Windows Defender ATP Robert Turnek NIL IT Architect

Windows Defender ATP Robert Turnšek, NIL IT Architect Microsoft p-seller
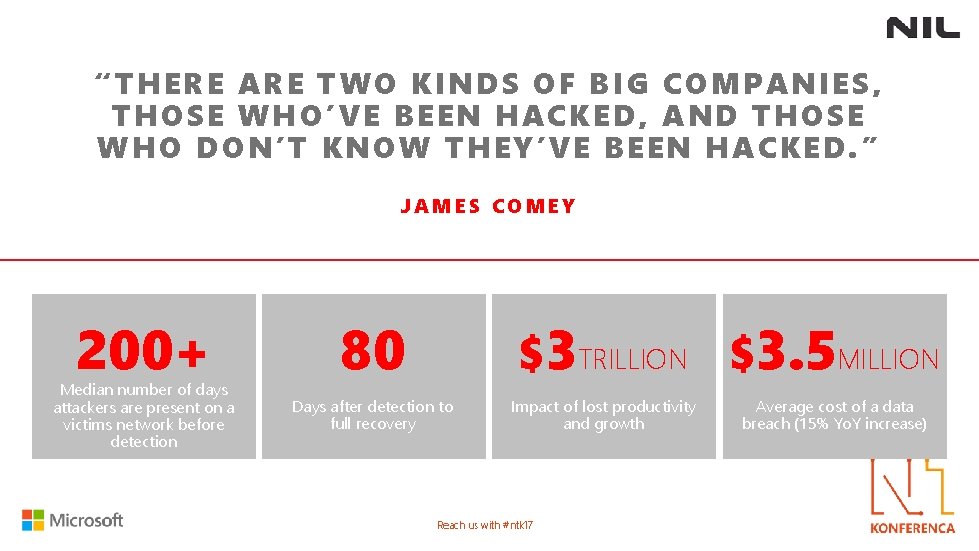
“ THERE ARE TW O KINDS OF BIG COMPANIES, THOSE WHO’ VE BEEN HACKE D, AND TH OSE WHO DON’ T KNOW THEY’VE BEEN H ACKED. ” JAMES COMEY 200+ Median number of days attackers are present on a victims network before detection 80 $3 TRILLION $3. 5 MILLION Days after detection to full recovery Impact of lost productivity and growth Reach us with #ntk 17 Average cost of a data breach (15% Yo. Y increase)

Reach us with #ntk 17
Reach us with #ntk 17

Reach us with #ntk 17
§ Highly Skilled § Well funded § New attack surface § Collaborate • Carbanak, a malicious banking campaign by organized group stole $300 million to $1 billion in total from more than 100 banks. Reach us with #ntk 17
Protecting against attacks is more challenging than ever § Increased amount of data § Cost- cyber-insurance policies are becoming a new operating expense Reach us with #ntk 17
