Why Invest in Qo S Internet FTP Server

![Custom Queuing Commands • queue-list queue byte-count – Designate byte-count allowed per queue [no] Custom Queuing Commands • queue-list queue byte-count – Designate byte-count allowed per queue [no]](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-37.jpg)
![Configuration fair-queue [congestive discard threshold] [#hashed_queues] [reserved_queues] Qcongestive discard policy hits conversations with more Configuration fair-queue [congestive discard threshold] [#hashed_queues] [reserved_queues] Qcongestive discard policy hits conversations with more](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-48.jpg)
![Diagnostics/Troubleshooting show interface [interface name] show queue interface name show queueing [fair | custom Diagnostics/Troubleshooting show interface [interface name] show queue interface name show queueing [fair | custom](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-50.jpg)
![Marking at the Edge: IP Precedence • CAR access-list – [no] access-list rate-limit <1– Marking at the Edge: IP Precedence • CAR access-list – [no] access-list rate-limit <1–](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-77.jpg)
![Generic Traffic Shaping Commands • Traffic-shape rate bit-rate [burst-size [excess-burst-size]] • Traffic-shape group access-list Generic Traffic Shaping Commands • Traffic-shape rate bit-rate [burst-size [excess-burst-size]] • Traffic-shape group access-list](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-85.jpg)
![Configuring RSVP ip rsvp bandwidth [interface-kbps] [single-flow-kbps] ! interface Serial 0/0 ip address 10. Configuring RSVP ip rsvp bandwidth [interface-kbps] [single-flow-kbps] ! interface Serial 0/0 ip address 10.](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-92.jpg)
- Slides: 120
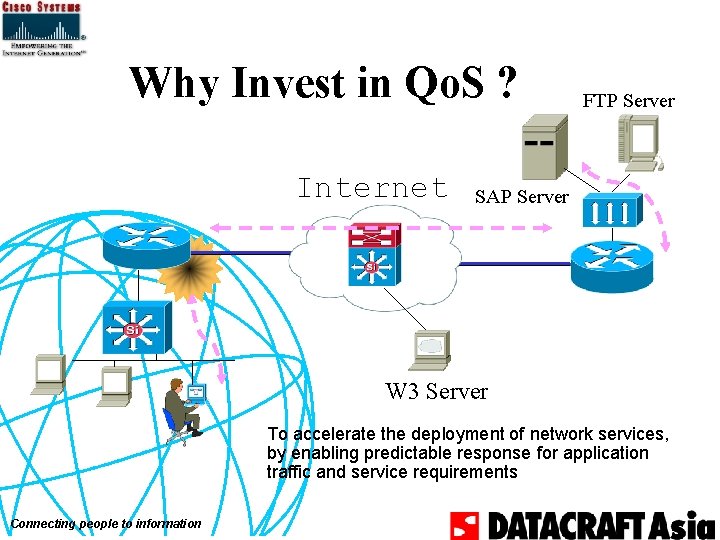
Why Invest in Qo. S ? Internet FTP Server SAP Server W 3 Server To accelerate the deployment of network services, by enabling predictable response for application traffic and service requirements Connecting people to information
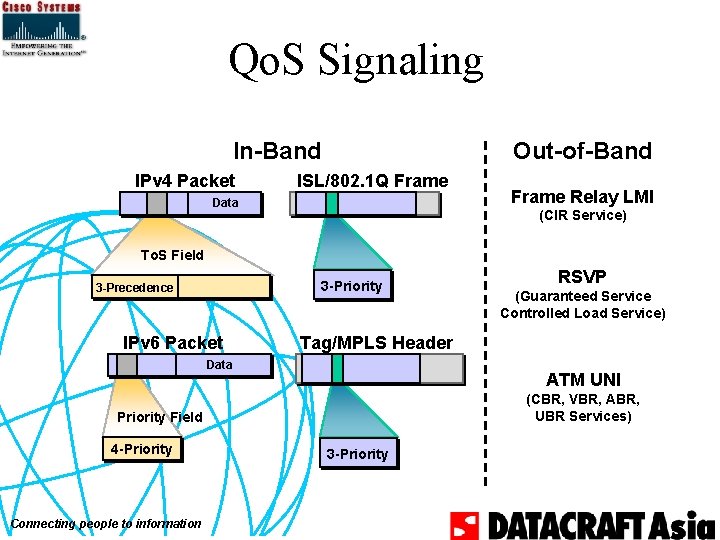
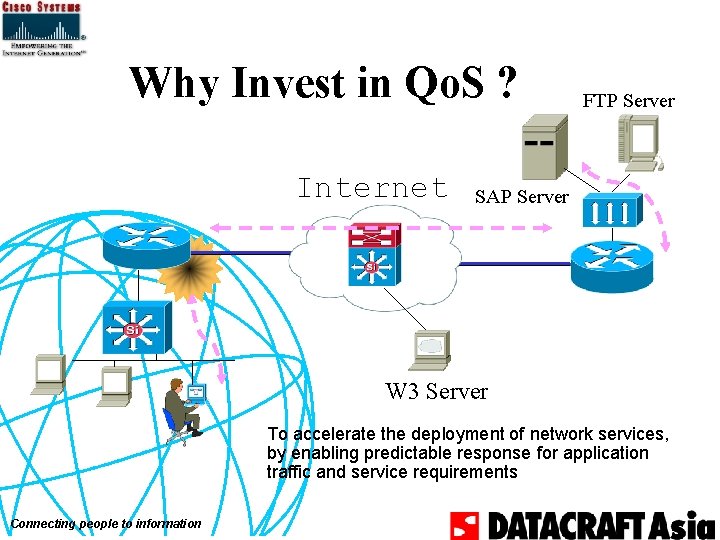
Qo. S Signaling In-Band IPv 4 Packet Out-of-Band ISL/802. 1 Q Frame Data Frame Relay LMI (CIR Service) To. S Field 3 -Priority 3 -Precedence IPv 6 Packet ATM UNI (CBR, VBR, ABR, UBR Services) Priority Field Connecting people to information (Guaranteed Service Controlled Load Service) Tag/MPLS Header Data 4 -Priority RSVP 3 -Priority
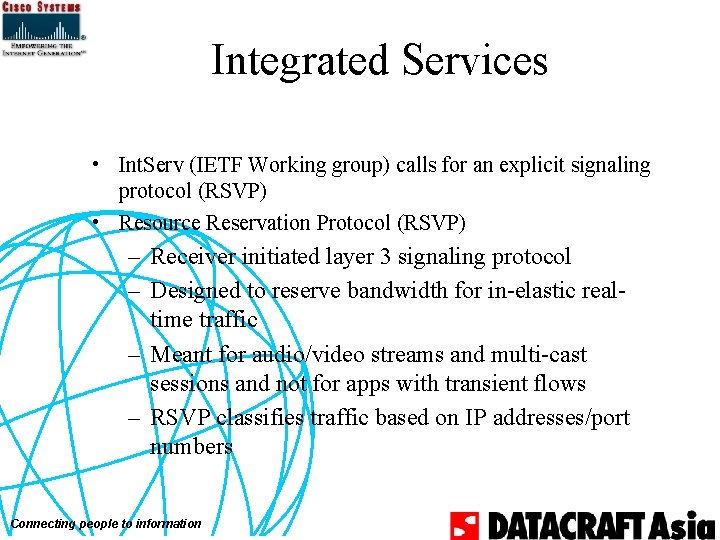
Integrated Services • Int. Serv (IETF Working group) calls for an explicit signaling protocol (RSVP) • Resource Reservation Protocol (RSVP) – Receiver initiated layer 3 signaling protocol – Designed to reserve bandwidth for in-elastic realtime traffic – Meant for audio/video streams and multi-cast sessions and not for apps with transient flows – RSVP classifies traffic based on IP addresses/port numbers Connecting people to information
Integrated Services - Int. Serv • An application explicitly signals its Qo. S requirements to the network • Network uses admission and policy control to decide if it can meet the application’s requirements. • Signaling is done using RSVP and flows from receiver to sender (RESV message) • At each hop, the network device enforces the contract via policing and prioritizes forwarding via multiple transmit queues Connecting people to information
Cisco Connecting people to information ® IOS Qo. S
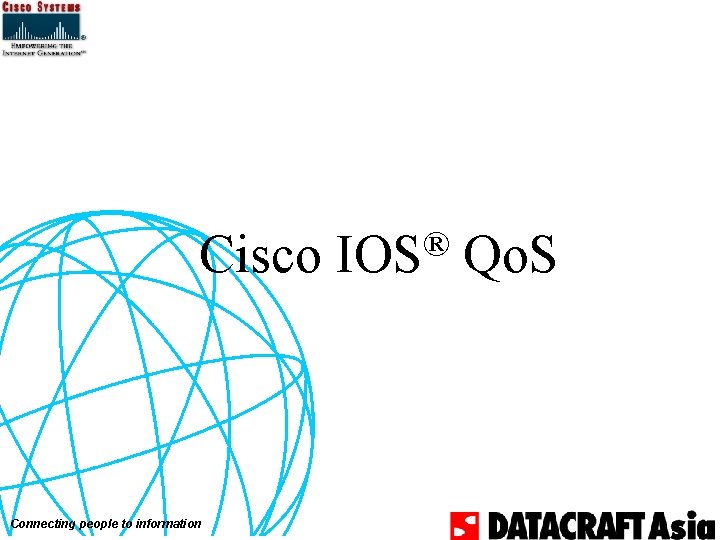
® IOS Cisco Qo. S Diff Serv Components Traffic Conditioner Mechanism Network Effect RED, WRED, Flow RED • Avoid Congestion by Notifying Source • Prioritize which Traffic Is Told to Reduce PQ, CQ, WFQ, CB WFQ, WRR, MDRR CAR, Policy Routing, DSCP, NFCII • Bandwidth Management: Traffic Priority • Set Servicing Sequence • Sets IP Precedence/DSCP • By Application, Protocol, Address, etc Metering (Policing) CAR • Enforce a Maximum Transmission Rate • Conform or Exceed Thresholds Shaping GTS, FRTS Drop Scheduling Marking Compress CRTP Fragment LFI, FRF. 12 Connecting people to information • Conforms Traffic to Committed Bandwidth • Interwork with Layer 2 Notification e. g. , BECN • Reduce the Volume of Traffic Sent • Reduce Delay on Slower Speed Links • Split, Recombine Larger Frames
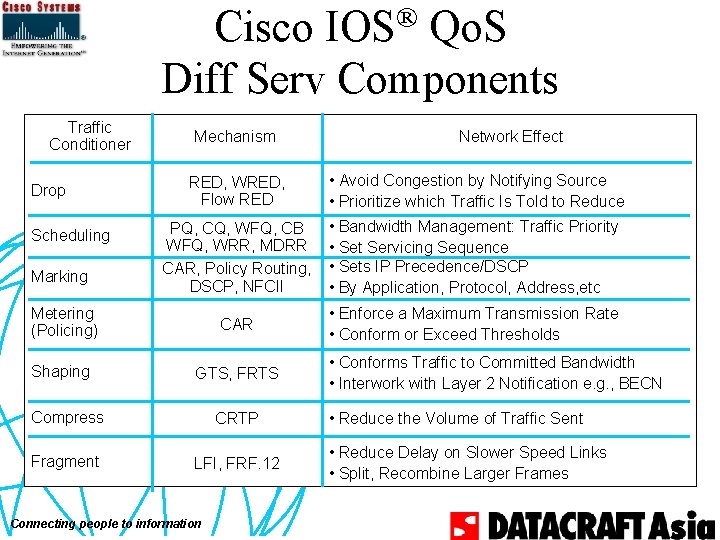
IP Qo. S 11. 1 11. 2 • WFQ • RED • WRED • RSVP • Net. Flow Switching 11. 1 CA 11. 1 CB (ISP 8) 11. 1 CC (FIB) 11. 1 CD (ISP 8+L 3) 11. 1 CE (FIB+L 3) Connecting people to information 11. 3 12. 0 CYH 2 ? 8 11. 1 CC • IP ATM Co. S (Ph I) • CEF • CAR/DCAR • DWFQ • DWRED • Qo. S Policy Propagation via BGP • Net. Flow Services 12. 0 T • IP ATM Co. S (Ph II)

One Common Policy Required: Treat Gold traffic with the highest service level over Silver and Bronze traffic Connecting people to information
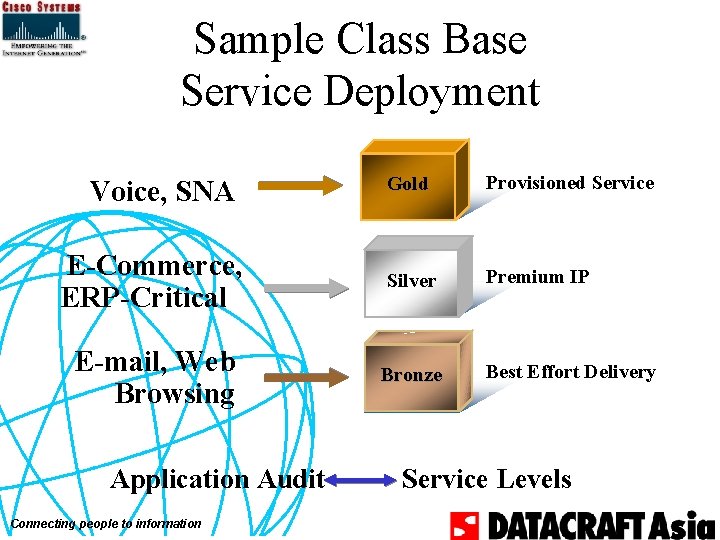
Sample Class Base Service Deployment Gold Provisioned Service E-Commerce, ERP-Critical Silver Premium IP E-mail, Web Browsing Bronze Best Effort Delivery Voice, SNA Application Audit Connecting people to information Service Levels
Queuing’s Premise • Getting better service is a matter of managing congested queues • Over-all latency and bandwidth are constant – Make some traffic absorb latency, and therefore give up bandwidth – Shield other traffic from latency, and therefore gain bandwidth Connecting people to information
Queuing Algorithms • Congestion management algorithms – First In First Out – Priority Queuing – Custom Queuing – Weighted Fair Queuing (WFQ) Connecting people to information
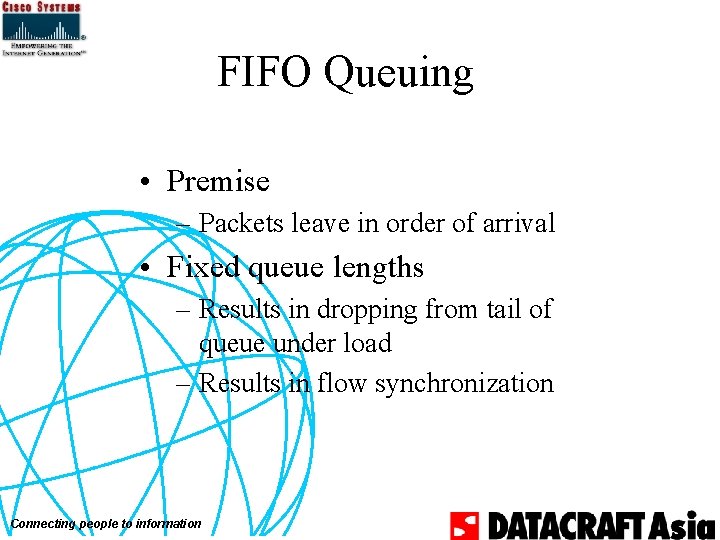
FIFO Queuing • Premise – Packets leave in order of arrival • Fixed queue lengths – Results in dropping from tail of queue under load – Results in flow synchronization Connecting people to information
