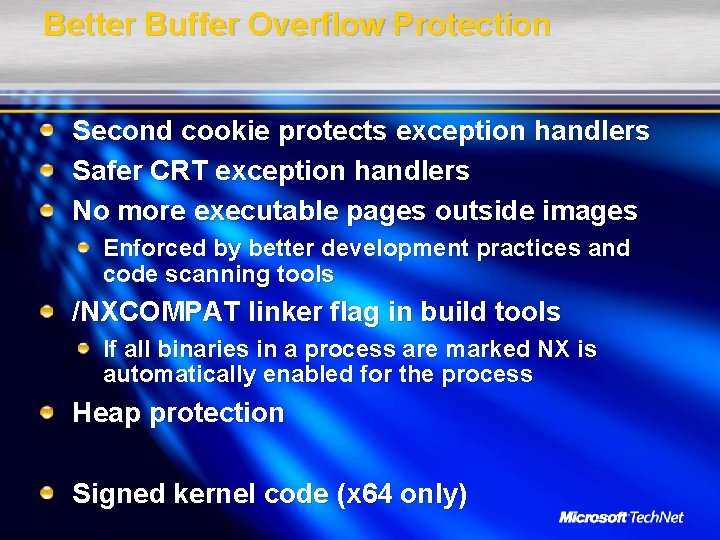
Better Buffer Overflow Protection Second cookie protects exception handlers Safer CRT exception handlers No more executable pages outside images Enforced by better development practices and code scanning tools /NXCOMPAT linker flag in build tools If all binaries in a process are marked NX is automatically enabled for the process Heap protection Signed kernel code (x 64 only)

Crypto Changes
Offline Files Encrypted Per User
Encrypted Pagefile
Suite-B Crypto Software and Smart Card Key Storage Providers Cryptographic configuration NIST ECC Prime Curves support (smart cards too) AES SHA-2 IPsec support for AES and ECDH ECC cipher suites in SSL EFS with smart cards
Cached Credentials Much Tougher
Improved Auditing
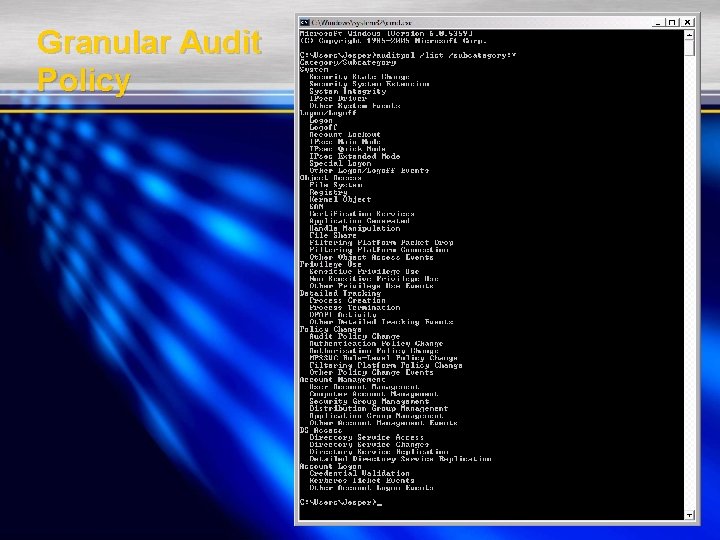
