Windows 7 Bit Locker Configuration and Deployment Paul


Windows 7 Bit. Locker: Configuration and Deployment Paul A. Cooke - CISSP Director Microsoft Session Code: CLI 311
Windows Vista Bit. Locker Encrypts the OS volume Helps prevent the unauthorized disclosure of data when it is at rest Designed to utilize a Trusted Platform Module (TPM) v 1. 2 Secure key storage Boot Integrity Vista SP 1 added support for multivolume/drive protection!
Windows 7 Bit. Locker What’s New • Bit. Locker Enhancements Automatic 100 Mb hidden boot partition New Key Protectors Domain Recovery Agent (DRA) Passwords Smart card Auto-Unlock
Windows 7 Bit. Locker What’s New Bit. Locker To Go Support for FAT* Protectors: DRA, passphrase, smart card and/or auto-unlock Management: protector configuration, encryption enforcement Read-only access on Windows Vista & Windows XP

Architectural Overview
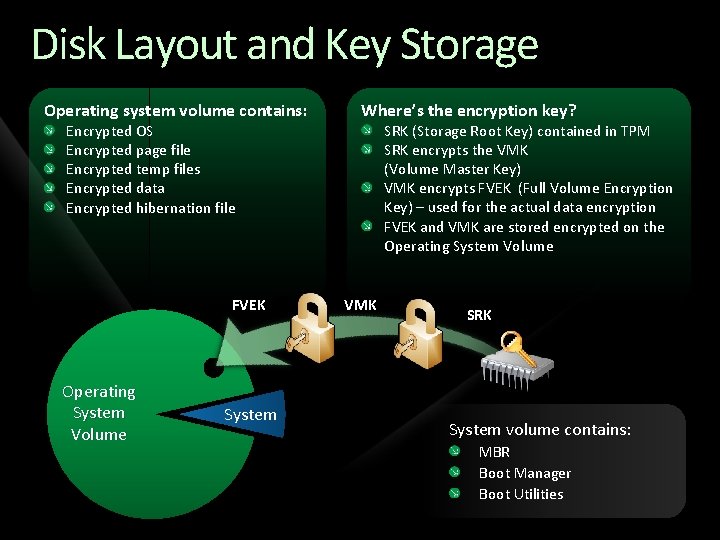
Disk Layout and Key Storage Operating system volume contains: Encrypted OS Encrypted page file Encrypted temp files Encrypted data Encrypted hibernation file FVEK Operating System Volume System Where’s the encryption key? SRK (Storage Root Key) contained in TPM SRK encrypts the VMK (Volume Master Key) VMK encrypts FVEK (Full Volume Encryption Key) – used for the actual data encryption FVEK and VMK are stored encrypted on the Operating System Volume VMK SRK System volume contains: MBR Boot Manager Boot Utilities
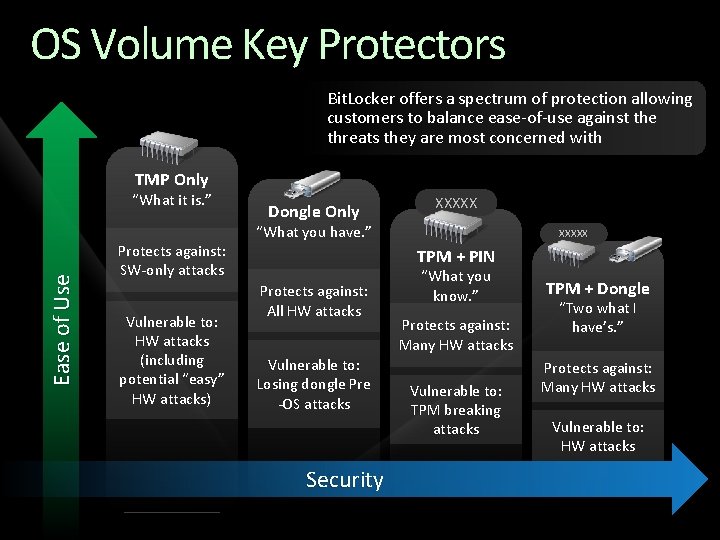
OS Volume Key Protectors Bit. Locker offers a spectrum of protection allowing customers to balance ease-of-use against the threats they are most concerned with TMP Only Ease of Use “What it is. ” Protects against: SW-only attacks Vulnerable to: HW attacks (including potential “easy” HW attacks) Dongle Only XXXXX “What you have. ” XXXXX TPM + PIN Protects against: All HW attacks Vulnerable to: Losing dongle Pre -OS attacks Security “What you know. ” Protects against: Many HW attacks Vulnerable to: TPM breaking attacks TPM + Dongle “Two what I have’s. ” Protects against: Many HW attacks Vulnerable to: HW attacks