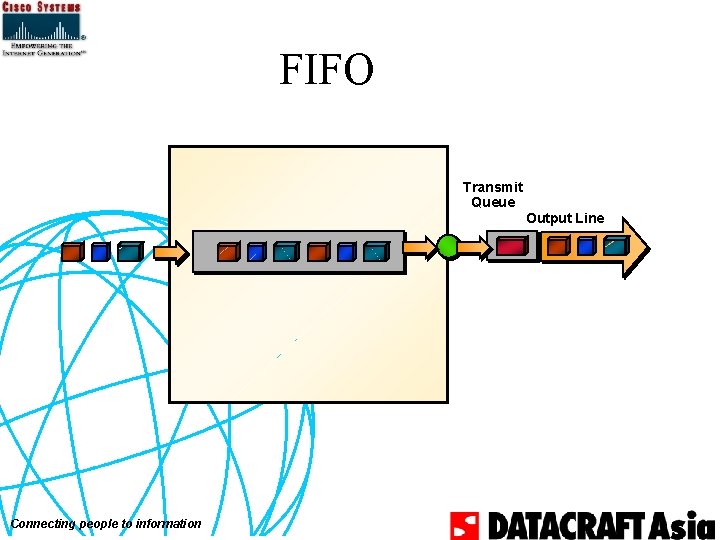
FIFO Transmit Queue Output Line Connecting people to information
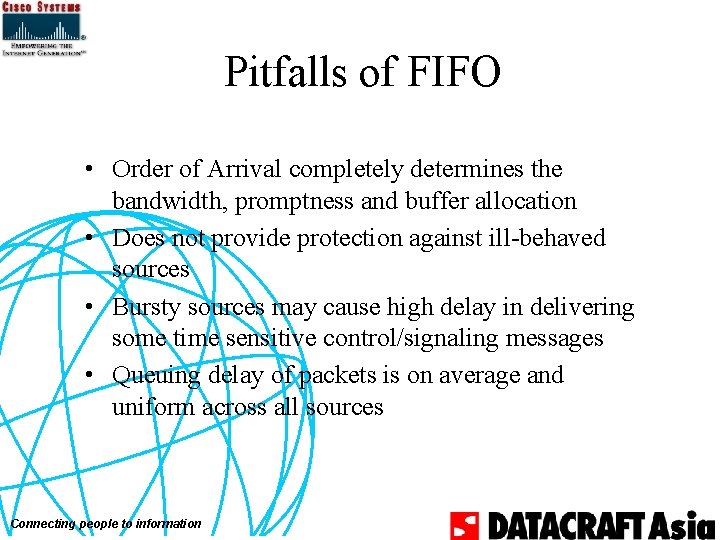
Pitfalls of FIFO • Order of Arrival completely determines the bandwidth, promptness and buffer allocation • Does not provide protection against ill-behaved sources • Bursty sources may cause high delay in delivering some time sensitive control/signaling messages • Queuing delay of packets is on average and uniform across all sources Connecting people to information
FIFO Default and Config • FIFO is a default queuing algorithm on interfaces that don’t support fancy queuing – i. e. X. 25, tunnel • FIFO can be explicitly configured by turning off WFQ on interface: no fair-queue Connecting people to information
FIFO Example caymans#sh int e 0 Ethernet 0 is up, line protocol is up Hardware is Lance, address is 0000. 0 c 14. 5 a 18 ( bia 0000. 0 c 14. 5 a 18) Internet address is 171. 69. 232. 116/28 MTU 1500 bytes, BW 10000 Kbit, DLY 1000 usec, rely 255/255, load 1/255 Encapsulation ARPA, loopback not set, keepalive set (10 sec) ARP type: ARPA, ARP Timeout 04: 00 Last input 00: 00, output 00: 02, output hang never Last clearing of "show interface" counters never Queueing strategy: fifo Output queue 0/40, 0 drops; input queue 0/75, 0 drops 5 minute input rate 0 bits/sec, 0 packets/sec 5 minute output rate 0 bits/sec, 0 packets/sec 78716 packets input, 25213248 bytes, 0 no buffer Received 78582 broadcasts, 0 runts, 0 giants, 0 throttles 3 input errors, 3 CRC, 3 frame, 0 overrun, 0 ignored, 0 abort 0 input packets with dribble condition detected 71241 packets output, 6905654 bytes, 0 underruns 0 output errors, 1 collisions, 3 interface resets 0 babbles, 0 late collision, 39 deferred 0 lost carrier, 0 no carrier 0 output buffer failures, 0 output buffers swapped out Connecting people to information
Simplest Qo. S Algorithm: Priority Queuing • Stated requirement: – If <application> has traffic waiting, send it next • Commonly implemented – Defined behavior of IP precedence Connecting people to information
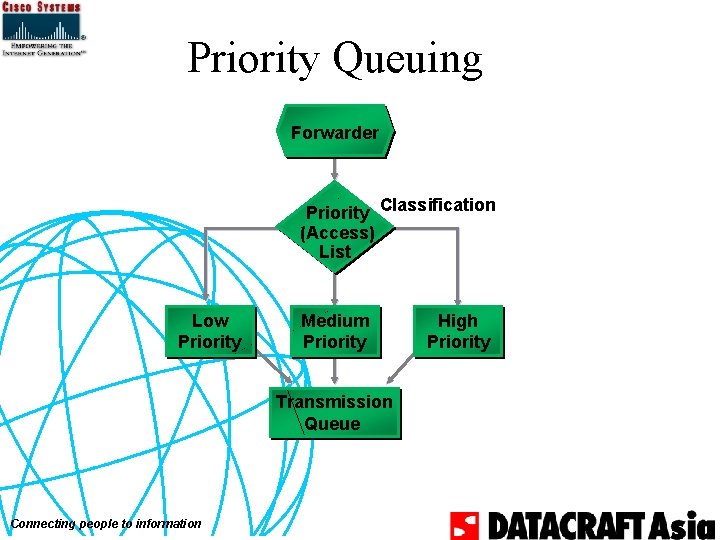
Priority Queuing Forwarder Priority Classification (Access) List Low Priority Medium Priority Transmission Queue Connecting people to information High Priority
Priority Queuing Implementation Approach • Identify interesting traffic – Priority-list by protocol – Priority-list by incoming interface • Place traffic in various queues • Dequeue in order of queue precedence Connecting people to information
Priority Queuing cont. • Four priority queues – High, Medium, Normal, Low • Packets not classified by priority-list mechanism fall into normal queue • Priority queuing not supported over X. 25 and Tunnel interfaces Connecting people to information
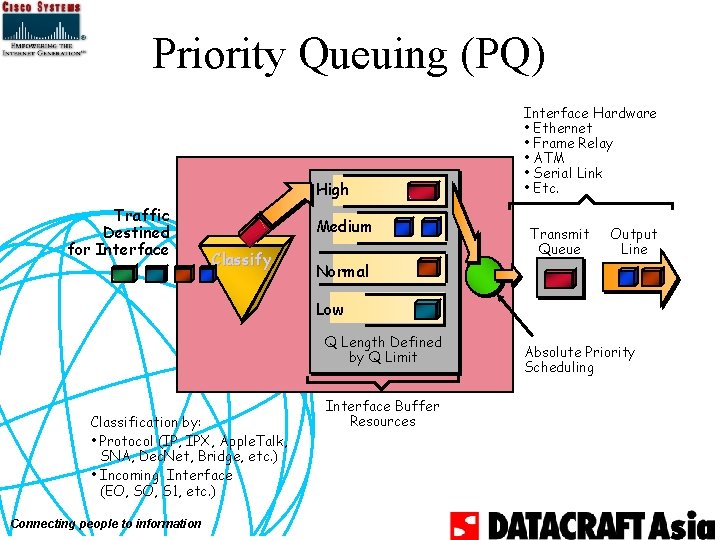
Priority Queuing (PQ) High Traffic Destined for Interface Medium Classify Interface Hardware • Ethernet • Frame Relay • ATM • Serial Link • Etc. Transmit Queue Output Line Normal Low Q Length Defined by Q Limit Classification by: • Protocol (IP, IPX, Apple. Talk, SNA, Dec. Net, Bridge, etc. ) • Incoming Interface (EO, S 1, etc. ) Connecting people to information Interface Buffer Resources Absolute Priority Scheduling
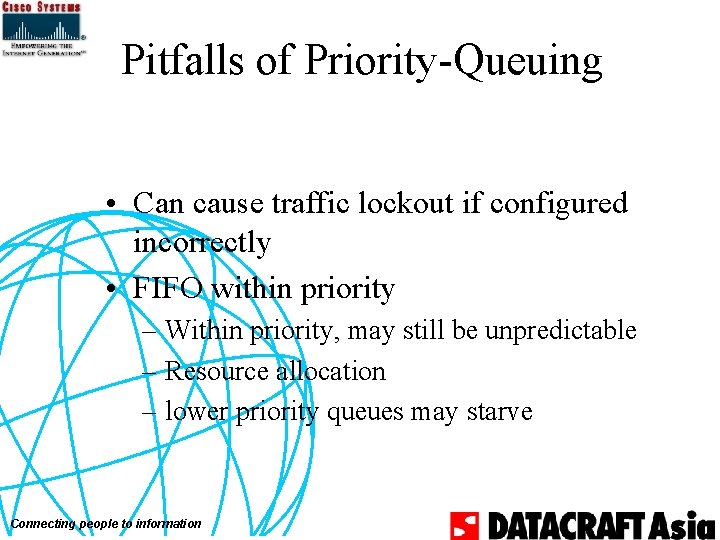
Pitfalls of Priority-Queuing • Can cause traffic lockout if configured incorrectly • FIFO within priority – Within priority, may still be unpredictable – Resource allocation – lower priority queues may starve Connecting people to information
Priority Queuing Commands • Priority-list protocol command – Establishes queuing priority based upon protocol type: [no] priority-list <list-number> protocol <protocol-name> {high | medium | normal | low} <queue-keyword> <keyword-value> • Priority-list interface command – Establishes queuing priority based on packets entering from interface: [no] priority-list <list-number> interface <interface-type> <interface-number> {high | medium | normal | low} Connecting people to information
Priority Queuing Commands • Priority-list default command – To assign priority-queue for those packets that do not match any rule in priority-list. If not specified, normal queue is default [no] priority-list <list> default <queuekeyword> • Priority-list queue-limit – Specify maximum number of packets that can be waiting in each priority queue [no] priority-list <list> queue-limit <high-lim> <medium-lim> <normal-lim> <low-lim> • Priority-group – Assigns a specified priority-list to an interface – [no] priority-group <1 -16> Connecting people to information
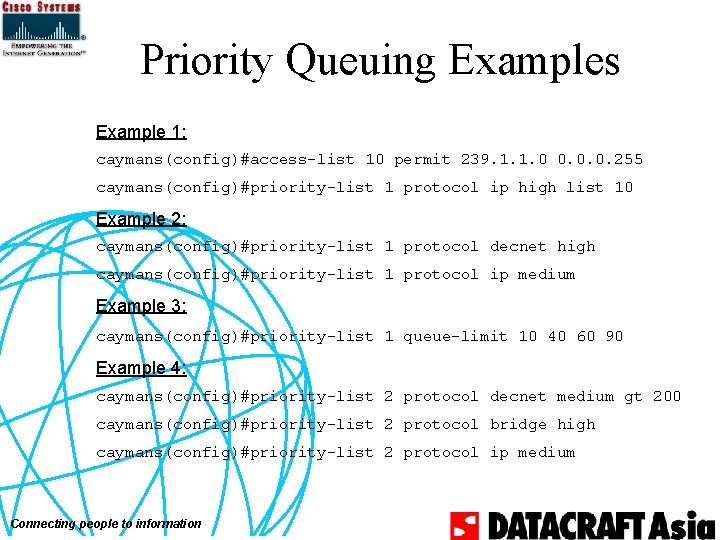
Priority Queuing Examples Example 1: caymans(config)#access-list 10 permit 239. 1. 1. 0 0. 0. 0. 255 caymans(config)#priority-list 1 protocol ip high list 10 Example 2: caymans(config)#priority-list 1 protocol decnet high caymans(config)#priority-list 1 protocol ip medium Example 3: caymans(config)#priority-list 1 queue-limit 10 40 60 90 Example 4: caymans(config)#priority-list 2 protocol decnet medium gt 200 caymans(config)#priority-list 2 protocol bridge high caymans(config)#priority-list 2 protocol ip medium Connecting people to information
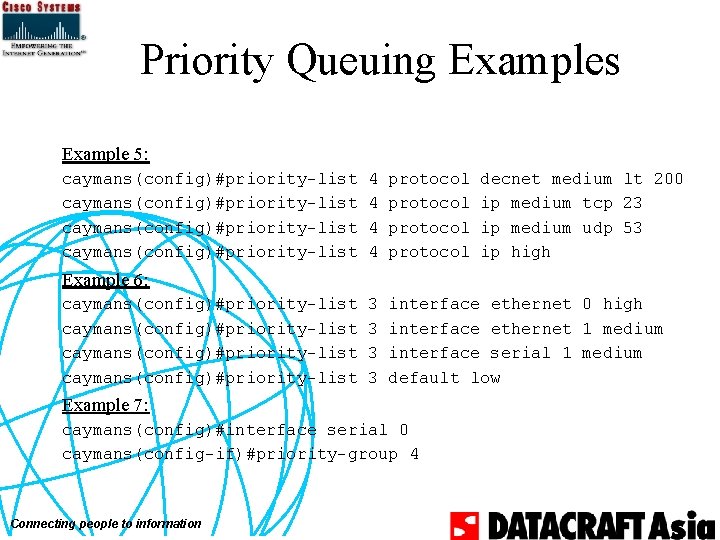
Priority Queuing Examples Example 5: caymans(config)#priority-list 4 4 protocol decnet medium lt 200 ip medium tcp 23 ip medium udp 53 ip high 3 3 interface ethernet 0 high interface ethernet 1 medium interface serial 1 medium default low Example 6: caymans(config)#priority-list Example 7: caymans(config)#interface serial 0 caymans(config-if)#priority-group 4 Connecting people to information
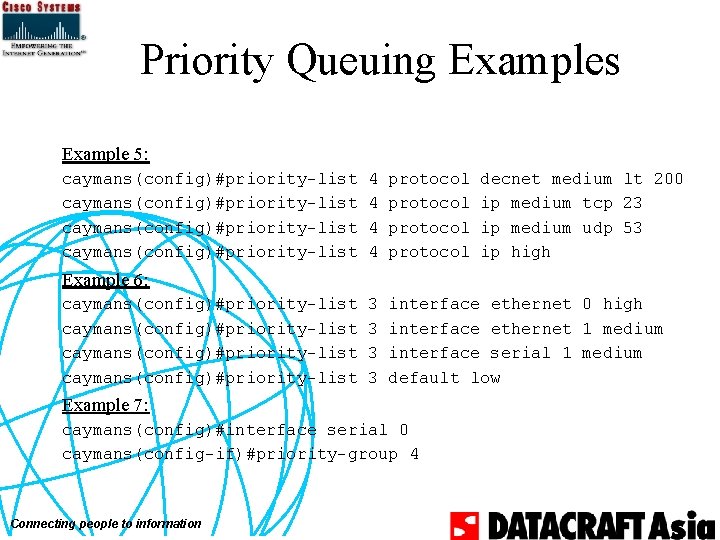