Granular Audit Policy
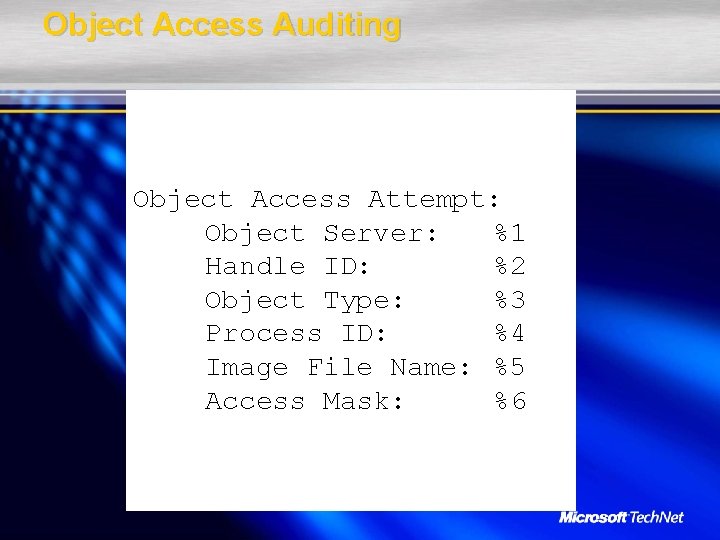
Object Access Auditing Object Access Attempt: Object Server: %1 Handle ID: %2 Object Type: %3 Process ID: %4 Image File Name: %5 Access Mask: %6
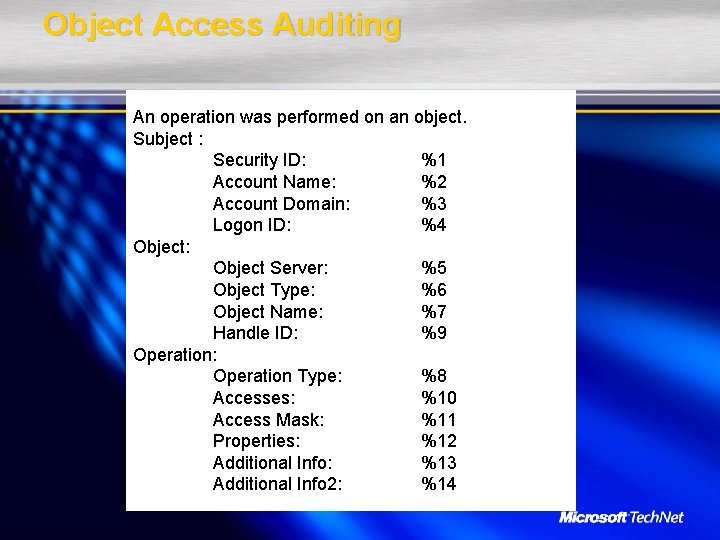
Object Access Auditing An operation was performed on an object. Subject : Security ID: %1 Account Name: %2 Account Domain: %3 Logon ID: %4 Object: Object Server: %5 Object Type: %6 Object Name: %7 Handle ID: %9 Operation: Operation Type: %8 Accesses: %10 Access Mask: %11 Properties: %12 Additional Info: %13 Additional Info 2: %14
Added Auditing For Registry value change audit events (old+new values) AD change audit events (old+new values) Improved operation-based audit Audit events for UAC Improved IPSec audit