Windows Server 2008 Security and Microsoft Security Bruce
• Windows Server 2008 Security and Microsoft Security Bruce Lynn Director of Server Business Group UK Microsoft Corporation Microsoft Confidential
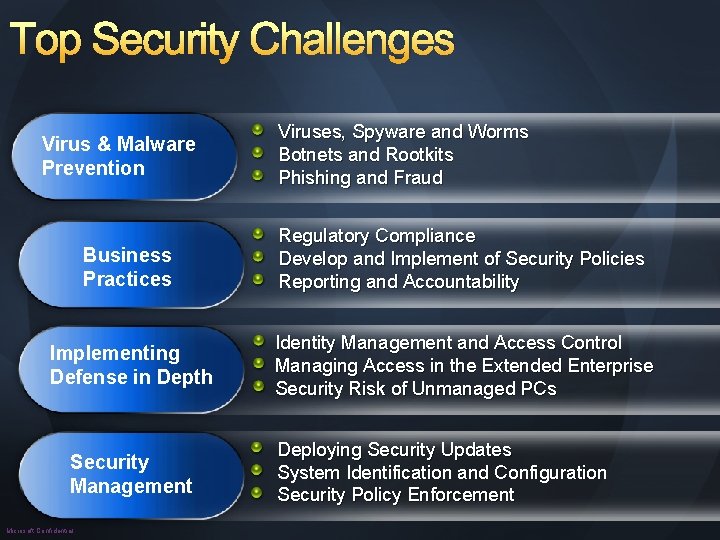
Top Security Challenges Virus & Malware Prevention Viruses, Spyware and Worms Botnets and Rootkits Phishing and Fraud Business Practices Regulatory Compliance Develop and Implement of Security Policies Reporting and Accountability Implementing Defense in Depth Identity Management and Access Control Managing Access in the Extended Enterprise Security Risk of Unmanaged PCs Security Management Microsoft Confidential Deploying Security Updates System Identification and Configuration Security Policy Enforcement
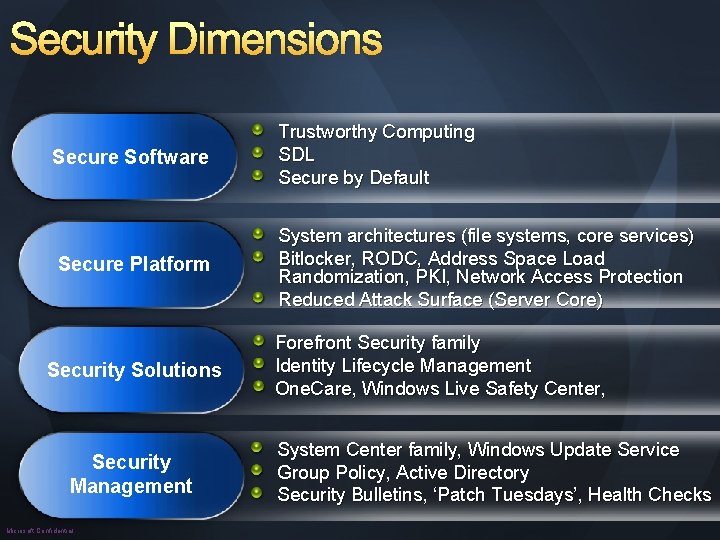
Security Dimensions Secure Software Trustworthy Computing SDL Secure by Default Secure Platform System architectures (file systems, core services) Bitlocker, RODC, Address Space Load Randomization, PKI, Network Access Protection Reduced Attack Surface (Server Core) Security Solutions Security Management Microsoft Confidential Forefront Security family Identity Lifecycle Management One. Care, Windows Live Safety Center, System Center family, Windows Update Service Group Policy, Active Directory Security Bulletins, ‘Patch Tuesdays’, Health Checks

Secure Software Microsoft Confidential
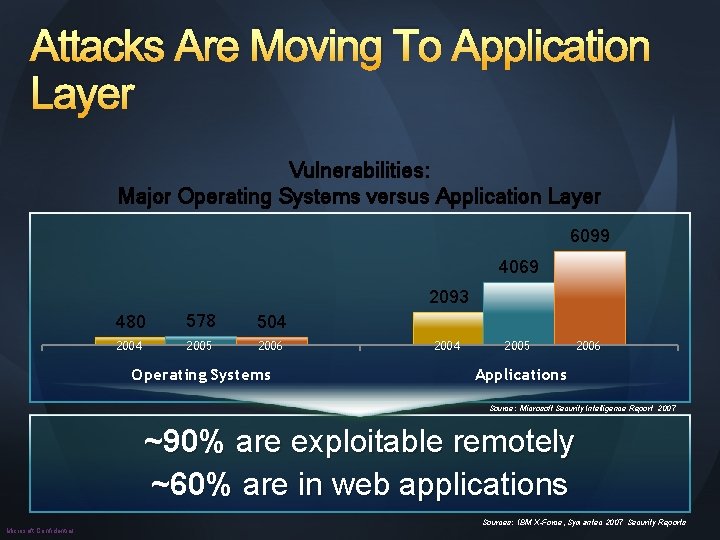