Priority Queuing Example caymans# sh queueing priority Current priority queue configuration: List 1 1 1 2 2 2 3 3 4 4 Connecting people to information Queue high medium high low medium high medium low high medium medium high Args protocol decnet protocol ip limit 10 limit 90 protocol decnet protocol bridge protocol ip default interface Ethernet 0 interface Ethernet 1 interface Serial 1 protocol decnet protocol ip list 10 gt 200 lt 200 tcp port telnet udp port domain
Priority Queuing Example caymans#sh int s 0 Serial 0 is down, line protocol is down Hardware is HD 64570 MTU 1500 bytes, BW 1544 Kbit, DLY 20000 usec, rely 255/255, load 1/255 Encapsulation HDLC, loopback not set, keepalive set (10 sec) Last input never, output hang never Last clearing of "show interface" counters never Input queue: 0/75/0 (size/max/drops); Total output drops: 0 Queueing strategy: priority-list 4 Output queue: high 0/20/0, medium 0/40/0, normal 0/60/0, low 0/80/0 5 minute input rate 0 bits/sec, 0 packets/sec 5 minute output rate 0 bits/sec, 0 packets/sec 0 packets input, 0 bytes, 0 no buffer Received 0 broadcasts, 0 runts, 0 giants, 0 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort 16 packets output, 2841 bytes, 0 underruns 0 output errors, 0 collisions, 22339 interface resets 0 output buffer failures, 0 output buffers swapped out 108 carrier transitions DCD=down DSR=down DTR=up RTS=up CTS=down Connecting people to information
Class-Based Queuing • Cisco feature: custom queuing • Stated requirement: – traffic with <characteristics> needs a guaranteed rate or latency • �Characteristics may be: – Application – Traffic source Connecting people to information
Custom Queuing Implementation Approach • Identify the traffic • Distribute into FIFO queue by class • Dequeue in some rotation – Remove some number of bytes at most – Move to next queue in round robin order Connecting people to information
Custom Queuing • Identify the traffic – queue-list by protocol – queue-list by incoming interface • Distribute into FIFO queue by class – Total 17 queues – Queue number 1 -16 is serviced sequentially – Queue number 0 is a system queue, ie. keepalives, therefore emptied first • Round Robin Dequeue – Configurable byte count to transmit before servicing – the next queue Connecting people to information
Custom Queuing Forwarder Control Traffic Priority (Access) List Queue #0 Queue #1 Queue #9 Queue #10 Queue #2 Queue #3 Queue #11 Queue #12 Queue #4 Queue #5 Queue #13 Queue #6 Queue #14 Queue #15 Queue #7 Queue #8 Queue #16 Transmission Queue Connecting people to information
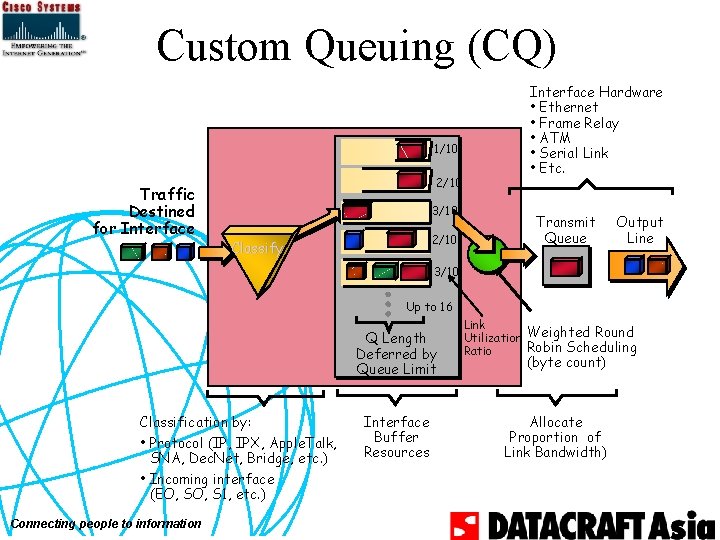
Custom Queuing (CQ) 1/10 Traffic Destined for Interface 2/10 3/10 2/10 Classify Interface Hardware • Ethernet • Frame Relay • ATM • Serial Link • Etc. Transmit Queue Output Line 3/10 Up to 16 Q Length Deferred by Queue Limit Classification by: • Protocol (IP, IPX, Apple. Talk, SNA, Dec. Net, Bridge, etc. ) • Incoming interface (EO, S 1, etc. ) Connecting people to information Interface Buffer Resources Link Utilization Weighted Round Robin Scheduling Ratio (byte count) Allocate Proportion of Link Bandwidth)
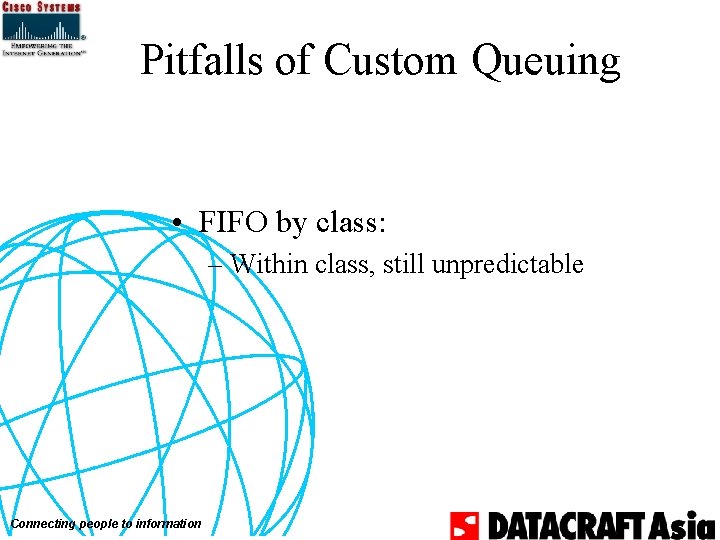
Pitfalls of Custom Queuing • FIFO by class: – Within class, still unpredictable Connecting people to information
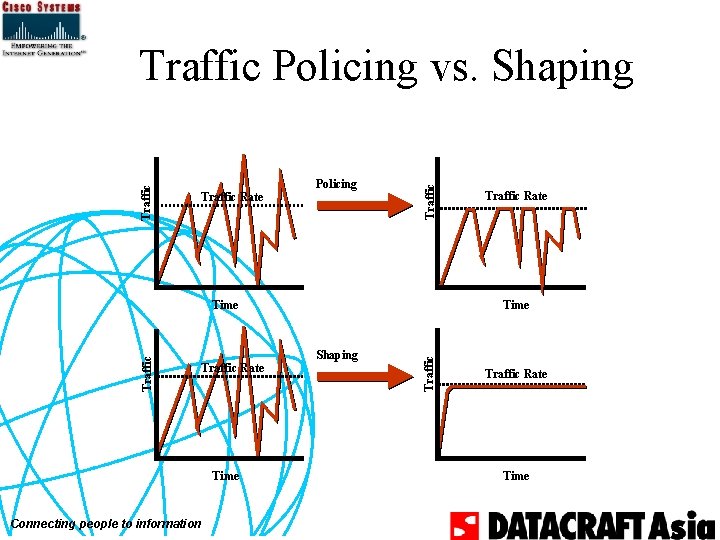
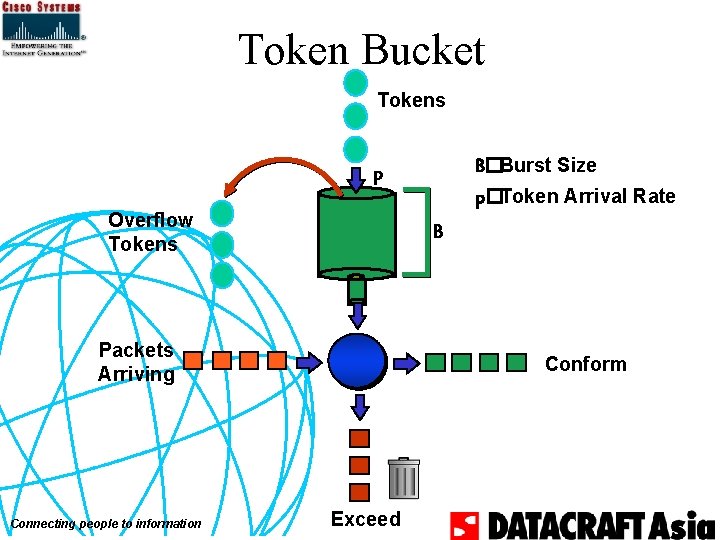
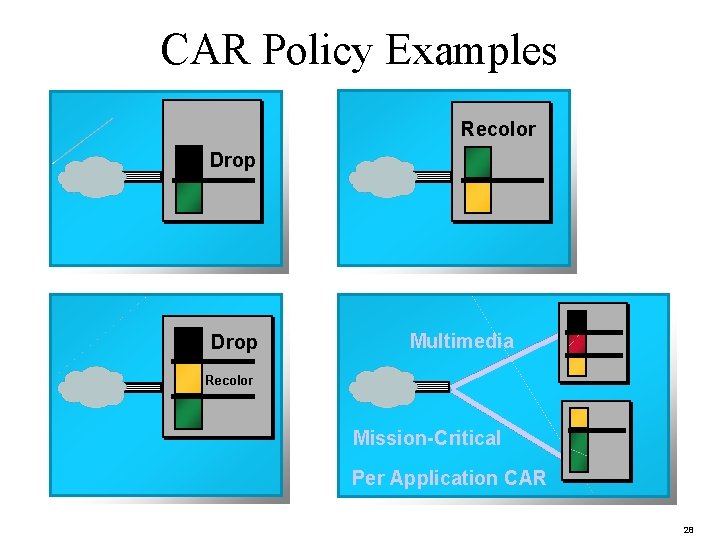
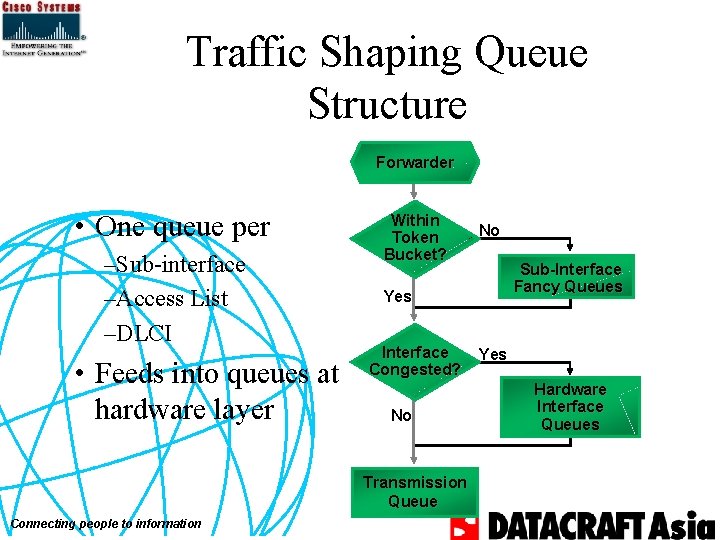
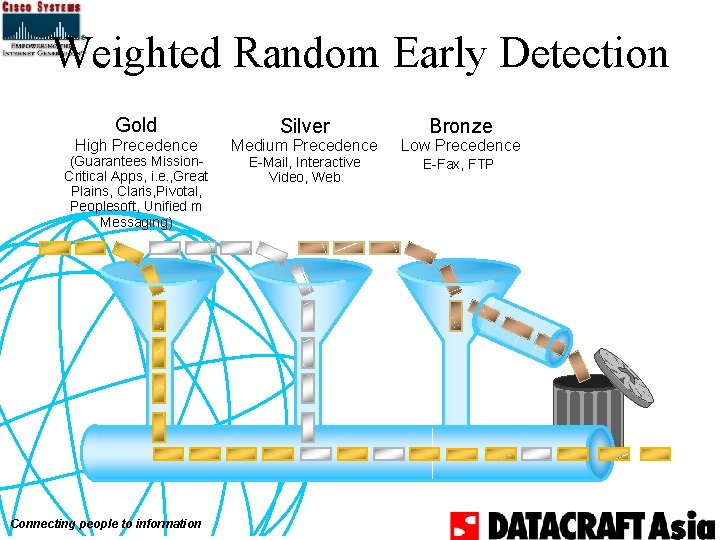
Custom Queuing Commands • queue-list protocol – Establishes queuing priority based on protocol type [no] queue-list <list-number> protocol <protocolname> <queue-number> <queue-keyword> <keywordvalue> • queue-list interface – Establishes queuing priority based on incoming interface [no] queue-list <list-number> interface <interface-name> <interface-number> <queue #> Connecting people to information
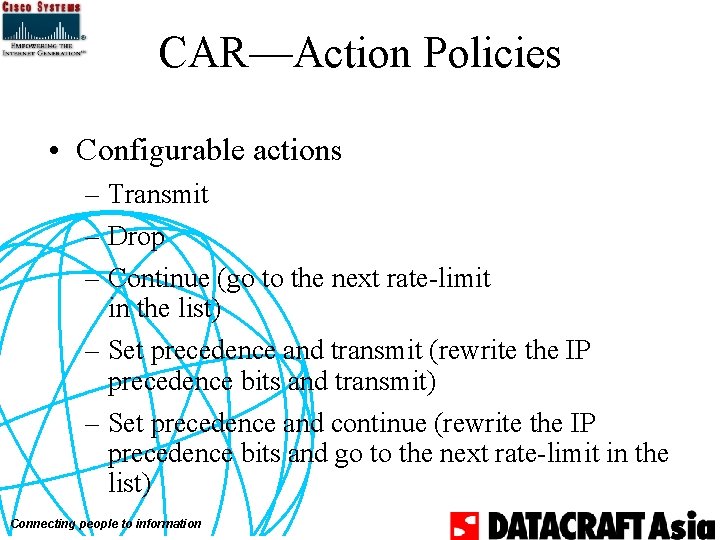
Custom Queuing Commands • queue-list default – Assigns priority-queue for those packets that do not match any rule in priority-list. If not specified, queue number 1 is default. [no] queue-list <list-number> default <queuenumber> • queue-list queue limit – Designate queue length limit for a custom queue [no] queue-list <list-number> queue <queuenumber> limit <limit-number> Connecting people to information
![Custom Queuing Commands queuelist queue bytecount Designate bytecount allowed per queue no Custom Queuing Commands • queue-list queue byte-count – Designate byte-count allowed per queue [no]](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-37.jpg)
Custom Queuing Commands • queue-list queue byte-count – Designate byte-count allowed per queue [no] queue-list <list-number> queue <queue-number> byte-count <byte-count-number> • queue-list lowest-custom – Sets lowest number of queue to be treated as custom [no] queue-list <list-number> lowest-custom <queuenumber> • custom-queue-list – Assigns a specified queue-list to an interface [no] custom-queue-list <list> Connecting people to information
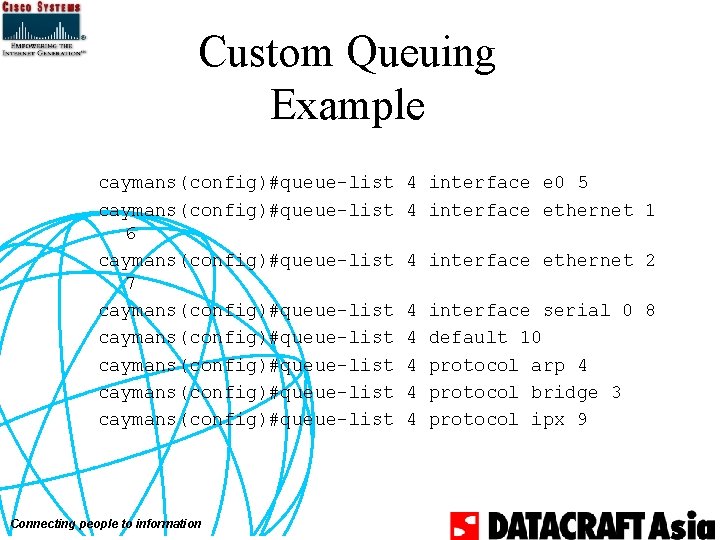
Custom Queuing Example caymans(config)#queue-list 6 caymans(config)#queue-list 7 caymans(config)#queue-list caymans(config)#queue-list Connecting people to information 4 interface e 0 5 4 interface ethernet 1 4 interface ethernet 2 4 4 4 interface serial 0 8 default 10 protocol arp 4 protocol bridge 3 protocol ipx 9
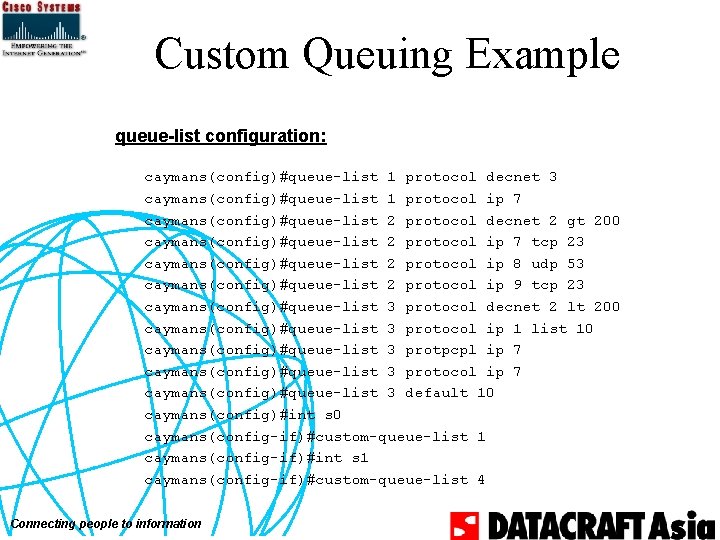
Custom Queuing Example queue-list configuration: caymans(config)#queue-list 1 protocol decnet 3 caymans(config)#queue-list 1 protocol ip 7 caymans(config)#queue-list 2 protocol decnet 2 gt 200 caymans(config)#queue-list 2 protocol ip 7 tcp 23 caymans(config)#queue-list 2 protocol ip 8 udp 53 caymans(config)#queue-list 2 protocol ip 9 tcp 23 caymans(config)#queue-list 3 protocol decnet 2 lt 200 caymans(config)#queue-list 3 protocol ip 1 list 10 caymans(config)#queue-list 3 protpcpl ip 7 caymans(config)#queue-list 3 protocol ip 7 caymans(config)#queue-list 3 default 10 caymans(config)#int s 0 caymans(config-if)#custom-queue-list 1 caymans(config-if)#int s 1 caymans(config-if)#custom-queue-list 4 Connecting people to information