events including support for Auth. IP RPC Call audit events Share Access audit events Share Management events Cryptographic function audit events NAP audit events (server only) IAS (RADIUS) audit events (server only)
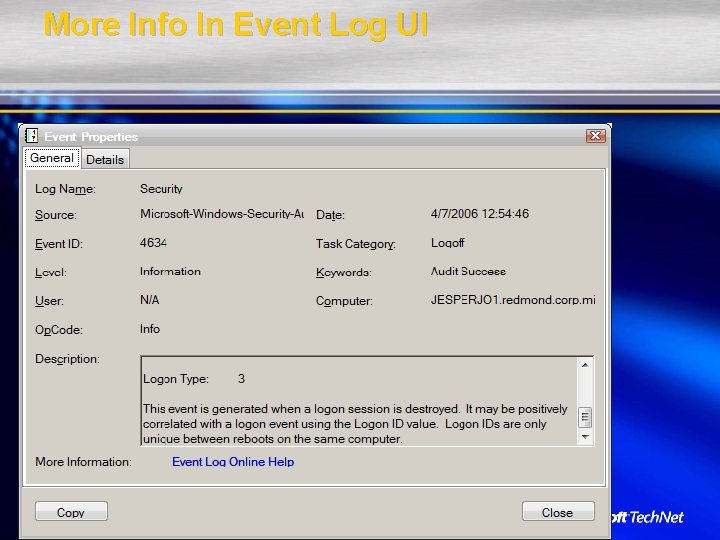
More Info In Event Log UI
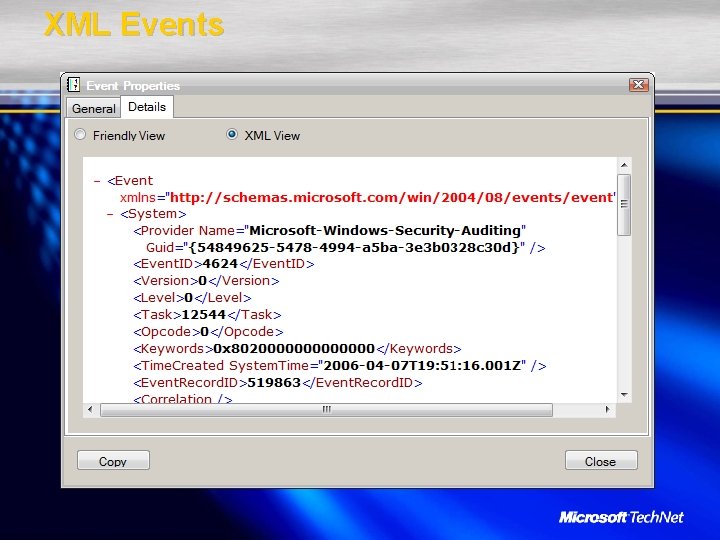
XML Events
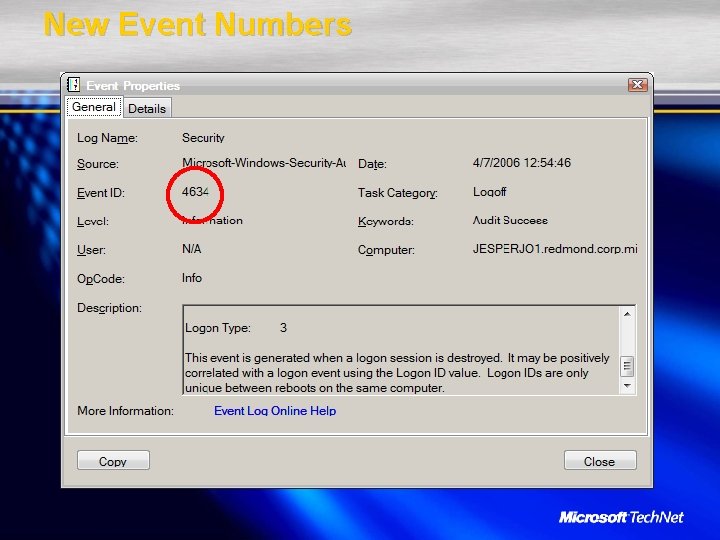
New Event Numbers

New and Modified User Rights
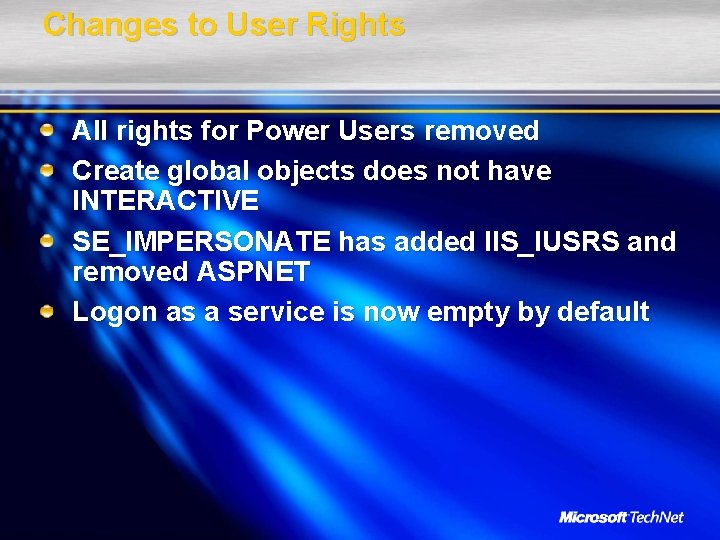
Changes to User Rights All rights for Power Users removed Create global objects does not have INTERACTIVE SE_IMPERSONATE has added IIS_IUSRS and removed ASPNET Logon as a service is now empty by default
New User Rights Access credential manager as a trusted caller Change time zone user right Create symbolic links Modify an object label Synchronize directory service data Increase a process working set