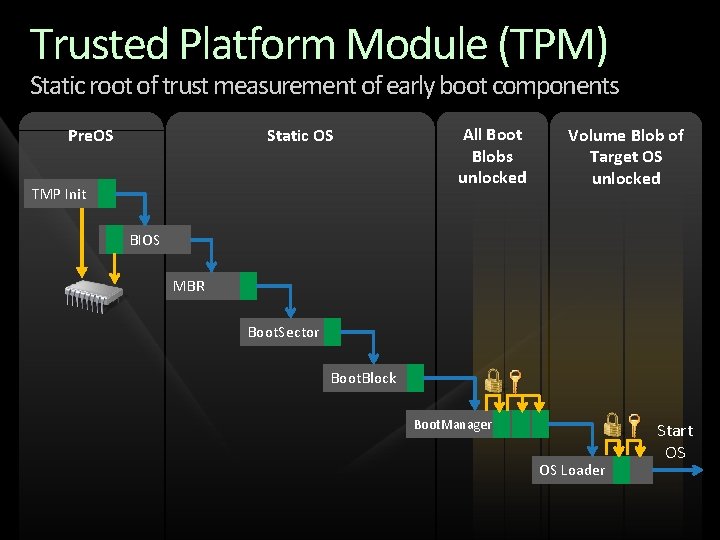
Trusted Platform Module (TPM) Static root of trust measurement of early boot components Pre. OS Static OS TMP Init All Boot Blobs unlocked Volume Blob of Target OS unlocked BIOS MBR Boot. Sector Boot. Block Boot. Manager OS Loader Start OS
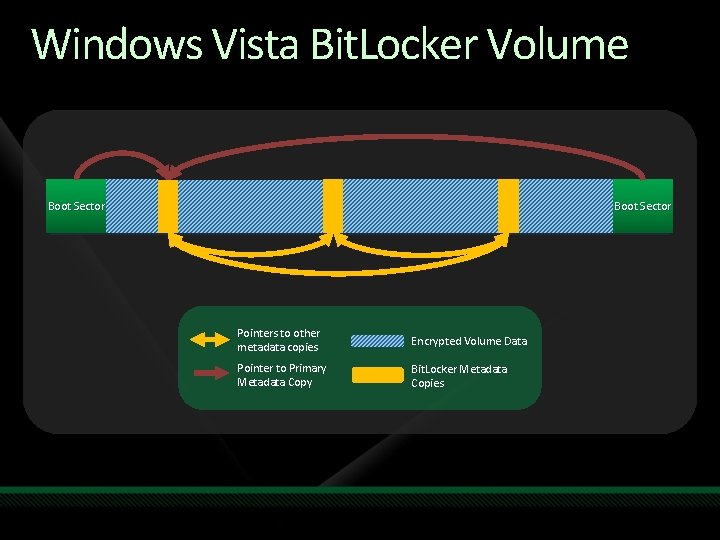
Windows Vista Bit. Locker Volume Boot Sector Pointers to other metadata copies Encrypted Volume Data Pointer to Primary Metadata Copy Bit. Locker Metadata Copies
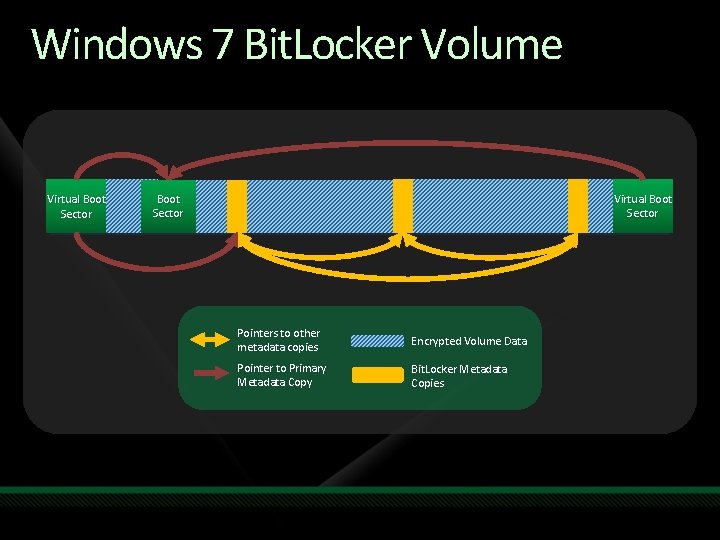
Windows 7 Bit. Locker Volume Virtual Boot Sector Pointers to other metadata copies Encrypted Volume Data Pointer to Primary Metadata Copy Bit. Locker Metadata Copies

Infrastructure Preparation Operating system partition
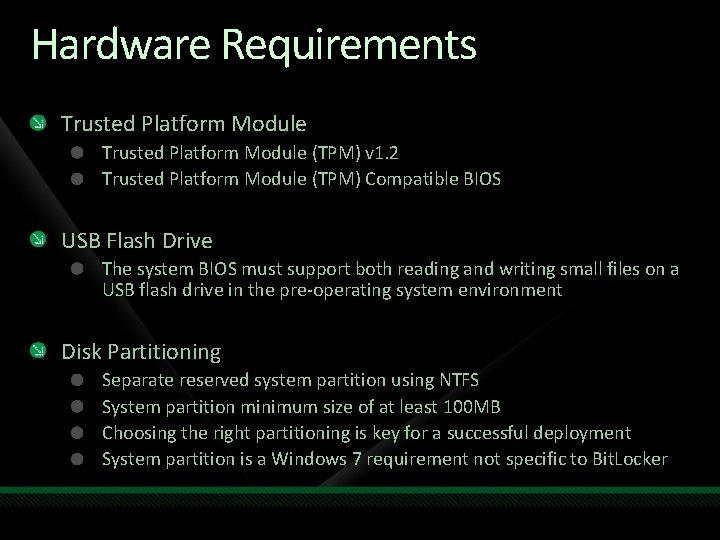
Hardware Requirements Trusted Platform Module (TPM) v 1. 2 Trusted Platform Module (TPM) Compatible BIOS USB Flash Drive The system BIOS must support both reading and writing small files on a USB flash drive in the pre-operating system environment Disk Partitioning Separate reserved system partition using NTFS System partition minimum size of at least 100 MB Choosing the right partitioning is key for a successful deployment System partition is a Windows 7 requirement not specific to Bit. Locker
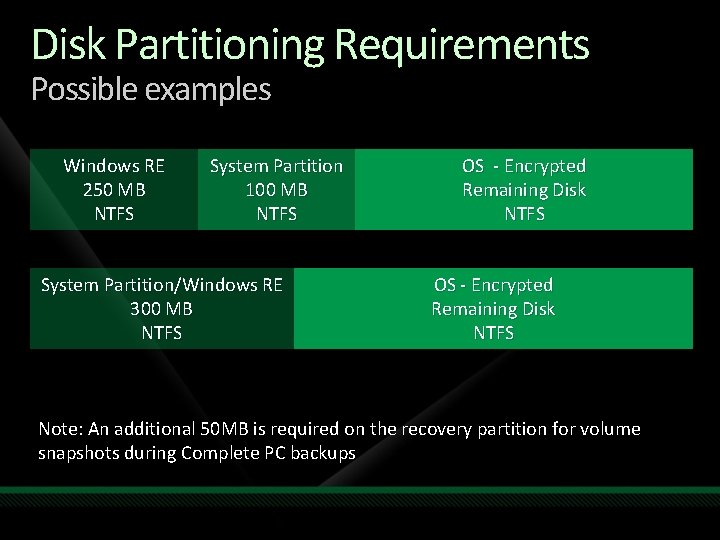
Disk Partitioning Requirements Possible examples Windows RE 250 MB NTFS System Partition 100 MB NTFS System Partition/Windows RE 300 MB NTFS OS - Encrypted Remaining Disk NTFS Note: An additional 50 MB is required on the recovery partition for volume snapshots during Complete PC backups
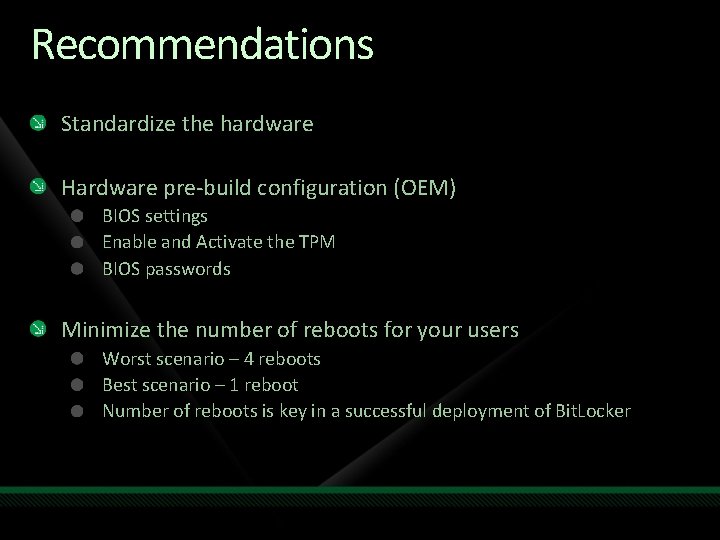
Recommendations Standardize the hardware Hardware pre-build configuration (OEM) BIOS settings Enable and Activate the TPM BIOS passwords Minimize the number of reboots for your users Worst scenario – 4 reboots Best scenario – 1 reboot Number of reboots is key in a successful deployment of Bit. Locker
