Windows Kernel Internals Common Coding Errors David B
Windows Kernel Internals Common Coding Errors David B. Probert, Ph. D. Windows Kernel Development Microsoft Corporation © Microsoft Corporation 1
Improving Software Resilience • Resilient to: – Attacks from malicious users – Resource limitations like low memory – Concurrency from multiple threads/processes and lock problems – Attempts to consume large amounts of scarce resources (memory, disk space, etc. ) – Being called from rarely seen but legitimate environments © Microsoft Corporation 2
Parameter Validation • Most important at interfaces that cross security boundaries • The following sub-types are common – Buffer length or numerical range check – Stack buffer overflows – Integer overflow and underflow – Probe and capture problems – Signed/Unsigned issues © Microsoft Corporation 3
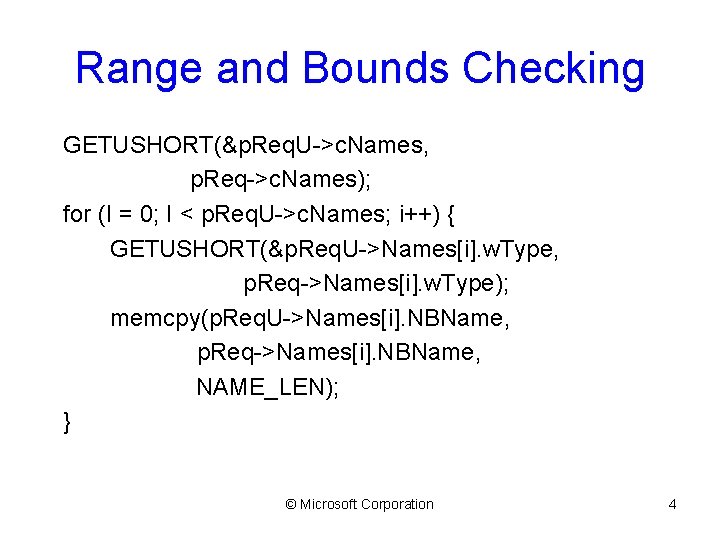
Range and Bounds Checking GETUSHORT(&p. Req. U->c. Names, p. Req->c. Names); for (I = 0; I < p. Req. U->c. Names; i++) { GETUSHORT(&p. Req. U->Names[i]. w. Type, p. Req->Names[i]. w. Type); memcpy(p. Req. U->Names[i]. NBName, p. Req->Names[i]. NBName, NAME_LEN); } © Microsoft Corporation 4
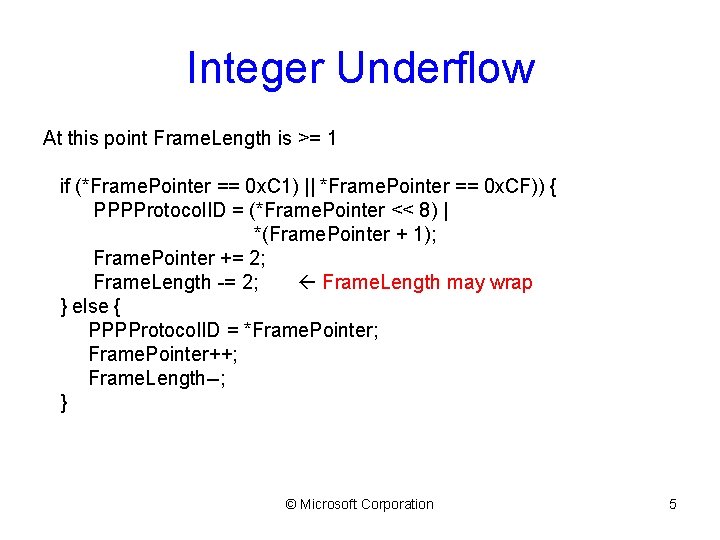