Reach us with #ntk 17
Reach us with #ntk 17
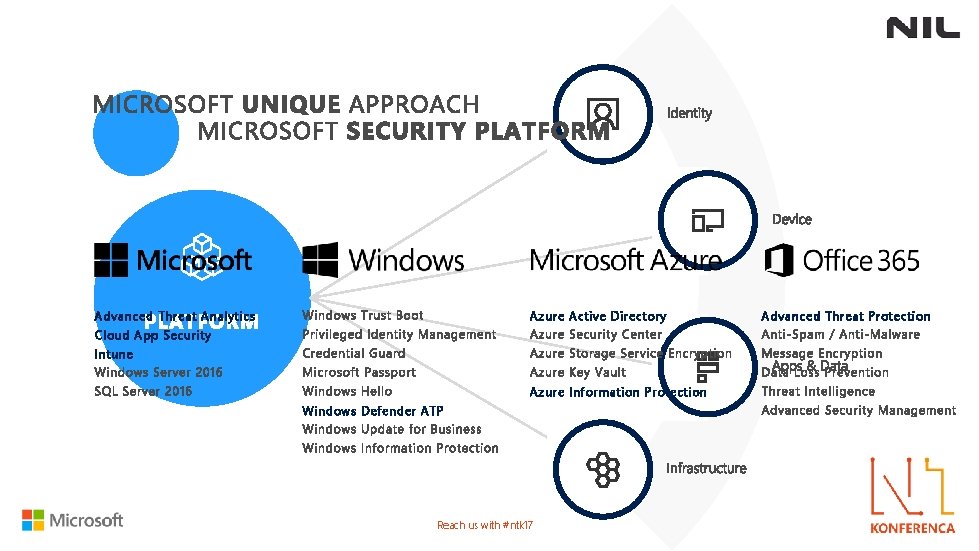
Advanced Threat Analytics Azure Active Directory Cloud App Security Intune Azure Information Protection Windows Defender ATP Reach us with #ntk 17 Advanced Threat Protection
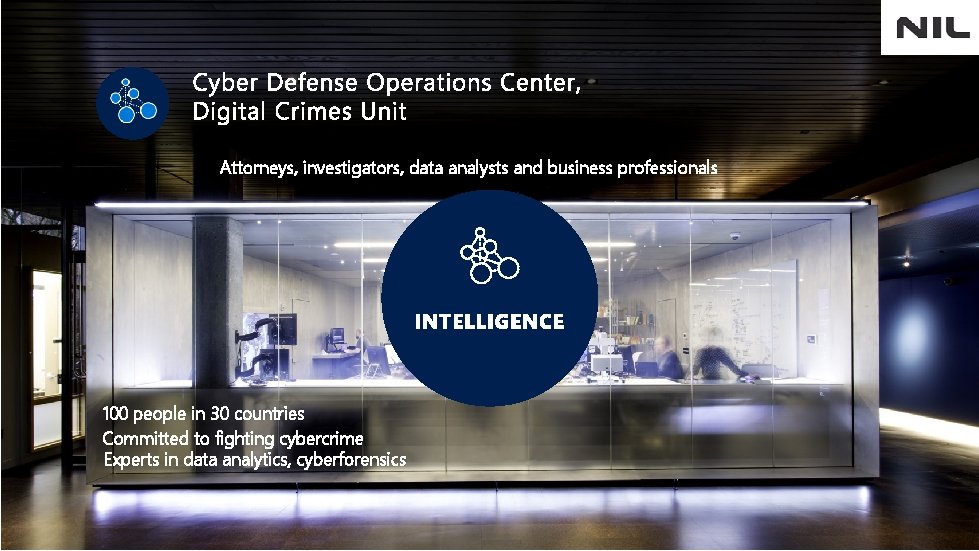
Attorneys, investigators, data analysts and business professionals 100 people in 30 countries Committed to fighting cybercrime Experts in data analytics, cyberforensics Reach us with #ntk 17
Reach us with #ntk 17

Not Anti-Virus

Nearly 1 Million new Malware threats released every day Reach us with #ntk 17
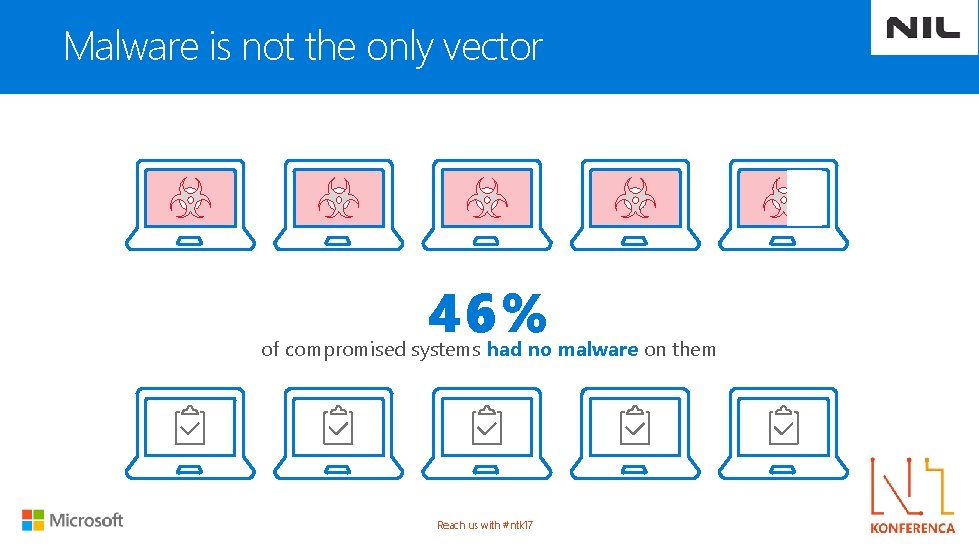
Malware is not the only vector 46% of compromised systems had no malware on them Reach us with #ntk 17
“APT” – Advanced Persistent Threat Reach us with #ntk 17
Attackers are hard to detect 200+ DAYS Median number of days attackers are present on a victims network before detection Reach us with #ntk 17