Security Options With Modified Defaults
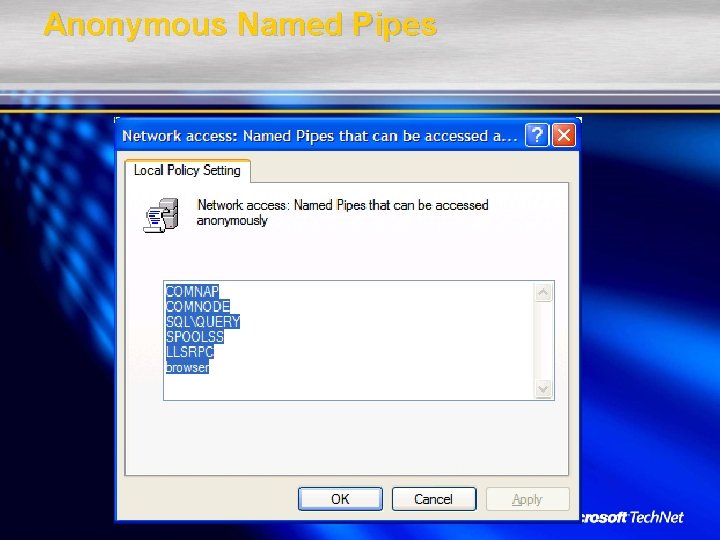
Anonymous Named Pipes
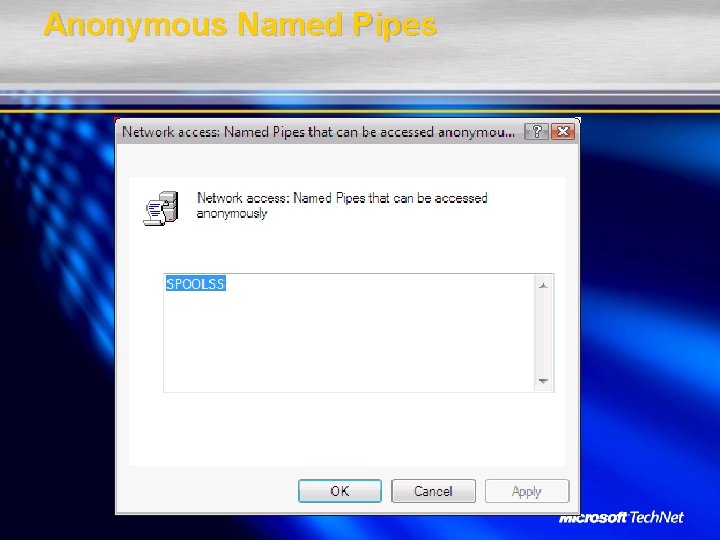
Anonymous Named Pipes
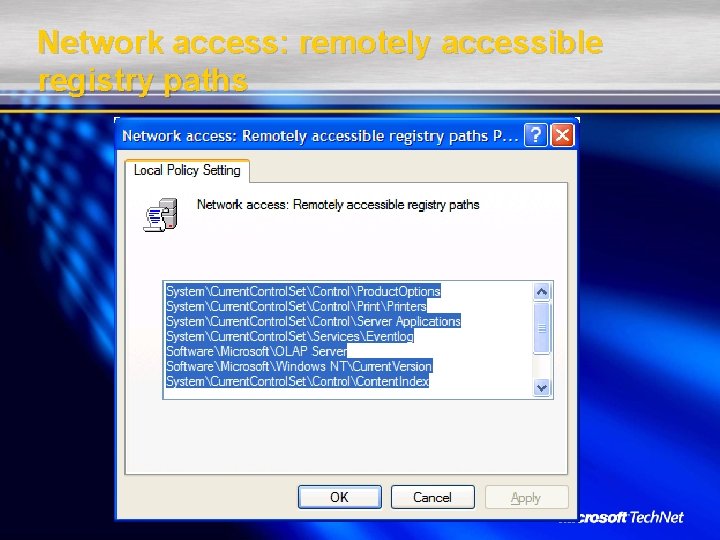
Network access: remotely accessible registry paths
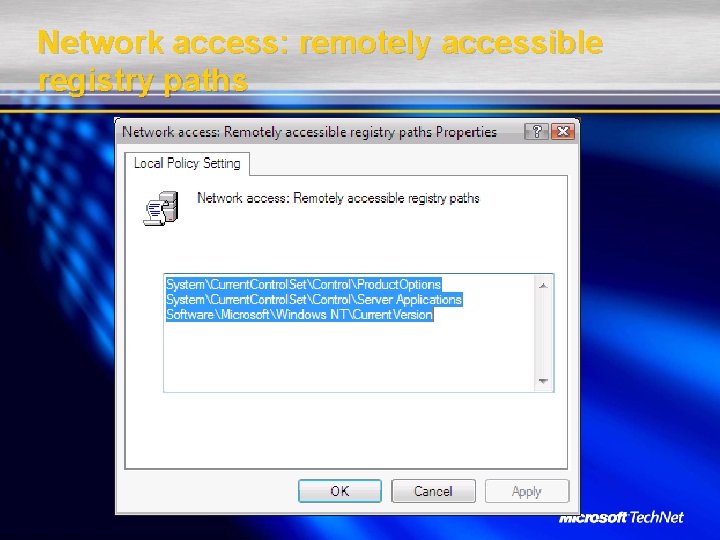
Network access: remotely accessible registry paths
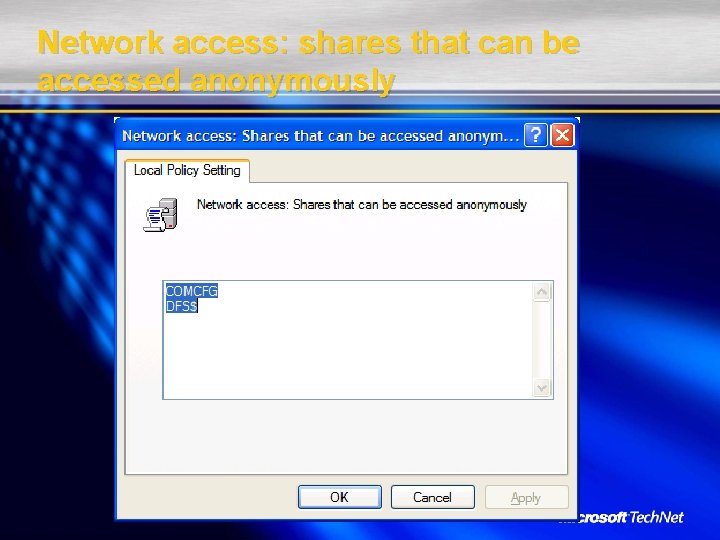
Network access: shares that can be accessed anonymously
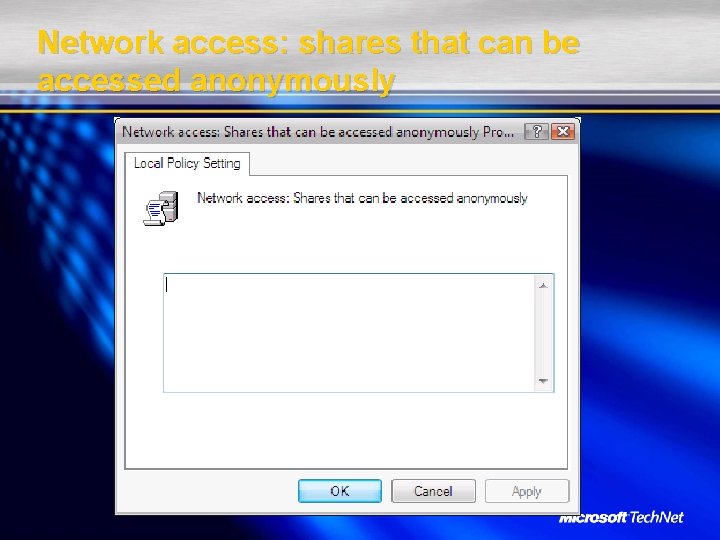
Network access: shares that can be accessed anonymously
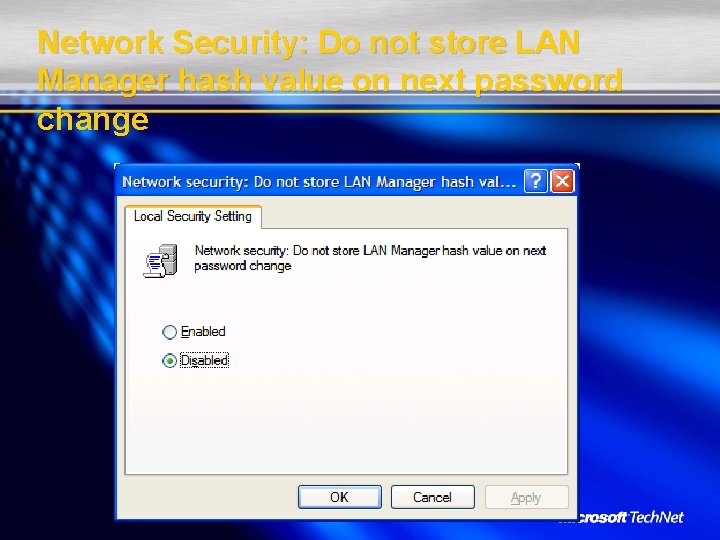
Network Security: Do not store LAN Manager hash value on next password change
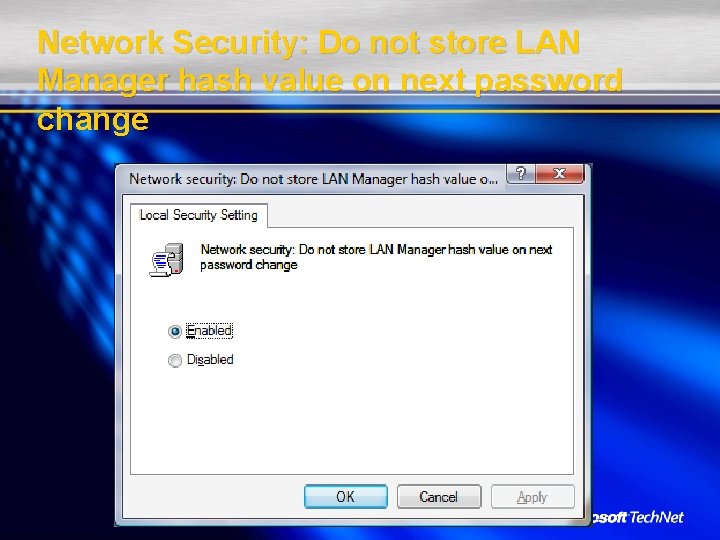