Attacks Are Moving To Application Layer Vulnerabilities: Major Operating Systems versus Application Layer 6099 4069 2093 480 578 504 2005 2006 Operating Systems 2004 2005 2006 Applications Source: Microsoft Security Intelligence Report 2007 ~90% are exploitable remotely ~60% are in web applications Microsoft Confidential Sources: IBM X-Force, Symantec 2007 Security Reports

Trustworthy Computing TWC Announced SDL begins 2002 Microsoft Confidential Windows Server 2003 Windows XP SP 2 DSI Launched 2004 SQL Server 2005 Visual Studio 2005 Windows Server 2003 SP 1 Malicious SW Removal Tool 2005 Windows Defender Windows Live One. Care 2006 Windows Vista Office 2007 Forefront 2007 Windows Server 2008 SQL Server 2008

Secure Platform Microsoft Confidential
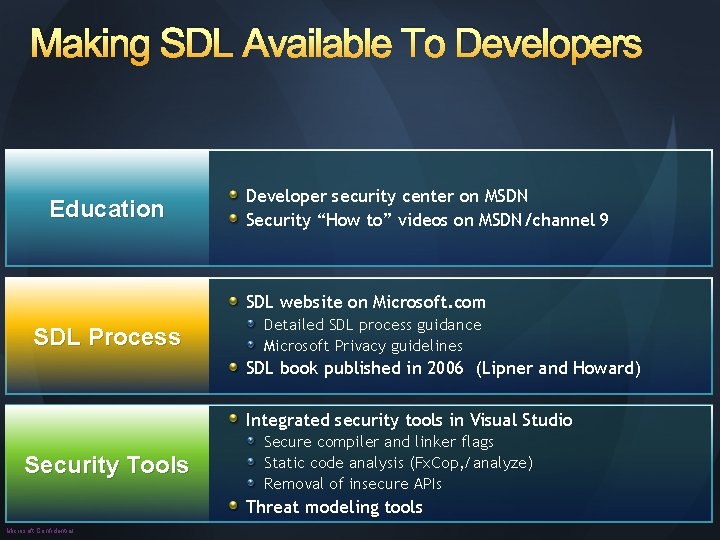
Making SDL Available To Developers Education Developer security center on MSDN Security “How to” videos on MSDN/channel 9 SDL website on Microsoft. com SDL Process Detailed SDL process guidance Microsoft Privacy guidelines SDL book published in 2006 (Lipner and Howard) Integrated security tools in Visual Studio Security Tools Secure compiler and linker flags Static code analysis (Fx. Cop, /analyze) Removal of insecure APIs Threat modeling tools Microsoft Confidential
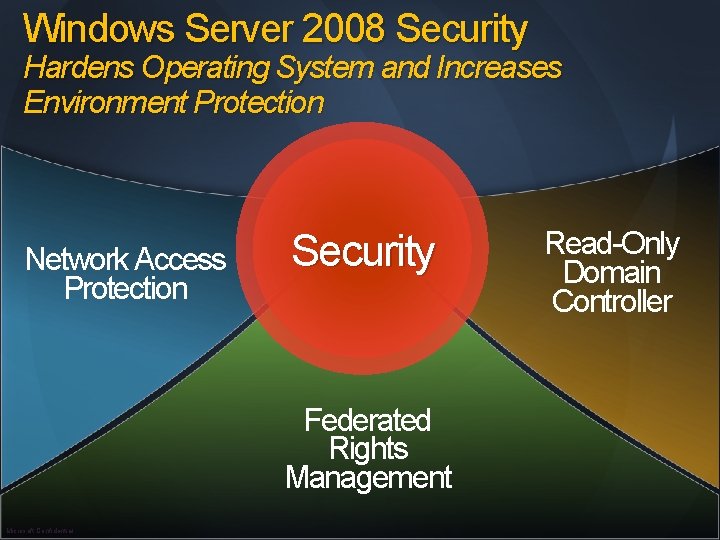
Windows Server 2008 Security Hardens Operating System and Increases Environment Protection Network Access Protection Security Federated Rights Management Microsoft Confidential Read-Only Domain Controller