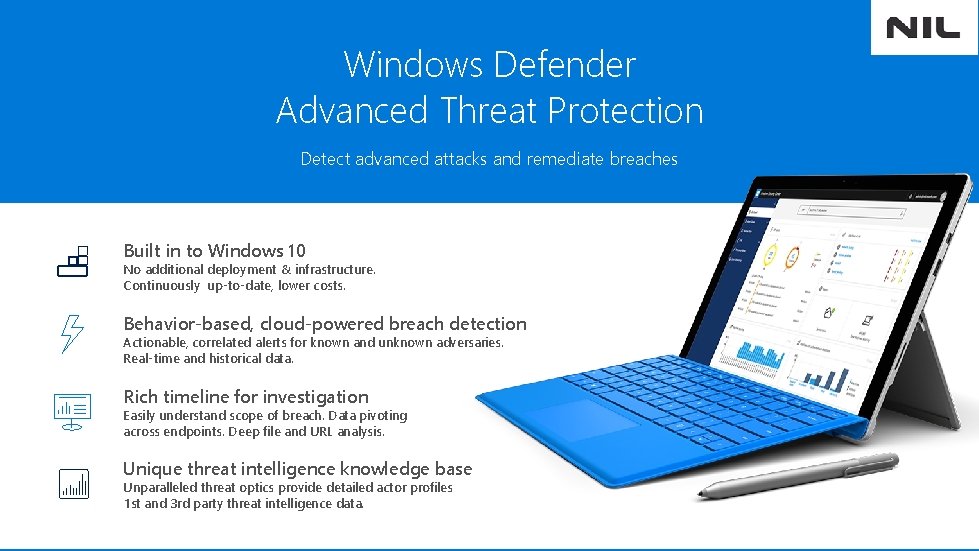
Windows Defender Advanced Threat Protection Detect advanced attacks and remediate breaches Built in to Windows 10 No additional deployment & infrastructure. Continuously up-to-date, lower costs. Behavior-based, cloud-powered breach detection Actionable, correlated alerts for known and unknown adversaries. Real-time and historical data. Rich timeline for investigation Easily understand scope of breach. Data pivoting across endpoints. Deep file and URL analysis. Unique threat intelligence knowledge base Unparalleled threat optics provide detailed actor profiles 1 st and 3 rd party threat intelligence data. Reach us with #ntk 17
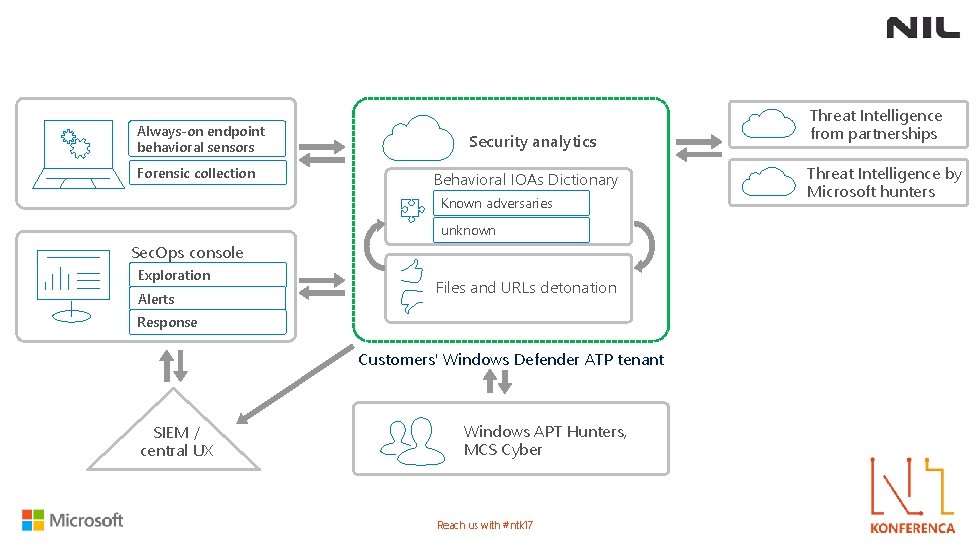
Always-on endpoint behavioral sensors Forensic collection Security analytics Behavioral IOAs Dictionary Known adversaries unknown Sec. Ops console Exploration Alerts Files and URLs detonation Response Customers' Windows Defender ATP tenant SIEM / central. SIEM UX Windows APT Hunters, MCS Cyber Reach us with #ntk 17 Threat Intelligence from partnerships Threat Intelligence by Microsoft hunters