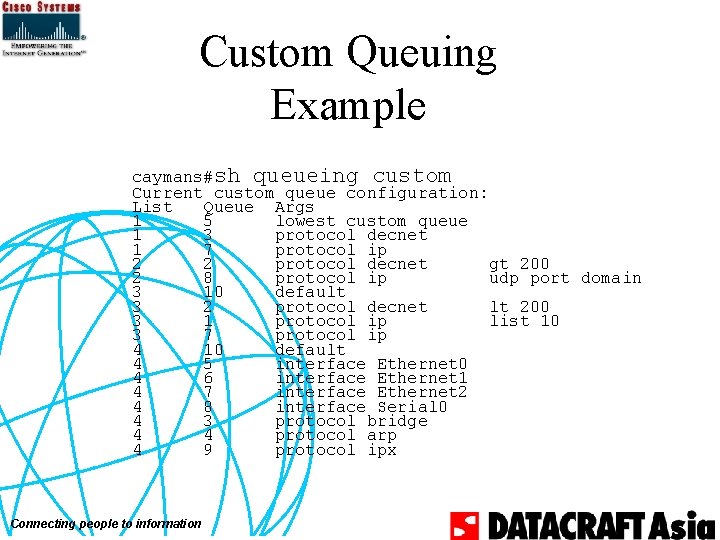
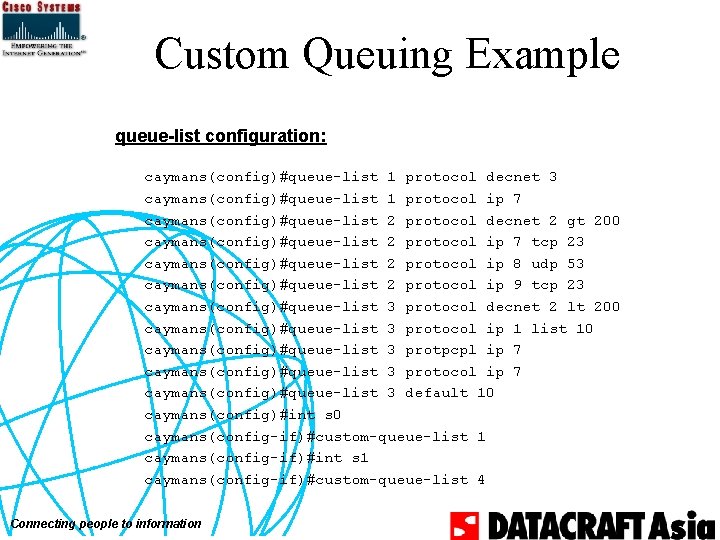
Custom Queuing Example caymans#sh queueing custom Current custom queue configuration: List Queue Args 1 5 lowest custom queue 1 3 protocol decnet 1 7 protocol ip 2 2 protocol decnet gt 200 2 8 protocol ip udp port domain 3 10 default 3 2 protocol decnet lt 200 3 1 protocol ip list 10 3 7 protocol ip 4 10 default 4 5 interface Ethernet 0 4 6 interface Ethernet 1 4 7 interface Ethernet 2 4 8 interface Serial 0 4 3 protocol bridge 4 4 protocol arp 4 9 protocol ipx Connecting people to information
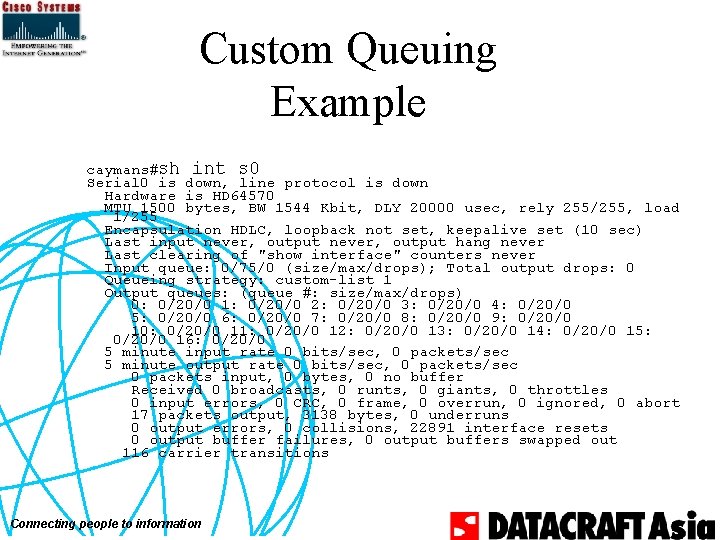
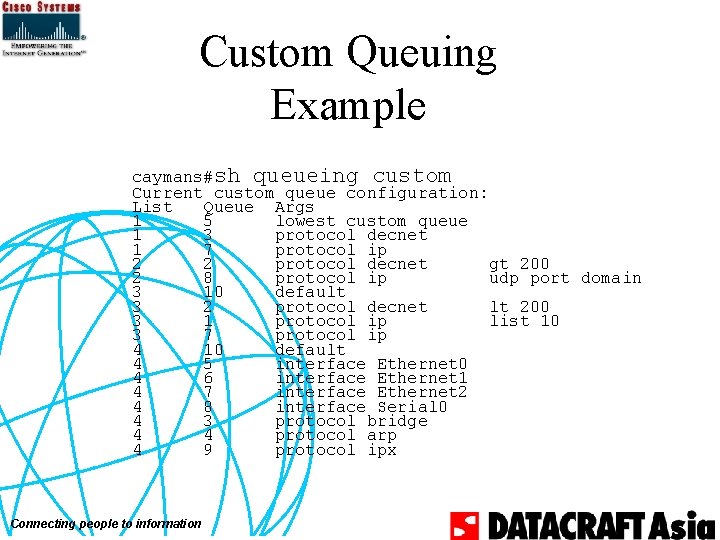
Custom Queuing Example caymans#sh int s 0 Serial 0 is down, line protocol is down Hardware is HD 64570 MTU 1500 bytes, BW 1544 Kbit, DLY 20000 usec, rely 255/255, load 1/255 Encapsulation HDLC, loopback not set, keepalive set (10 sec) Last input never, output hang never Last clearing of "show interface" counters never Input queue: 0/75/0 (size/max/drops); Total output drops: 0 Queueing strategy: custom-list 1 Output queues: (queue #: size/max/drops) 0: 0/20/0 1: 0/20/0 2: 0/20/0 3: 0/20/0 4: 0/20/0 5: 0/20/0 6: 0/20/0 7: 0/20/0 8: 0/20/0 9: 0/20/0 10: 0/20/0 11: 0/20/0 12: 0/20/0 13: 0/20/0 14: 0/20/0 15: 0/20/0 16: 0/20/0 5 minute input rate 0 bits/sec, 0 packets/sec 5 minute output rate 0 bits/sec, 0 packets/sec 0 packets input, 0 bytes, 0 no buffer Received 0 broadcasts, 0 runts, 0 giants, 0 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort 17 packets output, 3138 bytes, 0 underruns 0 output errors, 0 collisions, 22891 interface resets 0 output buffer failures, 0 output buffers swapped out 116 carrier transitions Connecting people to information
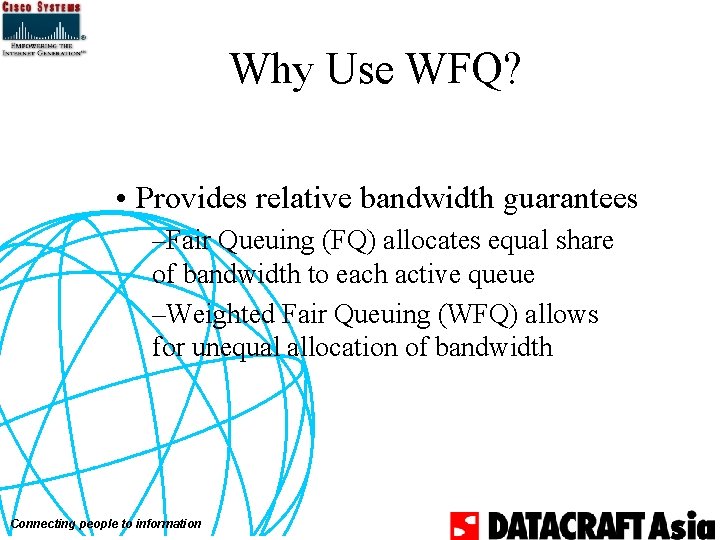
Why Use WFQ? • Provides relative bandwidth guarantees –Fair Queuing (FQ) allocates equal share of bandwidth to each active queue –Weighted Fair Queuing (WFQ) allows for unequal allocation of bandwidth Connecting people to information
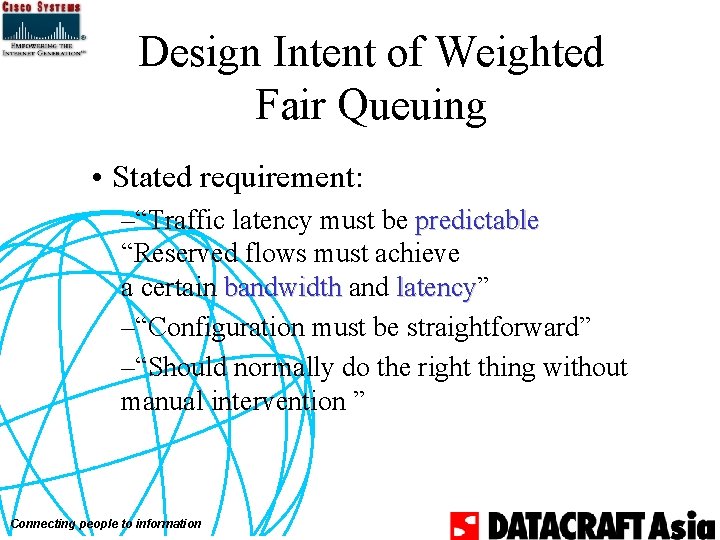
Design Intent of Weighted Fair Queuing • Stated requirement: –“Traffic latency must be predictable “Reserved flows must achieve a certain bandwidth and latency” latency –“Configuration must be straightforward” –“Should normally do the right thing without manual intervention ” Connecting people to information
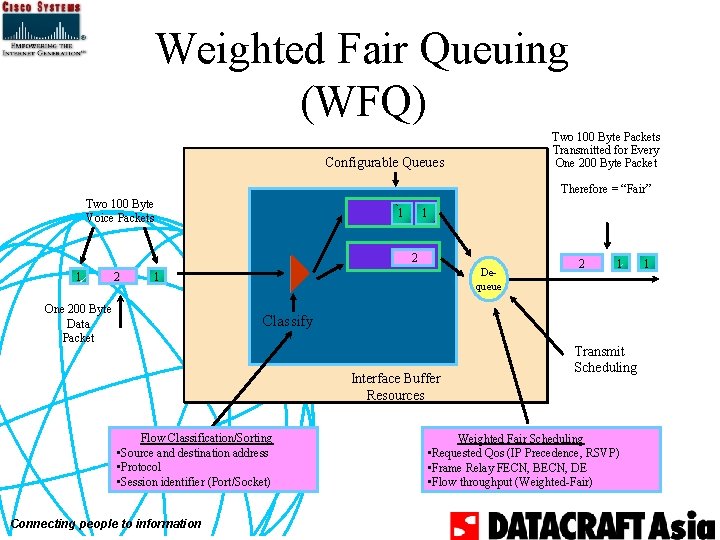
Weighted Fair Queuing (WFQ) Two 100 Byte Packets Transmitted for Every One 200 Byte Packet Configurable Queues Therefore = “Fair” Two 100 Byte Voice Packets 1 1 2 Dequeue 1 One 200 Byte Data Packet 2 1 Classify Interface Buffer Resources Flow Classification/Sorting • Source and destination address • Protocol • Session identifier (Port/Socket) Connecting people to information Transmit Scheduling Weighted Fair Scheduling • Requested Qos (IP Precedence, RSVP) • Frame Relay FECN, BECN, DE • Flow throughput (Weighted-Fair) 1
Feature Description QDynamically identifies data streams using an interface QDynamically prioritizes those data streams Connecting people to information
So What? QEqual access for File Transfer traffic QPriority for Interactive Traffic QFuture: Guarantees for Real Time Traffic QHands Free! No Access Lists! Connecting people to information
Fair Queuing “Conversations” Q Ideally: data streams exchanged by applications Q Practically: discernible data streams Source and destination address Protocol type Session identifier (port or socket number) Qo. S/TOS Connecting people to information
![Configuration fairqueue congestive discard threshold hashedqueues reservedqueues Qcongestive discard policy hits conversations with more Configuration fair-queue [congestive discard threshold] [#hashed_queues] [reserved_queues] Qcongestive discard policy hits conversations with more](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-48.jpg)
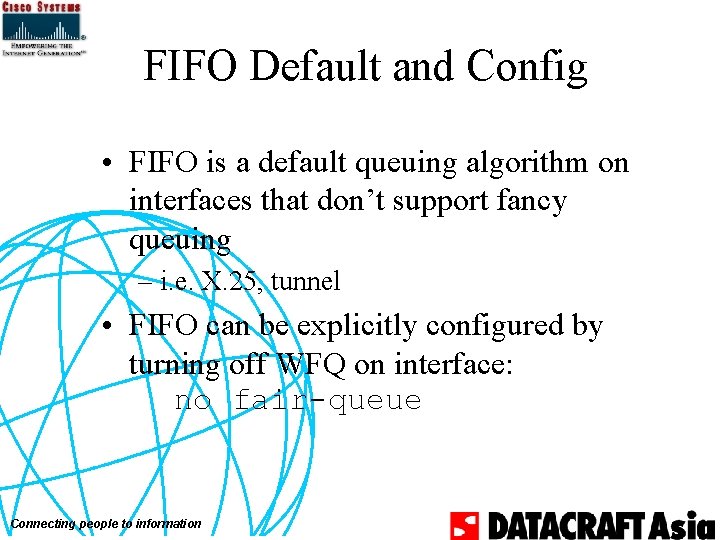
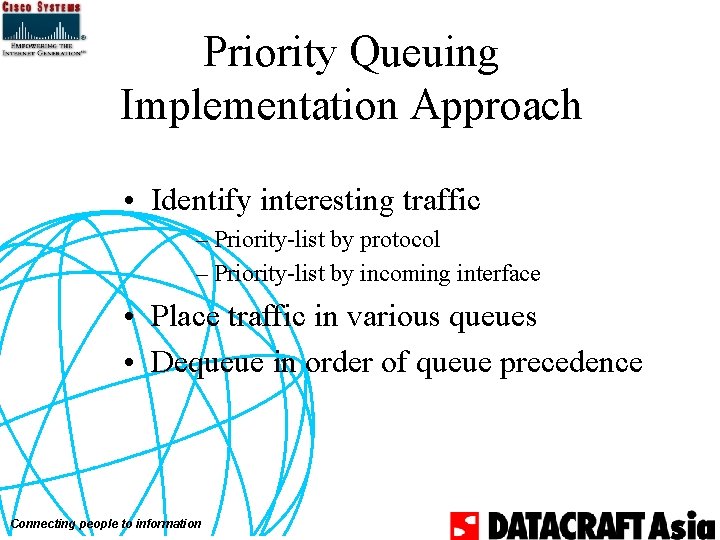
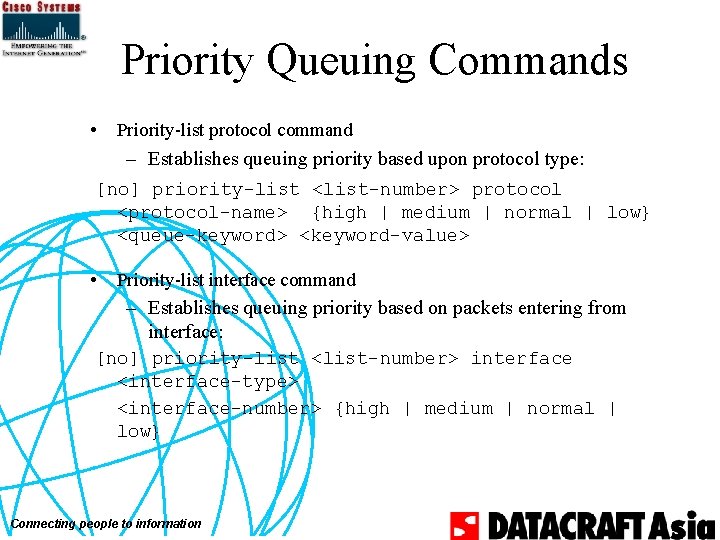
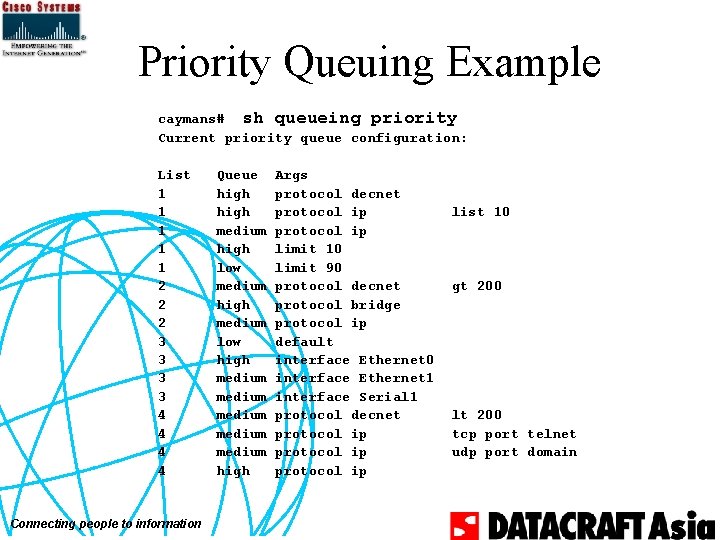
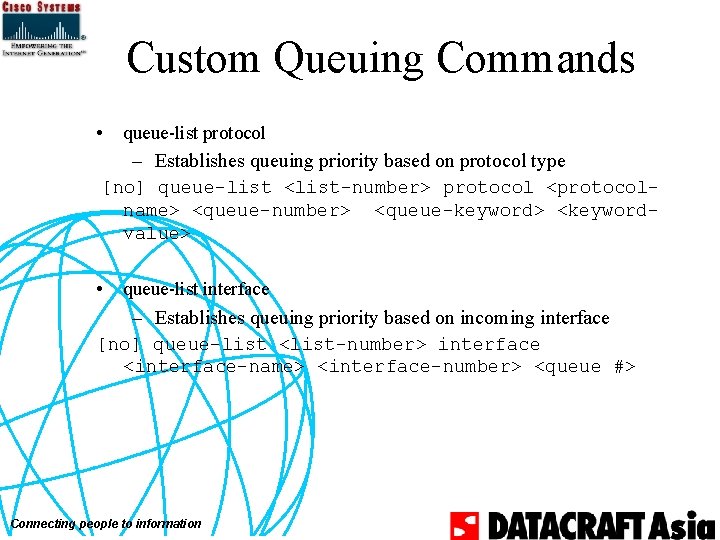
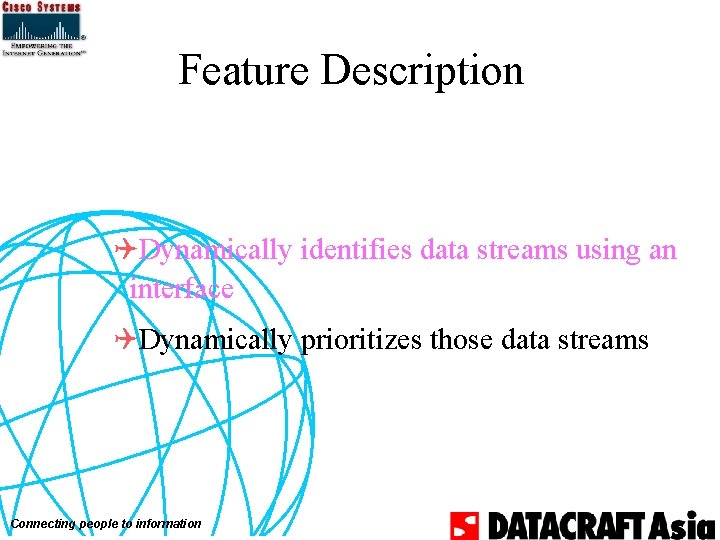
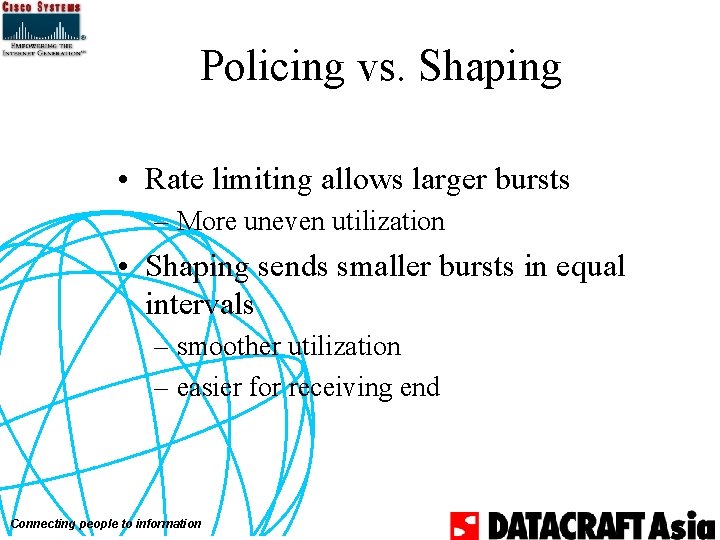
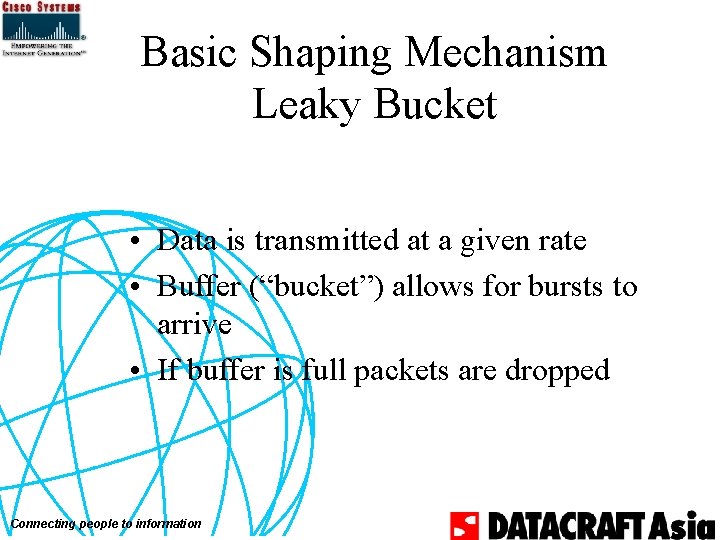
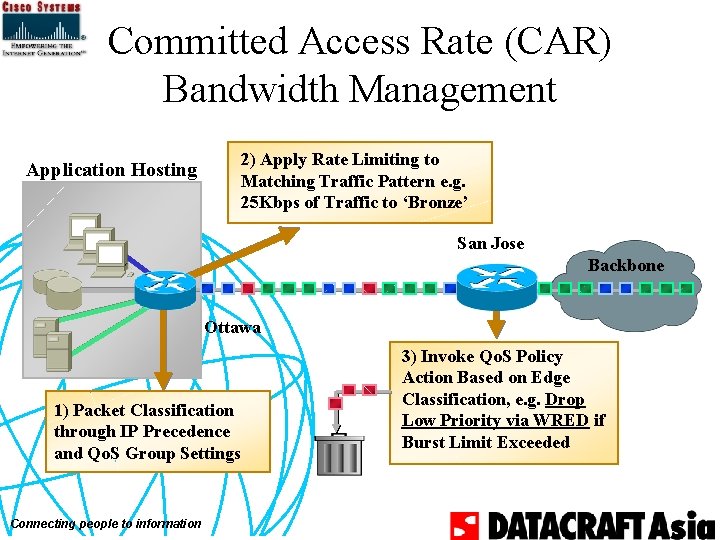
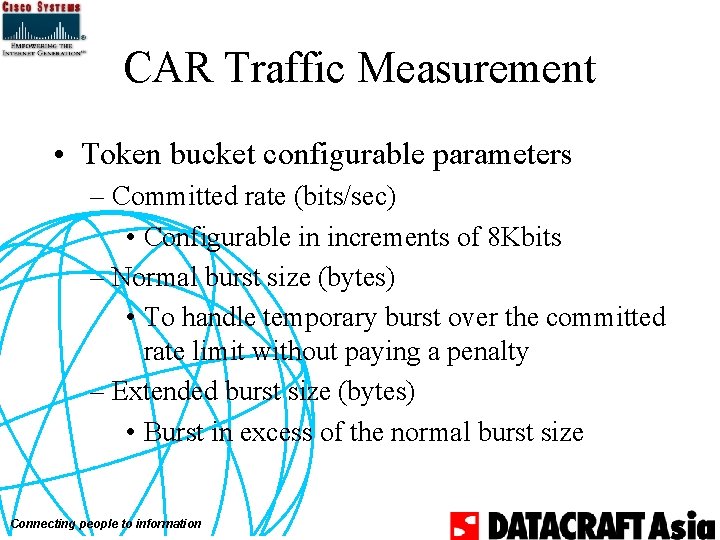
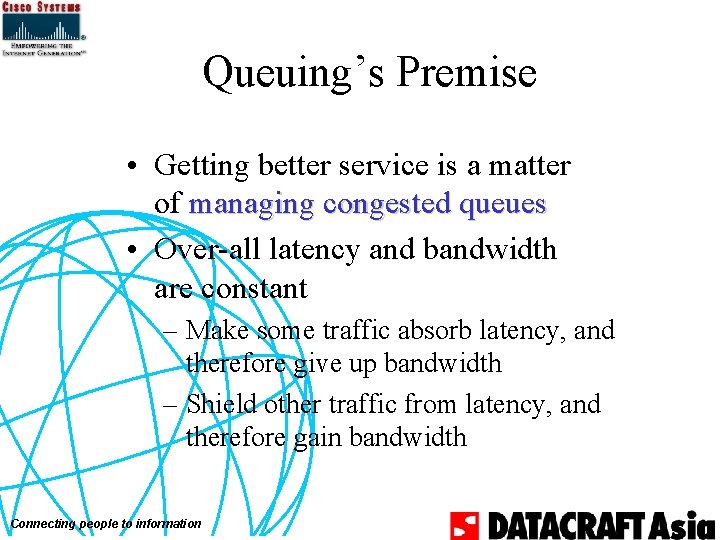
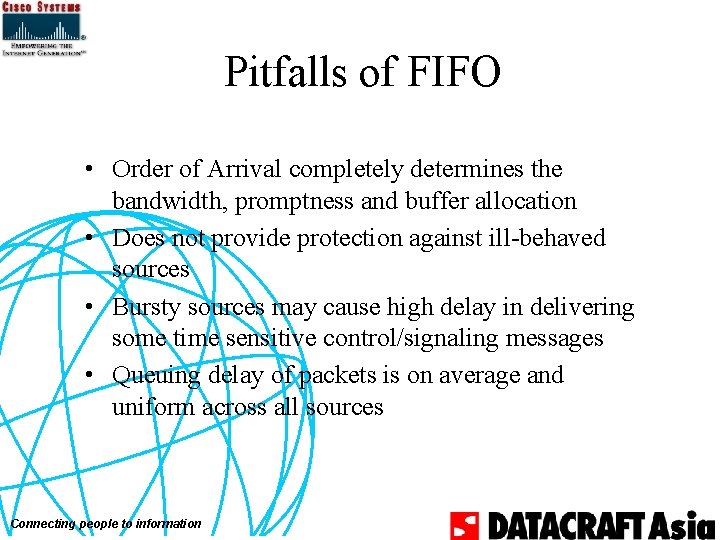
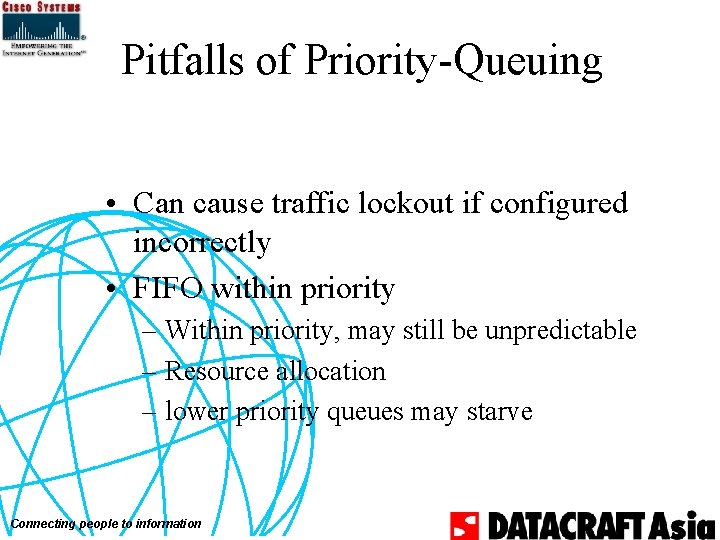
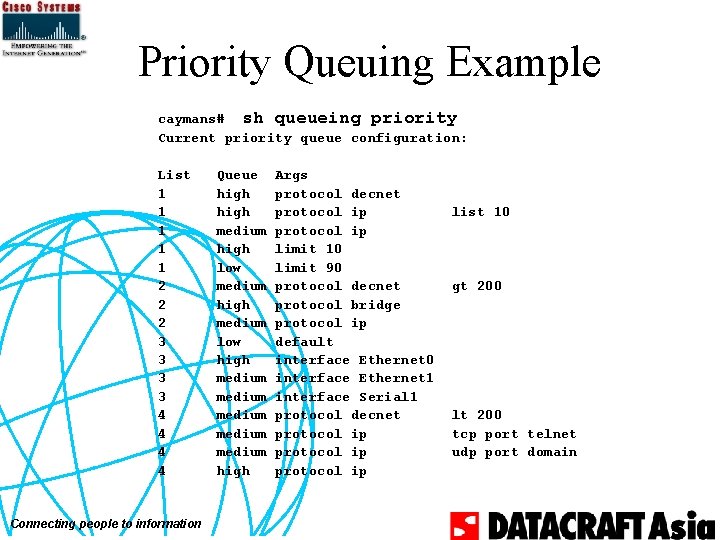
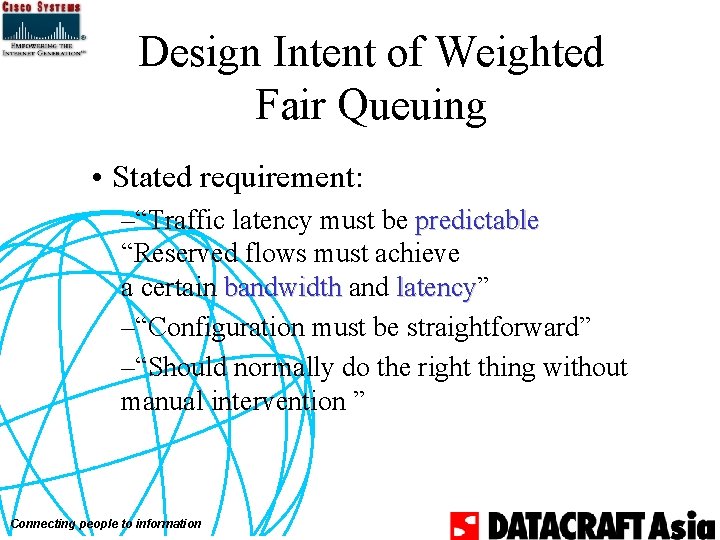
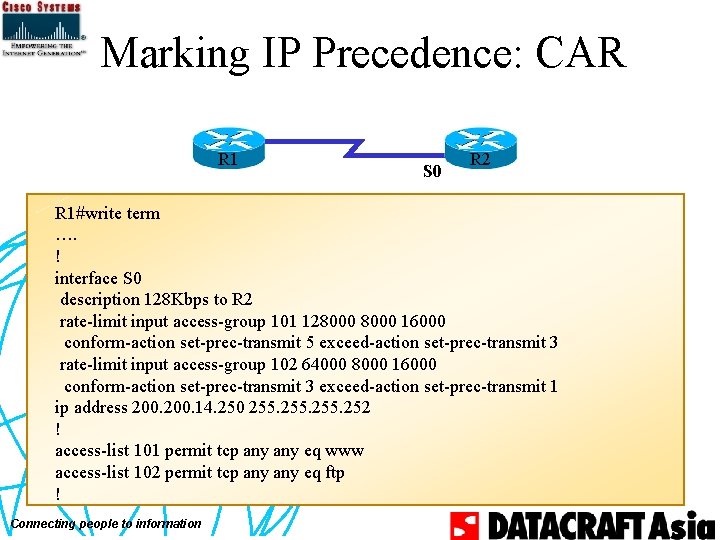
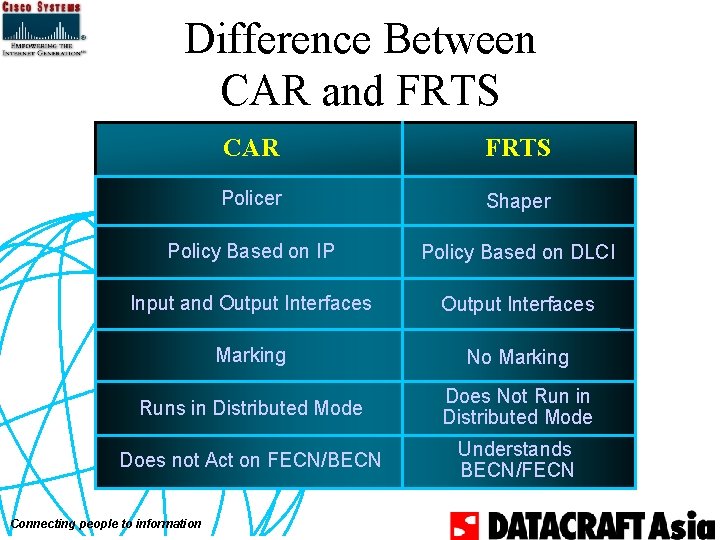
Configuration fair-queue [congestive discard threshold] [#hashed_queues] [reserved_queues] Qcongestive discard policy hits conversations with more than one message occurs when total number of messages > threshold Connecting people to information
Configuration Default Qinactive on LANs and high speed lines Qinactive on serial lines with LAPB, X. 25, PPP Compression, etc. Qactive on other serial lines at E-1 speed or below eg: PPP, HDLC, Frame Relay, SMDS Connecting people to information
![DiagnosticsTroubleshooting show interface interface name show queue interface name show queueing fair custom Diagnostics/Troubleshooting show interface [interface name] show queue interface name show queueing [fair | custom](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-50.jpg)
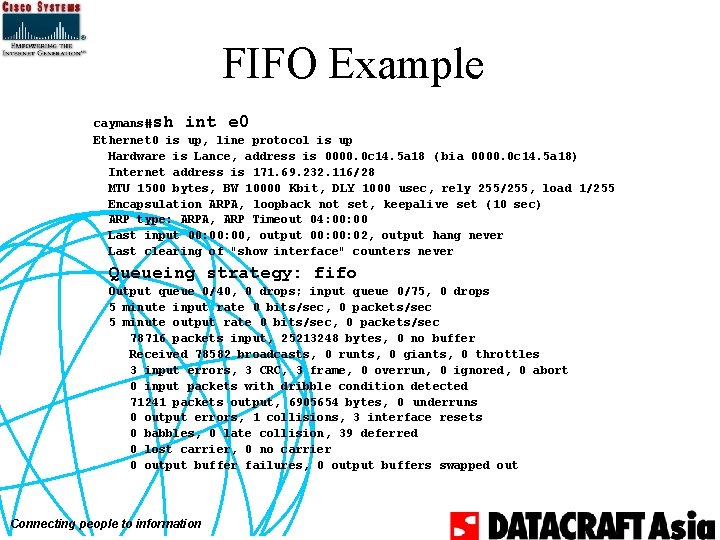
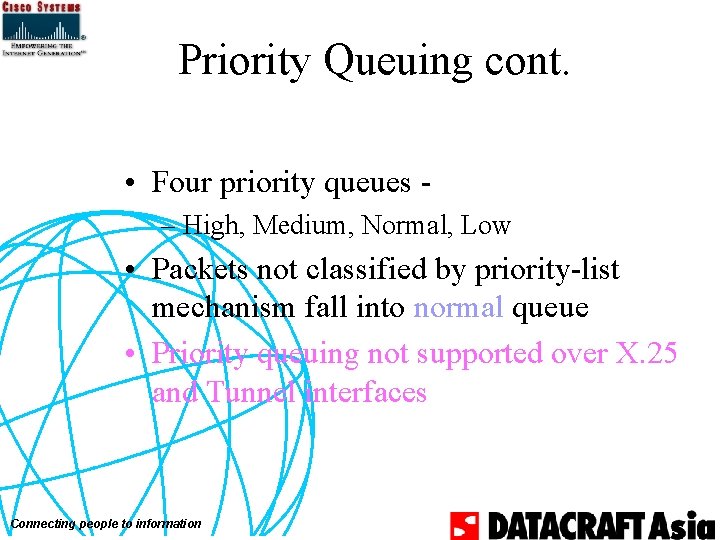
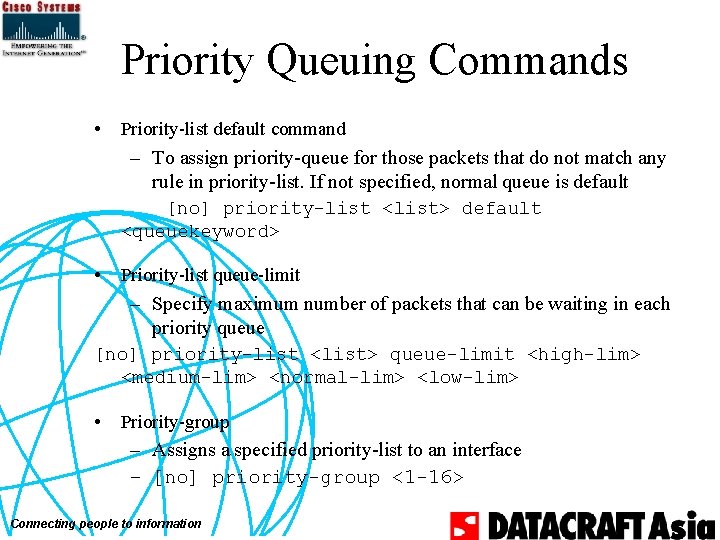
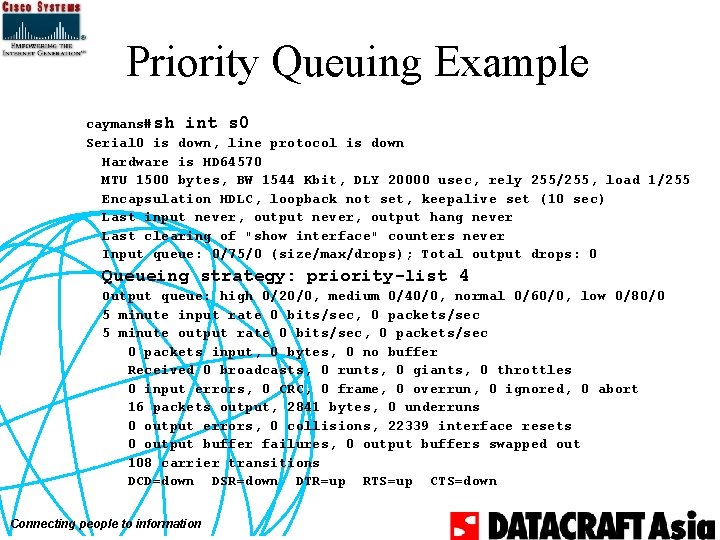