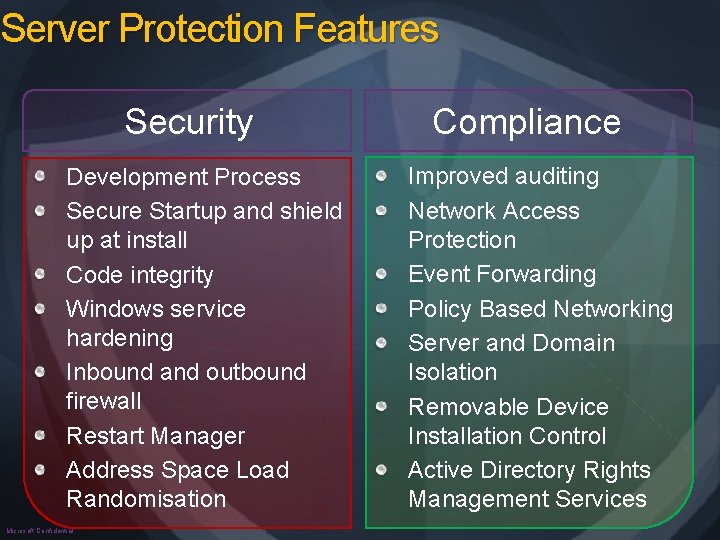
Server Protection Features Security Development Process Secure Startup and shield up at install Code integrity Windows service hardening Inbound and outbound firewall Restart Manager Address Space Load Randomisation Microsoft Confidential Compliance Improved auditing Network Access Protection Event Forwarding Policy Based Networking Server and Domain Isolation Removable Device Installation Control Active Directory Rights Management Services
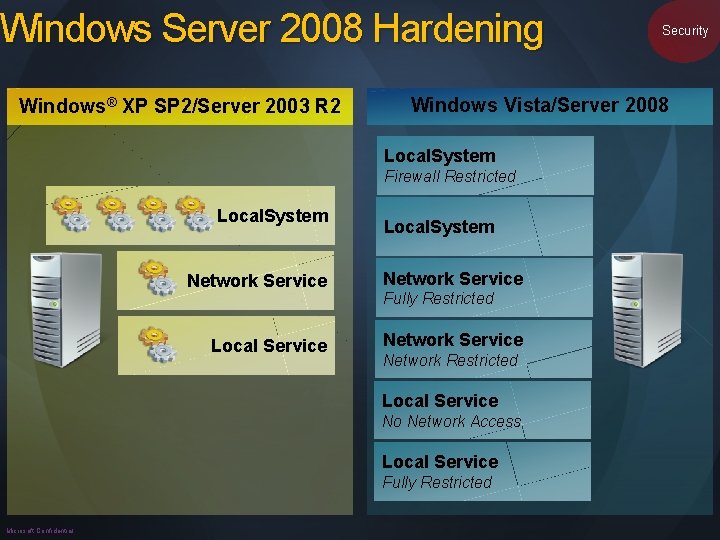
Windows Server 2008 Hardening Windows® XP SP 2/Server 2003 R 2 Windows Vista/Server 2008 Local. System Firewall Restricted Local. System Network Service Local Service Network Service Fully Restricted Network Restricted Local Service No Network Access Local Service Fully Restricted Microsoft Confidential Security
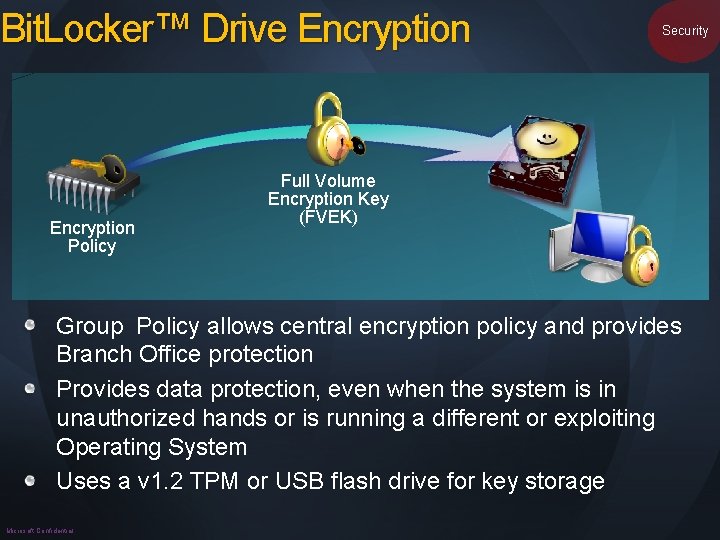
Bit. Locker™ Drive Encryption Policy Security Full Volume Encryption Key (FVEK) Group Policy allows central encryption policy and provides Branch Office protection Provides data protection, even when the system is in unauthorized hands or is running a different or exploiting Operating System Uses a v 1. 2 TPM or USB flash drive for key storage Microsoft Confidential
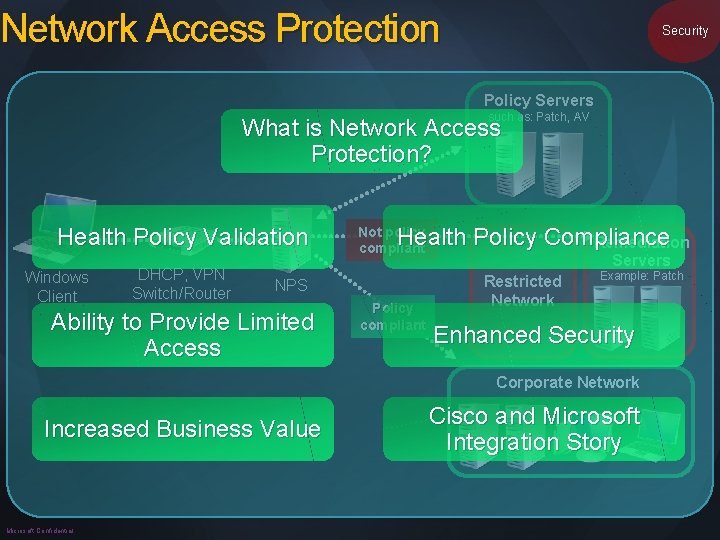