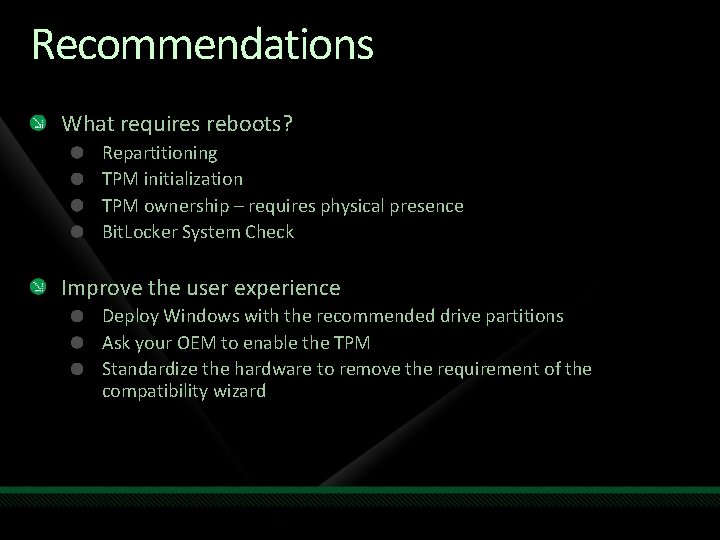
Recommendations What requires reboots? Repartitioning TPM initialization TPM ownership – requires physical presence Bit. Locker System Check Improve the user experience Deploy Windows with the recommended drive partitions Ask your OEM to enable the TPM Standardize the hardware to remove the requirement of the compatibility wizard

Management and Recovery Preparations
Group Policy Preparation Bit. Locker Group Policy settings can Turn on Bit. Locker backup to Active Directory Enable advanced startup options, recovery options, etc. Configure encryption method and strength Enable FIPS compliance - before setting up BDE keys! Enforce or disable specific protectors Enforce a minimum PIN length TPM Services Group Policy can Turn on TPM owner authorization backup to Active Directory Domain Services Configure the list of blocked TPM commands
Develop a Recovery Strategy Define the process end-users will follow when recovery of a Bit. Locker system is needed Anticipate the recovery scenarios How to handle lost or forgotten Key Protectors? Reset PIN, lost startup key How are disk drive failures recovered? How are TPM hardware failures treated? Recover from core files or pre-OS file (BIOS upgrade, etc…) updates which are not planned Recovering and diagnosing a deliberate attack
Active Directory Based Recovery By default, no recovery information is backed up to AD Administrators can configure GP to enable backup of Bit. Locker or TPM owner authorization recovery info Schema needs to be extended Windows Server 2008 and 2008 R 2 are “Bit. Locker Ready” All domain controllers in the domain must be at least Windows Server 2003 SP 1 Recovery data saved for each computer object Recovery passwords - a 48 -digit recovery password Key package data (optional) - helps recovery if the disk is severely damaged There is only one TPM owner password per computer There can be more than one recovery password per computer O/S Volume Data Volumes