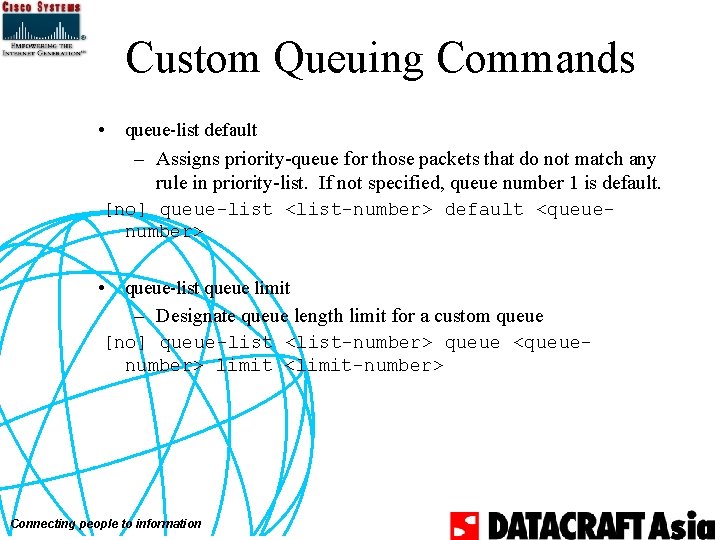
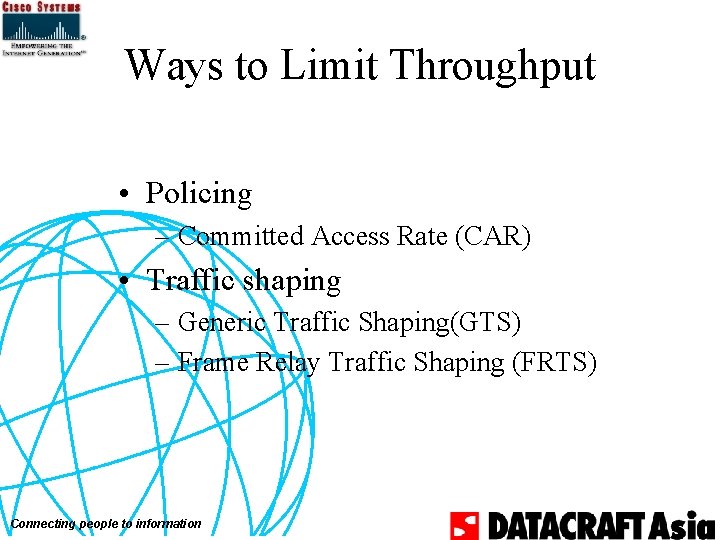
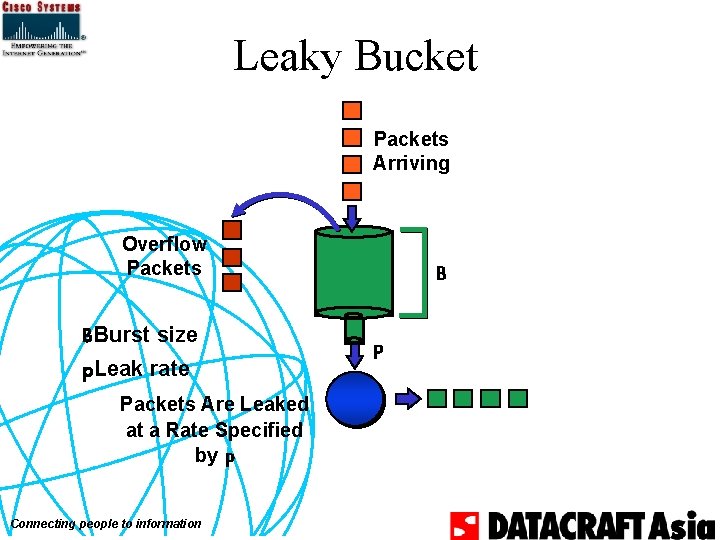
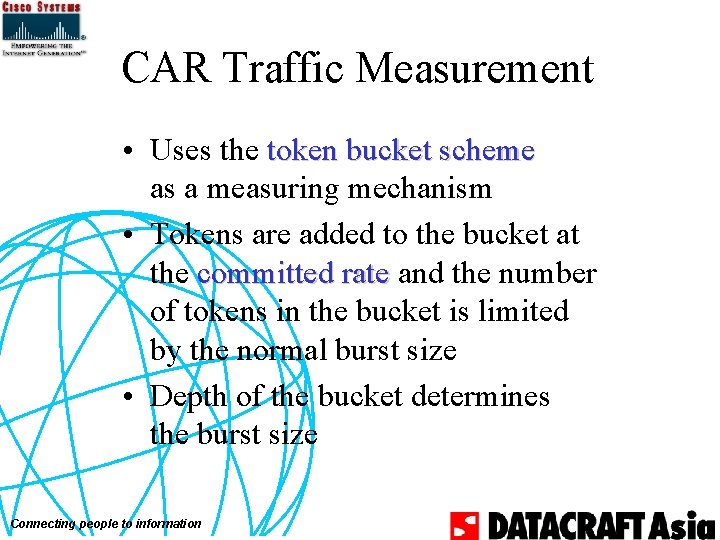
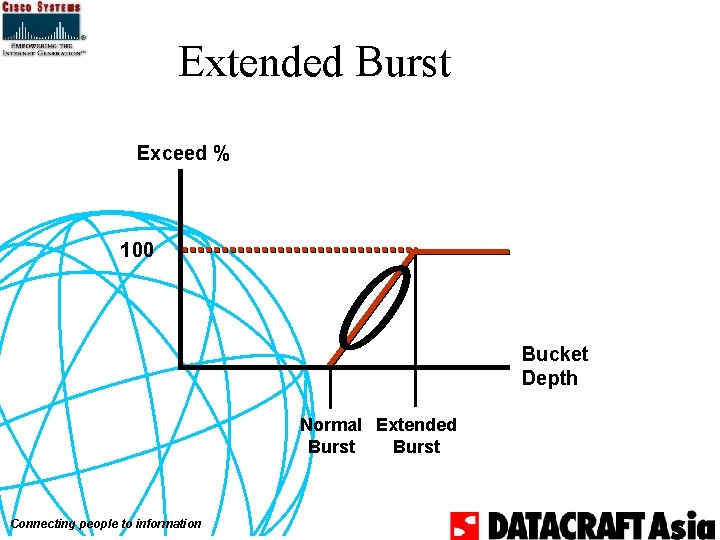
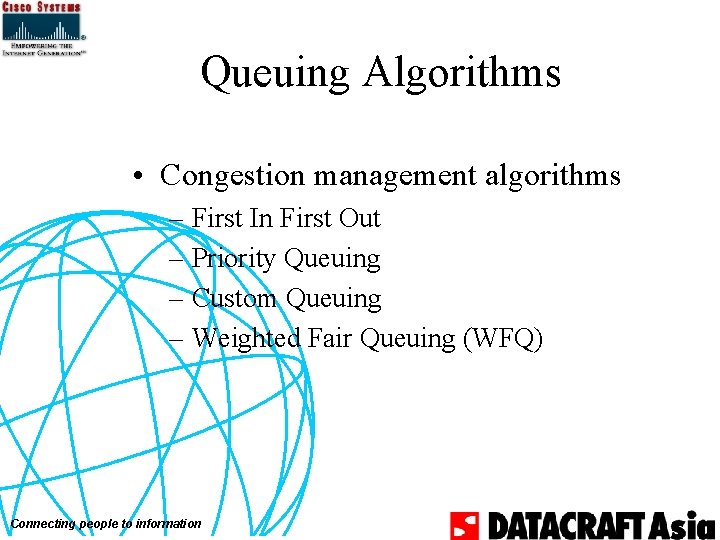
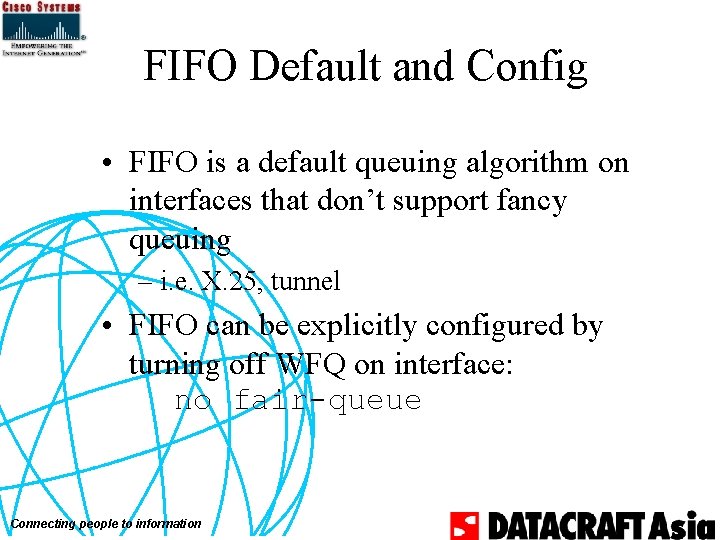
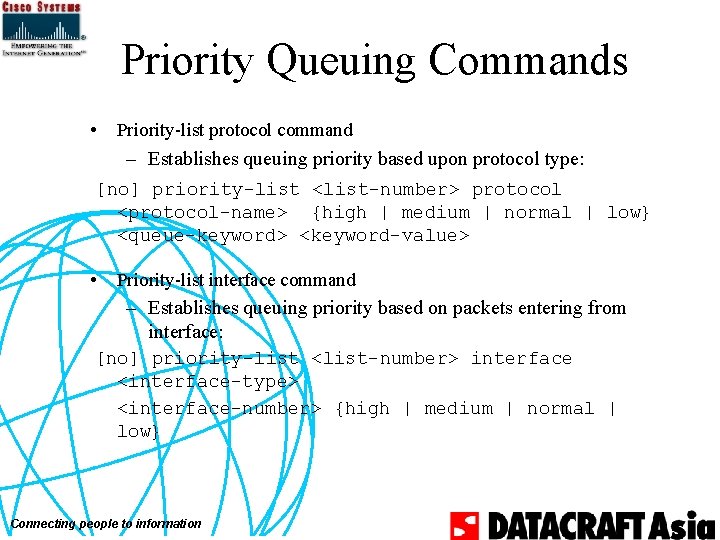
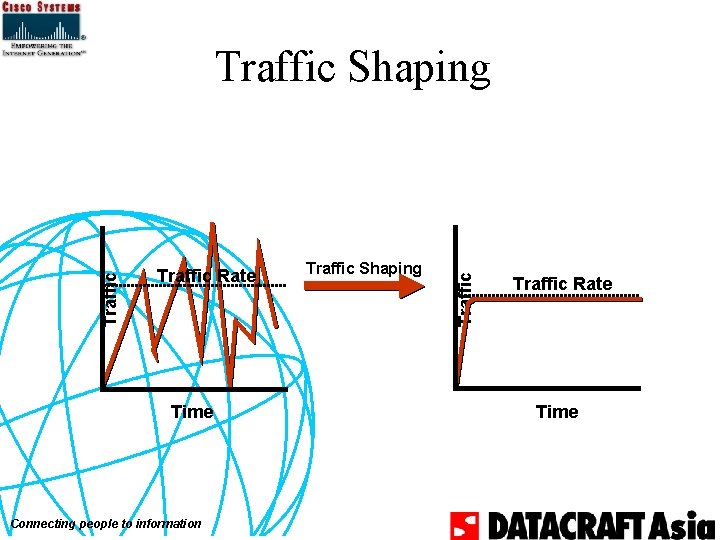
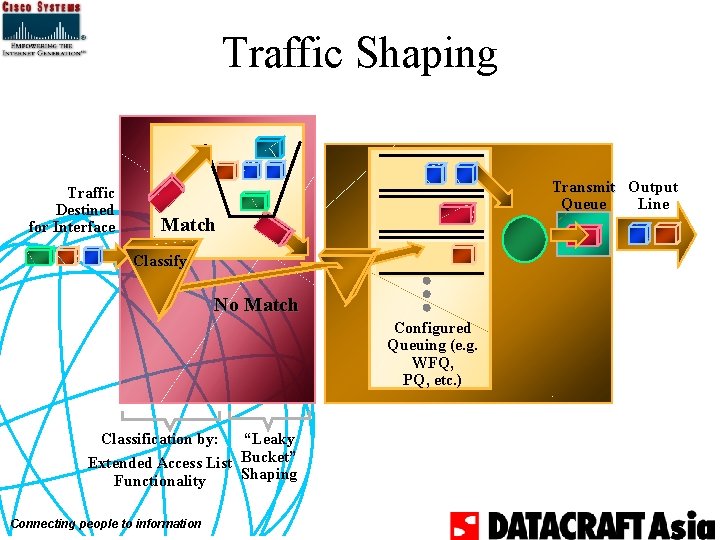
Diagnostics/Troubleshooting show interface [interface name] show queue interface name show queueing [fair | custom | priority] Connecting people to information
Pitfalls of Weighted Fair Queuing • Requires more sorting than other approaches Connecting people to information
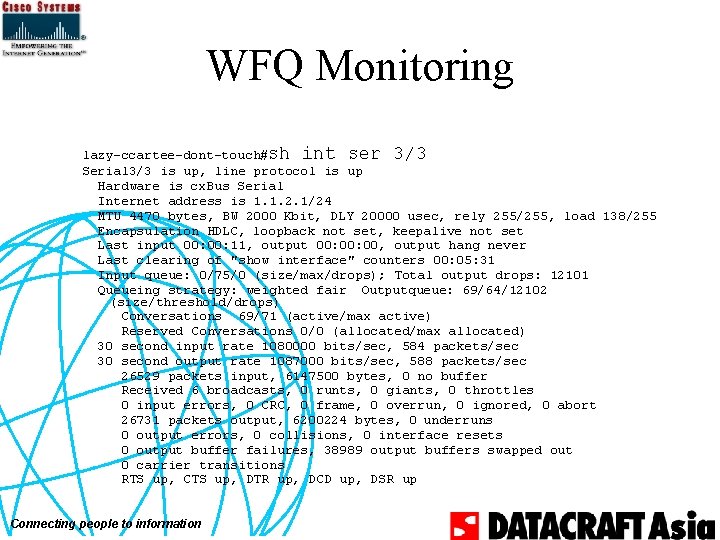
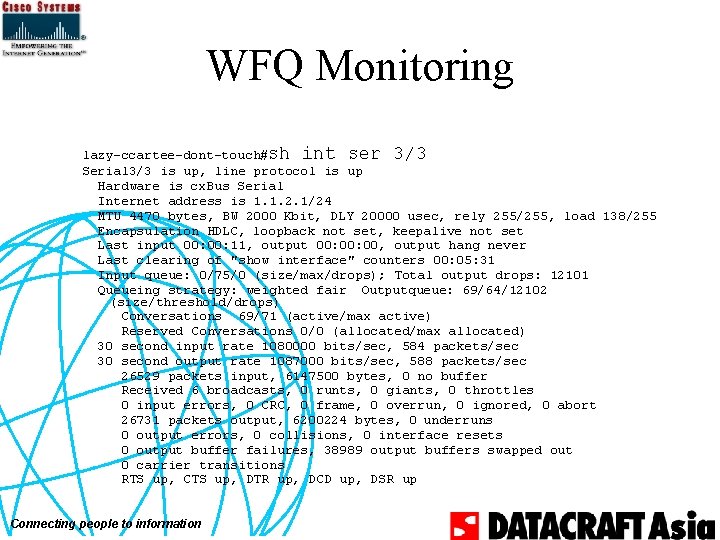
WFQ Monitoring lazy-ccartee-dont-touch#sh int ser 3/3 Serial 3/3 is up, line protocol is up Hardware is cx. Bus Serial Internet address is 1. 1. 2. 1/24 MTU 4470 bytes, BW 2000 Kbit, DLY 20000 usec, rely 255/255, load 138/255 Encapsulation HDLC, loopback not set, keepalive not set Last input 00: 11, output 00: 00, output hang never Last clearing of "show interface" counters 00: 05: 31 Input queue: 0/75/0 (size/max/drops); Total output drops: 12101 Queueing strategy: weighted fair Outputqueue: 69/64/12102 (size/threshold/drops) Conversations 69/71 (active/max active) Reserved Conversations 0/0 (allocated/max allocated) 30 second input rate 1080000 bits/sec, 584 packets/sec 30 second output rate 1087000 bits/sec, 588 packets/sec 26529 packets input, 6147500 bytes, 0 no buffer Received 6 broadcasts, 0 runts, 0 giants, 0 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort 26731 packets output, 6200224 bytes, 0 underruns 0 output errors, 0 collisions, 0 interface resets 0 output buffer failures, 38989 output buffers swapped out 0 carrier transitions RTS up, CTS up, DTR up, DCD up, DSR up Connecting people to information
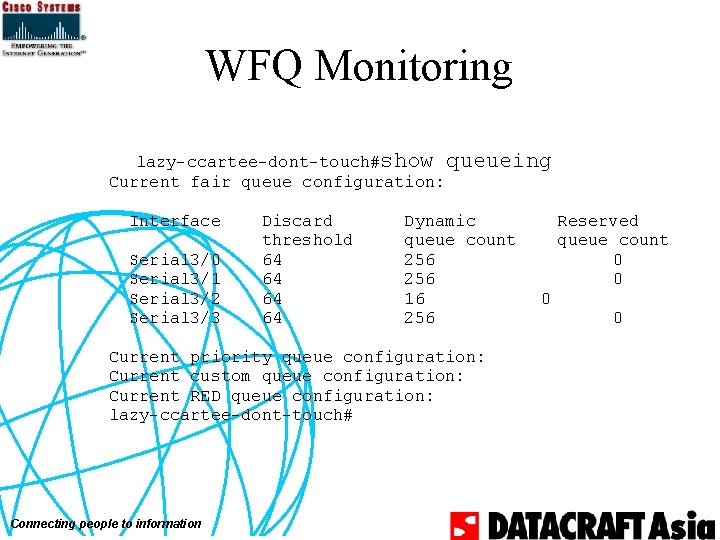
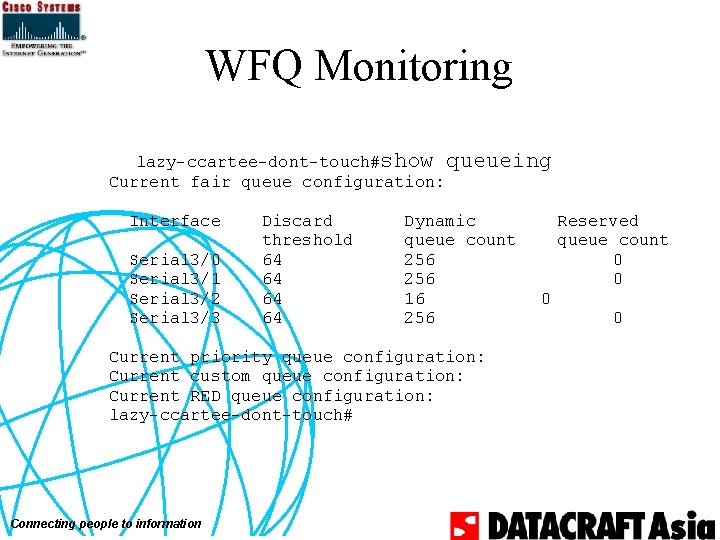
WFQ Monitoring lazy-ccartee-dont-touch#show queueing Current fair queue configuration: Interface Serial 3/0 Serial 3/1 Serial 3/2 Serial 3/3 Discard threshold 64 64 Dynamic queue count 256 16 256 Current priority queue configuration: Current custom queue configuration: Current RED queue configuration: lazy-ccartee-dont-touch# Connecting people to information Reserved queue count 0 0
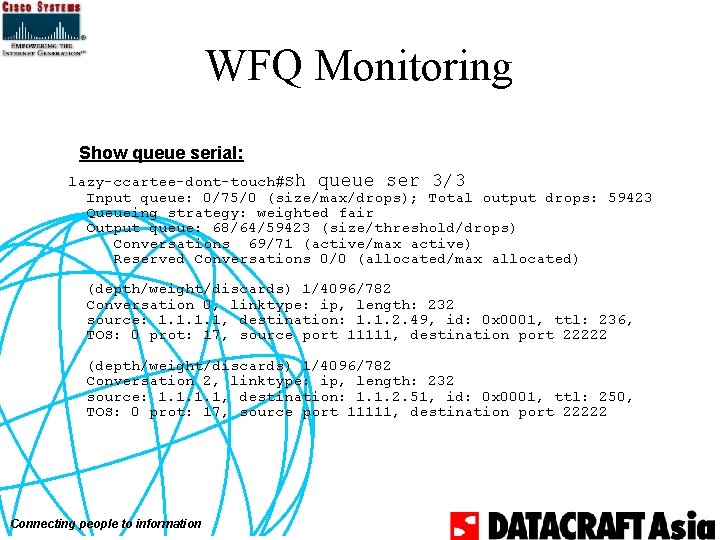
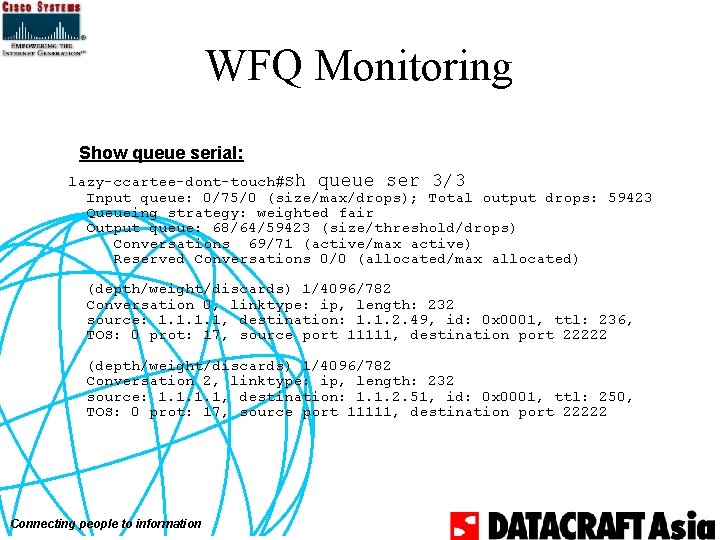
WFQ Monitoring Show queue serial: lazy-ccartee-dont-touch#sh queue ser 3/3 Input queue: 0/75/0 (size/max/drops); Total output drops: 59423 Queueing strategy: weighted fair Output queue: 68/64/59423 (size/threshold/drops) Conversations 69/71 (active/max active) Reserved Conversations 0/0 (allocated/max allocated) (depth/weight/discards) 1/4096/782 Conversation 0, linktype: ip, length: 232 source: 1. 1, destination: 1. 1. 2. 49, id: 0 x 0001, ttl: 236, TOS: 0 prot: 17, source port 11111, destination port 22222 (depth/weight/discards) 1/4096/782 Conversation 2, linktype: ip, length: 232 source: 1. 1, destination: 1. 1. 2. 51, id: 0 x 0001, ttl: 250, TOS: 0 prot: 17, source port 11111, destination port 22222 Connecting people to information
Policing & Shaping Connecting people to information
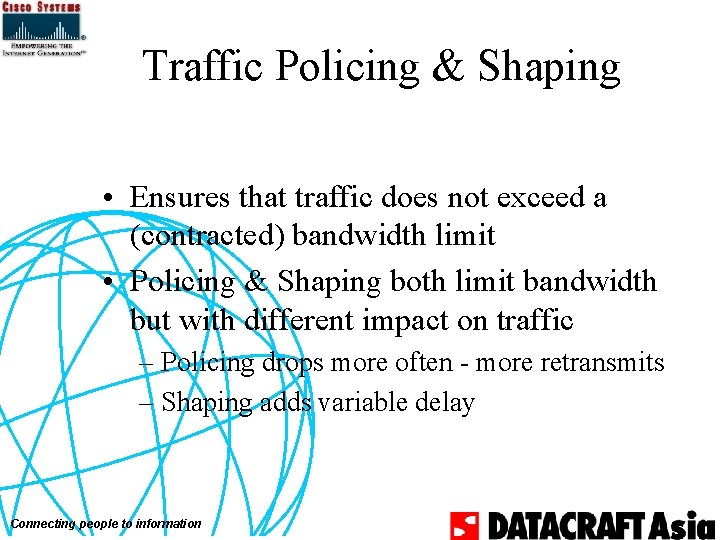
Traffic Policing & Shaping • Ensures that traffic does not exceed a (contracted) bandwidth limit • Policing & Shaping both limit bandwidth but with different impact on traffic – Policing drops more often - more retransmits – Shaping adds variable delay Connecting people to information
Traffic Rate Policing Traffic Policing vs. Shaping Traffic Rate Time Connecting people to information Time Shaping Traffic Time Traffic Rate Time
Policing vs. Shaping • Rate limiting allows larger bursts – More uneven utilization • Shaping sends smaller bursts in equal intervals – smoother utilization – easier for receiving end Connecting people to information
Ways to Limit Throughput • Policing – Committed Access Rate (CAR) • Traffic shaping – Generic Traffic Shaping(GTS) – Frame Relay Traffic Shaping (FRTS) Connecting people to information
Basic Policing Mechanism - Token Bucket • Data needs credits (“tokens”) to be transmitted, otherwise it is dropped • Tokens are issued at the policing rate • Tokens usually are accumulated in a “bucket” to accommodate bursts • No limit how fast tokens can be taken out of the bucket, allows bursts to use large chunks of bandwidth Connecting people to information
Token Bucket Tokens B�Burst Size p Overflow Tokens B Packets Arriving Connecting people to information p�Token Arrival Rate Conform Exceed
Basic Shaping Mechanism Leaky Bucket • Data is transmitted at a given rate • Buffer (“bucket”) allows for bursts to arrive • If buffer is full packets are dropped Connecting people to information
Leaky Bucket Packets Arriving Overflow Packets BBurst size p. Leak rate Packets Are Leaked at a Rate Specified by p Connecting people to information B p
Token vs. Leaky Bucket • Token bucket –Passes bursts –No buffering –Does not smoothes or shapes traffic • Leaky bucket –Smoothes or shapes traffic, this is achieved by buffering the traffic –Used in ATM networks for traffic shaping and policing • Known also as Generic Cell Rate Algorithm (GCRA) in ATM Connecting people to information
Committed Access Rate (CAR) • Two functions – Packet classification—IP precedence and Qo. S group setting – Access bandwidth management through rate limiting (policing) Connecting people to information
Marking: IP Precedence IP Packet • Qo. S marking • Inband • Differentiated network services across any media or topology Connecting people to information Data Type of Service (To. S) IP Precedence Diff Serv Code Point (DSCP) Data, Voice, Video