Network Access Protection Security Policy Servers such as: Patch, AV What is Network Access Protection? Health Policy Validation Windows Client DHCP, VPN Switch/Router Health Policy Compliance Remediation Not policy compliant NPS Ability to Provide Limited Access Policy compliant Servers Restricted Network Example: Patch Enhanced Security Corporate Network Increased Business Value Microsoft Confidential Cisco and Microsoft Integration Story
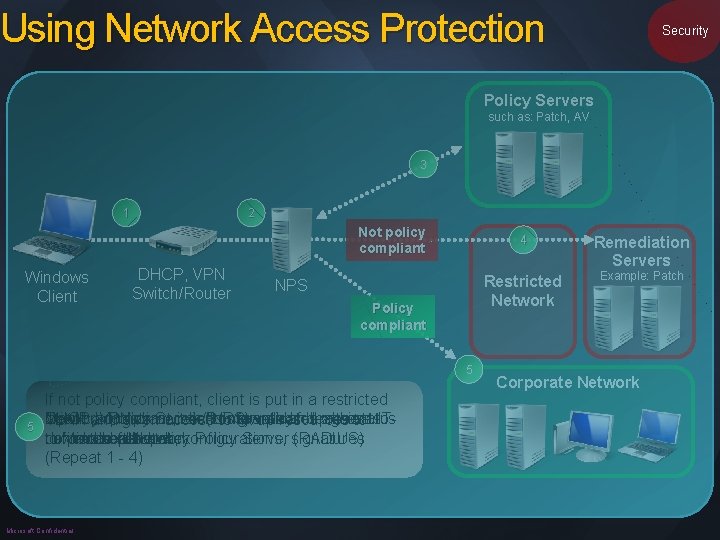
Using Network Access Protection Security Policy Servers such as: Patch, AV 3 1 2 Not policy compliant Windows Client DHCP, VPN Switch/Router NPS Policy compliant 5 2 3 4 5 1 If not policy compliant, client is put in a restricted Network Client DHCP, If policy requests VPN compliant, Policy or Switch/Router Server access client (NPS) toto isnetwork granted validates relays and full health presents against access status ITVLAN and given access fix up resources to to defined current to Microsoft corporate health network Network state policy Policy Server signatures (RADIUS) download patches, configurations, (Repeat 1 - 4) Microsoft Confidential 4 Remediation Servers Restricted Network Example: Patch Corporate Network
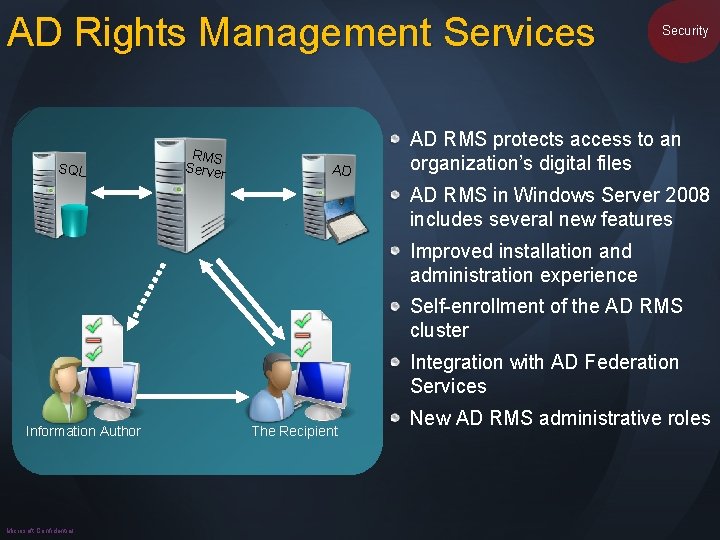
AD Rights Management Services SQL RMS Server AD Security AD RMS protects access to an organization’s digital files AD RMS in Windows Server 2008 includes several new features Improved installation and administration experience Self-enrollment of the AD RMS cluster Integration with AD Federation Services Information Author Microsoft Confidential The Recipient New AD RMS administrative roles