Integer Underflow At this point Frame. Length is >= 1 if (*Frame. Pointer == 0 x. C 1) || *Frame. Pointer == 0 x. CF)) { PPPProtocol. ID = (*Frame. Pointer << 8) | *(Frame. Pointer + 1); Frame. Pointer += 2; Frame. Length -= 2; Frame. Length may wrap } else { PPPProtocol. ID = *Frame. Pointer; Frame. Pointer++; Frame. Length--; } © Microsoft Corporation 5
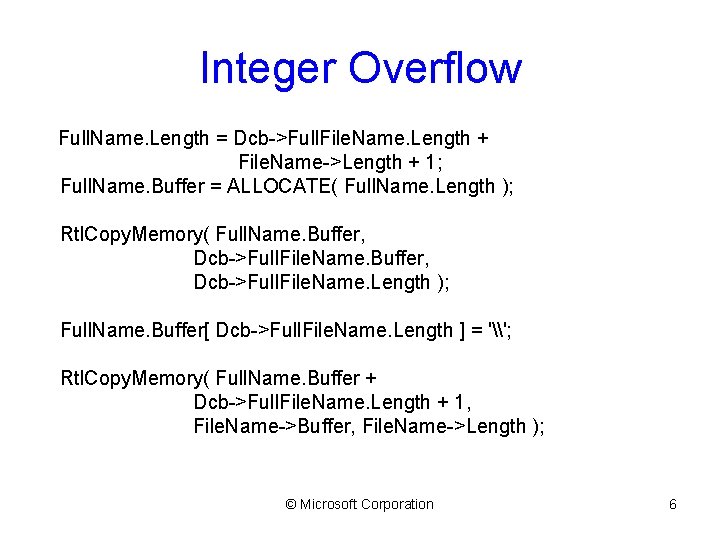
Integer Overflow Full. Name. Length = Dcb->Full. File. Name. Length + File. Name->Length + 1; Full. Name. Buffer = ALLOCATE( Full. Name. Length ); Rtl. Copy. Memory( Full. Name. Buffer, Dcb->Full. File. Name. Length ); Full. Name. Buffer[ Dcb->Full. File. Name. Length ] = '\'; Rtl. Copy. Memory( Full. Name. Buffer + Dcb->Full. File. Name. Length + 1, File. Name->Buffer, File. Name->Length ); © Microsoft Corporation 6
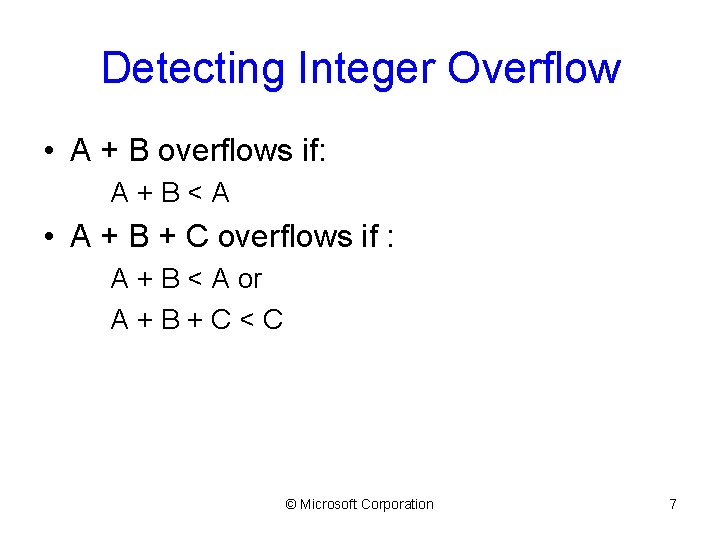
Detecting Integer Overflow • A + B overflows if: A+B<A • A + B + C overflows if : A + B < A or A+B+C<C © Microsoft Corporation 7
![Code Reordering For Overflows typdef struct _PATH_BUFFER { ULONG Path. Length; WCHAR Path[1]; } Code Reordering For Overflows typdef struct _PATH_BUFFER { ULONG Path. Length; WCHAR Path[1]; }](http://slidetodoc.com/presentation_image/197b89c6b6a0f2291f6c8db5671acc0e/image-8.jpg)