INTEGRATION WITH WINDOWS DEFENDER / SCEP Reach us with #ntk 17
Gartner Category: Endpoint Detection and Response (EDR) The endpoint detection and response (EDR) market is an emerging security technology created to continuously provide early identification of ongoing advanced attacks and to more rapidly respond to detected attacks. Solutions that have the following capabilities: 1. Detect security incidents at the endpoint 2. Investigate security incidents 3. Contain the incident 4. Remediate endpoints to a pre-infection state Reach us with #ntk 17
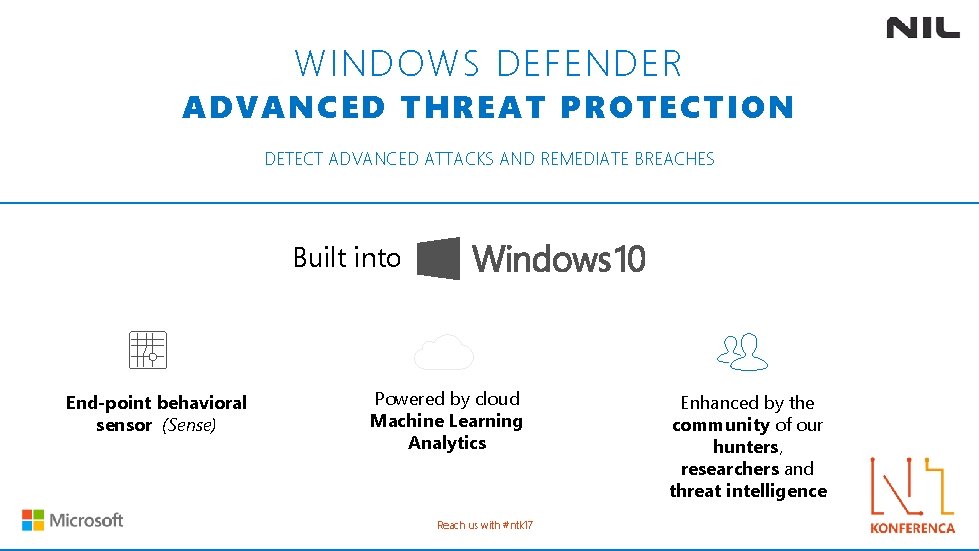
WINDOWS DEFENDER ADVANCED THREAT PROTECTION DETECT ADVANCED ATTACKS AND REMEDIATE BREACHES Built into End-point behavioral sensor (Sense) Powered by cloud Machine Learning Analytics Reach us with #ntk 17 Enhanced by the community of our hunters, researchers and threat intelligence
? IOC IOA Reach us with #ntk 17