CAR—Traffic Matching Specification • Identify packets of interest for packet classification or rate limiting or both • Matching specification – 1) All traffic – 2) IP precedence – 3) MAC address – 4) IP access list—standard and extended (slower) Connecting people to information
Committed Access Rate (CAR) • Two functions – Packet Classification IP precedence and Qo. S group setting – Access Bandwidth Management through rate limiting Connecting people to information
CAR—Action Policies • Configurable actions – Transmit – Drop – Continue (go to the next rate-limit in the list) – Set precedence and transmit (rewrite the IP precedence bits and transmit) – Set precedence and continue (rewrite the IP precedence bits and go to the next rate-limit in the list) Connecting people to information
Committed Access Rate (CAR) Bandwidth Management Application Hosting 2) Apply Rate Limiting to Matching Traffic Pattern e. g. 25 Kbps of Traffic to ‘Bronze’ San Jose Backbone Ottawa 1) Packet Classification through IP Precedence and Qo. S Group Settings Connecting people to information 3) Invoke Qo. S Policy Action Based on Edge Classification, e. g. Drop Low Priority via WRED if Burst Limit Exceeded
CAR Traffic Measurement • Uses the token bucket scheme as a measuring mechanism • Tokens are added to the bucket at the committed rate and the number of tokens in the bucket is limited by the normal burst size • Depth of the bucket determines the burst size Connecting people to information
CAR Traffic Measurement • Packets arriving with sufficient tokens in the bucket are said to conform • Packets arriving with insufficient tokens in the bucket are said to exceed Connecting people to information
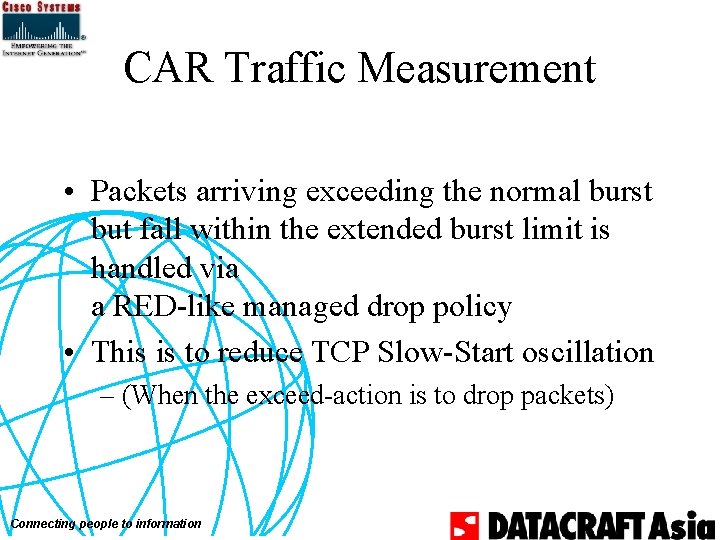
CAR Traffic Measurement • Packets arriving exceeding the normal burst but fall within the extended burst limit is handled via a RED-like managed drop policy • This is to reduce TCP Slow-Start oscillation – (When the exceed-action is to drop packets) Connecting people to information
CAR Traffic Measurement • Token bucket configurable parameters – Committed rate (bits/sec) • Configurable in increments of 8 Kbits – Normal burst size (bytes) • To handle temporary burst over the committed rate limit without paying a penalty – Extended burst size (bytes) • Burst in excess of the normal burst size Connecting people to information
Extended Burst Exceed % 100 Bucket Depth Normal Extended Burst Connecting people to information
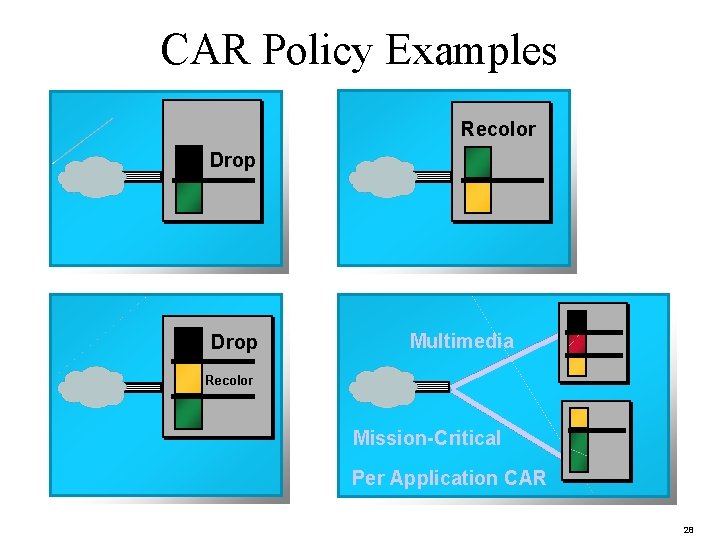
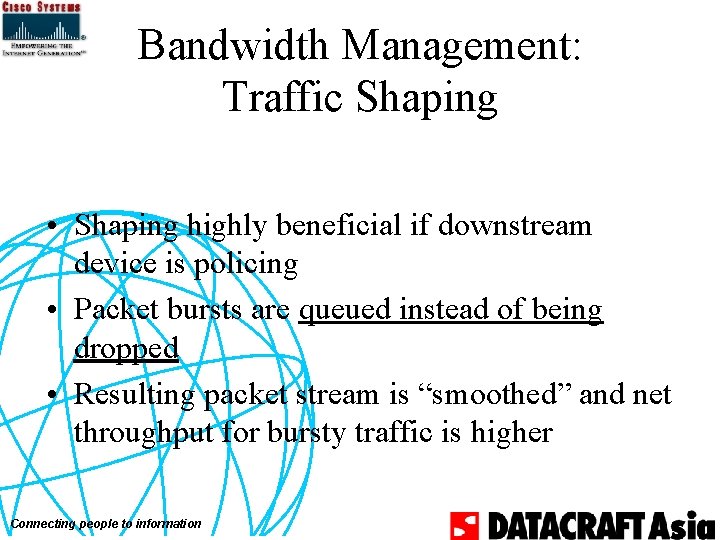
CAR Policy Examples Recolor Drop Multimedia Recolor Mission-Critical Per Application CAR 28
![Marking at the Edge IP Precedence CAR accesslist no accesslist ratelimit 1 Marking at the Edge: IP Precedence • CAR access-list – [no] access-list rate-limit <1–](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-77.jpg)
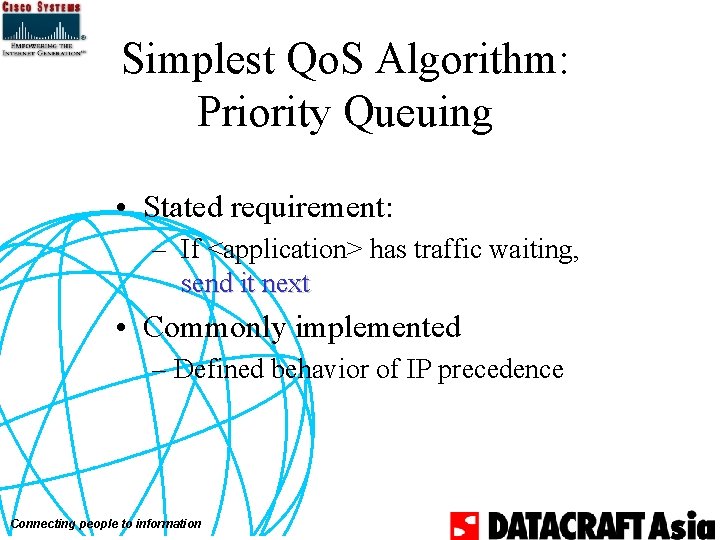
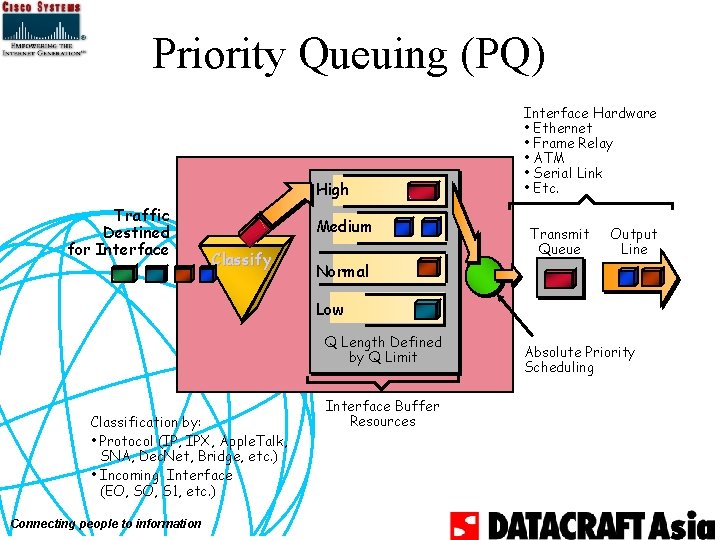
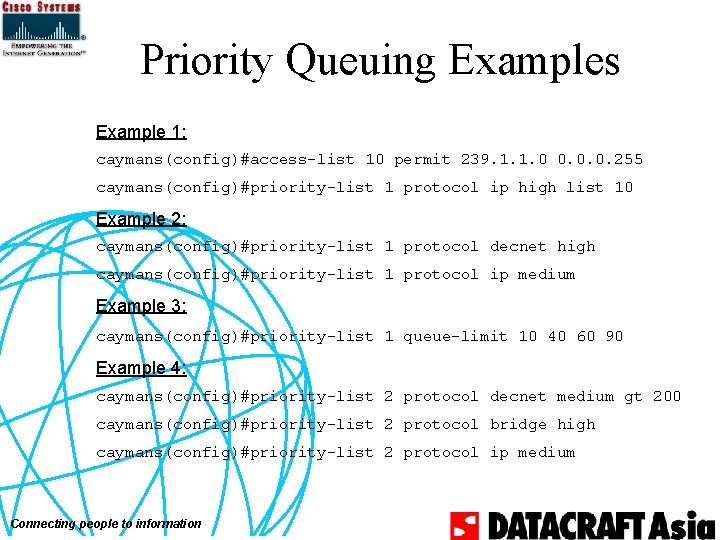
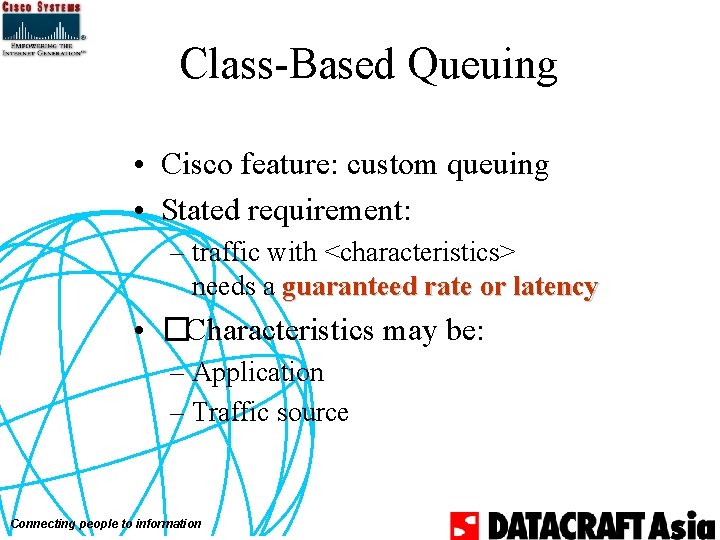
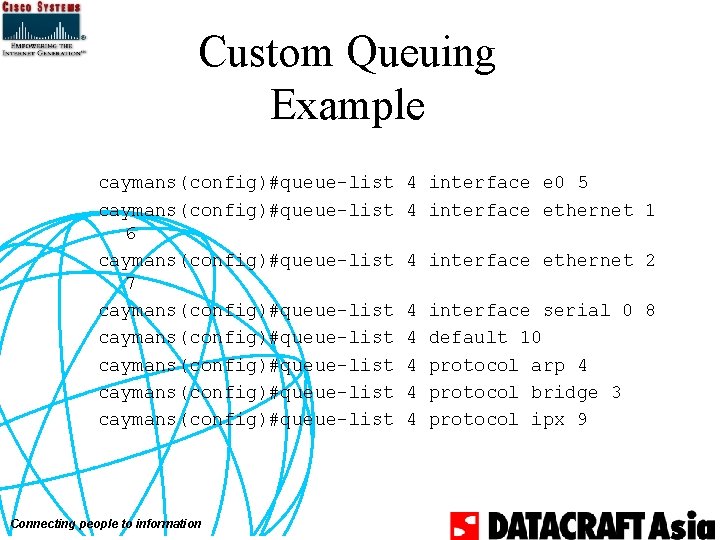
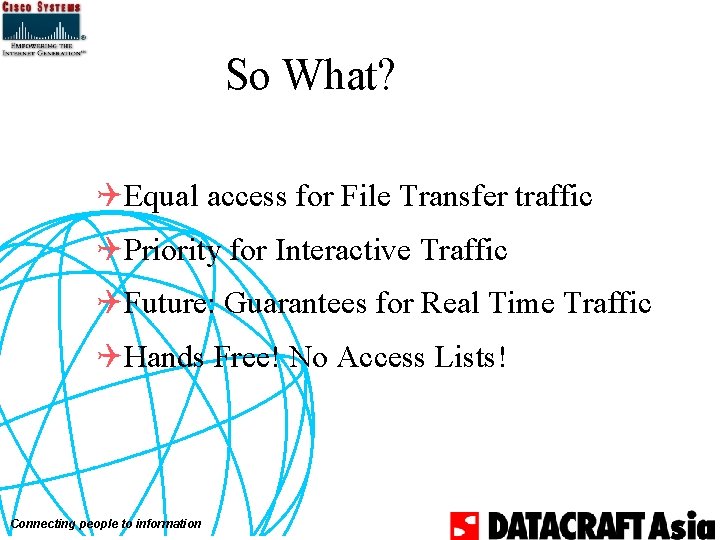
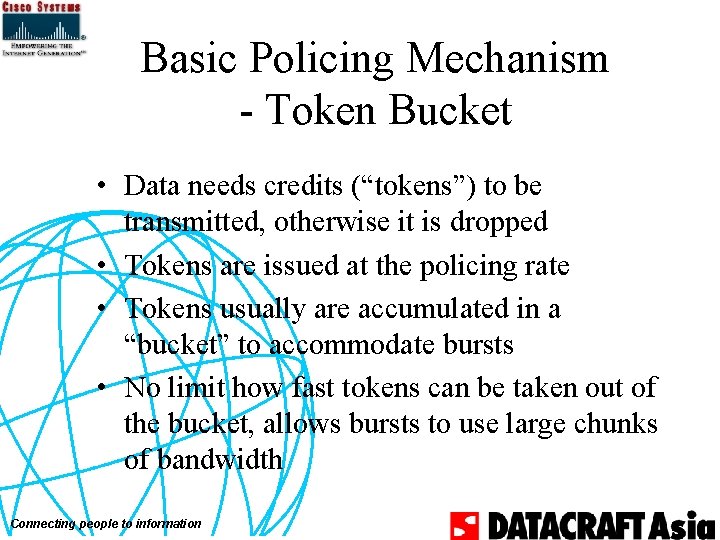
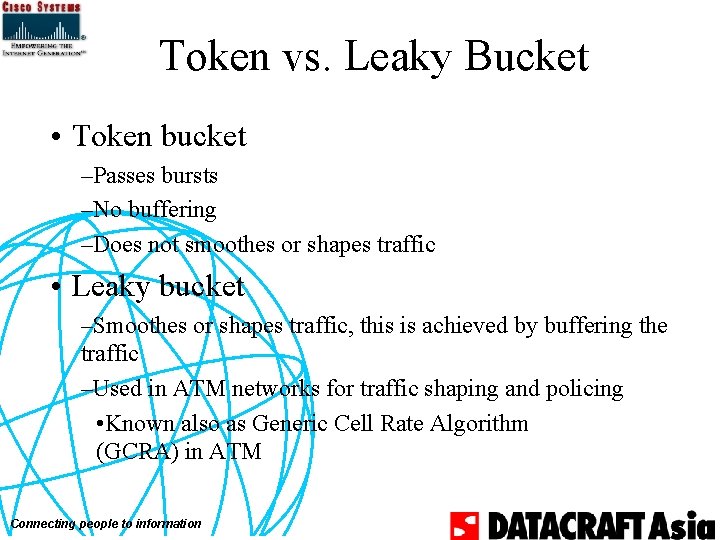
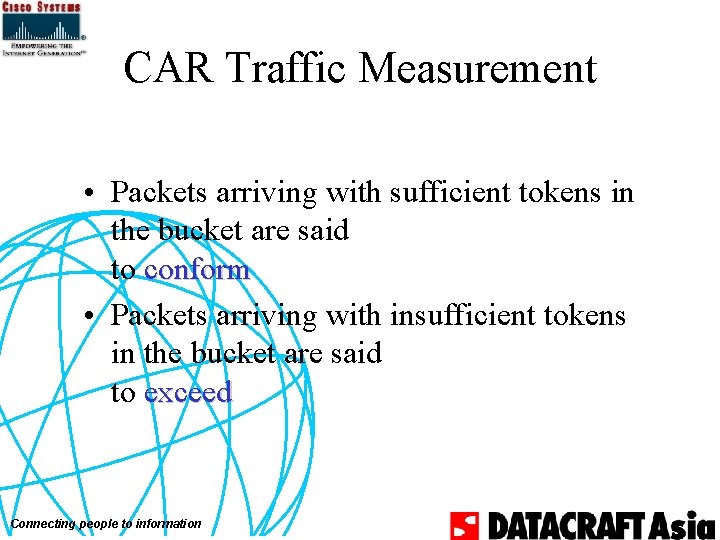
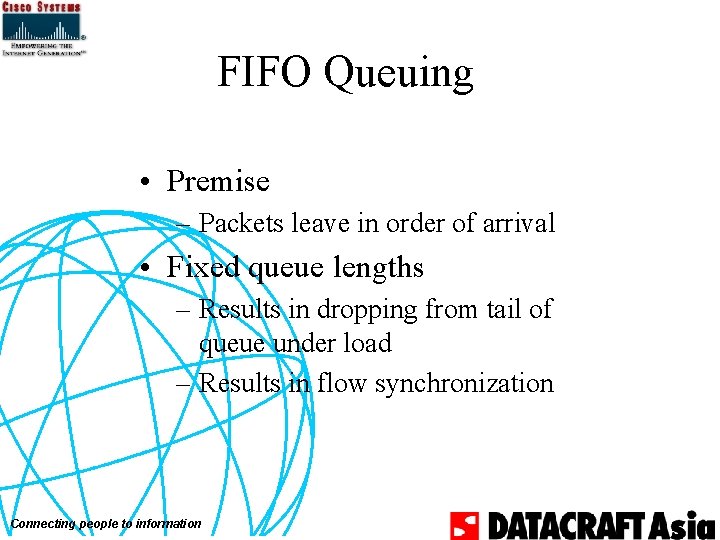
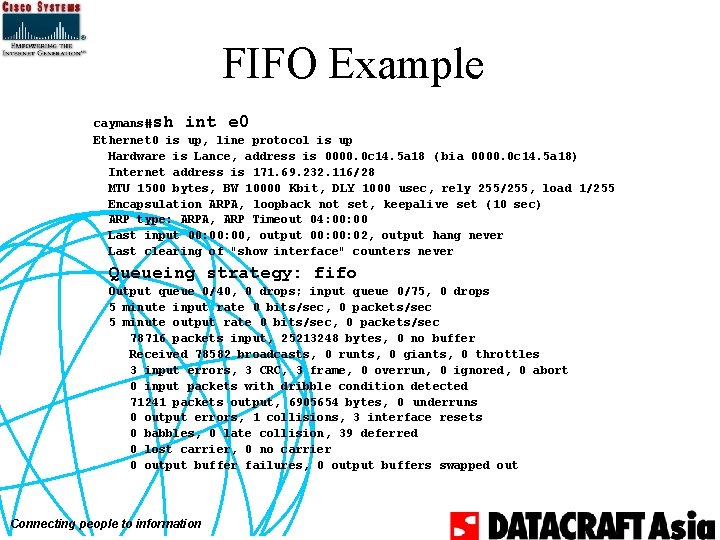
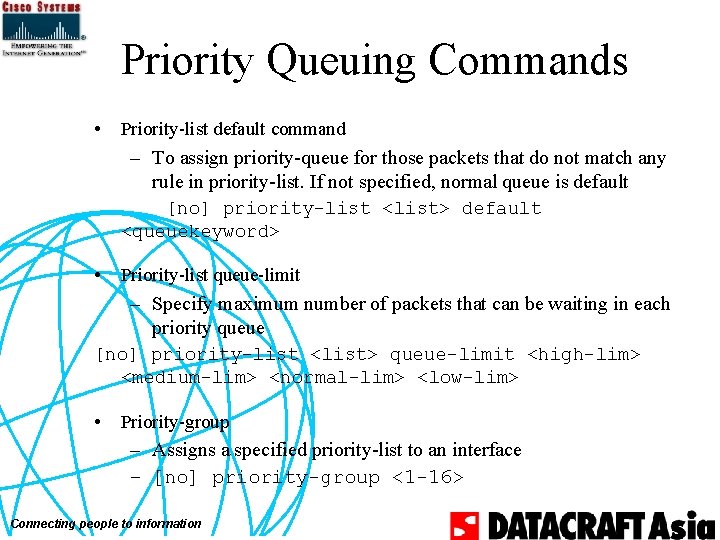
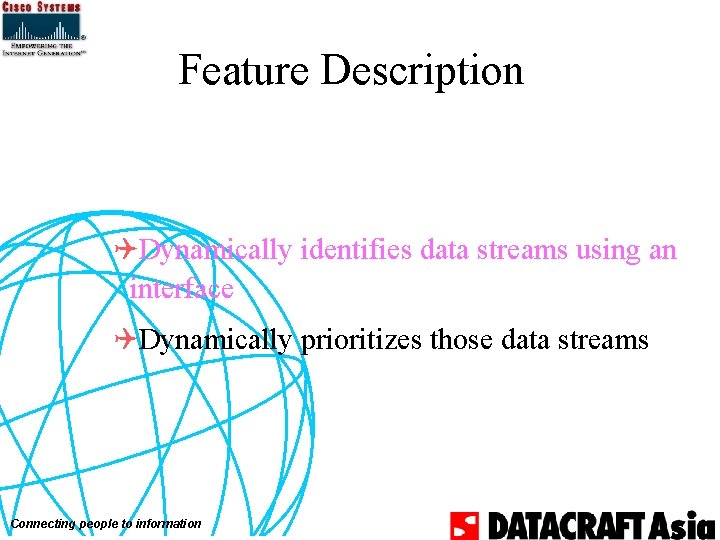
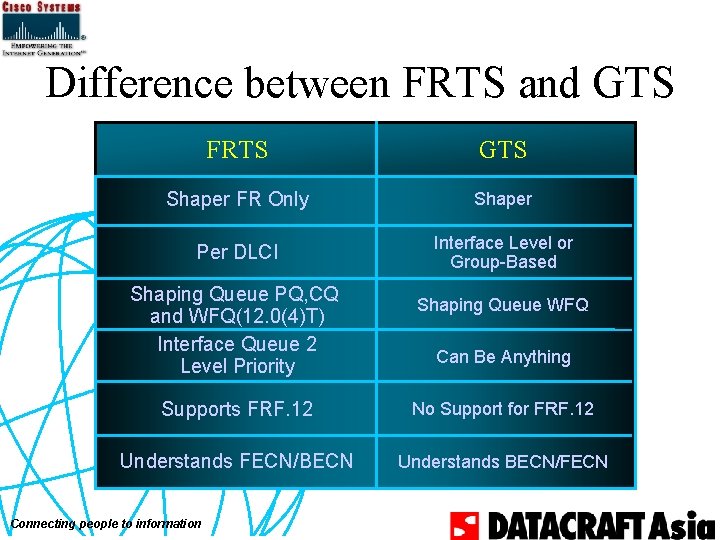
Marking at the Edge: IP Precedence • CAR access-list – [no] access-list rate-limit <1– 99> <ip_precedence> – [no] access-list rate-limit <100– 199> <mac_address> • CAR show command – Show interface [interface] rate-limit Connecting people to information
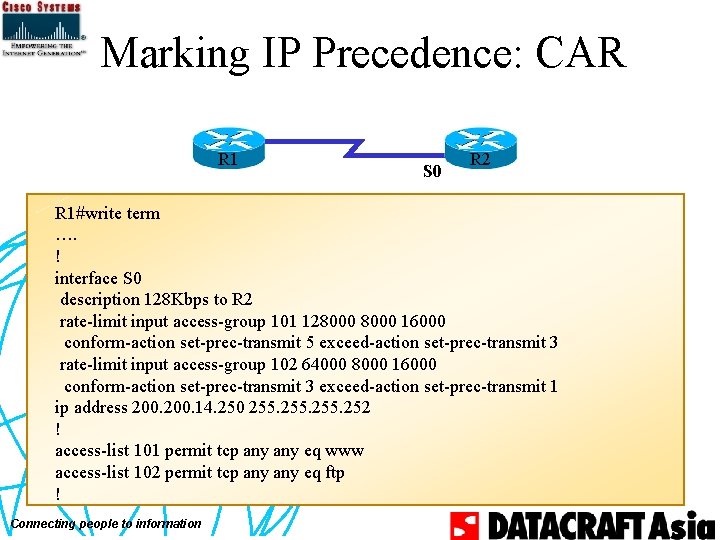
Marking IP Precedence: CAR R 1 S 0 R 2 R 1#write term …. ! interface S 0 description 128 Kbps to R 2 rate-limit input access-group 101 128000 16000 conform-action set-prec-transmit 5 exceed-action set-prec-transmit 3 rate-limit input access-group 102 64000 8000 16000 conform-action set-prec-transmit 3 exceed-action set-prec-transmit 1 ip address 200. 14. 250 255. 252 ! access-list 101 permit tcp any eq www access-list 102 permit tcp any eq ftp ! Connecting people to information
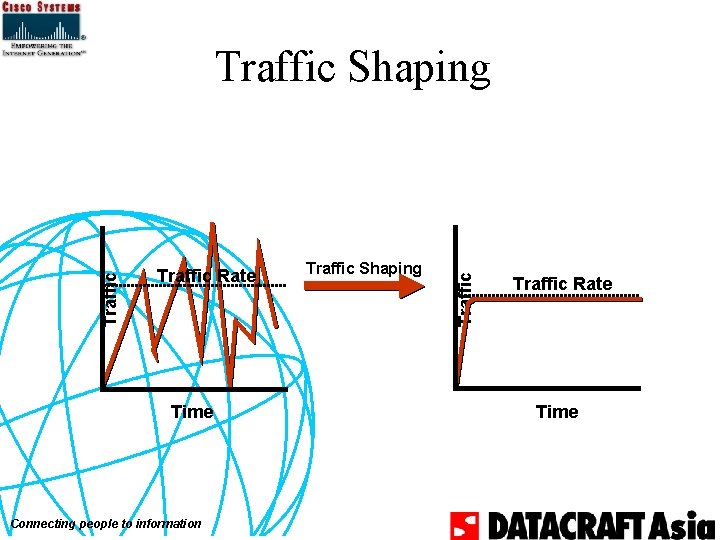
Traffic Rate Time Connecting people to information Traffic Shaping Traffic Rate Time
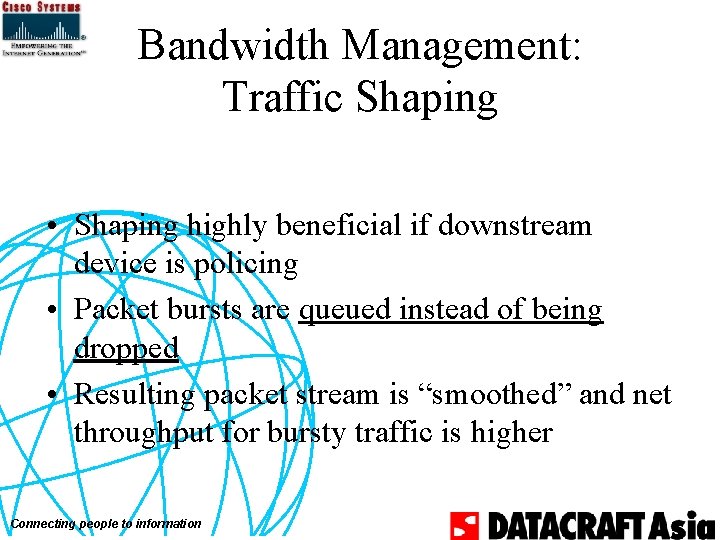
Bandwidth Management: Traffic Shaping • Shaping highly beneficial if downstream device is policing • Packet bursts are queued instead of being dropped • Resulting packet stream is “smoothed” and net throughput for bursty traffic is higher Connecting people to information
Traffic Shaping Queue Structure Forwarder • One queue per –Sub-interface –Access List –DLCI • Feeds into queues at hardware layer Within Token Bucket? Sub-Interface Fancy Queues Yes Interface Congested? No Transmission Queue Connecting people to information No Yes Hardware Interface Queues
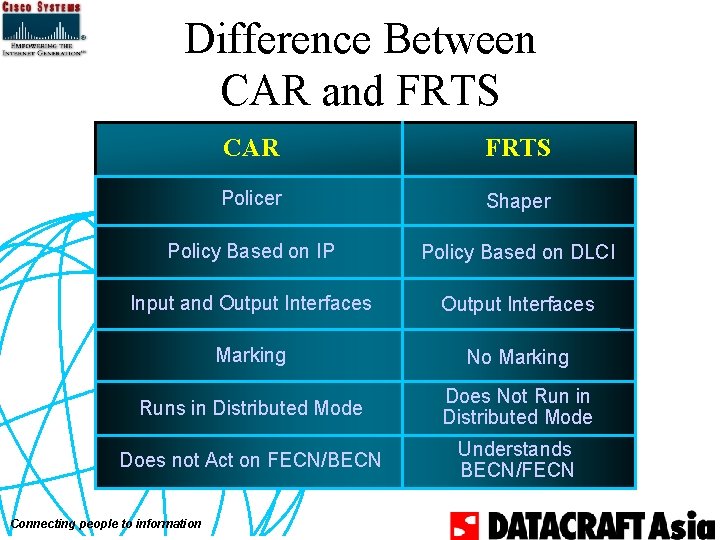
Difference Between CAR and FRTS CAR FRTS Policer Shaper Policy Based on IP Policy Based on DLCI Input and Output Interfaces Marking No Marking Runs in Distributed Mode Does Not Run in Distributed Mode Does not Act on FECN/BECN Understands BECN/FECN Connecting people to information
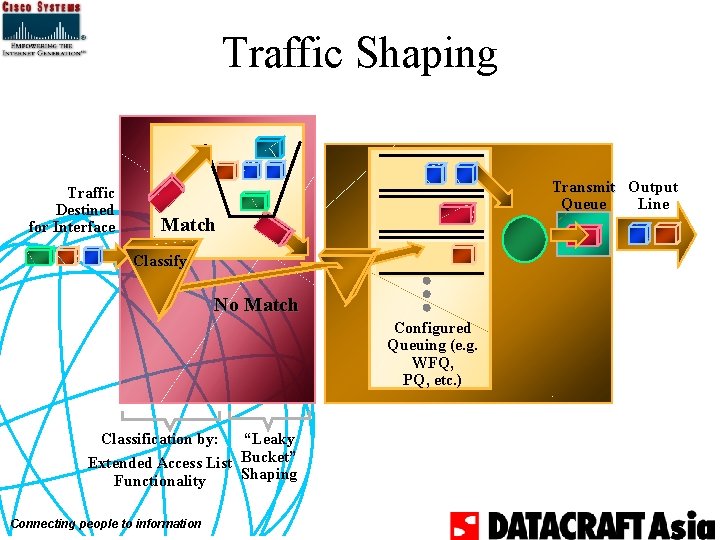
Traffic Shaping Traffic Destined for Interface Transmit Output Queue Line Match Classify No Match Configured Queuing (e. g. WFQ, PQ, etc. ) Classification by: “Leaky Extended Access List Bucket” Shaping Functionality Connecting people to information
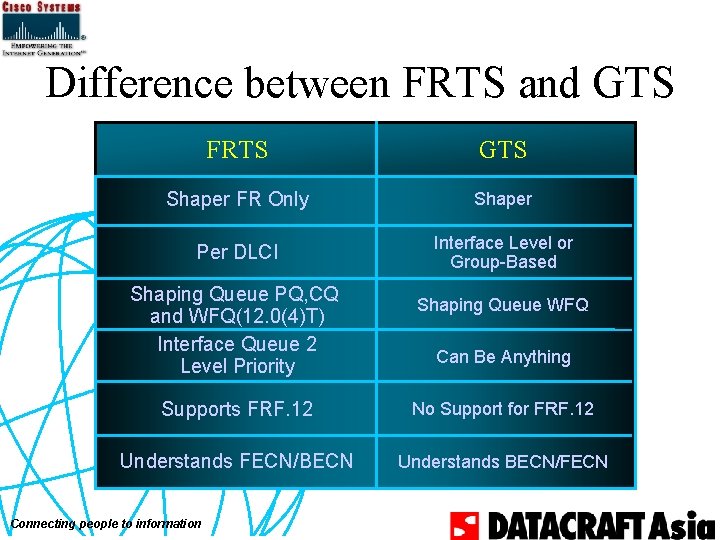
Difference between FRTS and GTS FRTS GTS Shaper FR Only Shaper Per DLCI Interface Level or Group-Based Shaping Queue PQ, CQ and WFQ(12. 0(4)T) Interface Queue 2 Level Priority Shaping Queue WFQ Can Be Anything Supports FRF. 12 No Support for FRF. 12 Understands FECN/BECN Understands BECN/FECN Connecting people to information