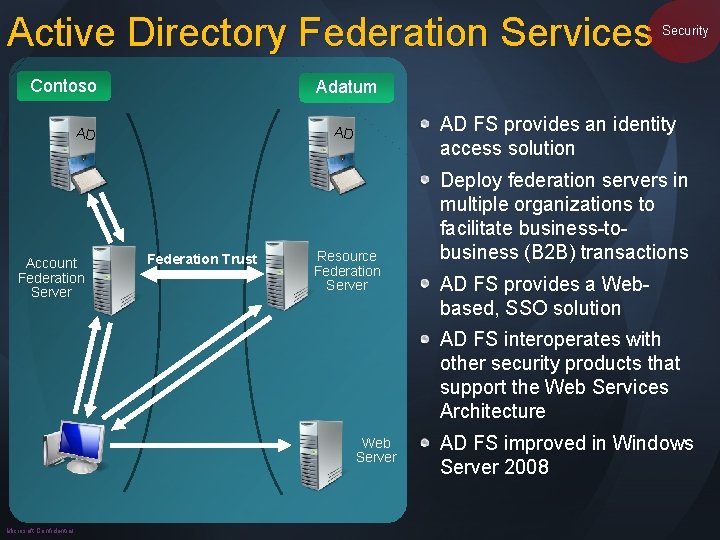
Active Directory Federation Services Contoso Adatum AD FS provides an identity access solution AD AD Account Federation Server Security Federation Trust Resource Federation Server Deploy federation servers in multiple organizations to facilitate business-tobusiness (B 2 B) transactions AD FS provides a Webbased, SSO solution AD FS interoperates with other security products that support the Web Services Architecture Web Server Microsoft Confidential AD FS improved in Windows Server 2008
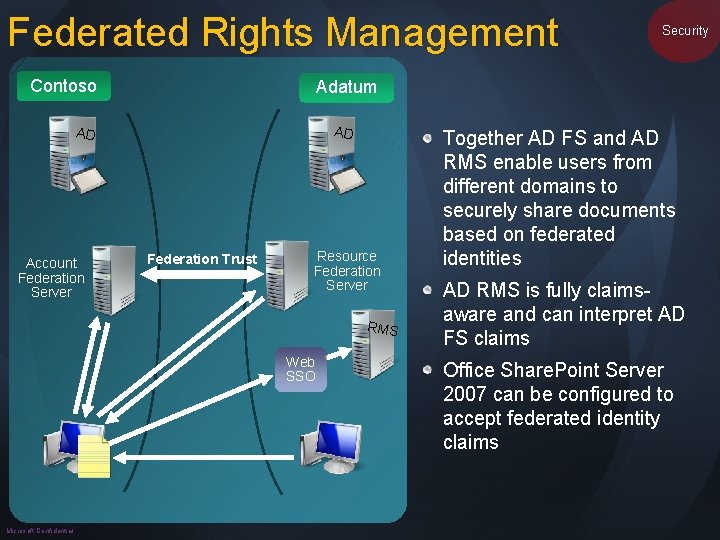
Federated Rights Management Contoso Adatum AD AD Account Federation Server Federation Trust Resource Federation Server RMS Web SSO Microsoft Confidential Security Together AD FS and AD RMS enable users from different domains to securely share documents based on federated identities AD RMS is fully claimsaware and can interpret AD FS claims Office Share. Point Server 2007 can be configured to accept federated identity claims
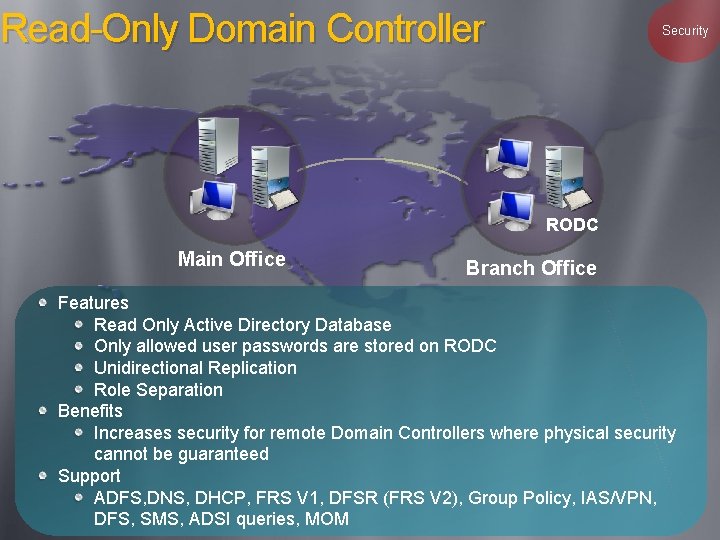
Read-Only Domain Controller Security RODC Main Office Branch Office Features Read Only Active Directory Database Only allowed user passwords are stored on RODC Unidirectional Replication Role Separation Benefits Increases security for remote Domain Controllers where physical security cannot be guaranteed Support ADFS, DNS, DHCP, FRS V 1, DFSR (FRS V 2), Group Policy, IAS/VPN, DFS, SMS, ADSI queries, MOM