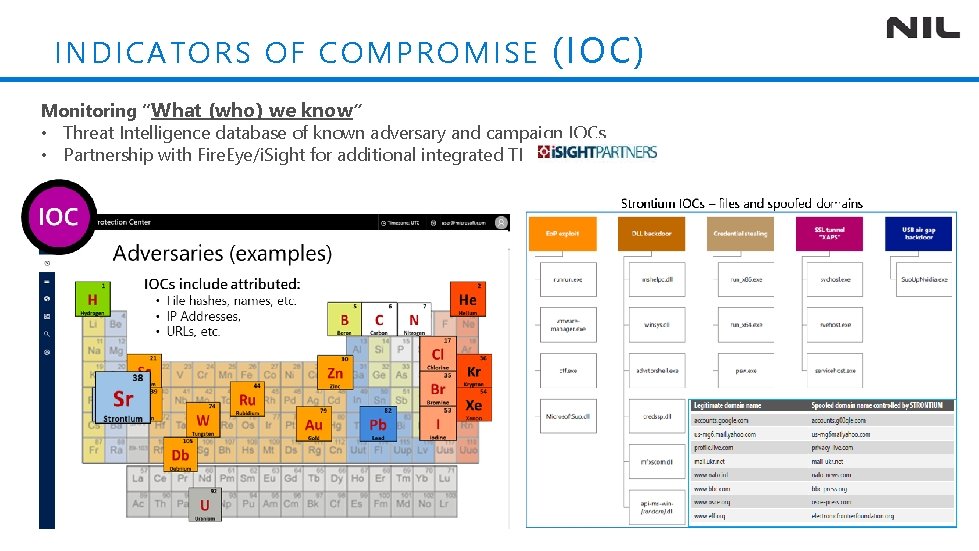
INDI CATORS O F COMPROMISE (IOC) Monitoring “What (who) we know” • Threat Intelligence database of known adversary and campaign IOCs • Partnership with Fire. Eye/i. Sight for additional integrated TI
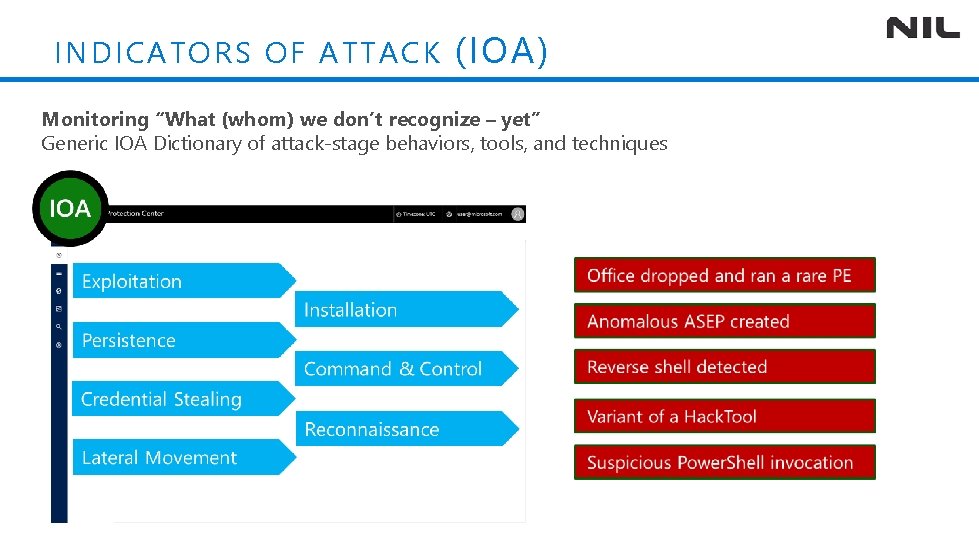
INDI CATORS O F ATTACK (IOA) Monitoring “What (whom) we don’t recognize – yet” Generic IOA Dictionary of attack-stage behaviors, tools, and techniques

Built in Not bolted on Compatible with other security products Kernel Sensor High Performance Reach us with #ntk 17
Best investigation experience Watch Everything Time Travel Detonation
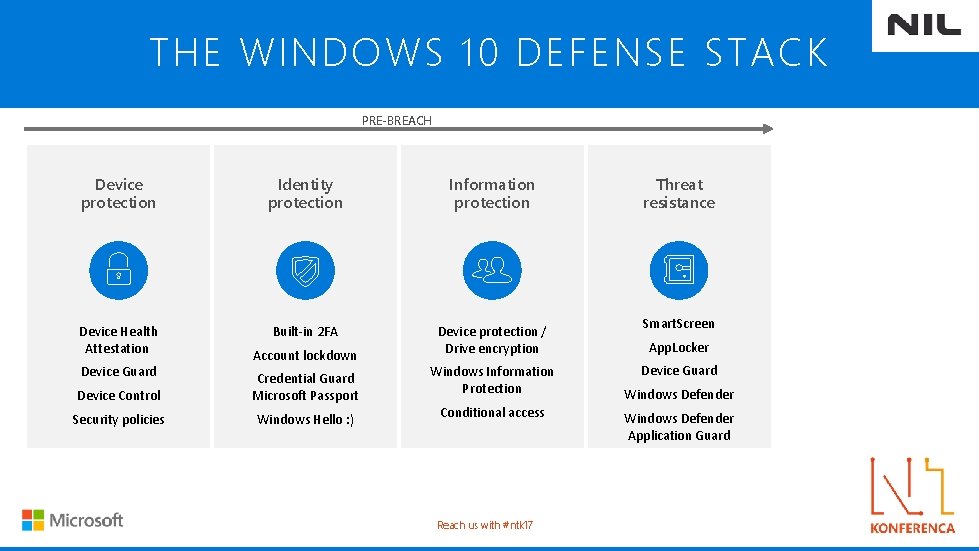
THE WINDOWS 10 DEFENSE STACK PRE-BREACH Device protection Threat Identity resistance protection Information Identity protection Device Health Attestation attestation Smart. Screen Built-in 2 FA Device protection / Built-in 2 FA Drive encryption Account lockdown Windows Information Credential Guard Protection Microsoft Passport