![Generic Traffic Shaping Commands Trafficshape rate bitrate burstsize excessburstsize Trafficshape group accesslist Generic Traffic Shaping Commands • Traffic-shape rate bit-rate [burst-size [excess-burst-size]] • Traffic-shape group access-list](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-85.jpg)
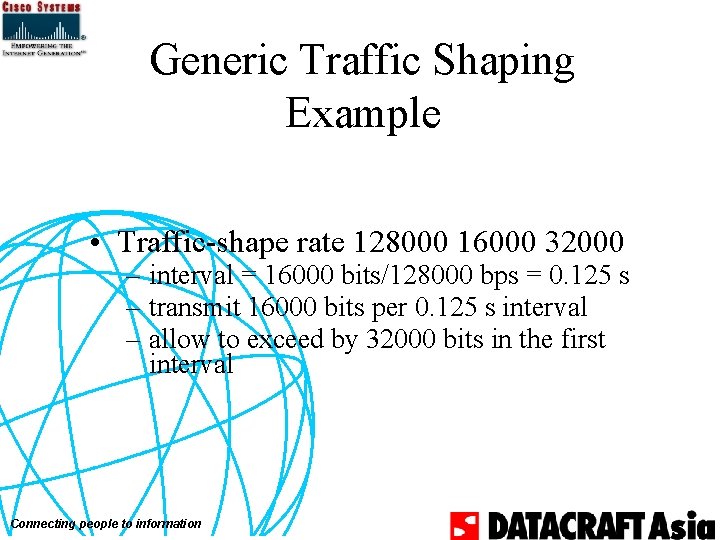
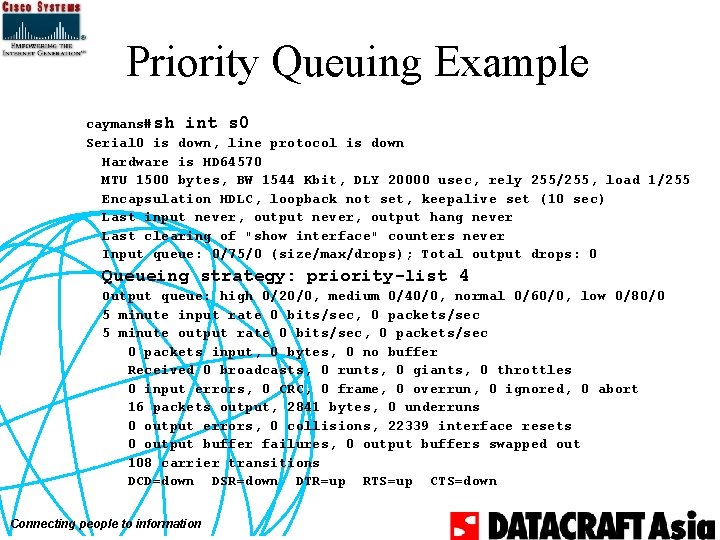
Generic Traffic Shaping Commands • Traffic-shape rate bit-rate [burst-size [excess-burst-size]] • Traffic-shape group access-list bit-rate [burst-size [excess-burst-size]] – bit-rate : access bit rate – burst-size : number of bits per interval – excess-burst-size : number of bits that can exceed burst-size in first interval of congestion – interval : burst-size/bit-rate Connecting people to information
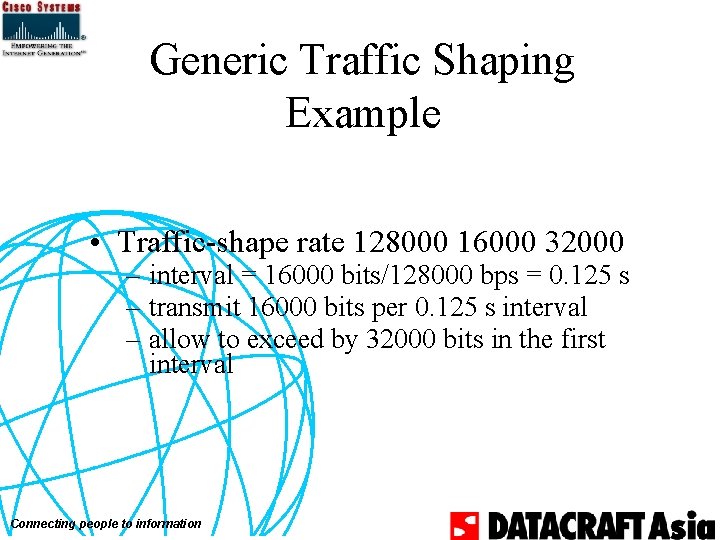
Generic Traffic Shaping Example • Traffic-shape rate 128000 16000 32000 – interval = 16000 bits/128000 bps = 0. 125 s – transmit 16000 bits per 0. 125 s interval – allow to exceed by 32000 bits in the first interval Connecting people to information
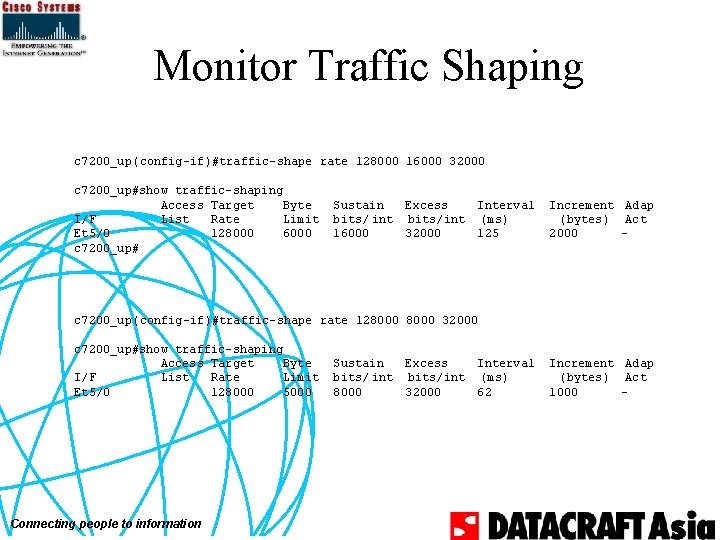
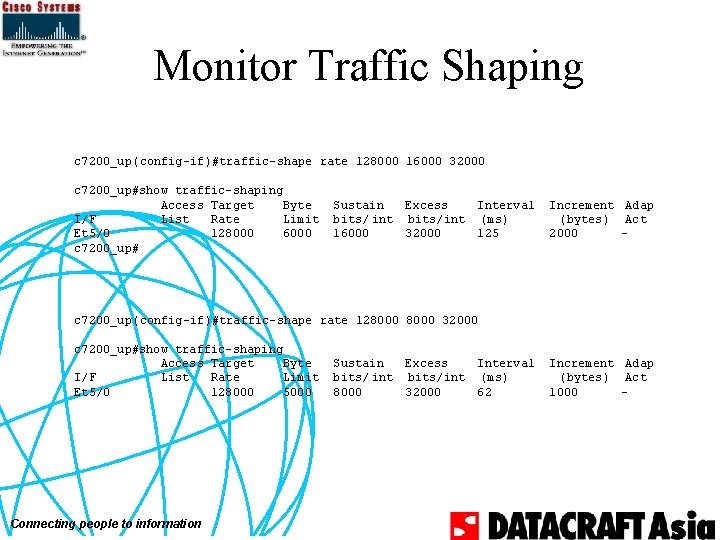
Monitor Traffic Shaping c 7200_up(config-if)#traffic-shape rate 128000 16000 32000 c 7200_up#show traffic-shaping Access Target Byte I/F List Rate Limit Et 5/0 128000 6000 c 7200_up# Sustain bits/ int 16000 Excess Interval bits/int (ms) 32000 125 Increment Adap (bytes) Act 2000 - c 7200_up(config-if)#traffic-shape rate 128000 32000 c 7200_up#show traffic-shaping Access Target Byte I/F List Rate Limit Et 5/0 128000 5000 Connecting people to information Sustain bits/ int 8000 Excess Interval bits/int (ms) 32000 62 Increment Adap (bytes) Act 1000 -
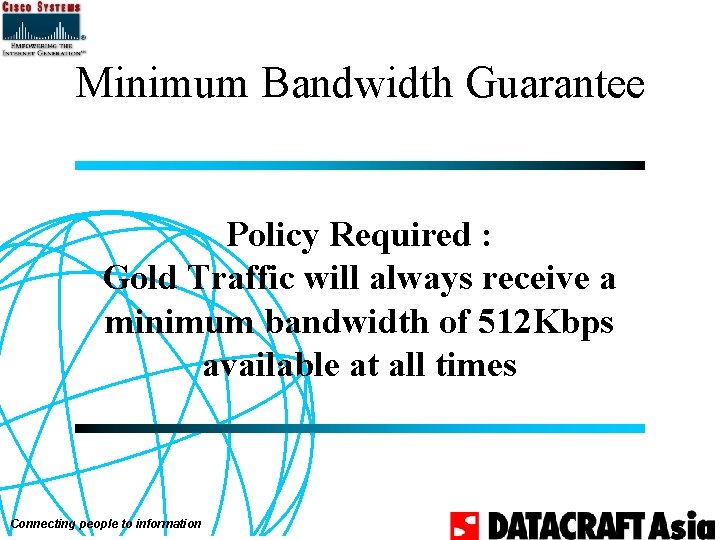
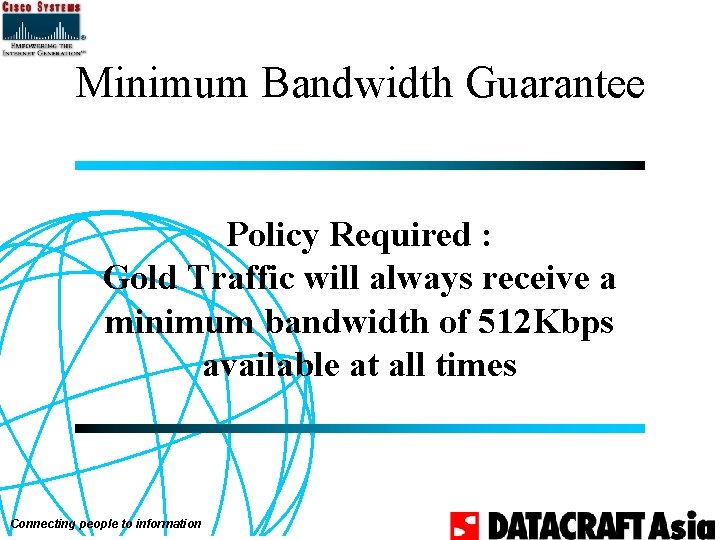
Minimum Bandwidth Guarantee Policy Required : Gold Traffic will always receive a minimum bandwidth of 512 Kbps available at all times Connecting people to information
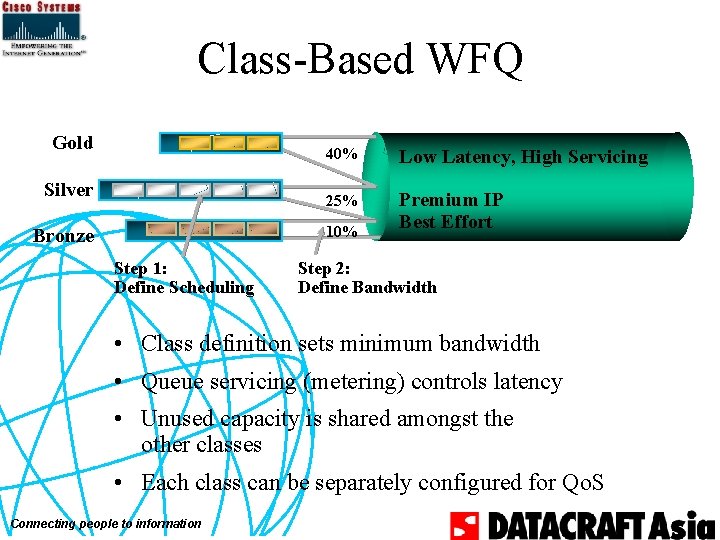
Class-Based WFQ Gold Silver 40% Low Latency, High Servicing 25% Premium IP Best Effort 10% Bronze Step 1: Define Scheduling Step 2: Define Bandwidth • Class definition sets minimum bandwidth • Queue servicing (metering) controls latency • Unused capacity is shared amongst the other classes • Each class can be separately configured for Qo. S Connecting people to information
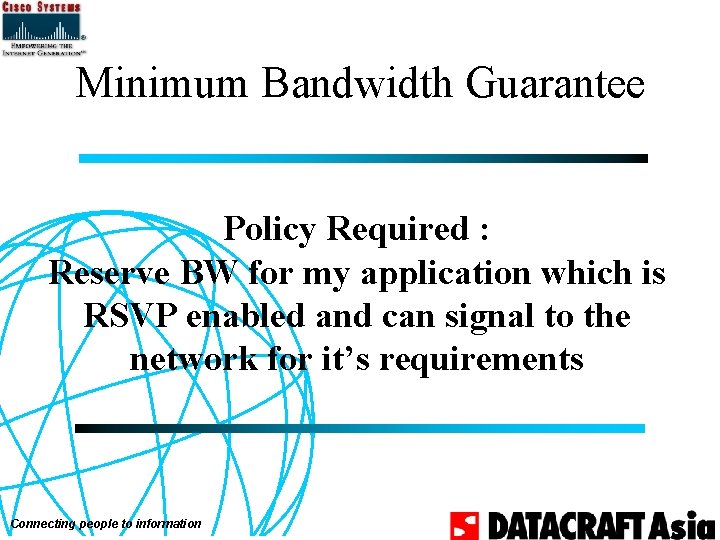
Minimum Bandwidth Guarantee Policy Required : Reserve BW for my application which is RSVP enabled and can signal to the network for it’s requirements Connecting people to information
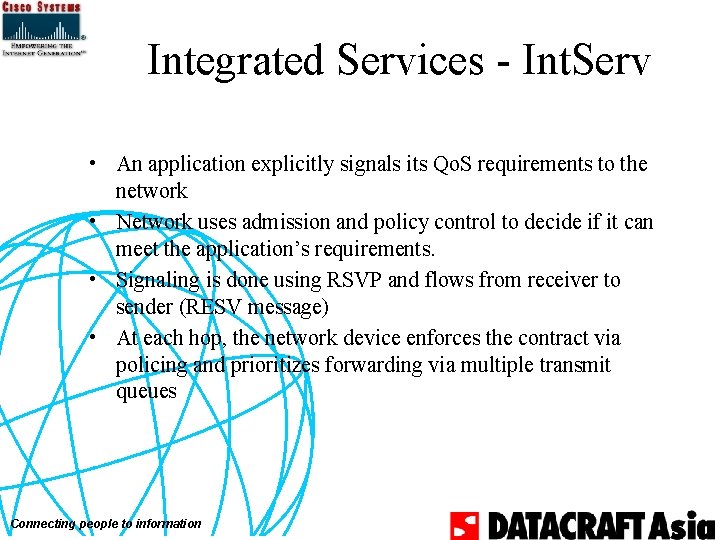
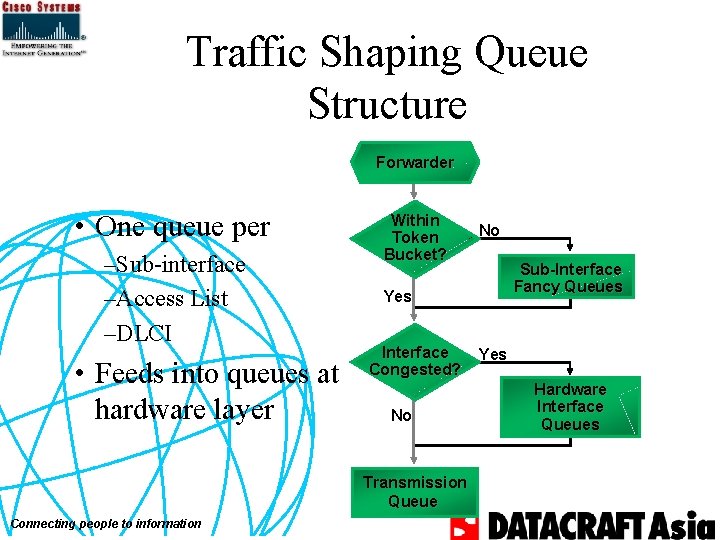
RSVP Policy • RSVP admission control – Accept or deny RSVP requests – Preempt existing reservations based on policy – Policy objects (future) • Configure RSVP parameters such as – Queuing parameters – Traffic shaping parameters Connecting people to information
![Configuring RSVP ip rsvp bandwidth interfacekbps singleflowkbps interface Serial 00 ip address 10 Configuring RSVP ip rsvp bandwidth [interface-kbps] [single-flow-kbps] ! interface Serial 0/0 ip address 10.](https://slidetodoc.com/presentation_image_h/1b1d7d77ca788d346877e5f3874b3270/image-92.jpg)
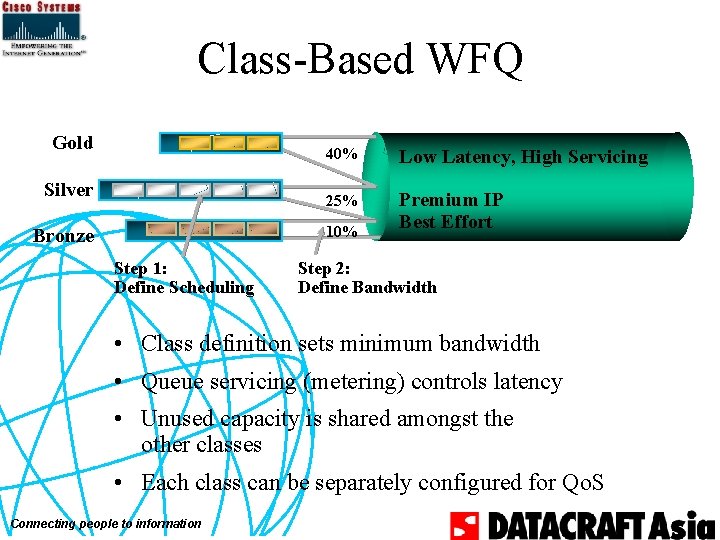
Configuring RSVP ip rsvp bandwidth [interface-kbps] [single-flow-kbps] ! interface Serial 0/0 ip address 10. 1. 1. 2 255. 0. 0 ip rsvp bandwidth 96 96 bandwidth 128 fair-queue 64 256 1000 ! Connecting people to information
Verifying Reservation Accepted bottom#sho ip rsvp installed BPS To From 24 K 10. 1. 1. 1 10. 1. 1. 2 Connecting people to information Protoc DPort Sport Weight Conversation UDP 16384 4 264
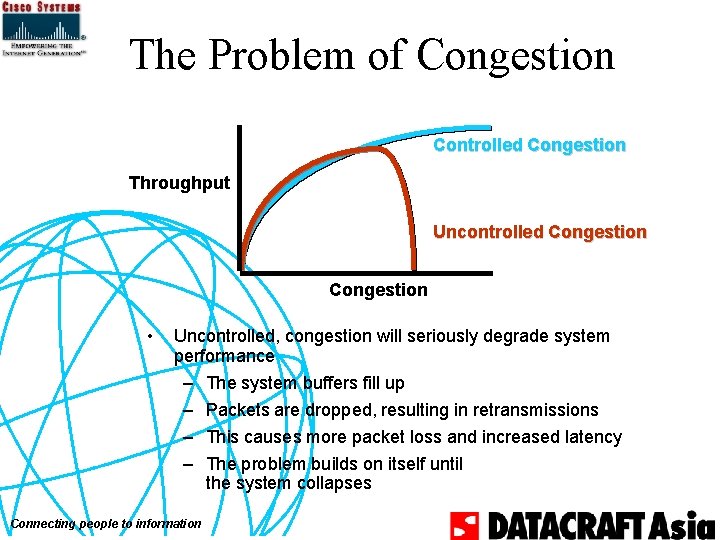
The Problem of Congestion Controlled Congestion Throughput Uncontrolled Congestion • Uncontrolled, congestion will seriously degrade system performance – The system buffers fill up – Packets are dropped, resulting in retransmissions – This causes more packet loss and increased latency – The problem builds on itself until the system collapses Connecting people to information
Drop Policy Required: Bronze or Silver traffic will be dropped when there is congestion. Gold traffic will be forwarded unaffected Connecting people to information
Where Does Internet Congestion Come From? • 95% of traffic is TCP • TCP slow start/fast retransmit – Assures maximal utilization of bottleneck – Therefore assures deep queues absent a control mechanism Connecting people to information
TCP flow control • TCP relies on advertised windows • Smaller TCP receive windows are better for slow links (Trade-off: throughput) • Larger TCP receive windows => more packets in transit Connecting people to information
Behavior of a TCP Receiver • When in receipt of “next message, ” schedules an ACK • When in receipt of something else, acknowledges all it can immediately Connecting people to information N N+ N+ 1 2 N+ 3 1 N+ k Ac +1 k. N 1 c A + k. N c A
Sender Response to ACK • If ACK acknowledges something – Update credit and send • If not, presume it indicates a lost packet – Send first unacknowledged message right away Connecting people to information N N+ N+ 1 2 N+ 3 1 N+ k Ac +1 k. N 1 c A + k. N c A N+ 1
Multiple Drops in TCP N N+ N+ 1 2 N+ 3 • In the event of multiple drops within the same session: –Current TCPs wait for time-out 1 N+ k Ac +1 k. N 1 c A + k. N c A N+ 1 Ack tic tic N+3 Connecting people to information N+3
RED Pushes Back by Drops • Minimizes work done by router • Minimizes average queue depth • Appropriate to interfaces that keep one or less packets in queue per flow Connecting people to information