Code Reordering For Overflows typdef struct _PATH_BUFFER { ULONG Path. Length; WCHAR Path[1]; } PATH_BUFFER, *P PATH_BUFFER; RETVAL Set. Path (VOID *Buffer, ULONG Input. Length) { PATH_BUFFER Path. Buffer = Buffer; if (FIELD_OFFSET(PATH_BUFFER, Path[0]) + Path. Buffer->Path. Length > Input. Length) { return ERROR; } © Microsoft Corporation 8
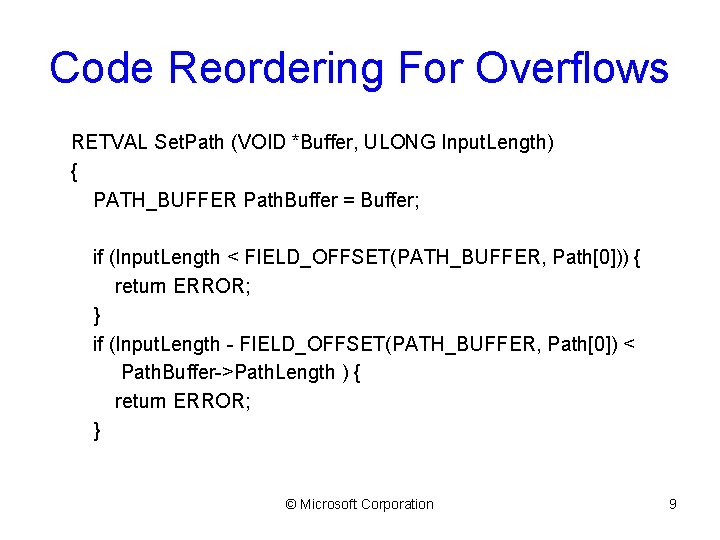
Code Reordering For Overflows RETVAL Set. Path (VOID *Buffer, ULONG Input. Length) { PATH_BUFFER Path. Buffer = Buffer; if (Input. Length < FIELD_OFFSET(PATH_BUFFER, Path[0])) { return ERROR; } if (Input. Length - FIELD_OFFSET(PATH_BUFFER, Path[0]) < Path. Buffer->Path. Length ) { return ERROR; } © Microsoft Corporation 9
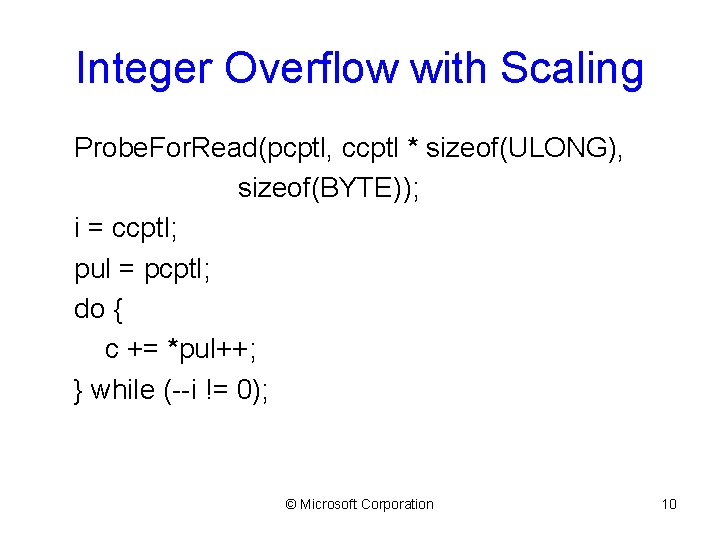
Integer Overflow with Scaling Probe. For. Read(pcptl, ccptl * sizeof(ULONG), sizeof(BYTE)); i = ccptl; pul = pcptl; do { c += *pul++; } while (--i != 0); © Microsoft Corporation 10
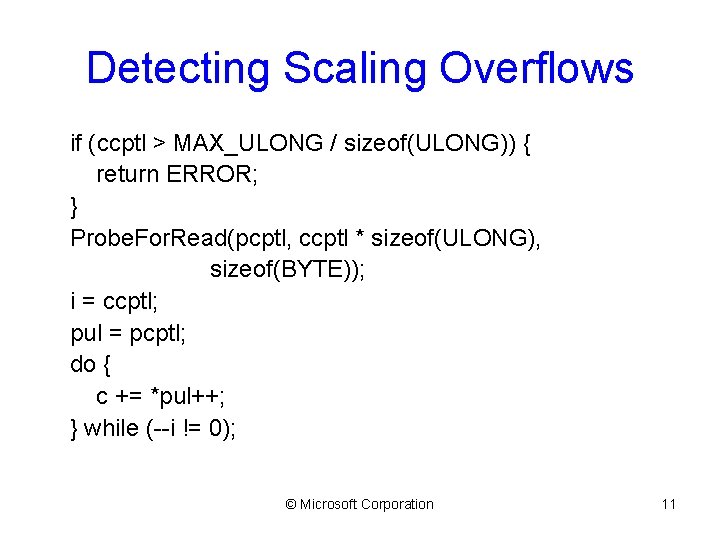
Detecting Scaling Overflows if (ccptl > MAX_ULONG / sizeof(ULONG)) { return ERROR; } Probe. For. Read(pcptl, ccptl * sizeof(ULONG), sizeof(BYTE)); i = ccptl; pul = pcptl; do { c += *pul++; } while (--i != 0); © Microsoft Corporation 11
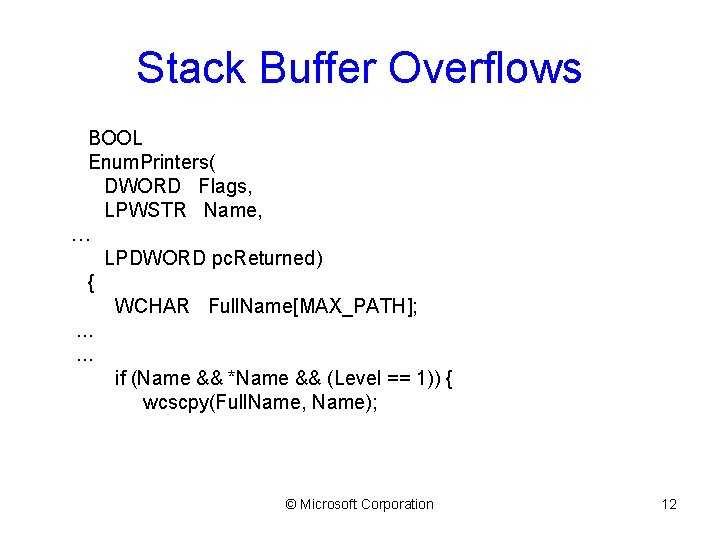