Conditional access Windows Hello ; ) Device Guard Device Control Security policies Account lockdown App. Locker Credential Guard Device Guard Microsoft Passport Windows Defender Windows Hello : ) Network/Firewall Reach us with #ntk 17 Information Threat protection resistance Smart. Screen Device protection / App. Locker Drive encryption Device Guard Enterprise Data Protection Windows Defender Conditional access Windows Defender Application Guard
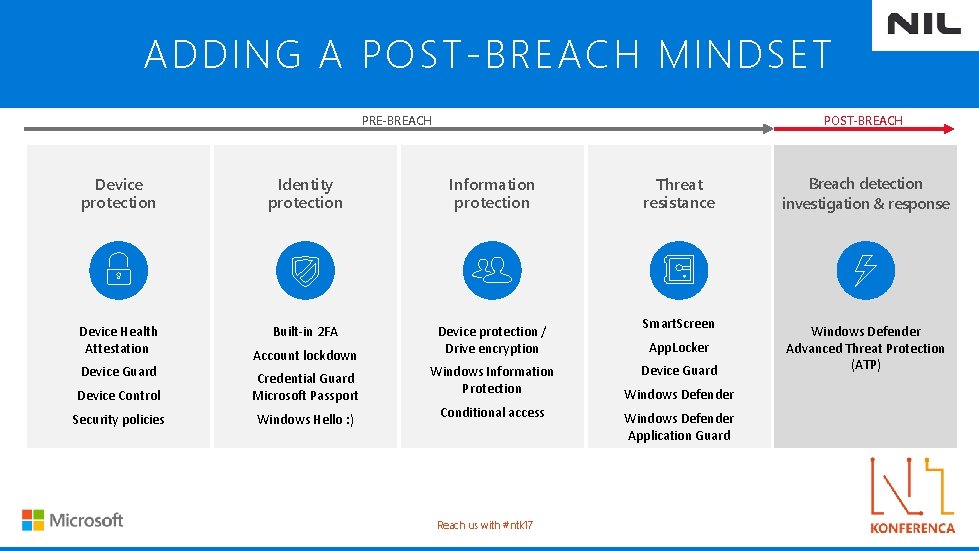
ADDING A POST-BREACH MINDSET PRE-BREACH POST-BREACH Device protection Threat Identity resistance protection Information Identity protection Device Health Attestation attestation Smart. Screen Built-in 2 FA Device protection / Built-in 2 FA Drive encryption Account lockdown Windows Information Credential Guard Protection Microsoft Passport Conditional access Windows Hello ; ) Device Guard Device Control Security policies Account lockdown App. Locker Credential Guard Device Guard Microsoft Passport Windows