Queuing Pushes Back in Time • Delays acknowledgments • Stabilizes delay experienced by packets • Appropriate to: – Interfaces that keep several messages in queue from each flow – Transactions Connecting people to information
Random Early Detection (RED) • “TCP slow-start” is used in the event of congestion – Pros: Congestion resolution – Cons: Possibility of global synchronization when multiple senders reduce transmission rates then ramp up all at once. Connecting people to information
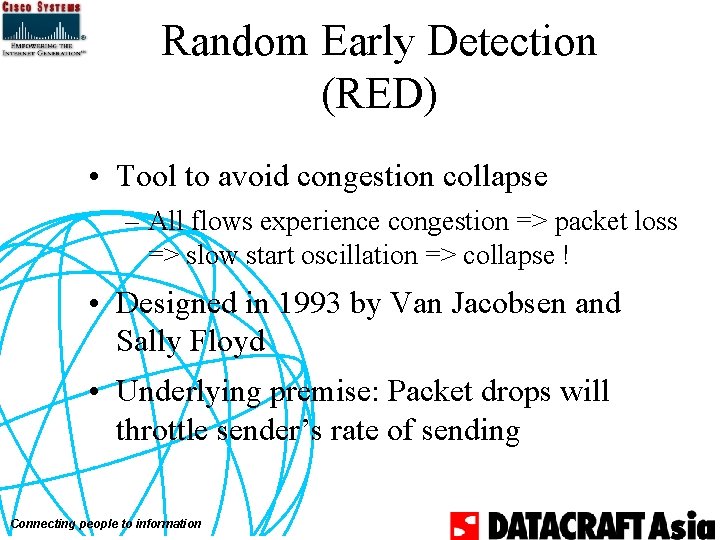
Random Early Detection (RED) • Tool to avoid congestion collapse – All flows experience congestion => packet loss => slow start oscillation => collapse ! • Designed in 1993 by Van Jacobsen and Sally Floyd • Underlying premise: Packet drops will throttle sender’s rate of sending Connecting people to information
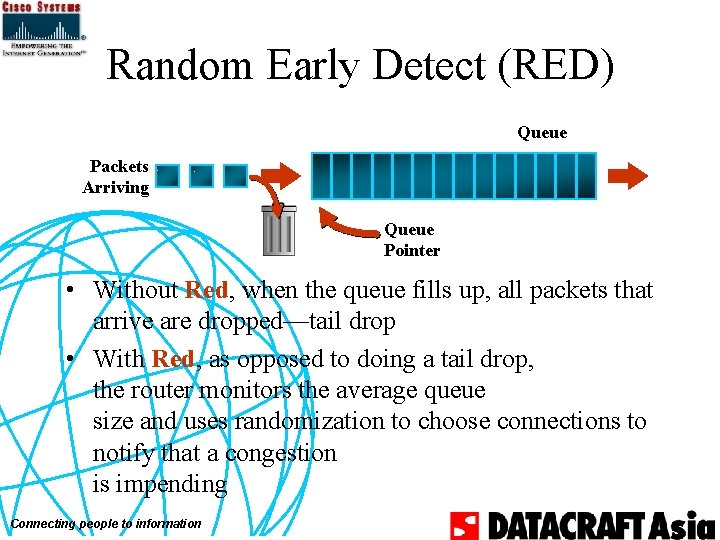
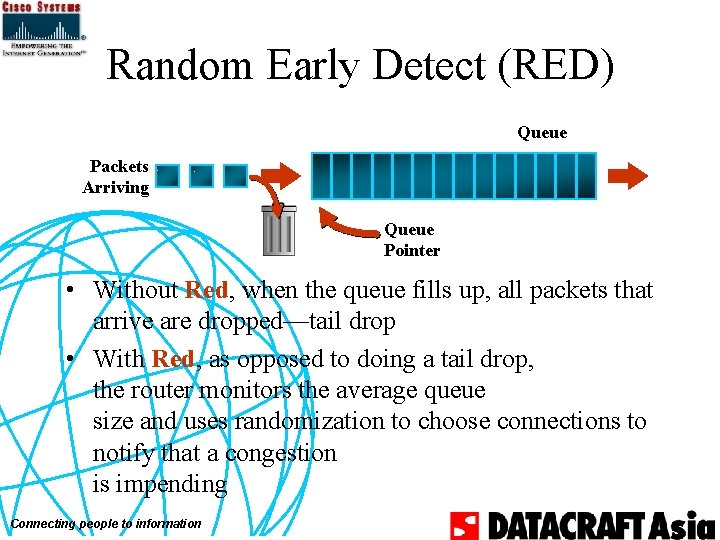
Random Early Detect (RED) Queue Packets Arriving Queue Pointer • Without Red, when the queue fills up, all packets that arrive are dropped—tail drop • With Red, as opposed to doing a tail drop, the router monitors the average queue size and uses randomization to choose connections to notify that a congestion is impending Connecting people to information
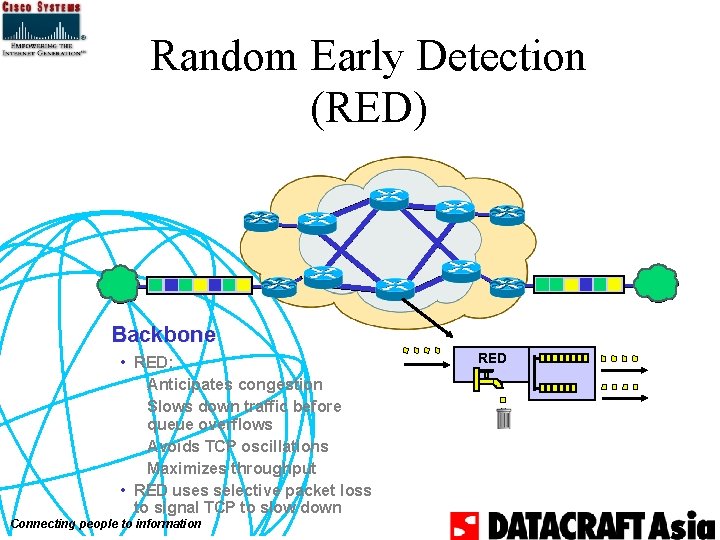
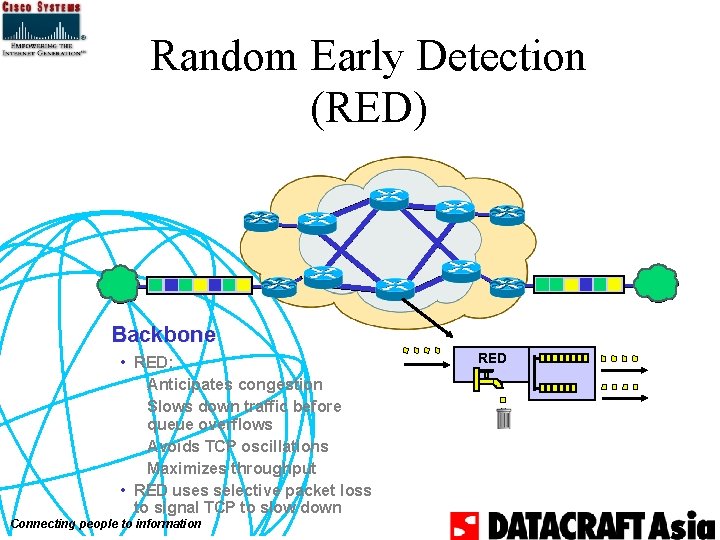
Random Early Detection (RED) Backbone • RED: Anticipates congestion Slows down traffic before queue overflows Avoids TCP oscillations Maximizes throughput • RED uses selective packet loss to signal TCP to slow down Connecting people to information RED
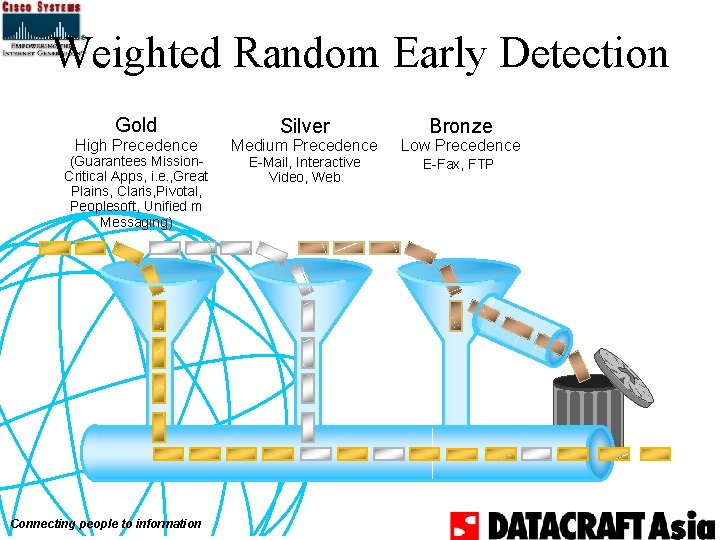
Weighted Random Early Detection Gold High Precedence (Guarantees Mission. Critical Apps, i. e. , Great Plains, Claris, Pivotal, Peoplesoft, Unified m Messaging) Connecting people to information Silver Medium Precedence E-Mail, Interactive Video, Web Bronze Low Precedence E-Fax, FTP
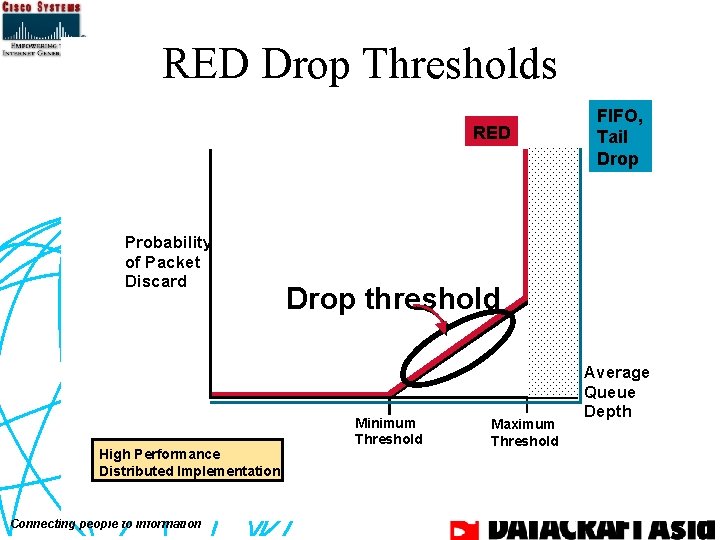
RED Drop Thresholds RED Packet Drop Thresholds FIFO, RED Probability of Packet Discard High Performance Distributed Implementation Connecting people to information Tail Drop threshold Minimum Threshold Maximum Threshold Average Queue Depth
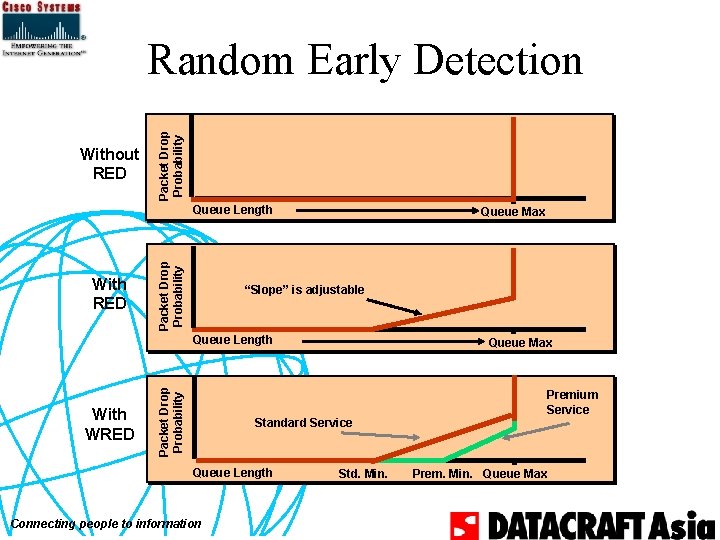
Without RED Packet Drop Probability Random Early Detection With RED Packet Drop Probability Queue Length Queue Max “Slope” is adjustable With WRED Packet Drop Probability Queue Length Queue Max Standard Service Queue Length Connecting people to information Std. Min. Premium Service Prem. Min. Queue Max
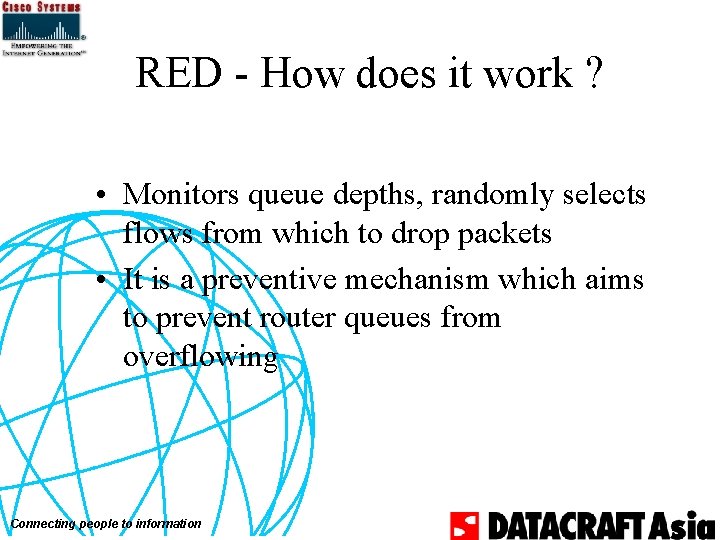
RED - How does it work ? • Monitors queue depths, randomly selects flows from which to drop packets • It is a preventive mechanism which aims to prevent router queues from overflowing Connecting people to information
RED—Packet-Drop Probability • Packets are dropped sufficiently frequently to control the average queue size • The probability that a packet is dropped from a connection is proportional to the amount of packets sent by the connection Connecting people to information
RED - When not to use it • For protocols like voice over RTP over UDP over IP. • For non-conforming traffic like Novell Netware of Appletalk Connecting people to information
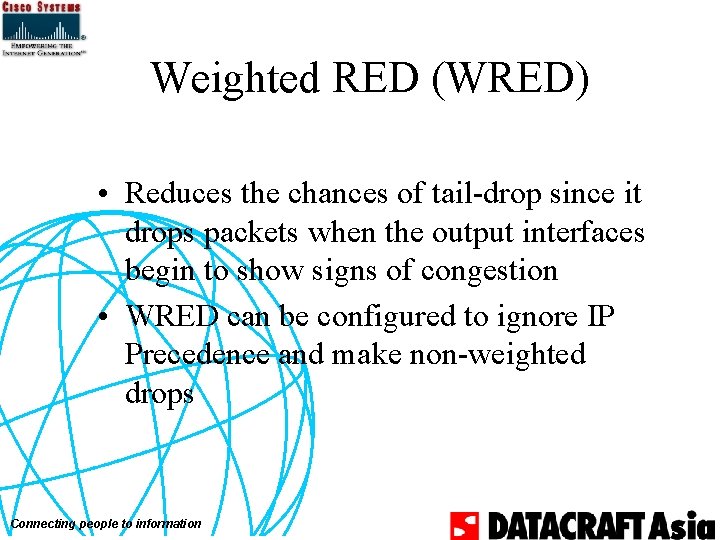
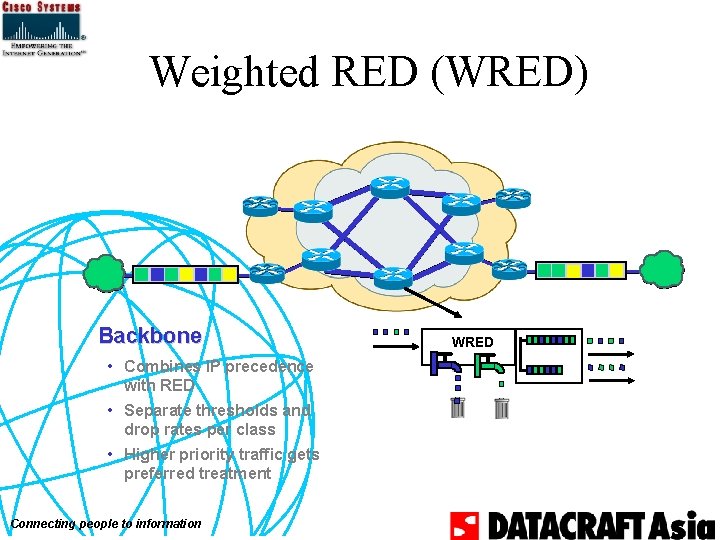
Weighted RED (WRED) • WRED combines RED with IP Precedence to implement multiple service classes • Each service class has a defined min and max thresholds, and drop rates Connecting people to information
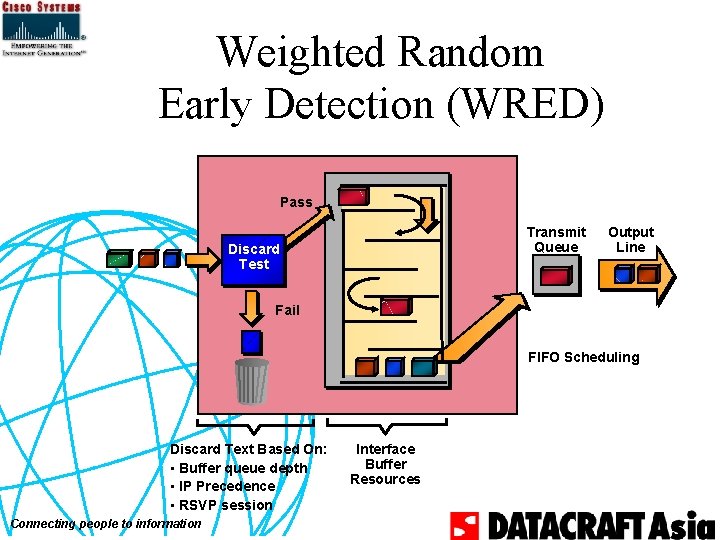
Weighted Random Early Detection (WRED) Pass Transmit Queue Discard Test Output Line Fail FIFO Scheduling Discard Text Based On: • Buffer queue depth • IP Precedence • RSVP session Connecting people to information Interface Buffer Resources
Weighted RED (WRED) • Reduces the chances of tail-drop since it drops packets when the output interfaces begin to show signs of congestion • WRED can be configured to ignore IP Precedence and make non-weighted drops Connecting people to information
When Should I Use WRED? • Congested long-haul links (e. g. , trans-oceanic links) • Not recommended for campus networks • When the bulk of your traffic is TCP as oppose to UDP – Remember only TCP will react to a packet drop UDP will not Connecting people to information
Weighted RED (WRED) Backbone • Combines IP precedence with RED • Separate thresholds and drop rates per class • Higher priority traffic gets preferred treatment Connecting people to information WRED
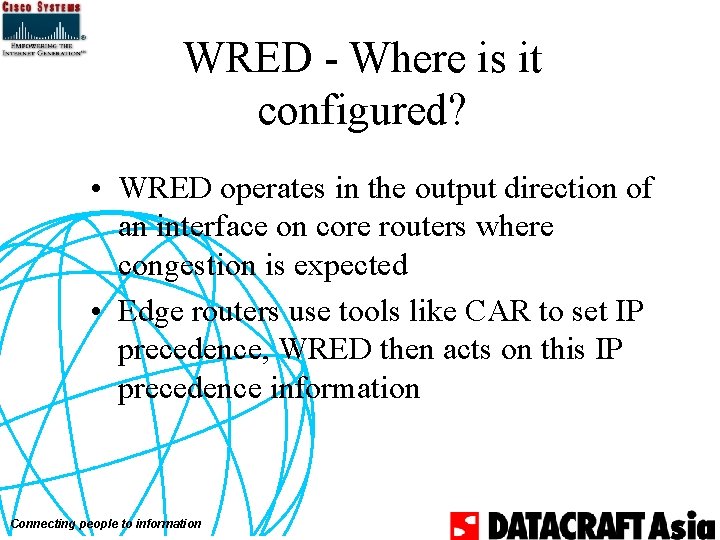
WRED - Where is it configured? • WRED operates in the output direction of an interface on core routers where congestion is expected • Edge routers use tools like CAR to set IP precedence, WRED then acts on this IP precedence information Connecting people to information
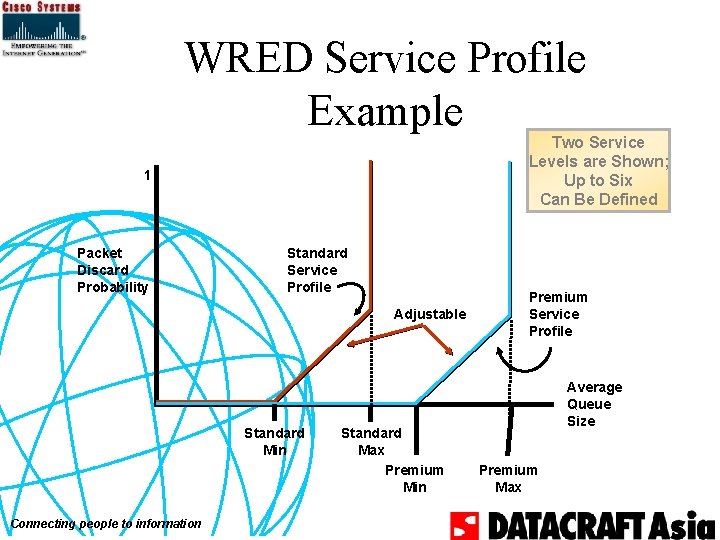
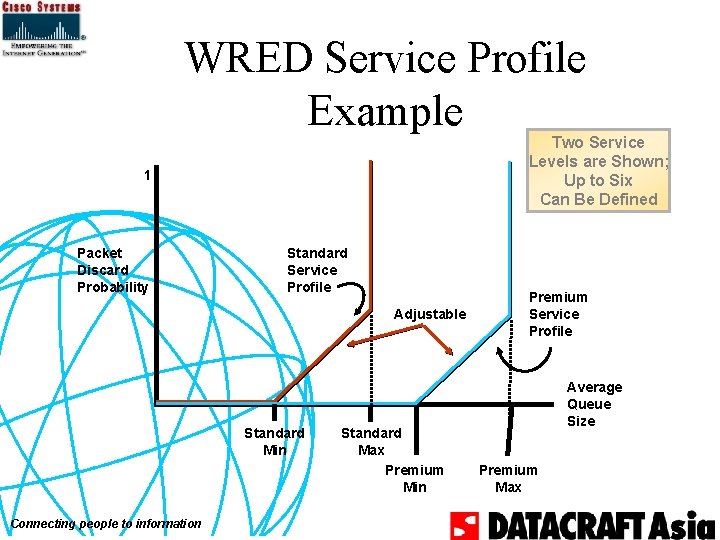
WRED Service Profile Example Two Service Levels are Shown; Up to Six Can Be Defined 1 Packet Discard Probability Standard Service Profile Adjustable Standard Min Connecting people to information Standard Max Premium Min Premium Service Profile Average Queue Size Premium Max
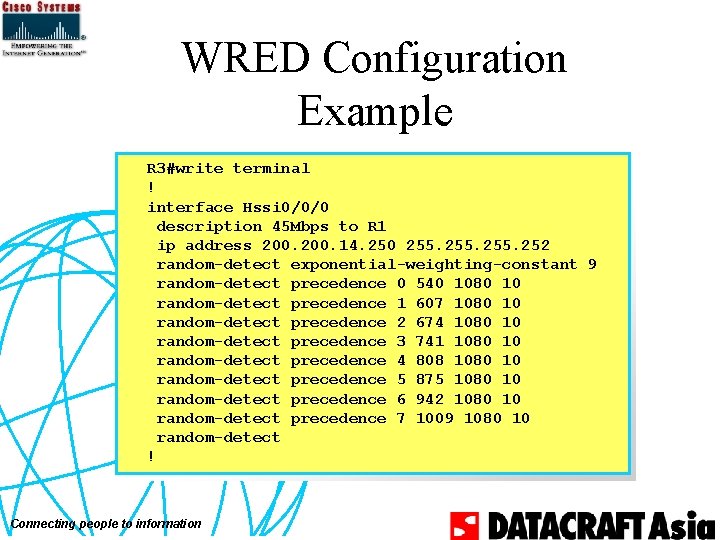
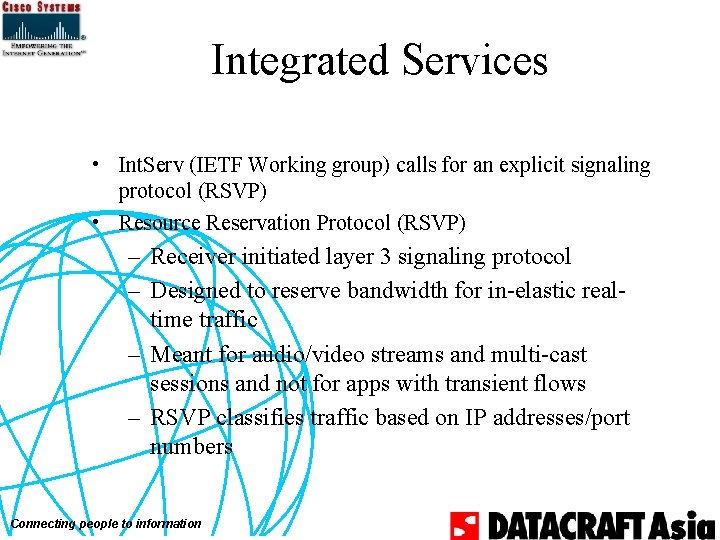
WRED Configuration Example R 3#write terminal ! interface Hssi 0/0/0 description 45 Mbps to R 1 ip address 200. 14. 250 255. 252 random-detect exponential-weighting-constant 9 random-detect precedence 0 540 1080 10 random-detect precedence 1 607 1080 10 random-detect precedence 2 674 1080 10 random-detect precedence 3 741 1080 10 random-detect precedence 4 808 1080 10 random-detect precedence 5 875 1080 10 random-detect precedence 6 942 1080 10 random-detect precedence 7 1009 1080 10 random-detect ! Connecting people to information