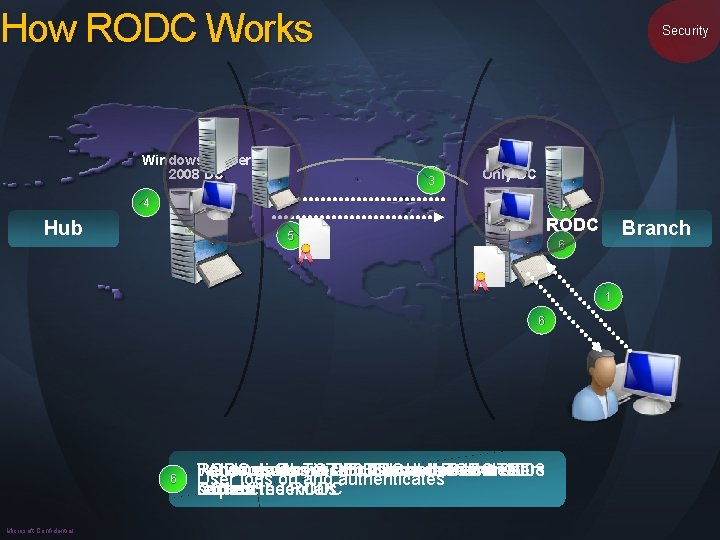
How RODC Works Windows Server 2008 DC Security 3 Read Only DC 4 2 Hub RODC 5 Branch 6 1 6 2 3 4 5 6 1 Microsoft Confidential RODC: Looks in DB: "I don't have the. TGT users RODC Forwards Windows Returns gives authentication Server Request 2008 toto. User Windows DC response and authenticates RODC Server and will 2008 User logs on TGT and authenticates secrets" DC request back cache tocredentials the RODC
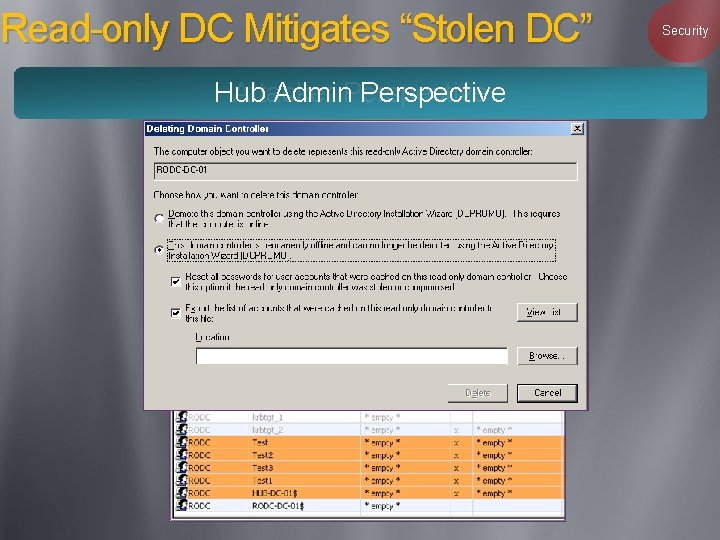
Read-only DC Mitigates “Stolen DC” Hub Admin. Perspective Attacker Security
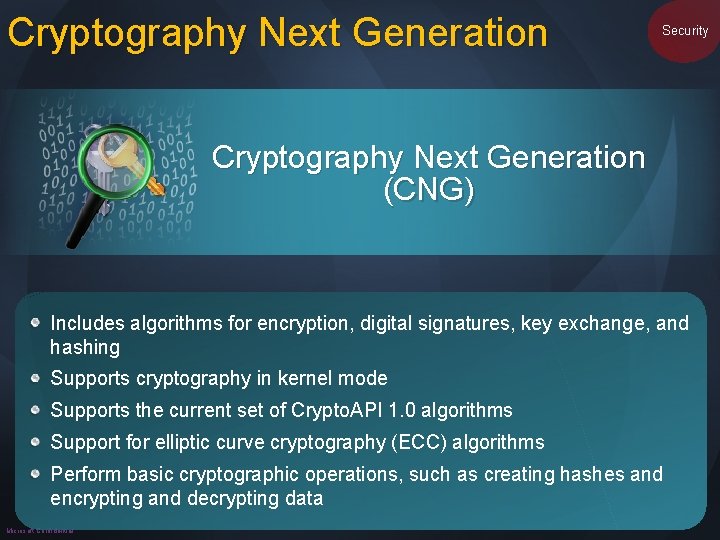
Cryptography Next Generation Security Cryptography Next Generation (CNG) Includes algorithms for encryption, digital signatures, key exchange, and hashing Supports cryptography in kernel mode Supports the current set of Crypto. API 1. 0 algorithms Support for elliptic curve cryptography (ECC) algorithms Perform basic cryptographic operations, such as creating hashes and encrypting and decrypting data Microsoft Confidential

Security Software Microsoft Confidential
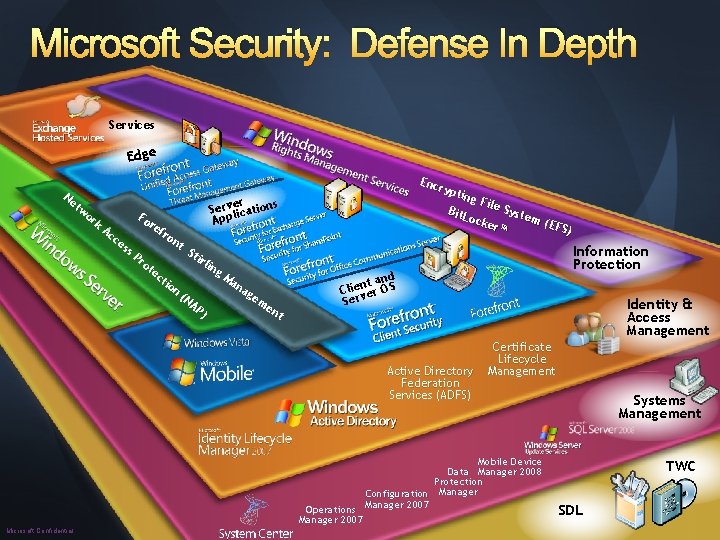