Network Security: Do not store LAN Manager hash value on next password change
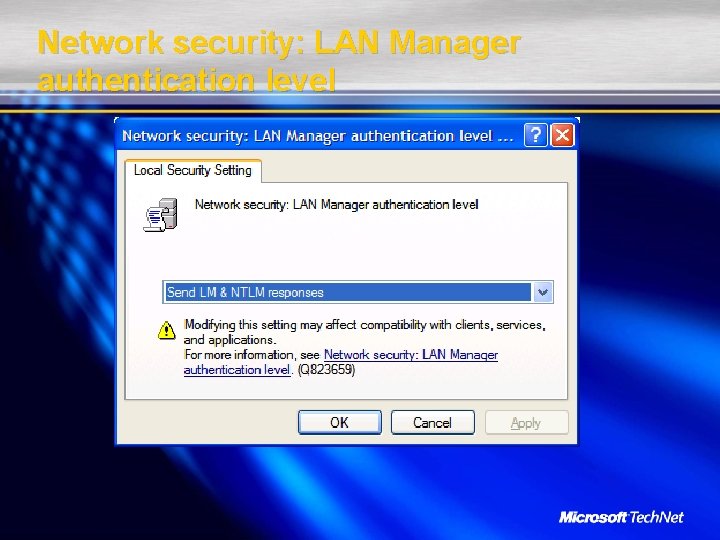
Network security: LAN Manager authentication level
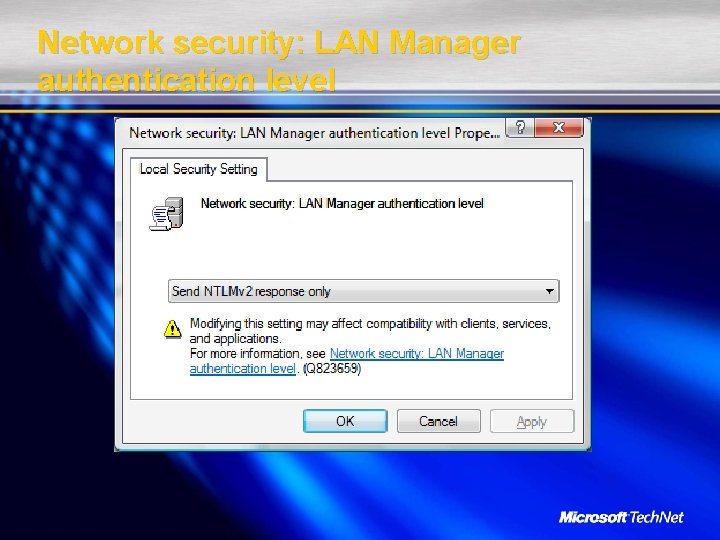
Network security: LAN Manager authentication level
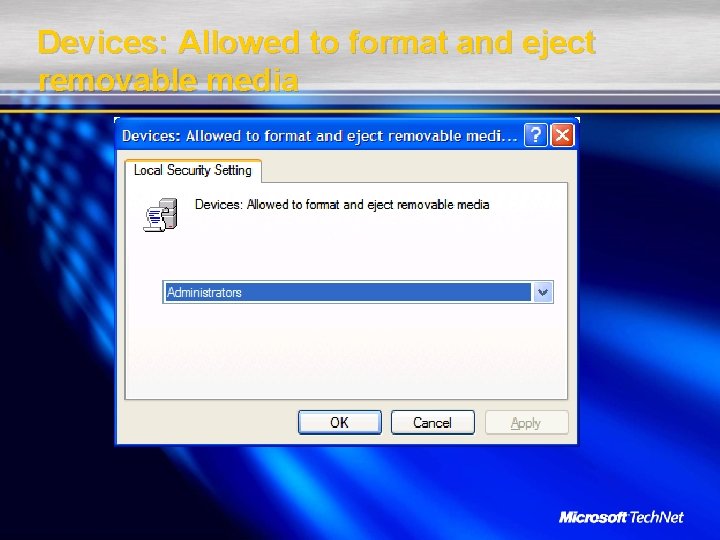
Devices: Allowed to format and eject removable media
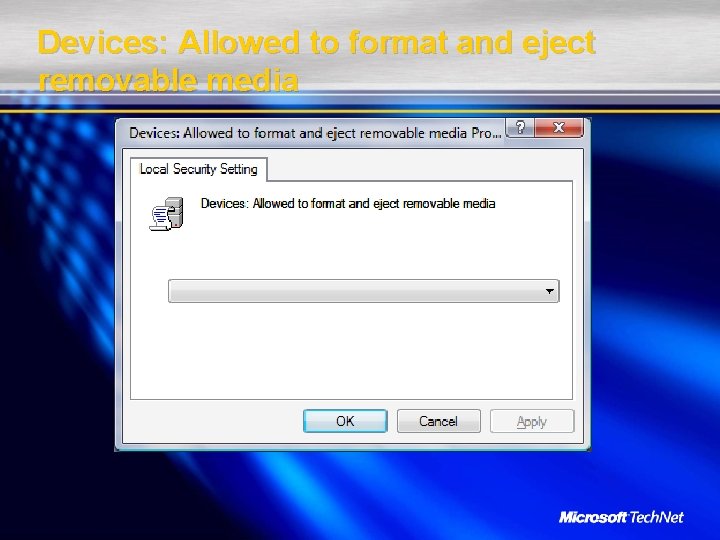
Devices: Allowed to format and eject removable media
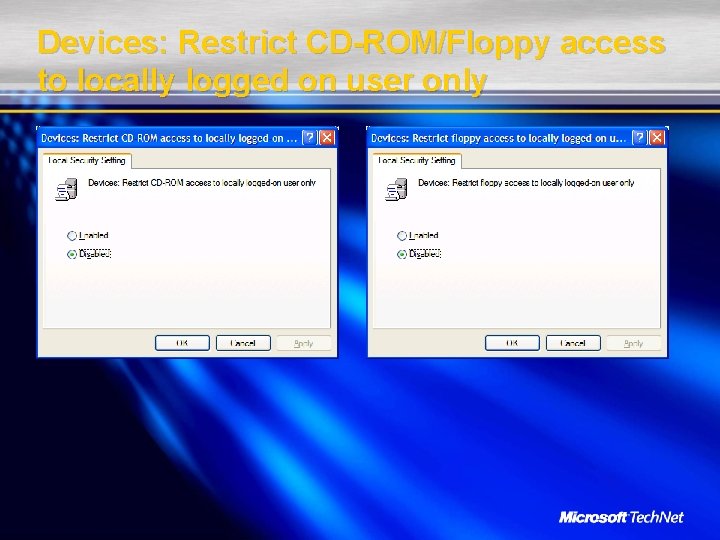
Devices: Restrict CD-ROM/Floppy access to locally logged on user only
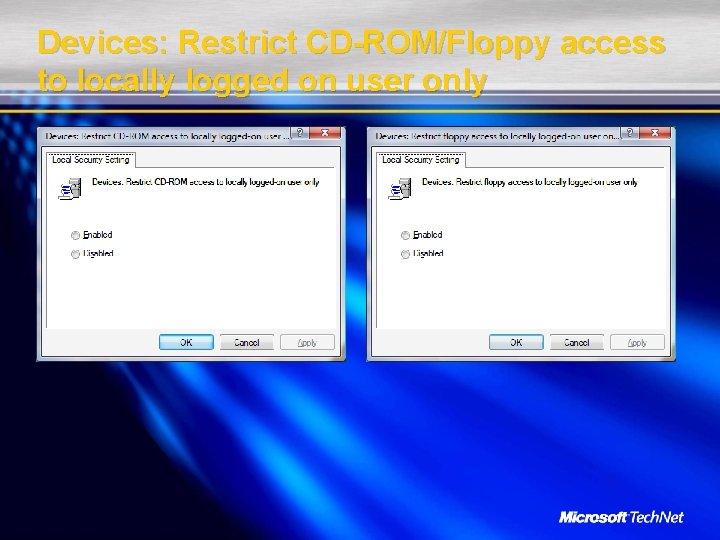
Devices: Restrict CD-ROM/Floppy access to locally logged on user only

Devices: Unsigned driver installation behavior

Devices: Unsigned driver installation behavior
Why Change It?