Stack Buffer Overflows BOOL Enum. Printers( DWORD Flags, LPWSTR Name, … LPDWORD pc. Returned) { WCHAR Full. Name[MAX_PATH]; . . . if (Name && *Name && (Level == 1)) { wcscpy(Full. Name, Name); © Microsoft Corporation 12
![Signed/Unsigned Issues typedef struct _EXCEPTION_RECORD { ULONG Number. Parameters; ULONG Exception. Information[EXCEPTION_MAXIMUM_PARAMETERS]; } EXCEPTION_RECORD; Signed/Unsigned Issues typedef struct _EXCEPTION_RECORD { ULONG Number. Parameters; ULONG Exception. Information[EXCEPTION_MAXIMUM_PARAMETERS]; } EXCEPTION_RECORD;](http://slidetodoc.com/presentation_image/197b89c6b6a0f2291f6c8db5671acc0e/image-13.jpg)
Signed/Unsigned Issues typedef struct _EXCEPTION_RECORD { ULONG Number. Parameters; ULONG Exception. Information[EXCEPTION_MAXIMUM_PARAMETERS]; } EXCEPTION_RECORD; LONG Length; Length = Exception. Record->Number. Parameters; if (Length > EXCEPTION_MAXIMUM_PARAMETERS) { return STATUS_INVALID_PARAMETER; } Length = (sizeof(EXCEPTION_RECORD) + ((Length - EXCEPTION_MAXIMUM_PARAMETERS) * sizeof(ULONG))); © Microsoft Corporation 13
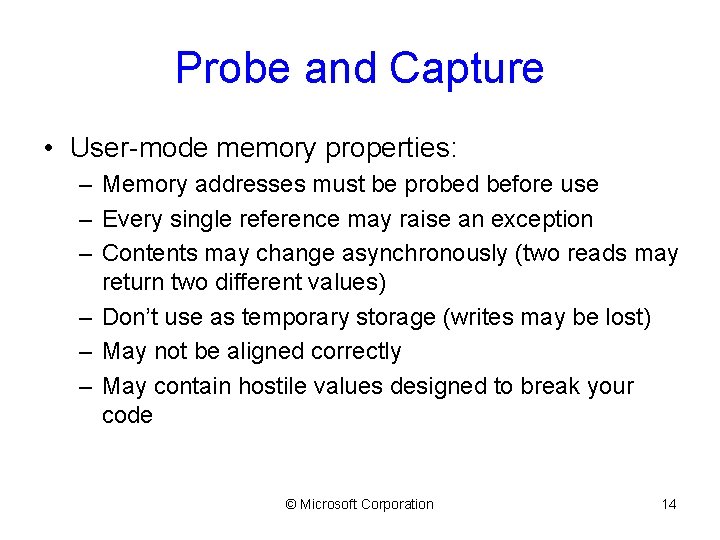
Probe and Capture • User-mode memory properties: – Memory addresses must be probed before use – Every single reference may raise an exception – Contents may change asynchronously (two reads may