Microsoft Security: Defense In Depth Services Edge Ne tw or k Ac Fo ce re ss P ro t Edge er s Servlication p p A fro ec nt tio n St irl in g. M an ag e (N AP ) me nt Enc rypt ing File Syst Bit. L em ock (EFS er™ ) Server Applications nd nt a Cliever OS Ser Active Directory Federation Services (ADFS) Information Protection Client and Server OS Certificate Lifecycle Management Mobile Device Data Manager 2008 Protection Configuration Manager 2007 Operations Manager 2007 Microsoft Confidential Identity & Access Management Systems Management TWC SDL
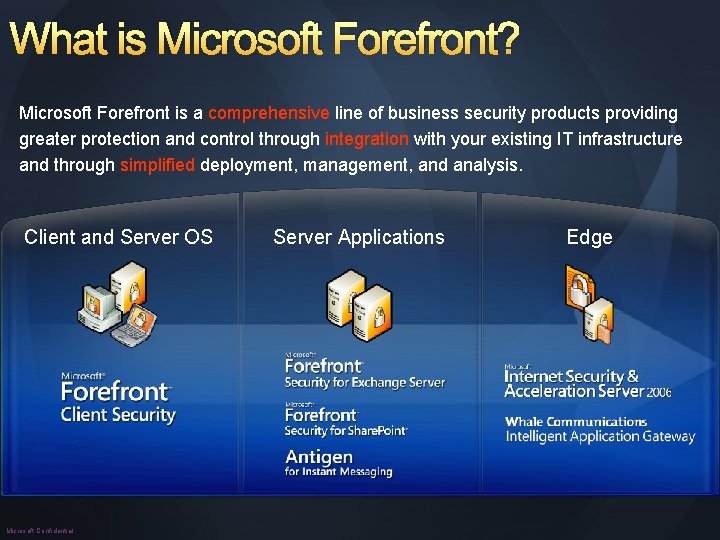
What is Microsoft Forefront? Microsoft Forefront is a comprehensive line of business security products providing greater protection and control through integration with your existing IT infrastructure and through simplified deployment, management, and analysis. Client and Server OS Microsoft Confidential Server Applications Edge
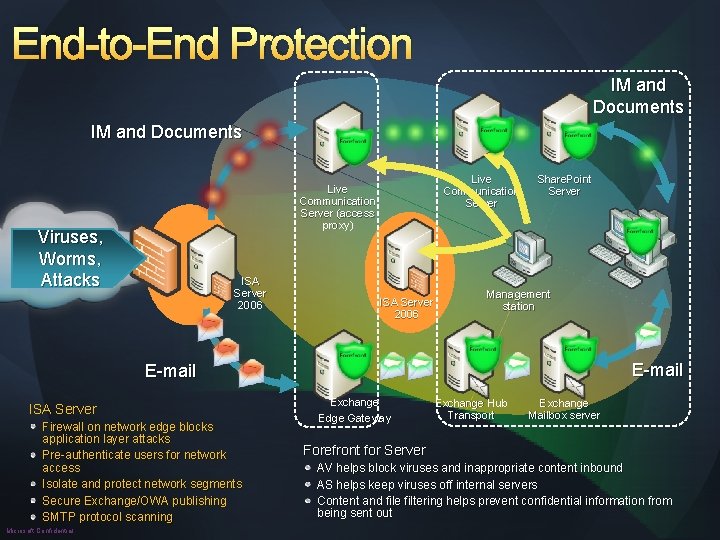
End-to-End Protection IM and Documents Live Communication Server (access proxy) Viruses, Worms, Attacks ISA Server 2006 Share. Point Server Management station E-mail ISA Server Firewall on network edge blocks application layer attacks Pre-authenticate users for network access Isolate and protect network segments Secure Exchange/OWA publishing SMTP protocol scanning Microsoft Confidential Exchange Edge Gateway Exchange Hub Transport Exchange Mailbox server Forefront for Server AV helps block viruses and inappropriate content inbound AS helps keep viruses off internal servers Content and file filtering helps prevent confidential information from being sent out