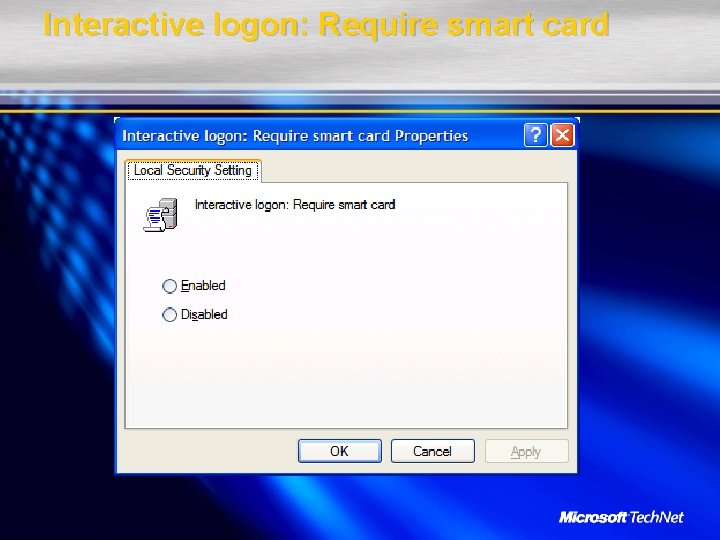
Interactive logon: Require smart card
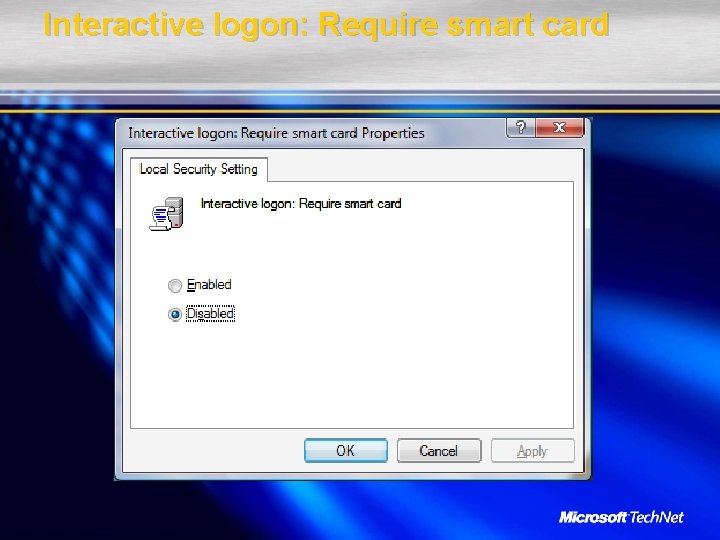
Interactive logon: Require smart card

New Security Options
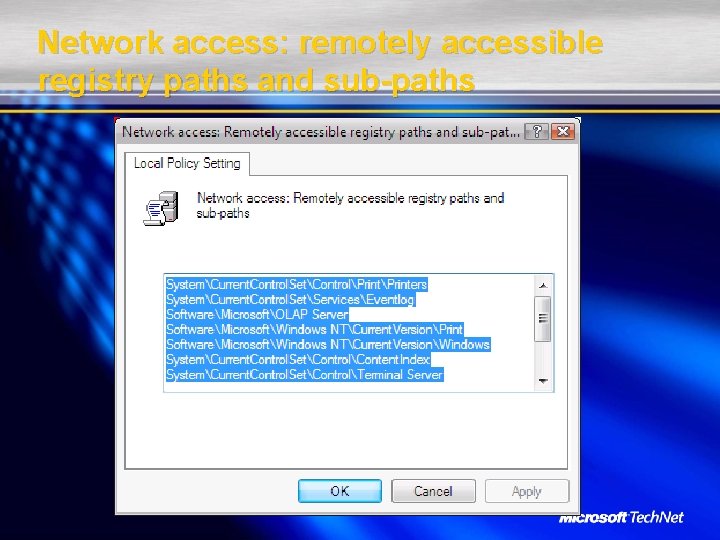
Network access: remotely accessible registry paths and sub-paths
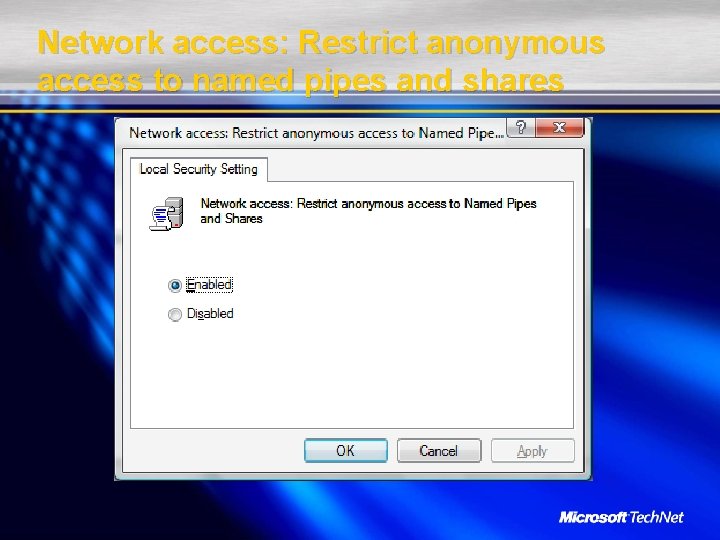
Network access: Restrict anonymous access to named pipes and shares
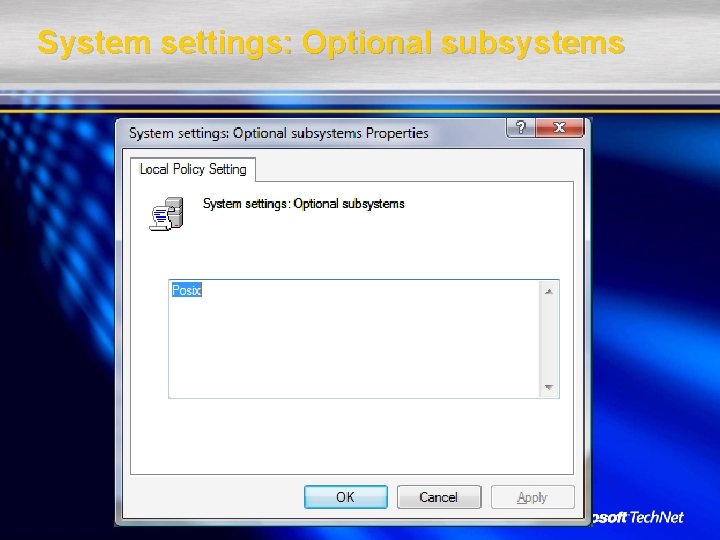
System settings: Optional subsystems
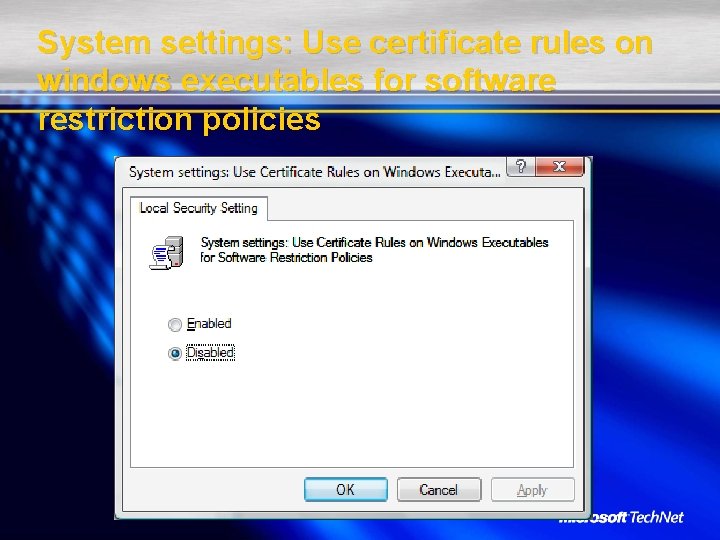
System settings: Use certificate rules on windows executables for software restriction policies