Data Recovery Agent New Recovery Mechanism Certificate-based key protector A certificate containing a public key is distributed through Group Policy and is applied to any drive that mounts The corresponding private key is held by a data recovery agent in the IT department Allows IT department to have a way to unlock all protected drives in an enterprise Saves space in AD – same Key Protector on all drives
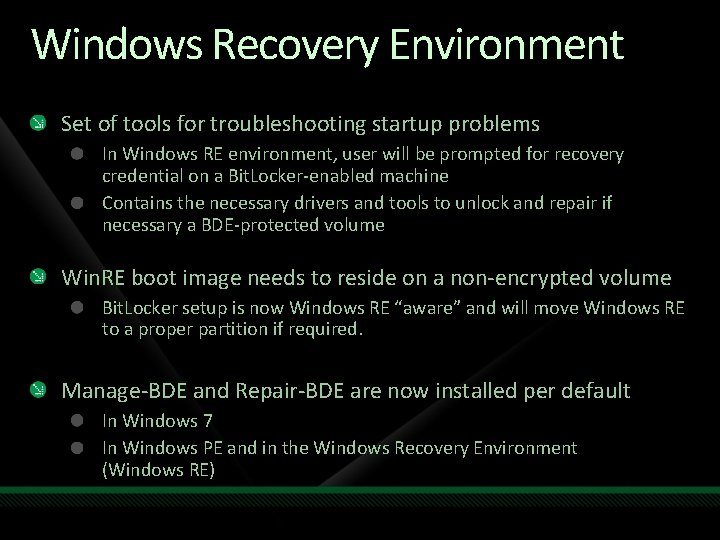
Windows Recovery Environment Set of tools for troubleshooting startup problems In Windows RE environment, user will be prompted for recovery credential on a Bit. Locker-enabled machine Contains the necessary drivers and tools to unlock and repair if necessary a BDE-protected volume Win. RE boot image needs to reside on a non-encrypted volume Bit. Locker setup is now Windows RE “aware” and will move Windows RE to a proper partition if required. Manage-BDE and Repair-BDE are now installed per default In Windows 7 In Windows PE and in the Windows Recovery Environment (Windows RE)
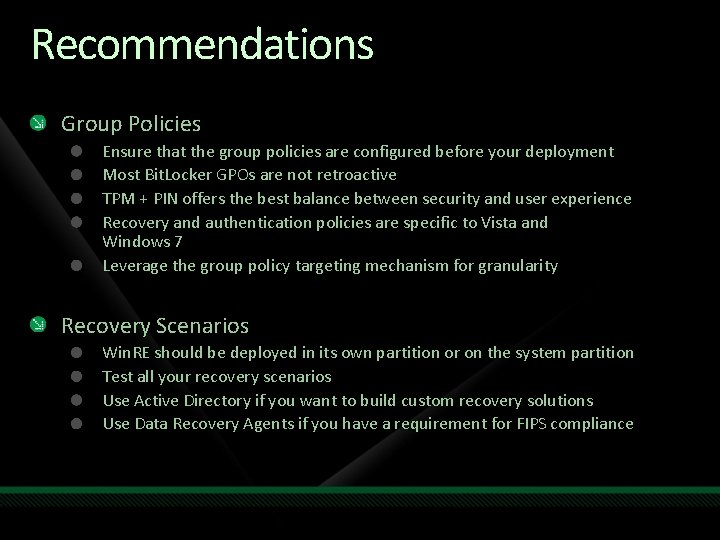
Recommendations Group Policies Ensure that the group policies are configured before your deployment Most Bit. Locker GPOs are not retroactive TPM + PIN offers the best balance between security and user experience Recovery and authentication policies are specific to Vista and Windows 7 Leverage the group policy targeting mechanism for granularity Recovery Scenarios Win. RE should be deployed in its own partition or on the system partition Test all your recovery scenarios Use Active Directory if you want to build custom recovery solutions Use Data Recovery Agents if you have a requirement for FIPS compliance

Bit. Locker Deployment Operating system partition
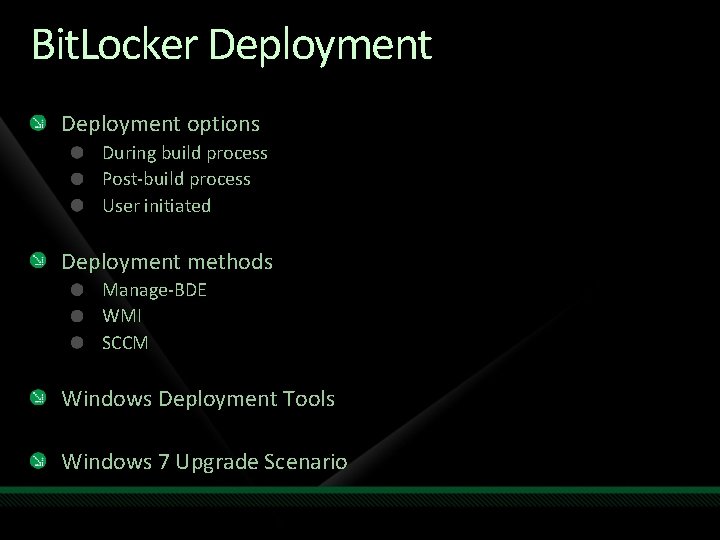
Bit. Locker Deployment options During build process Post-build process User initiated Deployment methods Manage-BDE WMI SCCM Windows Deployment Tools Windows 7 Upgrade Scenario
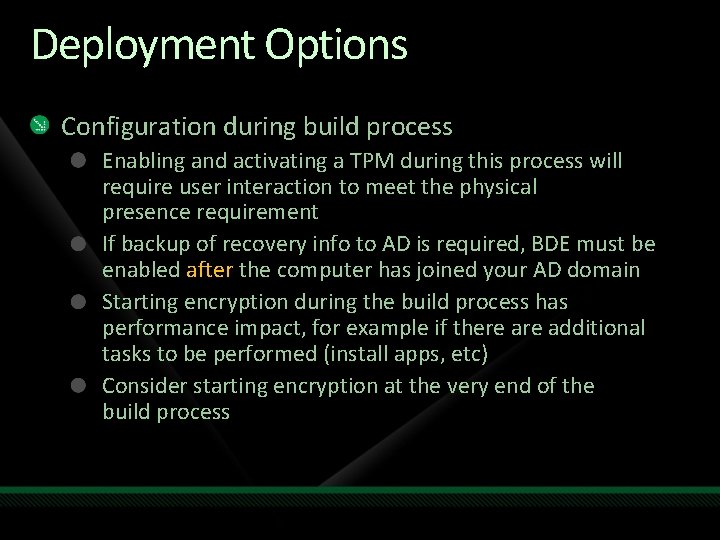