Defender Windows Hello : ) Network/Firewall Reach us with #ntk 17 Information Threat protection resistance Smart. Screen Device protection / App. Locker Drive encryption Device Guard Enterprise Data Protection Windows Defender Conditional access Windows Defender Application Guard Breach detection investigation & response Windows Defender ATP Windows Defender Advanced Threat Protection (ATP)
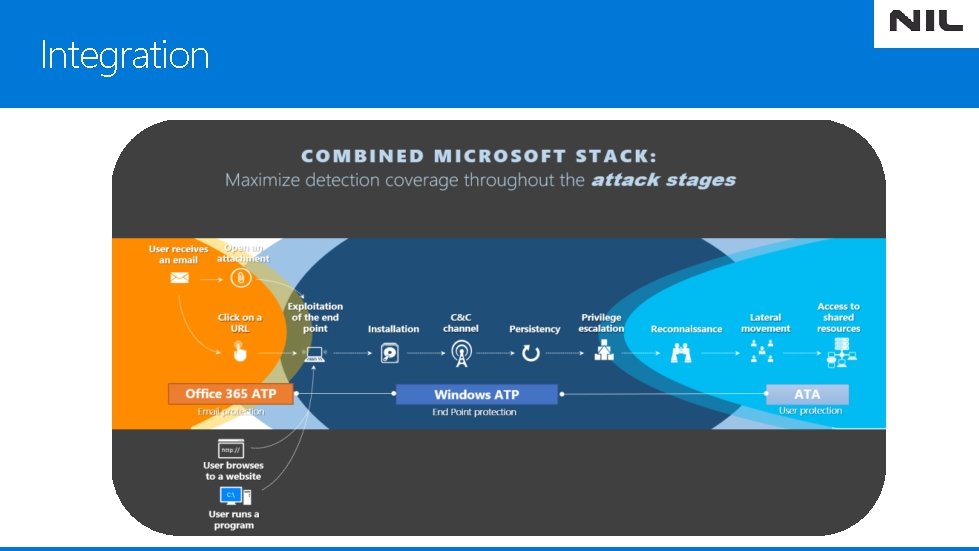
Integration
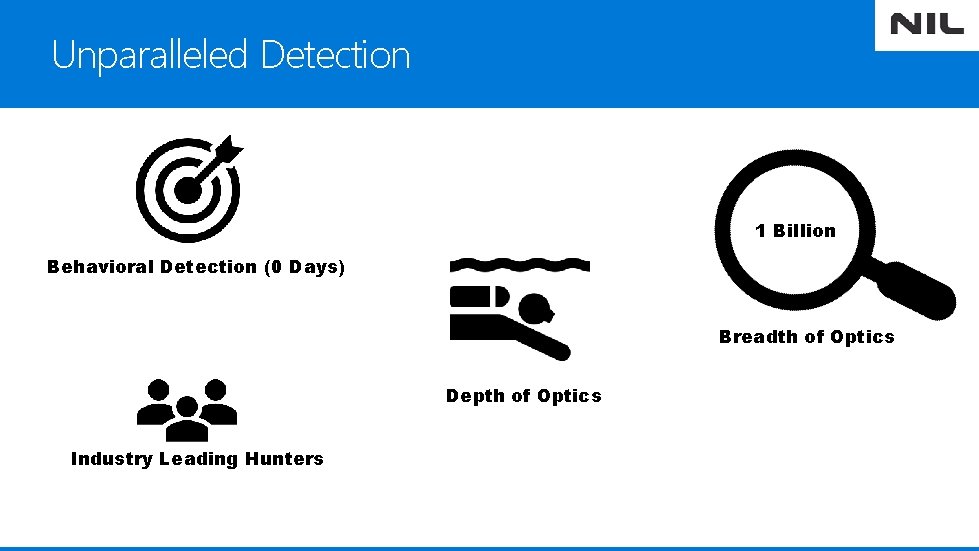
Unparalleled Detection 1 Billion Behavioral Detection (0 Days) Breadth of Optics Depth of Optics Industry Leading Hunters
Cloud Powered Detection Service Cloud ( hidden from attacker) Infinite Scale out Non Domain Joined Stream of new features ( outside Windows )

Remember 1. 2. 3. Built-In - No on premise infrastructure Integration Most Data

More Information https: //aka. ms/wdatp Tech. Net resources @ https: //aka. ms/technet-wdatp Read MSFT Case Study @ https: //t. co/pa. X 7 MQhez. U

- Slides: 39