Lots and lots of GP changes
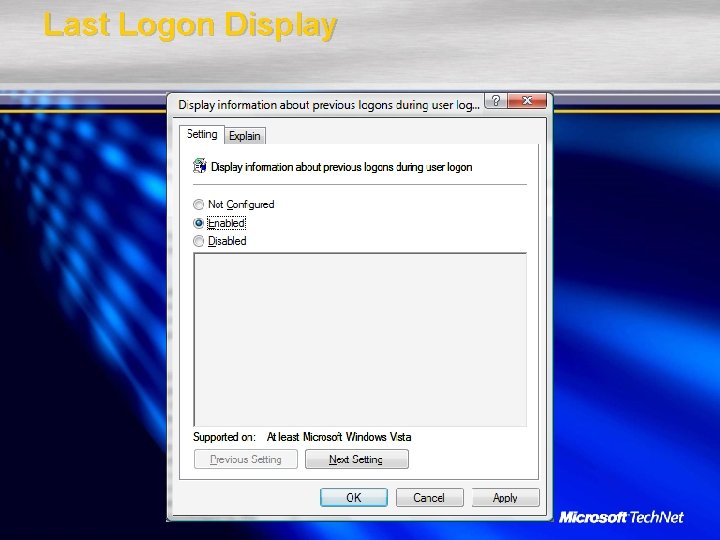
Last Logon Display
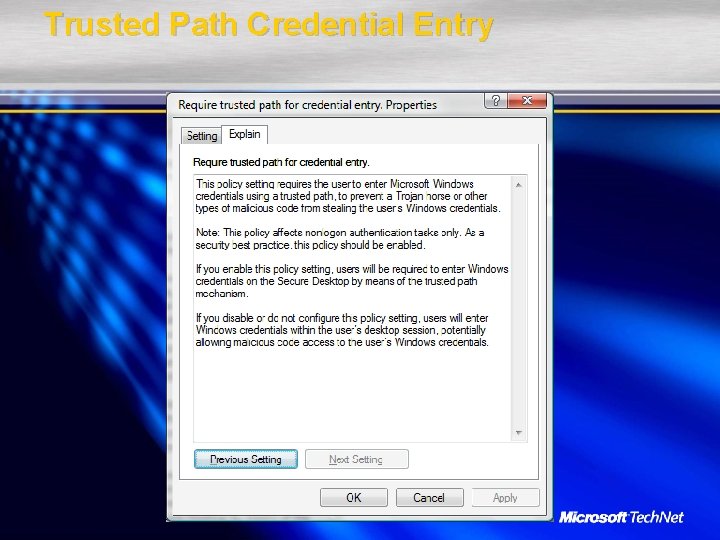
Trusted Path Credential Entry
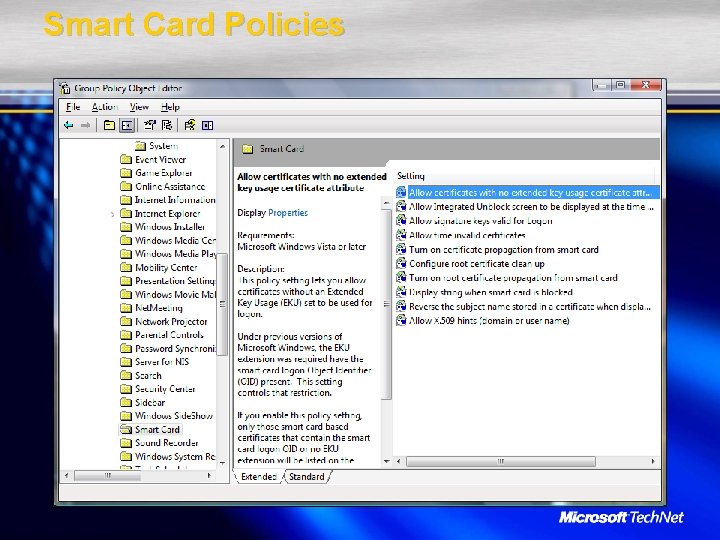
Smart Card Policies
SMBv 2
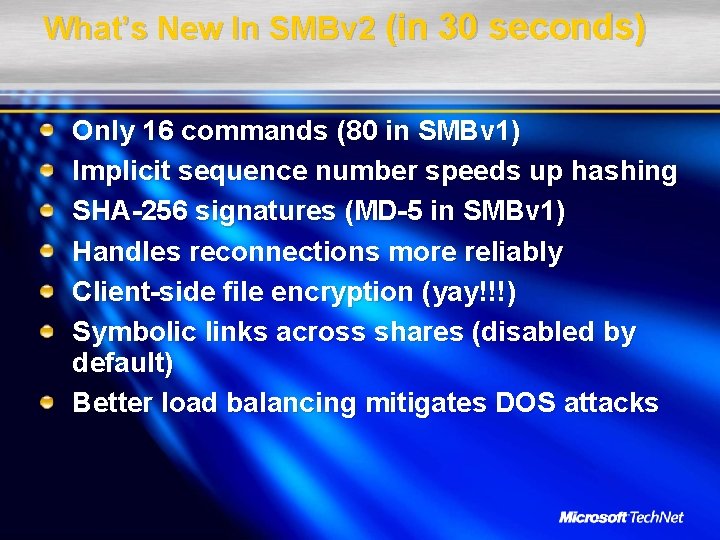
What’s New In SMBv 2 (in 30 seconds) Only 16 commands (80 in SMBv 1) Implicit sequence number speeds up hashing SHA-256 signatures (MD-5 in SMBv 1) Handles reconnections more reliably Client-side file encryption (yay!!!) Symbolic links across shares (disabled by default) Better load balancing mitigates DOS attacks