Deployment Options Configuration during build process Enabling and activating a TPM during this process will require user interaction to meet the physical presence requirement If backup of recovery info to AD is required, BDE must be enabled after the computer has joined your AD domain Starting encryption during the build process has performance impact, for example if there additional tasks to be performed (install apps, etc) Consider starting encryption at the very end of the build process
Deployment Options Post-build configuration Triggered immediately after the system build process completes Or triggered at a later time after the computer is delivered to the end user Software distribution tool (SCCM) GP scripting Logon scripts Very flexible and can be accomplished using numerous methods User initiated configuration Allow users to selectively enroll and configure their machines for BDE Not recommended if Bit. Locker is mandatory
Deployment Methods Manage-BDE. exe command-line tool Provides configuration / administration on individual and remote machines Location: %systemdrive%Windowssystem 32 Leverages the Bit. Locker and TPM WMI providers Create scripts with Bit. Locker and TPM WMI providers Useful when integrating support of Bit. Locker machines into your help desk environment, or user initiated configuration type of deployment Sample script (Enable. Bit. Locker. vbs) available Recommendation: Use for large enterprise deployments
Deployment Methods Bit. Locker WMI Methods allows to Enable/activate TPM, take ownership and generate random owner pass Enable Bit. Locker protection using supported authentication methods Create additional recovery key and recovery password Reset TPM owner information Use and modify existing sample script Manage-BDE. wsf Location: %systemdrive%Windowssystem 32 Only provided as an example Scripts can generate a rich log file, WMI exit codes are logged Microsoft recommends Using Bit. Locker and TPM WMI providers for enterprise deployment Using manage-bde for administration of Bit. Locker enabled machines