return two different values) – Don’t use as temporary storage (writes may be lost) – May not be aligned correctly – May contain hostile values designed to break your code © Microsoft Corporation 14
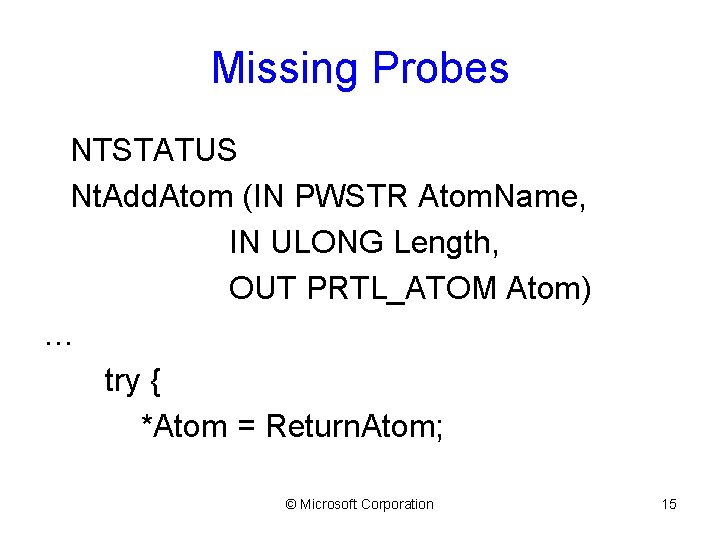
Missing Probes NTSTATUS Nt. Add. Atom (IN PWSTR Atom. Name, IN ULONG Length, OUT PRTL_ATOM Atom) … try { *Atom = Return. Atom; © Microsoft Corporation 15
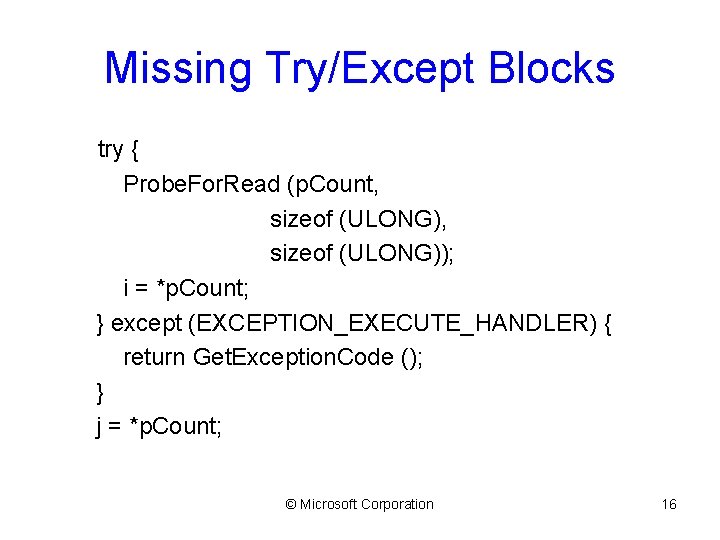
Missing Try/Except Blocks try { Probe. For. Read (p. Count, sizeof (ULONG)); i = *p. Count; } except (EXCEPTION_EXECUTE_HANDLER) { return Get. Exception. Code (); } j = *p. Count; © Microsoft Corporation 16
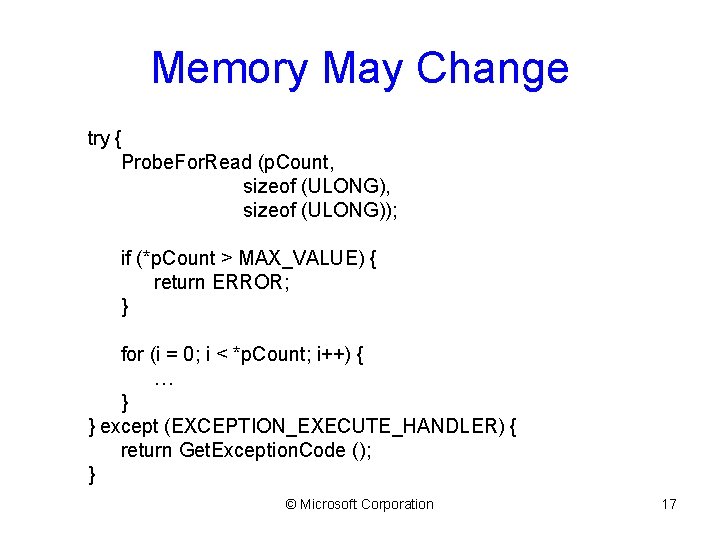
Memory May Change try { Probe. For. Read (p. Count, sizeof (ULONG)); if (*p. Count > MAX_VALUE) { return ERROR; } for (i = 0; i < *p. Count; i++) { … } } except (EXCEPTION_EXECUTE_HANDLER) { return Get. Exception. Code (); } © Microsoft Corporation 17
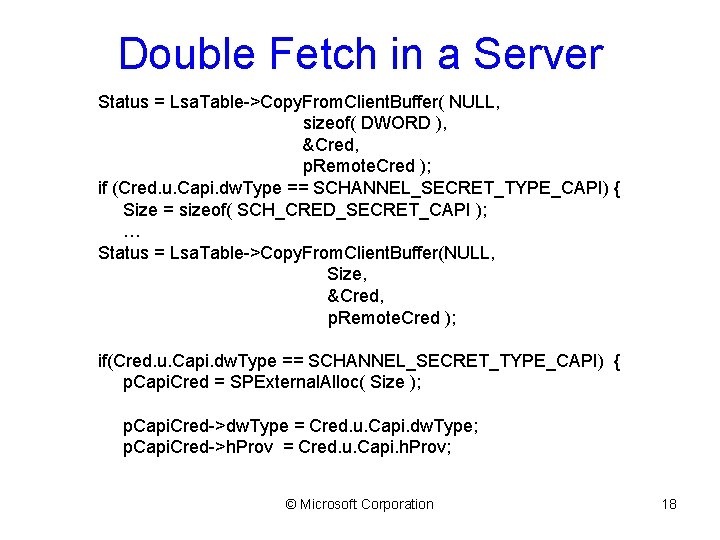
Double Fetch in a Server Status = Lsa. Table->Copy. From. Client. Buffer( NULL, sizeof( DWORD ), &Cred, p. Remote. Cred ); if (Cred. u. Capi. dw. Type == SCHANNEL_SECRET_TYPE_CAPI) { Size = sizeof( SCH_CRED_SECRET_CAPI ); … Status = Lsa. Table->Copy. From. Client. Buffer(NULL, Size, &Cred, p. Remote. Cred ); if(Cred. u. Capi. dw. Type == SCHANNEL_SECRET_TYPE_CAPI) { p. Capi. Cred = SPExternal. Alloc( Size ); p. Capi. Cred->dw. Type = Cred. u. Capi. dw. Type; p. Capi. Cred->h. Prov = Cred. u. Capi. h. Prov; © Microsoft Corporation 18
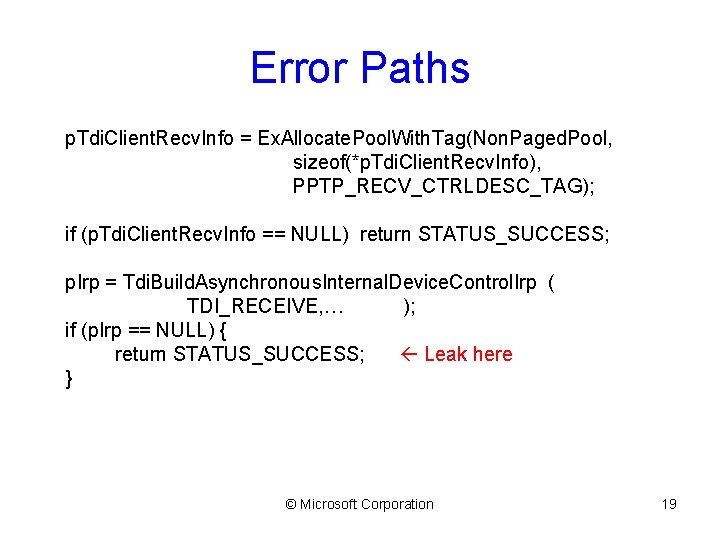
Error Paths p. Tdi. Client. Recv. Info = Ex. Allocate. Pool. With. Tag(Non. Paged. Pool, sizeof(*p. Tdi. Client. Recv. Info), PPTP_RECV_CTRLDESC_TAG); if (p. Tdi. Client. Recv. Info == NULL) return STATUS_SUCCESS; p. Irp = Tdi. Build. Asynchronous. Internal. Device. Control. Irp ( TDI_RECEIVE, … ); if (p. Irp == NULL) { return STATUS_SUCCESS; Leak here } © Microsoft Corporation 19
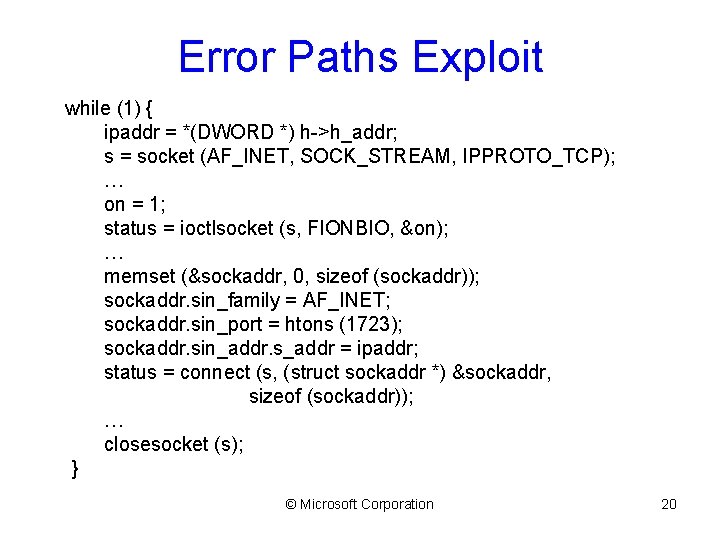
Error Paths Exploit while (1) { ipaddr = *(DWORD *) h->h_addr; s = socket (AF_INET, SOCK_STREAM, IPPROTO_TCP); … on = 1; status = ioctlsocket (s, FIONBIO, &on); … memset (&sockaddr, 0, sizeof (sockaddr)); sockaddr. sin_family = AF_INET; sockaddr. sin_port = htons (1723); sockaddr. sin_addr. s_addr = ipaddr; status = connect (s, (struct sockaddr *) &sockaddr, sizeof (sockaddr)); … closesocket (s); } © Microsoft Corporation 20
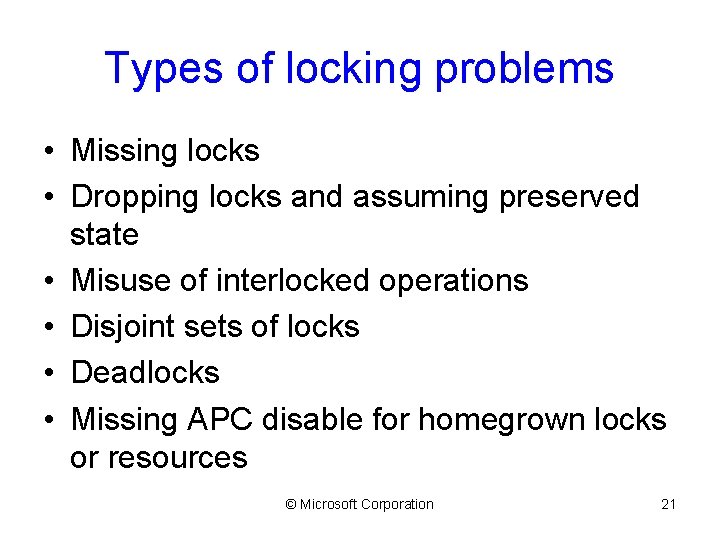