Miscellany
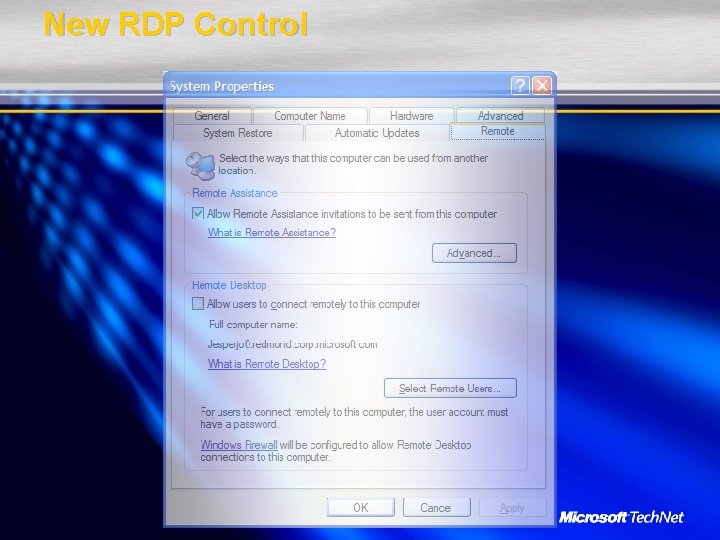
New RDP Control
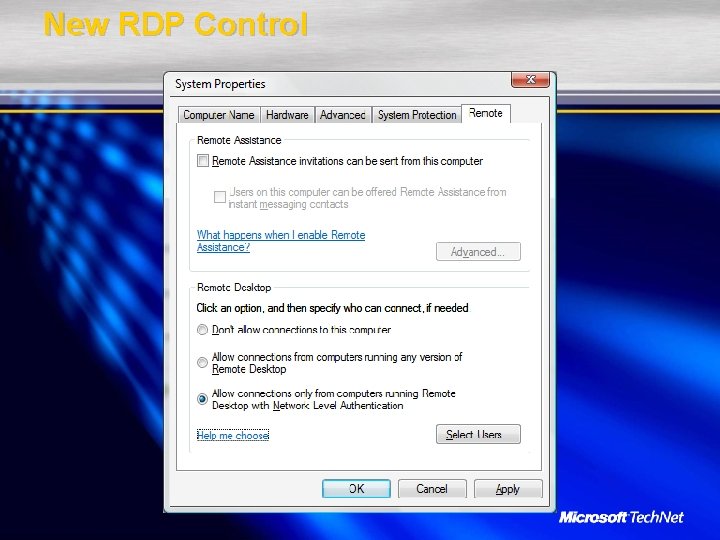
New RDP Control
Timeless Security Advice! Order online: http: //www. protectyourwindowsnetwo rk. com

Thanks to Jesper M. Johansson, Ph. D. for creating the slides Steve Lamb Technical Security Evangelist @ Microsoft Ltd Stephen. lamb@microsoft. com http: //blogs. technet. com/steve_lamb © 2006 Microsoft Corporation. All rights reserved. This presentation is for informational purposes only. Microsoft makes no warranties, express or implied, in this summary.
- Slides: 70