Deployment Methods Systems Center Configuration Manager 2007 Unify the deployment toolsets for both client and server Deliver an end-to-end process for deployment Provide high degrees of flexibility to accommodate complex enterprise requirements Use native toolsets found in Windows Supports Bit. Locker natively

Windows Deployment Tools Systems Center Configuration Manager 2007 http: //www. microsoft. com/systemcenter/ Microsoft Deployment Toolkit 2008 http: //technet. microsoft. com/en-us/solutionaccelerators/dd 407791. aspx Windows Deployment Services Unattended Installation Imaging with Image. X
Windows 7 Upgrade Scenario Upgrade from a Bit. Locker machine No decryption required but you need to suspend Bit. Locker Current partitioning will be preserved System partition will be 1. 5 GB Drive letter will not be removed Upgrade from a non-Bit. Locker machine Current partitioning will be preserved (single partition) Bit. Locker will automatically create a system partition System partition will be 300 MB with no drive letter
Bit. Locker Server Scenarios Bit. Locker is a feature on Windows Server (optional component) The feature needs to be installed through Server Manager All the recommendations made in this presentation apply to the server scenario Bit. Locker provides great value in branch office scenarios Branch Office Tech. Center http: //technet. microsoft. com/en-us/branchoffice/default. aspx
Recommendations Bare Metal install ≠ Clean install Make sure to partition the disk File base imaging does not partition the disk per default Turn on Bit. Locker in the post build process Provides the most flexibility Do not partition the disk post installation Deploy Windows 7 using the right partitions Only Shrink the O/S volume when no other options are available If you need to shrink the disk use bdehdcfg. exe post installation or the Bit. Locker Setup Wizard Do not shrink from Vista for large deployments

Bit. Locker Deployment Data Drive
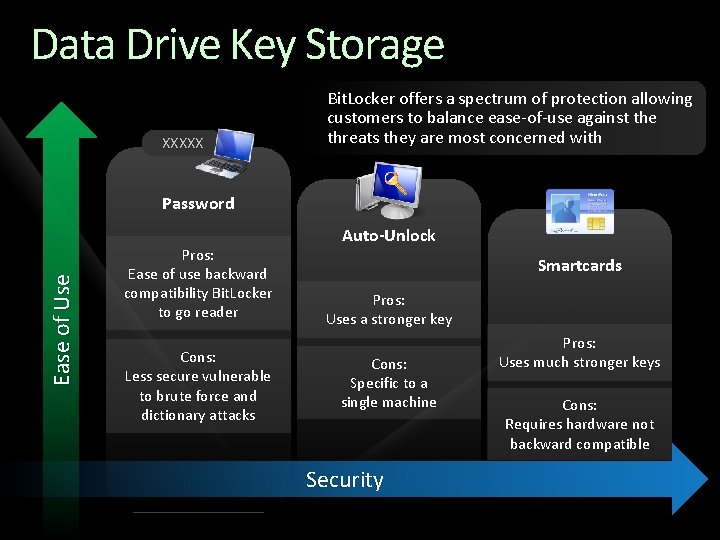