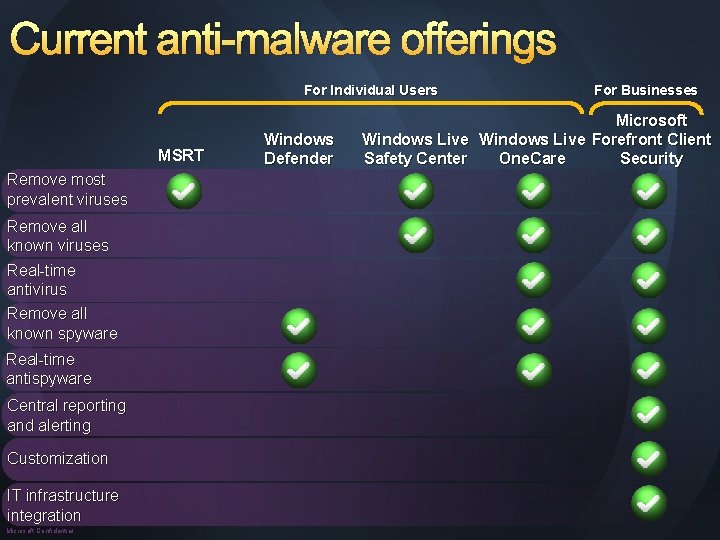
Current anti-malware offerings For Individual Users MSRT Remove most prevalent viruses Remove all known viruses Real-time antivirus Remove all known spyware Real-time antispyware Central reporting and alerting Customization IT infrastructure integration Microsoft Confidential Windows Defender For Businesses Microsoft Windows Live Forefront Client Security Safety Center One. Care

Security Management Microsoft Confidential
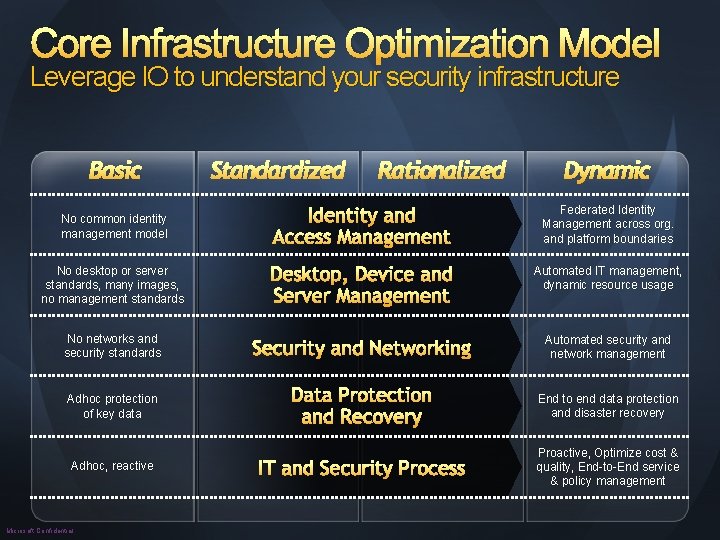
Core Infrastructure Optimization Model Leverage IO to understand your security infrastructure Basic Standardized Rationalized Dynamic No common identity management model Identity and Access Management Federated Identity Management across org. and platform boundaries No desktop or server standards, many images, no management standards Desktop, Device and Server Management Automated IT management, dynamic resource usage No networks and security standards Security and Networking Automated security and network management Adhoc protection of key data Data Protection and Recovery End to end data protection and disaster recovery IT and Security Process Proactive, Optimize cost & quality, End-to-End service & policy management Adhoc, reactive Microsoft Confidential
© 2006 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION. Microsoft Confidential
- Slides: 29