Types of locking problems • Missing locks • Dropping locks and assuming preserved state • Misuse of interlocked operations • Disjoint sets of locks • Deadlocks • Missing APC disable for homegrown locks or resources © Microsoft Corporation 21
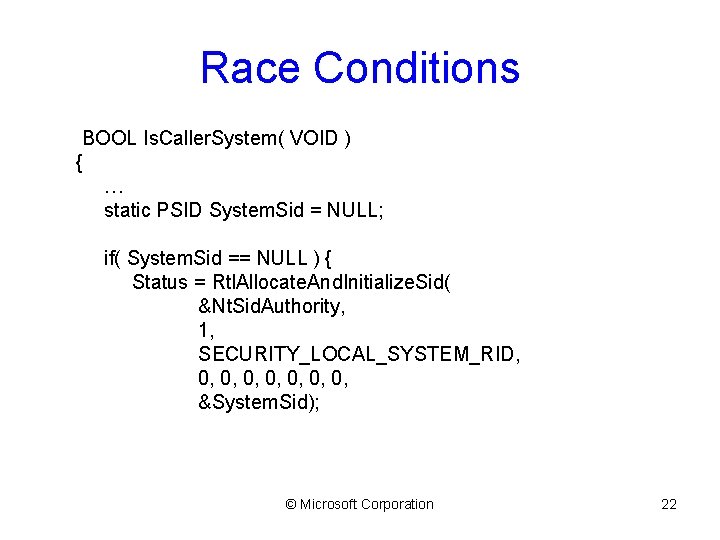
Race Conditions BOOL Is. Caller. System( VOID ) { … static PSID System. Sid = NULL; if( System. Sid == NULL ) { Status = Rtl. Allocate. And. Initialize. Sid( &Nt. Sid. Authority, 1, SECURITY_LOCAL_SYSTEM_RID, 0, 0, &System. Sid); © Microsoft Corporation 22
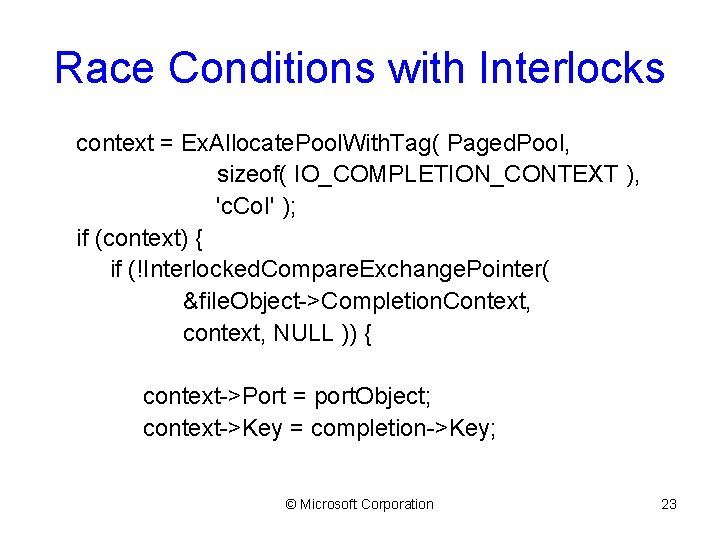
Race Conditions with Interlocks context = Ex. Allocate. Pool. With. Tag( Paged. Pool, sizeof( IO_COMPLETION_CONTEXT ), 'c. Co. I' ); if (context) { if (!Interlocked. Compare. Exchange. Pointer( &file. Object->Completion. Context, context, NULL )) { context->Port = port. Object; context->Key = completion->Key; © Microsoft Corporation 23
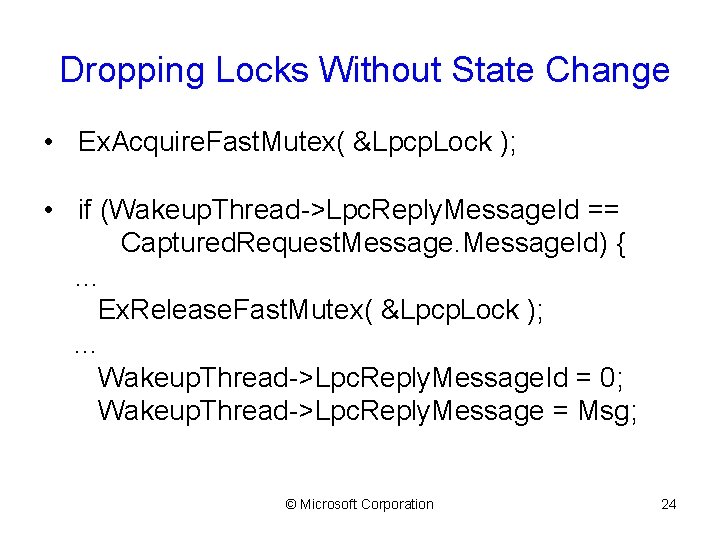
Dropping Locks Without State Change • Ex. Acquire. Fast. Mutex( &Lpcp. Lock ); • if (Wakeup. Thread->Lpc. Reply. Message. Id == Captured. Request. Message. Id) { … Ex. Release. Fast. Mutex( &Lpcp. Lock ); . . . Wakeup. Thread->Lpc. Reply. Message. Id = 0; Wakeup. Thread->Lpc. Reply. Message = Msg; © Microsoft Corporation 24
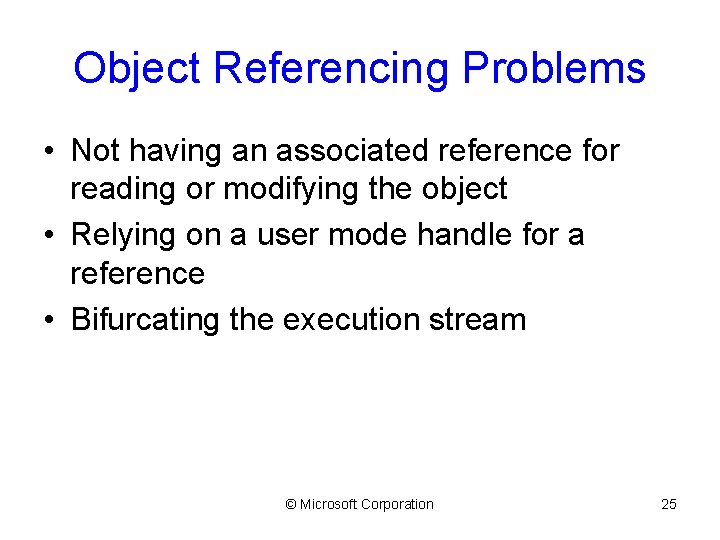