Data Drive Key Storage XXXXX Bit. Locker offers a spectrum of protection allowing customers to balance ease-of-use against the threats they are most concerned with Ease of Use Password Pros: Ease of use backward compatibility Bit. Locker to go reader Cons: Less secure vulnerable to brute force and dictionary attacks Auto-Unlock Smartcards Pros: Uses a stronger key Cons: Specific to a single machine Security Pros: Uses much stronger keys Cons: Requires hardware not backward compatible
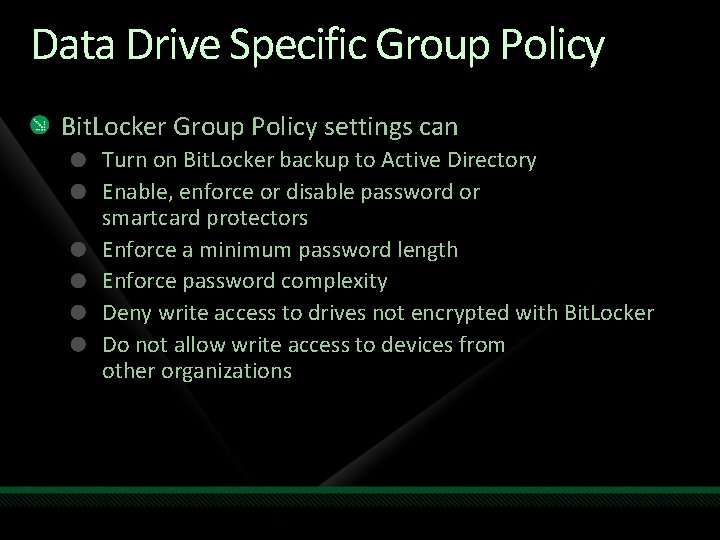
Data Drive Specific Group Policy Bit. Locker Group Policy settings can Turn on Bit. Locker backup to Active Directory Enable, enforce or disable password or smartcard protectors Enforce a minimum password length Enforce password complexity Deny write access to drives not encrypted with Bit. Locker Do not allow write access to devices from other organizations
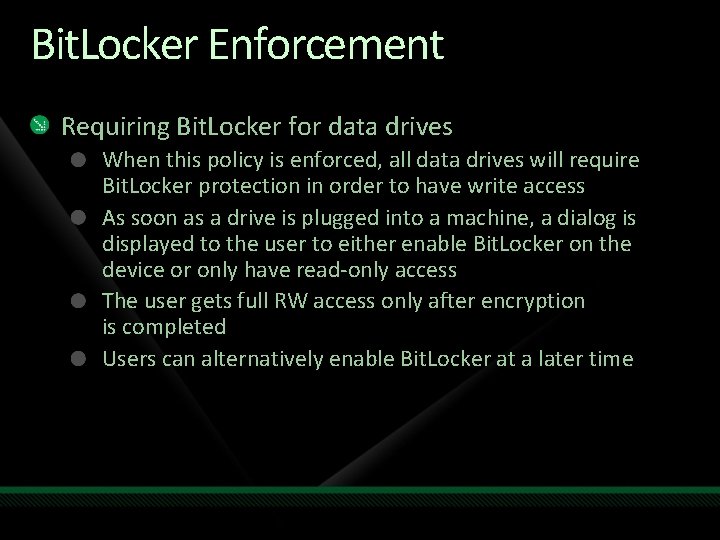
Bit. Locker Enforcement Requiring Bit. Locker for data drives When this policy is enforced, all data drives will require Bit. Locker protection in order to have write access As soon as a drive is plugged into a machine, a dialog is displayed to the user to either enable Bit. Locker on the device or only have read-only access The user gets full RW access only after encryption is completed Users can alternatively enable Bit. Locker at a later time
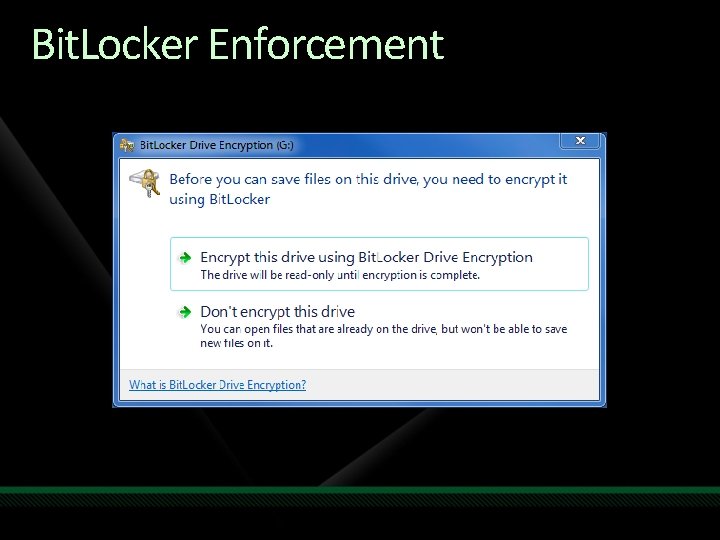
Bit. Locker Enforcement
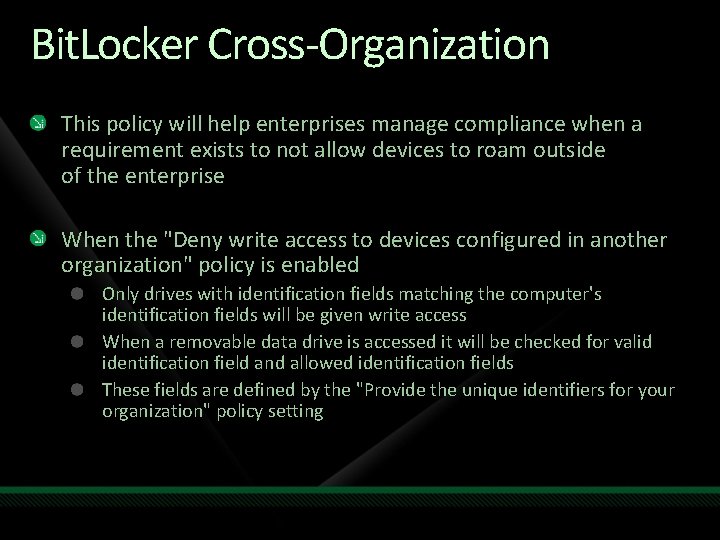
Bit. Locker Cross-Organization This policy will help enterprises manage compliance when a requirement exists to not allow devices to roam outside of the enterprise When the "Deny write access to devices configured in another organization" policy is enabled Only drives with identification fields matching the computer's identification fields will be given write access When a removable data drive is accessed it will be checked for valid identification field and allowed identification fields These fields are defined by the "Provide the unique identifiers for your organization" policy setting



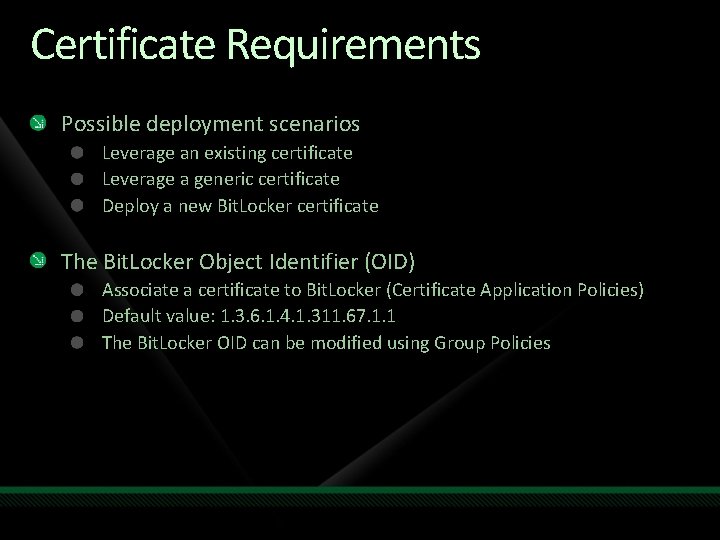
Certificate Requirements Possible deployment scenarios Leverage an existing certificate Leverage a generic certificate Deploy a new Bit. Locker certificate The Bit. Locker Object Identifier (OID) Associate a certificate to Bit. Locker (Certificate Application Policies) Default value: 1. 3. 6. 1. 4. 1. 311. 67. 1. 1 The Bit. Locker OID can be modified using Group Policies
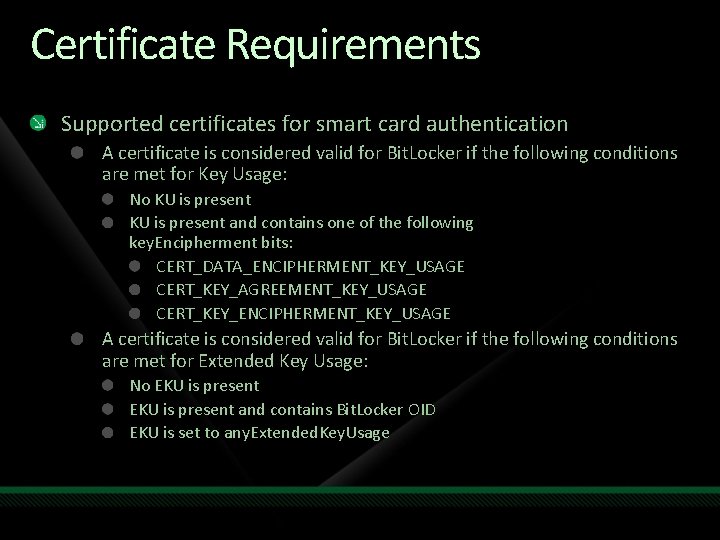
Certificate Requirements Supported certificates for smart card authentication A certificate is considered valid for Bit. Locker if the following conditions are met for Key Usage: No KU is present and contains one of the following key. Encipherment bits: CERT_DATA_ENCIPHERMENT_KEY_USAGE CERT_KEY_AGREEMENT_KEY_USAGE CERT_KEY_ENCIPHERMENT_KEY_USAGE A certificate is considered valid for Bit. Locker if the following conditions are met for Extended Key Usage: No EKU is present and contains Bit. Locker OID EKU is set to any. Extended. Key. Usage
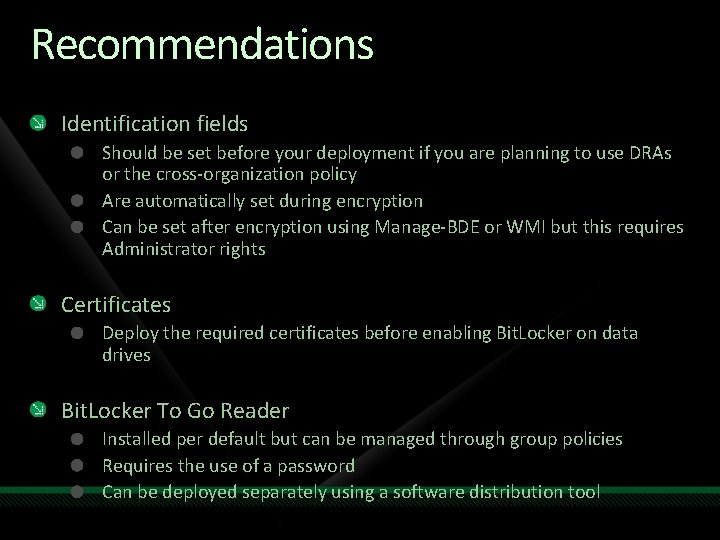
Recommendations Identification fields Should be set before your deployment if you are planning to use DRAs or the cross-organization policy Are automatically set during encryption Can be set after encryption using Manage-BDE or WMI but this requires Administrator rights Certificates Deploy the required certificates before enabling Bit. Locker on data drives Bit. Locker To Go Reader Installed per default but can be managed through group policies Requires the use of a password Can be deployed separately using a software distribution tool

demo Bit. Locker & Bit. Locker To Go

question & answer

Resources www. microsoft. com/teched www. microsoft. com/learning Sessions On-Demand & Community Microsoft Certification & Training Resources http: //microsoft. com/technet http: //microsoft. com/msdn Resources for IT Professionals Resources for Developers
Complete an evaluation on Comm. Net and enter to win an Xbox 360 Elite!

© 2009 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.
- Slides: 53