Object Referencing Problems • Not having an associated reference for reading or modifying the object • Relying on a user mode handle for a reference • Bifurcating the execution stream © Microsoft Corporation 25
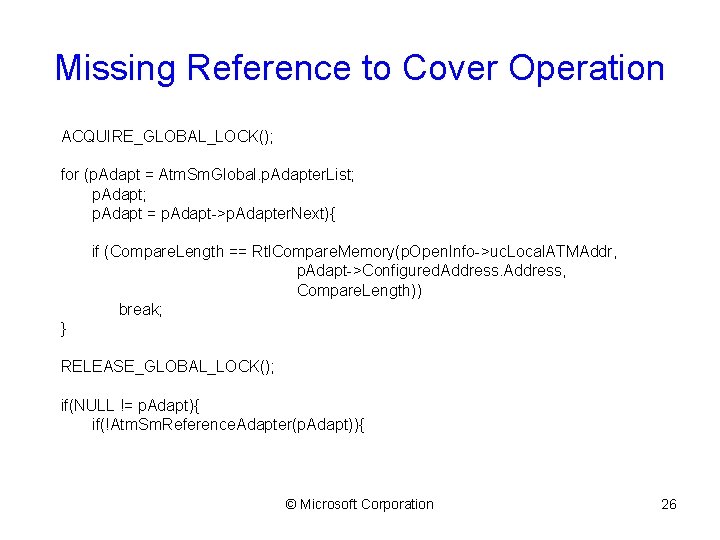
Missing Reference to Cover Operation ACQUIRE_GLOBAL_LOCK(); for (p. Adapt = Atm. Sm. Global. p. Adapter. List; p. Adapt = p. Adapt->p. Adapter. Next){ if (Compare. Length == Rtl. Compare. Memory(p. Open. Info->uc. Local. ATMAddr, p. Adapt->Configured. Address, Compare. Length)) break; } RELEASE_GLOBAL_LOCK(); if(NULL != p. Adapt){ if(!Atm. Sm. Reference. Adapter(p. Adapt)){ © Microsoft Corporation 26
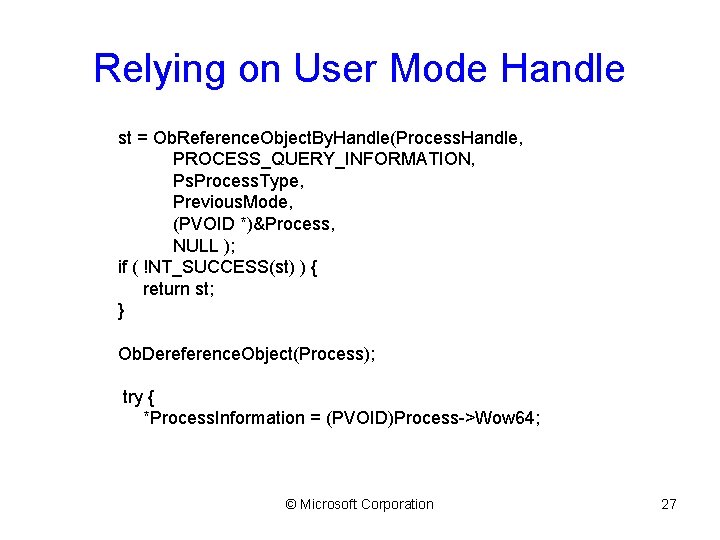
Relying on User Mode Handle st = Ob. Reference. Object. By. Handle(Process. Handle, PROCESS_QUERY_INFORMATION, Ps. Process. Type, Previous. Mode, (PVOID *)&Process, NULL ); if ( !NT_SUCCESS(st) ) { return st; } Ob. Dereference. Object(Process); try { *Process. Information = (PVOID)Process->Wow 64; © Microsoft Corporation 27
Summary • Most errors could be limited by knowing your application environment • Code for hostile and failure prone environments • Test failure paths with fault injection © Microsoft Corporation 28
Discussion © Microsoft Corporation 29
- Slides: 29